Search results for "Analysis"
-

 4.3KVulnerabilities
4.3KVulnerabilitiesSystemBC Malware’s C2 Server Analysis Exposes Payload Delivery Tricks
Cybersecurity researchers have shed light on the command-and-control (C2) server workings of a known malware family called SystemBC. “SystemBC can be purchased...
-

 3.9KMalware
3.9KMalwareResearchers Unveal GuLoader Malware’s Latest Anti-Analysis Techniques
Threat hunters have unmasked the latest tricks adopted by a malware strain called GuLoader in an effort to make analysis more challenging....
-

 2.1KMalware
2.1KMalwareTurla Updates Kazuar Backdoor with Advanced Anti-Analysis to Evade Detection
The Russia-linked hacking crew known as Turla has been observed using an updated version of a known second-stage backdoor referred to as...
-

 4.8KMalware
4.8KMalwareAnalysis and Config Extraction of Lu0Bot, a Node.js Malware with Considerable Capabilities
Nowadays, more malware developers are using unconventional programming languages to bypass advanced detection systems. The Node.js malware Lu0Bot is a testament to...
-

 4.6KMalware
4.6KMalwareNew Analysis Reveals Raspberry Robin Can be Repurposed by Other Threat Actors
A new analysis of Raspberry Robin’s attack infrastructure has revealed that it’s possible for other threat actors to repurpose the infections for...
-
 2.9KInfosec
2.9KInfosecBest Malware Analysis Tools List For Security Researchers & Malware Analyst 2023
Malware analysis tools are highly essential for Security Professionals who always need to learn many tools, techniques, and concepts to analyze sophisticated...
-
 3.1KMalware
3.1KMalwareGuLoader Malware Uses Advanced Anti-Analysis Techniques to Evade Detection
An advanced malware downloader named GuLoader has recently been exposed by cybersecurity researchers at CrowdStrike. This advanced downloader has the capability to...
-

 2.0KMalware
2.0KMalwareNerbian RAT: New malware with advanced anti-analysis and anti-reversing capabilities uses information about WHO and COVID-19 for its spreading
Proofpoint researchers report the detection of a new variant of remote access Trojan (RAT) characterized by the use of multiple techniques and...
-
 4.6KMalware
4.6KMalwarePackage Analysis – OpenSSf Tool to Detect Malicious Packages in Popular Open-Source Repositories
A prototype version of the Package Analysis tool has been recently released by the Open Source Security Foundation (OpenSSF), and it is...
-

 2.7KMalware
2.7KMalwareResearchers Share In-Depth Analysis of PYSA Ransomware Group
An 18-month-long analysis of the PYSA ransomware operation has revealed that the cybercrime cartel followed a five-stage software development cycle from August...
-

 4.2KMalware
4.2KMalwareHow to Build a Custom Malware Analysis Sandbox
Before hunting malware, every researcher needs to find a system where to analyze it. There are several ways to do it: build...
-

 2.7KMalware
2.7KMalwareHow Malware Analysis Helps You Detect Reused Malware code
The fight against malware has taken another angle. Cybersecurity experts found a way to detect reused malware, improving malware analysis. In this...
-

 2.8KTutorials
2.8KTutorialsHow to do automatic vulnerability analysis and assessment of your applications & network free of cost?
The automatic analysis of potential security flaws has become one of the essential tasks for developers, researchers and experts in vulnerability assessment,...
-

 2.3KInfosec
2.3KInfosecWhy Companies Should Start Taking Behavioural Analysis Seriously?
Behavioural analysis uses machine learning, artificial intelligence, big data, and analytics to recognize malicious behavior by examining differences in everyday activities. Behavioural...
-
 1.2KTutorials
1.2KTutorialsTop 6 remote access Trojans (RAT) used by Russian hackers. Which one is the best as per malware analysis experts?
Remote access Trojans (RATs) are one of the most popular hacking tools, as they allow attackers to remotely control a compromised system....
-

