Search results for "Brute Force"
-

 618Tutorials
618TutorialsHow to do local privilege escalation attacks on Windows to brute force the local administrator account?
Privilege escalation attacks pose a severe cyber security risk to all kinds of systems in public and private organizations. In these attacks,...
-

 2.6KNews
2.6KNewsT-Mobile hacker used brute force attack to steal customers’ data
A 21-year-old US citizen named John Binns has claimed responsibility for the T-Mobile data breach and labeled the carrier’s “security is awful.”...
-

 3.0KMalware
3.0KMalwareRussian APT Hackers Launched A Mass Global Brute Force Attack to Hack Enterprise & Cloud Networks
Recently, in a joint warning, the cybersecurity agencies of the US and UK have released a set of large-scale brute-force attacks escorted...
-

 3.2KWeb Application Security
3.2KWeb Application SecurityWPCracker – WordPress User Enumeration And Login Brute Force Tool
WordPress user enumeration and login Brute Force tool for Windows and Linux With the Brute Force tool, you can control how...
-
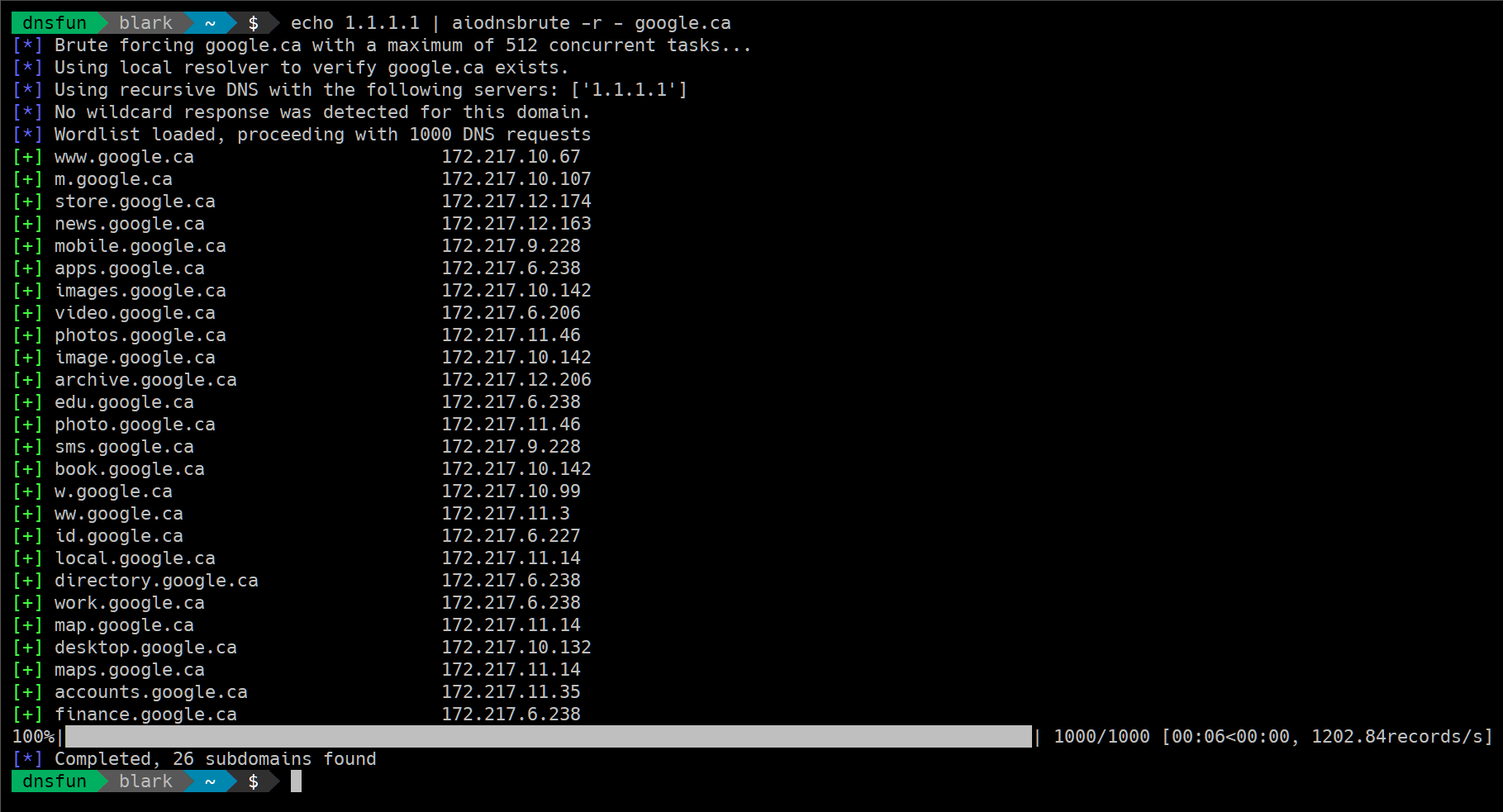
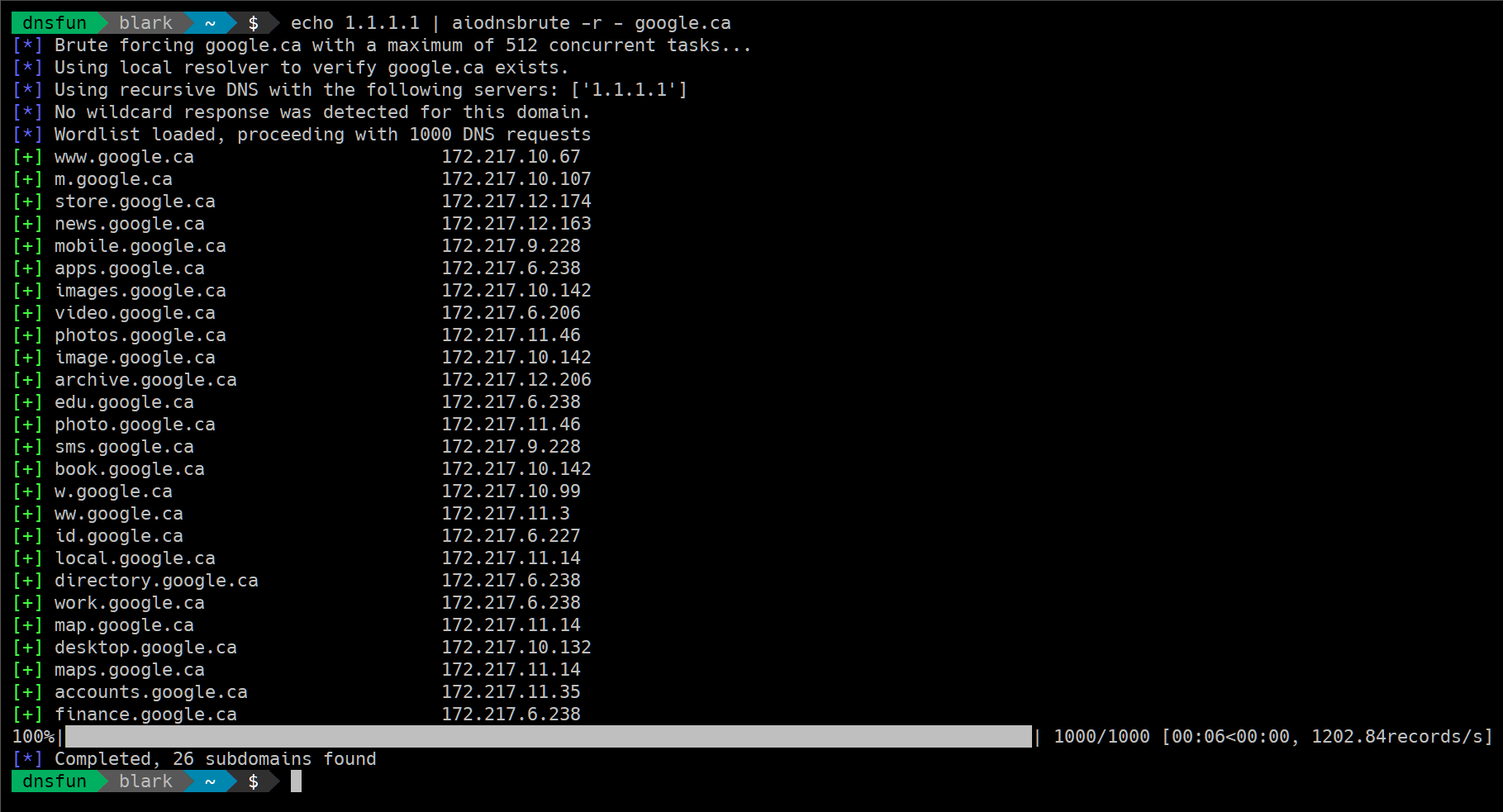 3.5KHackers Repository
3.5KHackers RepositoryAsync DNS Brute: DNS asynchronous brute force utility
Async DNS Brute A Python 3.5+ tool that uses asyncio to brute force domain names asynchronously. Speed It’s fast. Benchmarks on small...
-

