Search results for "Anonymity"
-

 1.4KNews
1.4KNewsCross-browser tracking vulnerability compromises user anonymity
The vulnerability affects top browsers including Chrome, Firefox, Safari, and even Tor. It is not unusual for a user to switch between...
-

 4.7KSurveillance
4.7KSurveillanceAbout Internet Anonymity, Our Life and Its Relativity
So, you have some reason to remain anonymous on the net. You open Google, type in something like: “Basics of Internet anonymity”...
-

 3.5KSecurity Tools
3.5KSecurity ToolsTails 4.0 – Live System to Preserve Your Privacy and Anonymity
Tails is a live system that aims to preserve your privacy and anonymity. It helps you to use the Internet anonymously...
-
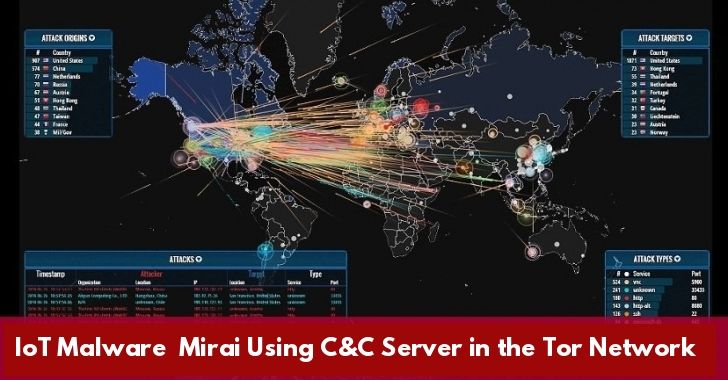
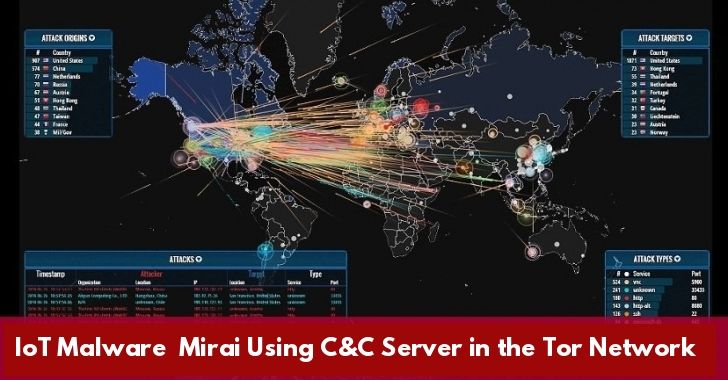 254Malware
254MalwareMost Dangerous IoT Malware Mirai Now Using C&C Server in the Tor Network For Anonymity
Researchers discovered new Mirai Malware samples with the updated functions, in which malware authors implemented its Command & Control server in the...
-

 286Data Security
286Data SecurityIs Flawless Anonymity Possible?
The condition of being anonymous is called anonymity – Let’s suppose you want to post the most anonymous comment on a social...
-

 257Anonymity
257AnonymityTop 4 Linux Operating Systems for Privacy & Anonymity – 2019
With the development of the Internet, personal information is becoming more and more transparent. For preventing the leak information, many security teams are...
-

 368Geek
368GeekLinux Releases: GNOME 3.30 ‘Almeria’ Desktop & Tails 3.9 Anonymity Distro Are Here
GNOME 3.30 GNOME is one of the best options when it comes to choosing a desktop environment for Linux. Many popular distros...
-

 212Hacked
212HackedRichard Stallman Proposes Ceasing Of Data Collection To Safeguard Privacy And Anonymity
The aftermath of Facebook CA scandal has attracted several comments and criticism from common people and prominent figures alike. Now Richard Stallman,...
-

 237Hacked
237HackedMIT’s ‘Veil’ Fixes Holes In Private Browsing Modes To Boost Anonymity
Web browsers’ private browsing mode is the first resolution taken by most users to protect their privacy online. But subconsciously they’re aware that...
-

 226Anonymity
226AnonymityWhonix – An Operating System Focused On Anonymity, Privacy and Security
Whonix is a free and open-source desktop operating system (OS) that is specifically designed for advanced security and privacy. Based on Tor,...
-