 1.6KRansomware
1.6KRansomwareResearchers Perform An Analysis on Chinese Malware Used Against Russian Government
Security researchers from the threat hunting and intelligence company Group-IB have revealed that in 2020, at least two espionage groups from China...
-
 3.8KMalware
3.8KMalwareCertified Malware Analyst – Exploit Development, Expert Malware Analysis & Reverse Engineering
Certified Malware Analyst: In 2020, sophisticated Cyber attacks keep on increasing by APT threats that target most of the enterprise-level networks and...
-
 2.8KVulnerability Analysis
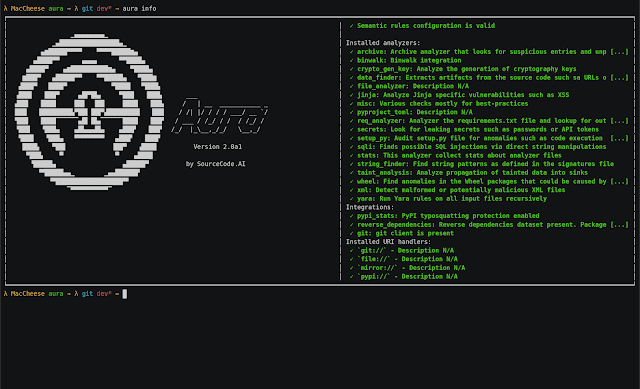
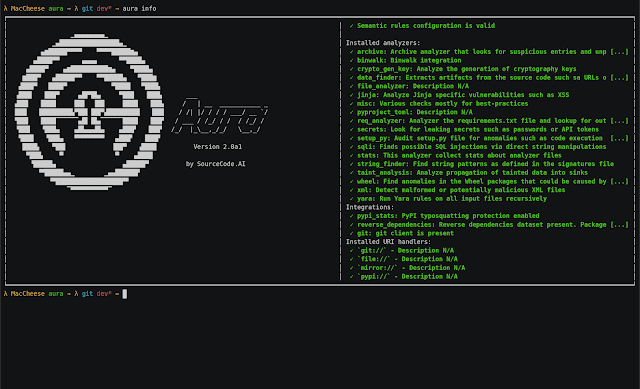
2.8KVulnerability AnalysisAura – Python Source Code Auditing And Static Analysis On A Large Scale
Aura is a static analysis framework developed as a response to the ever-increasing threat of malicious packages and vulnerable code published...
-