 468Exploitation Tools
468Exploitation ToolsXMLRPC Bruteforcer – An XMLRPC Brute Forcer Targeting WordPress
An XMLRPC brute forcer targeting WordPress written in Python 3. In the context of xmlrpc brute forcing, its faster than Hydra...
-
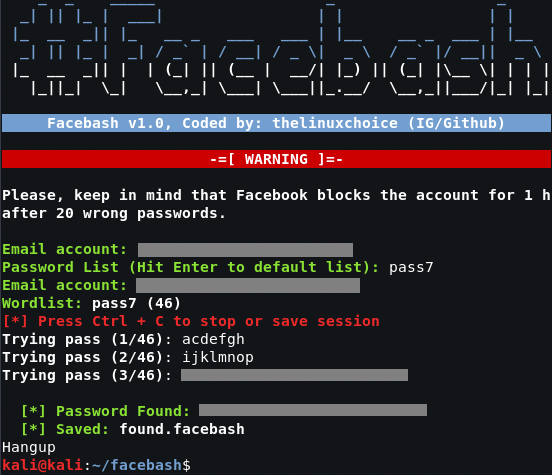
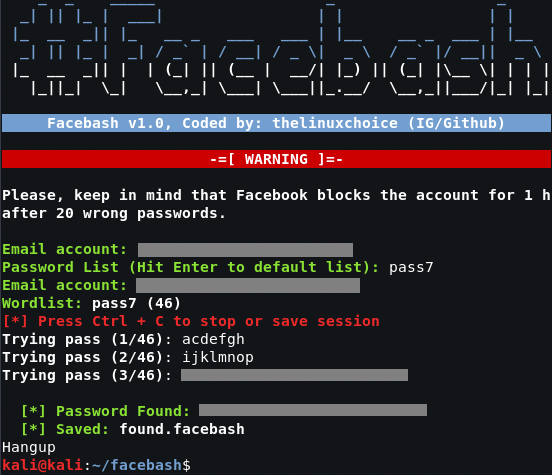 662Bruteforcing
662BruteforcingFacebash – Facebook Brute Forcer in shellscript using TOR
Facebook Brute Forcer in shellscript using TOR WARNING: Facebook blocks account for 1 hour after 20 wrong passwords, so this script can...
-

 3.4KRansomware
3.4KRansomwareGetCrypt Ransomware Encrypts Files, Brute Forces Credentials
Here’s a new ransomware that not only encrypts files and programs on a computer, but attempts to brute force credentials as well....
-

