Search results for "Bluetooth"
-

 3.0KVulnerabilities
3.0KVulnerabilitiesNew Bluetooth Flaw Let Hackers Take Over Android, Linux, macOS, and iOS Devices
A critical Bluetooth security flaw could be exploited by threat actors to take control of Android, Linux, macOS and iOS devices. Tracked...
-

 1.6KVulnerabilities
1.6KVulnerabilitiesCritical vulnerability in Bluetooth Low Energy (BLE) allows easily hacking Tesla cars, smart locks and millions of devices that use this Bluetooth technology
Specialists from the security firm NCC Group developed a tool capable of deploying relay attacks against Bluetooth Low Energy (BLE), which would...
-

 3.8KVulnerabilities
3.8KVulnerabilitiesDon’t buy this Fisher Price phone for kids; anyone can use its Bluetooth to spy on your family
Cybersecurity specialists report the appearance of a new toy with Bluetooth capabilities whose malicious use would allow threat actors to deploy complex...
-

 4.1KVulnerabilities
4.1KVulnerabilitiesDozens of critical vulnerabilities affecting Intel CPU and Bluetooth products; update ASAP
Intel issued 29 security alerts to correct some severe bios firmware flaws for Intel processors, as well as in its Bluetooth products,...
-

 2.7KMalware
2.7KMalwareNew Bluetooth Flaws Let Attackers Impersonate Legitimate Devices
Adversaries could exploit newly discovered security weaknesses in Bluetooth Core and Mesh Profile Specifications to masquerade as legitimate devices and carry out...
-

 5.1KMalware
5.1KMalwareNew Bluetooth Flaws Let Attackers Impersonate Legitimate Devices
Adversaries could exploit newly discovered security weaknesses in Bluetooth Core and Mesh Profile Specifications to masquerade as legitimate devices and carry out...
-
 4.4KVulnerabilities
4.4KVulnerabilitiesZero-click Linux Bluetooth vulnerability allows taking control remotely without even user clicking a link
After months of research and rumors, the technical details of BleedingTooth, a zero-click attack on the Linux Bluetooth subsystem that would have...
-

 1.9KInformation Gathering
1.9KInformation GatheringRadareEye – Scan Nearby devices [BLE, Bluetooth And Wifi]
A tool made for specially scanning nearby devices[BLE,Bluetooth & Wifi] and execute our given command on our system when the target...
-

 3.3KTutorials
3.3KTutorialsRevenge your neighbor’s party by jamming any Bluetooth speaker. Creating a Bluetooth jammer with just 9 commands without any special hardware
We’ve all dealt with annoying neighbors who keep listening to music at a high volume, even in the early morning and thanks...
-
 2.9KVulnerabilities
2.9KVulnerabilitiesHow to use headphones or Bluetooth to hack and take control of any Android device
A recent research published by vulnerability testing specialists from Purdue University details a new exploit that abuses some Android operating system smartphones...
-
 1.8KHack Tools
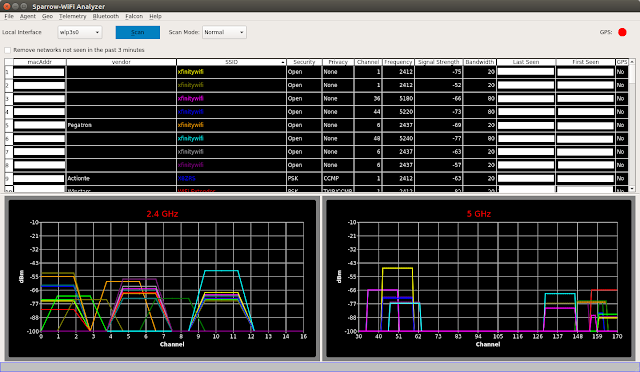
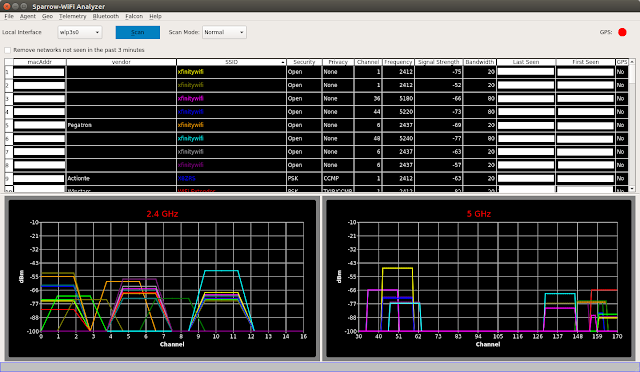
1.8KHack ToolsSparrow-Wifi – Next-Gen GUI-based WiFi And Bluetooth Analyzer For Linux
Sparrow-wifi has been built from the ground up to be the next generation 2.4 GHz and 5 GHz Wifi spectral awareness tool....
-