 3.8KCyber Crime
3.8KCyber CrimeEmotet strikes Quebec’s Department of Justice: An ESET Analysis
The cyberattack, which affected 14 inboxes belonging to the Department of Justice, was confirmed by ESET researchers
-
 2.4KHackers Repository
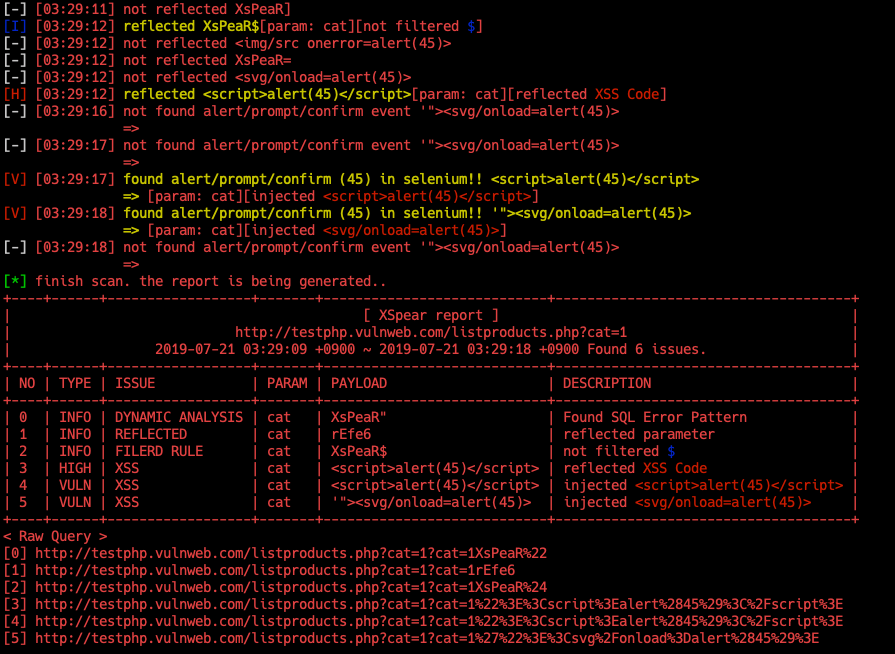
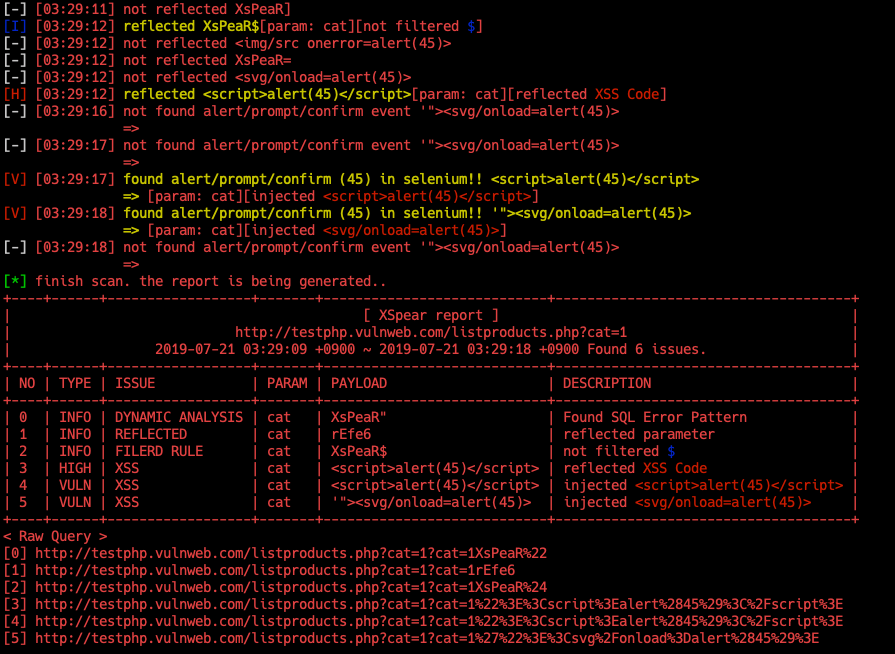
2.4KHackers RepositoryXSpear v1.3 releases: Powerfull XSS Scanning and Parameter Analysis tool