 215Geek
215GeekSopranica: Text And Call Using This Open Source Cellular Network For Complete Anonymity
Even without the revelations made by NSA whistleblower Edward Snowden and others, it was known to many that different governments across the...
-

 341Geek
341Geek10 Most Secure Linux Distros For Complete Privacy & Anonymity | 2017 Edition
Short Bytes: One of the most compelling reasons to use Linux is its ability to deliver a secure computing experience. There are...
-

 328Pentest Linux Distributions
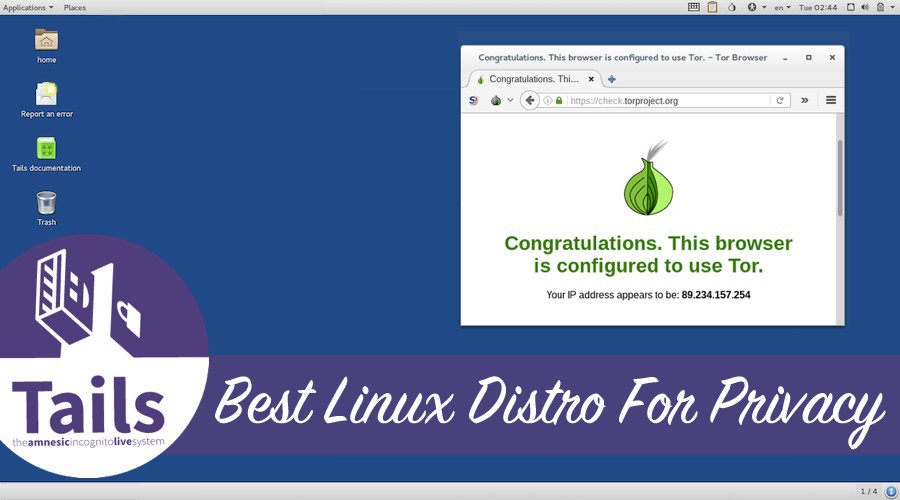
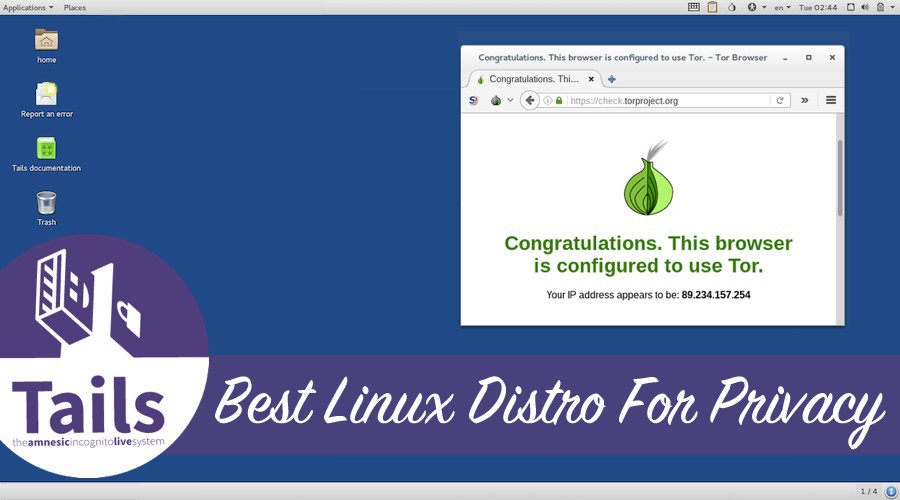
328Pentest Linux DistributionsTails 3.2 – Live System to Preserve Your Privacy and Anonymity
Tails is a live system that aims to preserve your privacy and anonymity. It helps you to use the Internet anonymously and...
-
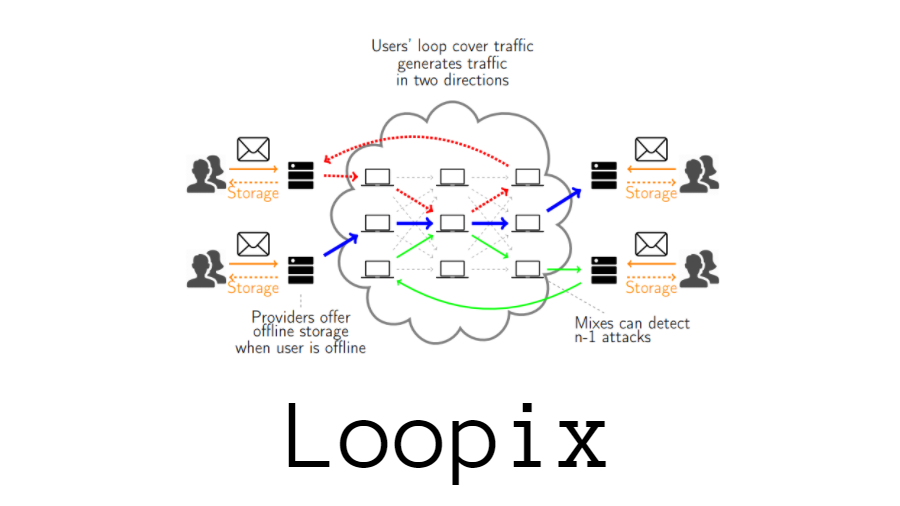
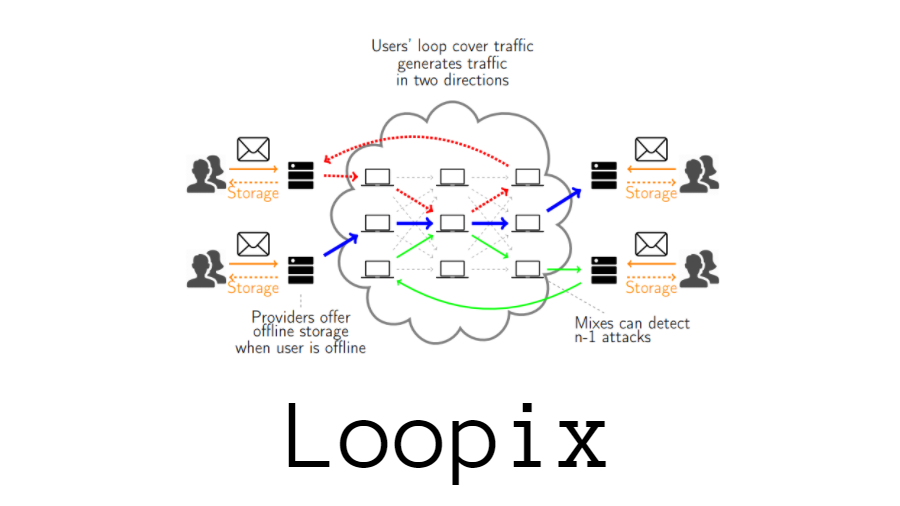 208Hacked
208HackedThe Loopix Anonymity System Can Be A Good Tor Alternative, Comparison Shows
Loopix is another name that adds to the list of anonymity networks like Tor. It is developed by the researchers at the University...
-
 219Data Security
219Data SecurityThe Loopix Anonymity System Wants to Be a More Secure Alternative to Tor
Loopix is a new anonymity network developed by a group of researchers from University College London (UCL) that comes with all the...
-
 290Hacked