 389Vulnerabilities
389VulnerabilitiesTurn off your Bluetooth. Experts discover new Bluetooth KNOB vulnerability
A group of vulnerability testing researchers has revealed a new method to break Bluetooth’s encryption key negotiation protocol; the attack, dubbed ‘Key...
-

 414Vulnerabilities
414VulnerabilitiesNew Bluetooth vulnerability allows hacking iOS and Android devices
Wireless protocols are not exempt from cybersecurity risks. IT security audit specialists say that more than one billion Bluetooth-enabled devices (smartphones, IoT...
-

 232Vulnerabilities
232VulnerabilitiesNew Bluetooth Vulnerability Lets Attackers Spy On Encrypted Connections
Over a billion Bluetooth-enabled devices, including smartphones, laptops, smart IoT devices, and industrial devices, have been found vulnerable to a high severity...
-

 338News
338NewsBluetooth Flaw Allows Tracking Of Windows, iOS, macOS Devices But Android Is Safe
A recent flaw found in Bluetooth can be used to track Bluetooth devices, which mostly include phones, laptops and other devices by...
-
 227News
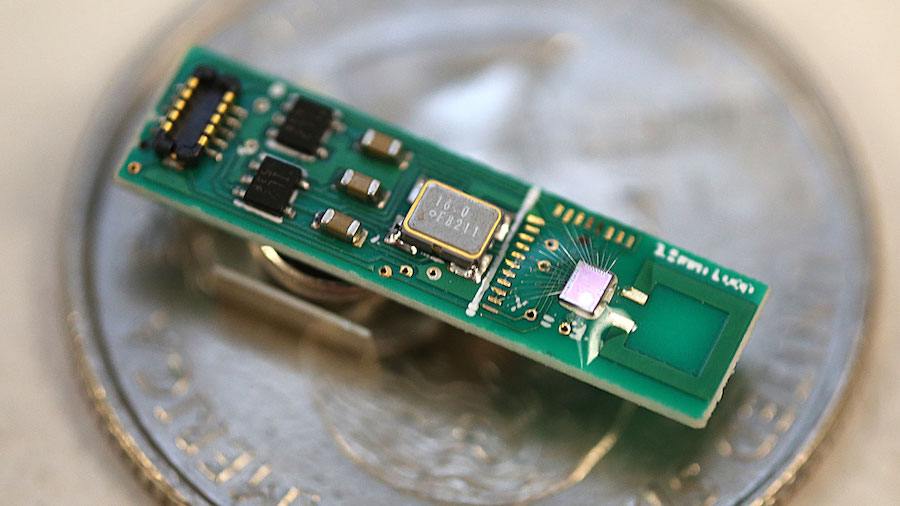
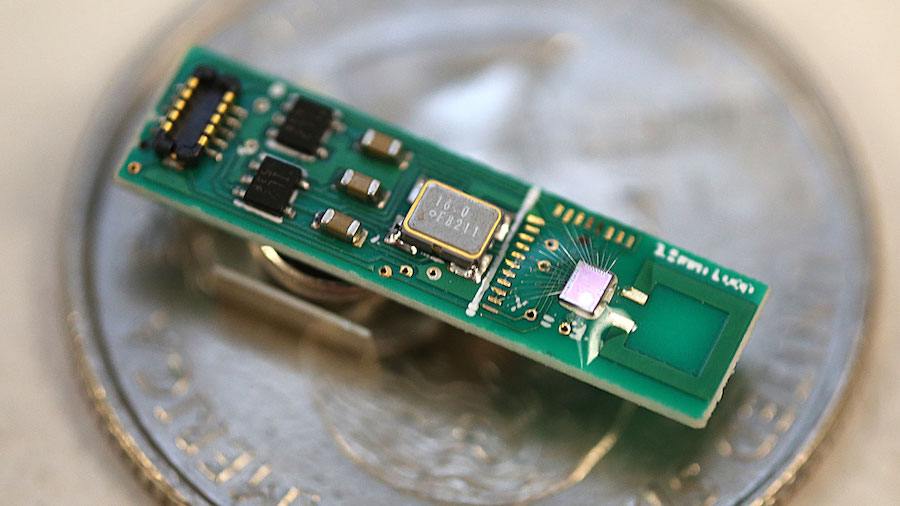
227NewsFirst Millimeter-sized Bluetooth Chip Invented To Send Low-Energy Data Packets
We are surrounded by Bluetooth radio signals and most of the devices that we see around — smartphones, wireless computer networks, and wireless...
-