XSpear XSpear is XSS Scanner on ruby gems Key features Pattern matching based XSS scanning Detect alert confirm prompt event on headless browser (with Selenium) Testing...
-
 2.5KHack Tools
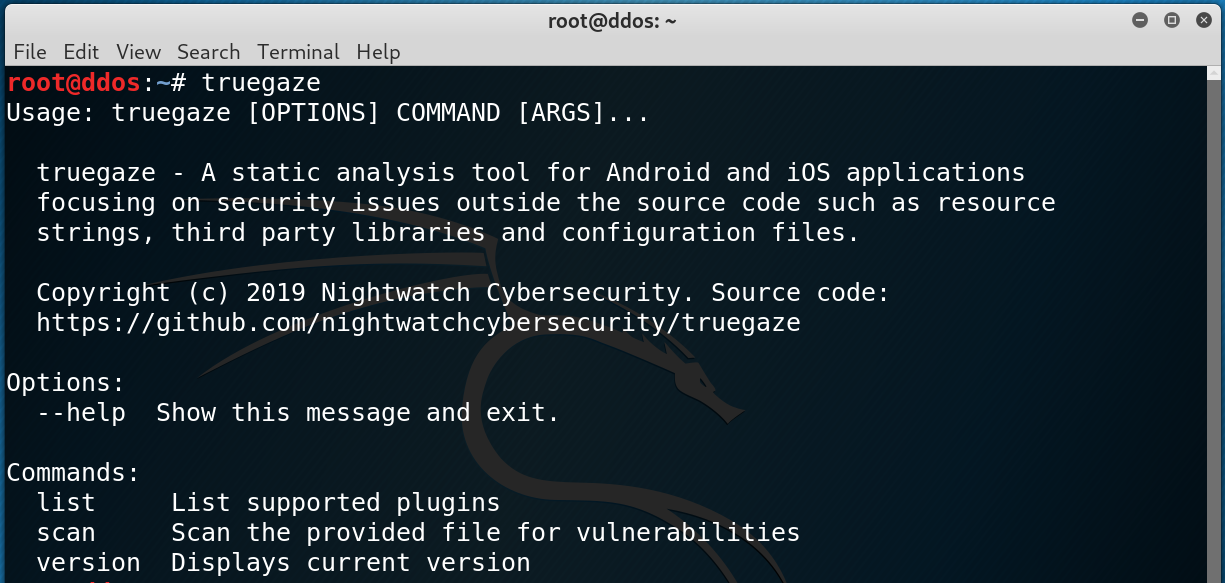
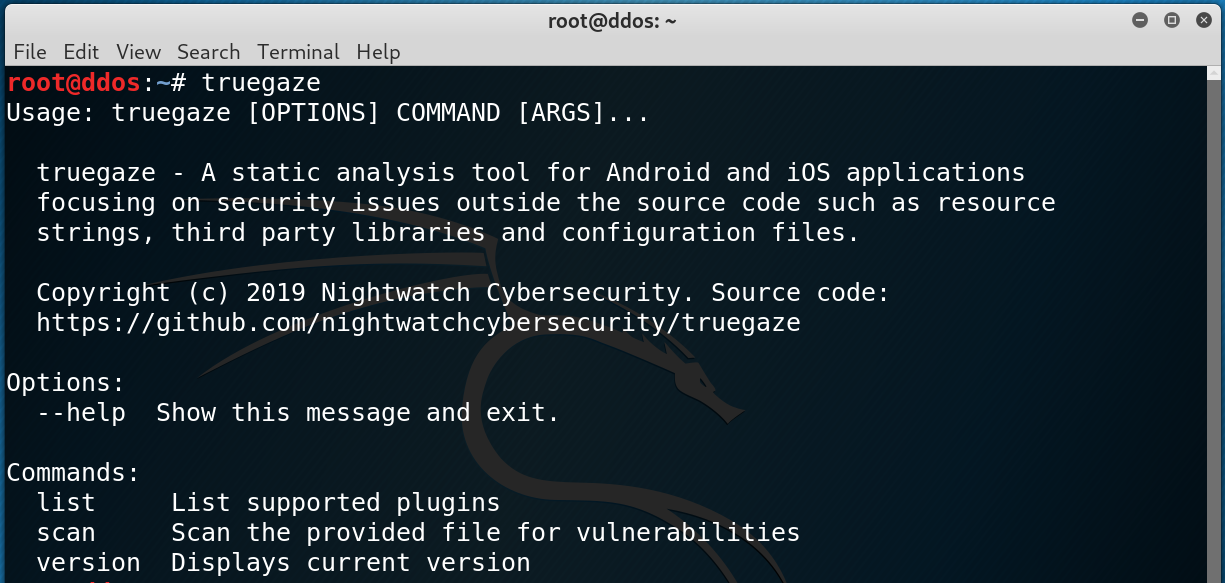
2.5KHack Toolstruegaze v0.1.5 releases: Static analysis tool for Android/iOS apps focusing on security issues
truegaze A static analysis tool for Android and iOS applications focusing on security issues outside the source code such as resource strings,...






