Cybersecurity specialists reported the finding of a critical information disclosure vulnerability in the Linux kernel, the successful exploitation of which would allow sensitive information to be extracted from the compromised system memory. Tracked as CVE-2020-28588, the flaw lies in the /proc/pid/syscall functionality of 32-bit ARM devices running Linux and exists due to incorrect conversion of numeric values when reading the file. The flaw was discovered by the Cisco Talos team.
A threat actor can generate 24 bytes of uninitialized stack memory using a few commands, which could prevent randomization of kernel address space design (KASLR), an anti-exploitation technique that implements multiple random objects to avoid predictable patterns that a threat actor might guess.
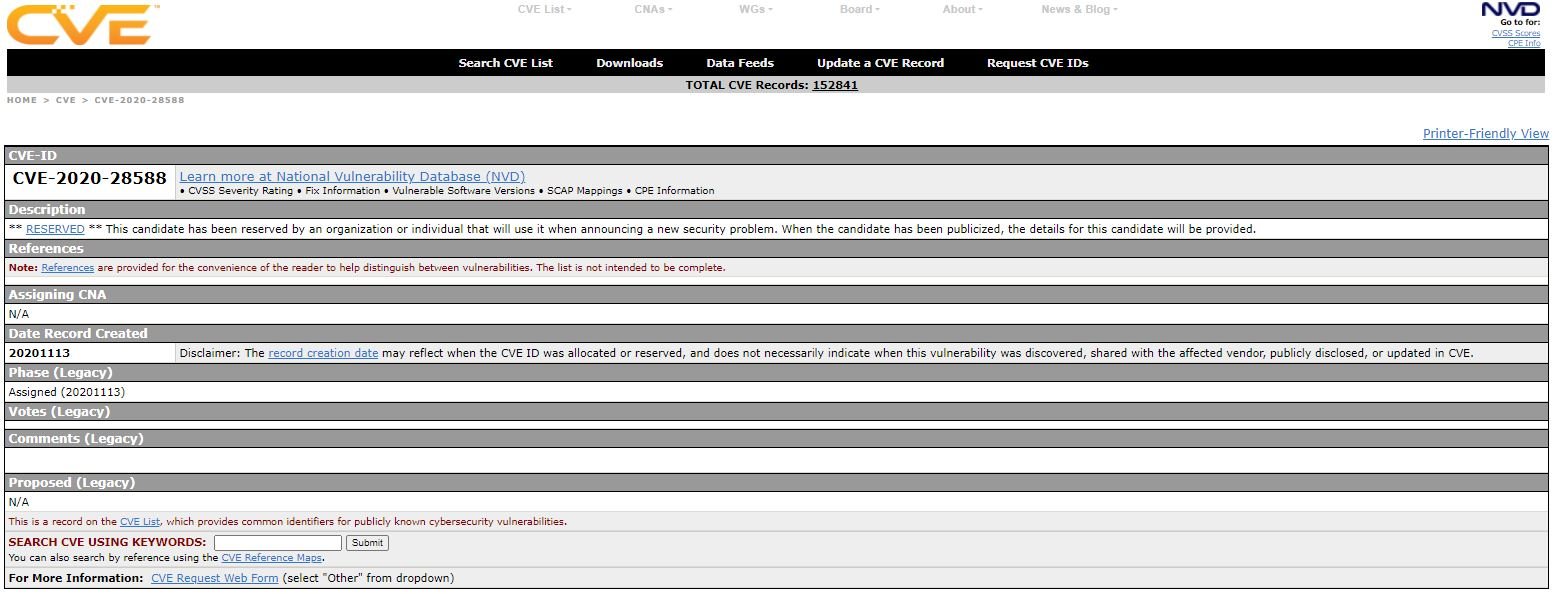
According to the report, an attack would be virtually impossible to detect on a network remotely, and successful attacks could abuse this information leak to successfully exploit some unpatched vulnerabilities on Linux systems.
Proc is a special pseudo-file system on Unix-like operating systems that is used to dynamically access process data found in the kernel. An attacker could exploit the flaw by reading /proc/<pid>/syscall: “We can see the output on any given Linux system whose kernel was configured with CONFIG_HAVE_ARCH_TRACEHOOK“, the report mentions.
The file exposes the system call number and argument records of the system call that the process is currently executing, followed by stack pointer values and program counter logs: “The values of the six argument records are exposed, although most system calls use fewer records,” Cisco experts add.
Researchers first discovered the problem on an Azure Sphere v20.10 device, a 32-bit ARM device running an updated Linux kernel.
Although Linux kernel flaws are unusual, they eventually occur. In late 2020, a report by Intel and Google warned the cybersecurity community about detecting BleedingTooth flaw in Bluez, the Bluetooth protocol stack for Linux-based Internet of Things (IoT) devices.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.
He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.