 297Reviews
297ReviewsMi Sports Bluetooth Earphones Basic Review: Portability Meets Decent Performance
Apart from offering the amazingly-priced smartphones with an amazingly-prepared spec sheet, Xiaomi also competes in the audio accessory arena. Among the various...
-
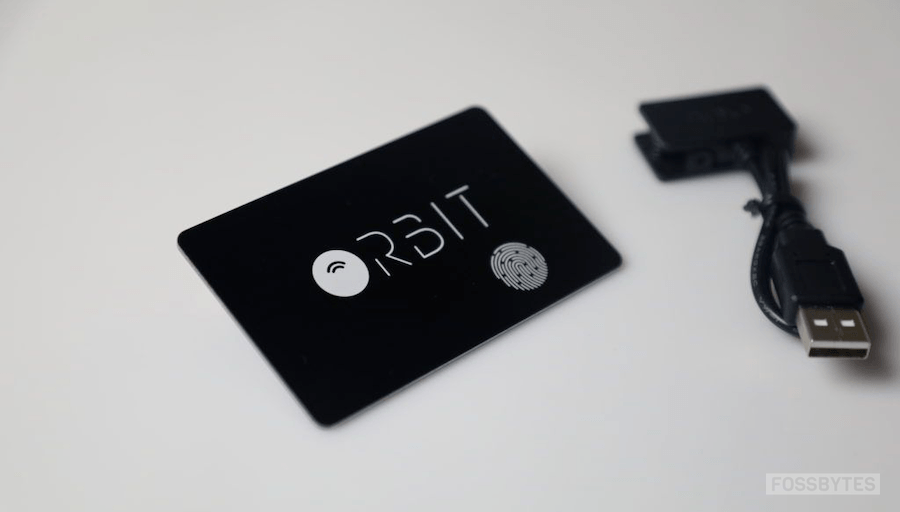
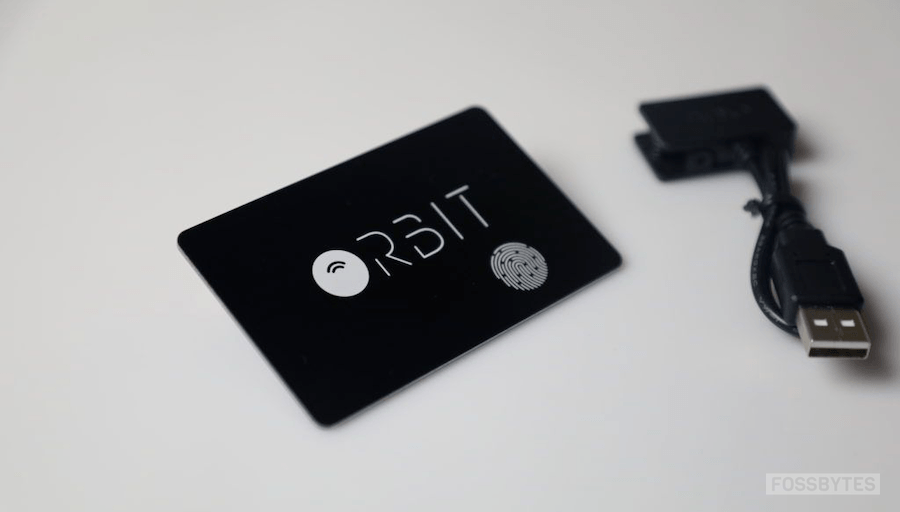 224Reviews
224ReviewsNever Lose Your Wallet Again With Orbit Bluetooth Tracker
For someone like me who frequently taps the pocket to reassure that I still have my wallet, a Bluetooth tracker is a...
-

 235News
235NewsIntel Discovers And Publishes New Bluetooth Vulnerability
Turns out, Intel has now discovered and published a new Bluetooth vulnerability, which could help intercept and manipulate transmissions between two compatible...
-

 307Data Security
307Data SecurityBluetooth hack affecting millions of devices from several vendors
Another Bluetooth attack technique has been disclosed Specialists in enterprise data protection services have found a highly critical vulnerability that affects some Bluetooth implementations...
-

 322Data Security
322Data SecurityUpdate your devices: New Bluetooth flaw lets attackers monitor traffic
The Bluetooth flaw also opens door to a man-in-the-middle attack. The IT security researchers at Israel Institute of Technology have discovered a critical security vulnerability in...