290HackedYour Web History Can Be Traced Even After Anonymity, According To Researchers
Short Bytes: A team of German researchers shared that an individual’s secret web history and habit can be traced. Surprisingly, even after it goes...
-
 288Hacked
288HackedSandboxed Tor Browser 0.0.2 “Alpha” Is Here To Protect Your Anonymity
Short Bytes: Tor developers have created their own version of Sandboxed Tor Browser. At the moment, an early Alpha version of Sandboxed...
-

 213Data Security
213Data SecurityDNS traffic monitoring, a threat to Tor users’ anonymity
Tor Network Users May No Longer Enjoy Anonymity due to Exploitation of DNS Traffic Monitoring Karlstad University researchers in collaboration with KTH...
-

 230Hacked
230HackedRiffle: MIT Creates New Anonymity Network Which Is More Secure Than TOR
Short Bytes: Researchers at MIT and EPFL have come up with a new anonymity network that is said to be more secure...
-
 255Hacked
255HackedTails 2.4 Launched With TOR 6.0 — Best Linux Distro For Anonymity And Privacy
Short Bytes: Popular anonymous Linux Live distribution Tails is here with its version 2.4. This latest release of Debian-based operating system features...
-

 300Anonymity
300AnonymityHow To Setup VPN On Kali Linux For Anonymity
Virtual Private Networks (vpn) create an encrypted ‘tunnel’ between your computer and the host server, with the internet traffic going in and...