 274Password Attacks
274Password AttacksBruteX v1.9 – Automatically Brute Force All Services Running On A Target
Automatically brute force all services running on a target Open ports Usernames Passwords INSTALL: ./install.sh USAGE: brutex target <port> DOCKER: docker build...
-
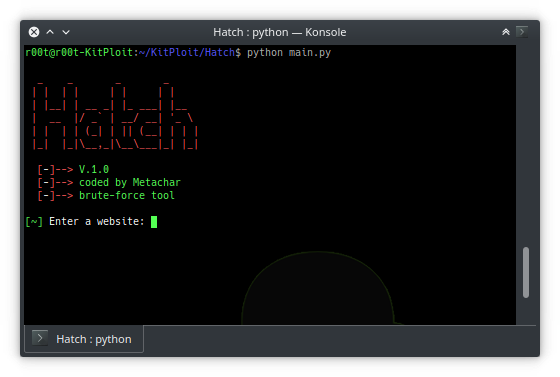
 371Bruteforcing
371BruteforcingHatch – Tool To Brute Force Most Websites
Hatch is a brute force tool that is used to brute force most websites Installation Instructions git clone https://github.com/MetaChar/Hatch python2 main.py Requirements...
-

 510Password Attacks
510Password AttacksW3Brute – Automatic Web Application Brute Force Attack Tool
w3brute is an open source penetration testing tool that automates attacks directly to the website’s login page. w3brute is also supported for...
-
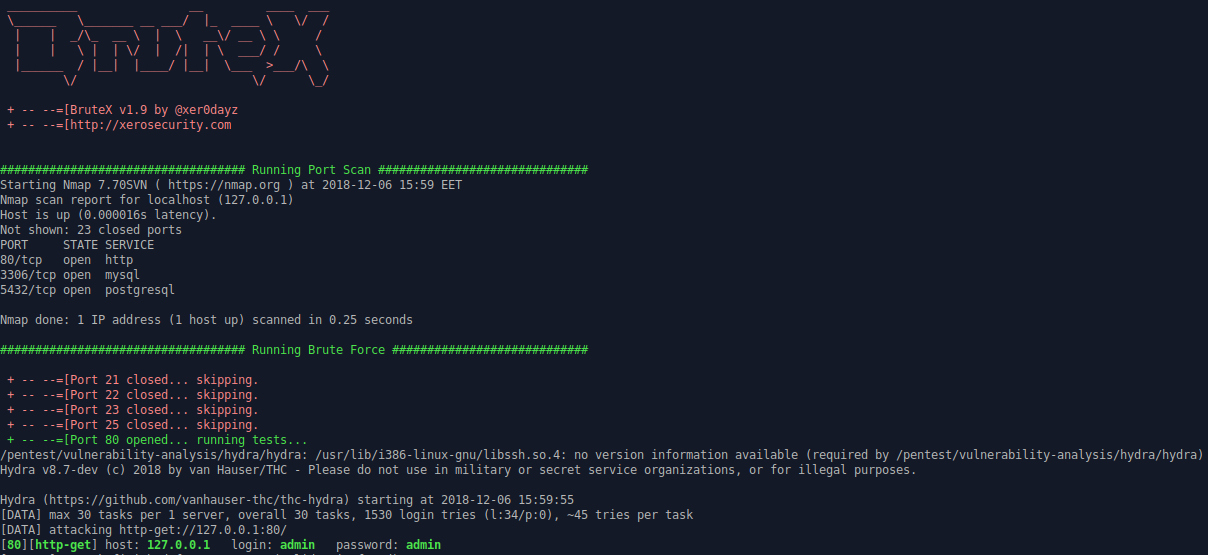
 507Hacking Tools
507Hacking ToolsBrutex – Open Source Tool for Brute Force Automation
Brutex is a shell based open source tool to make your work faster. It combines the power of Nmap, Hydra and DNSenum....
-

 430Incidents
430IncidentsA very simple hack evades iOS password entry limit, possibilities of brute force attacks
A researcher specialized in information security training recently discovered an Apple operating system failure that allows anyone with a Lightning cable the...
-

 356Hacked
356HackediPhone Brute Force Hack: Researcher Finds How To Bypass iPhone’s Passcode Limit
Over the past years, Apple has been playing cat and mouse with the security researchers and hackers who keep trying to develop...
-

 310Data Security
310Data SecurityA hacker figured out how to brute force iPhone passcodes
The attack allows any would-be-hacker to run as many passcodes as they want, without destroying the data. A security researcher has figured...
-
 308Data Security
308Data SecurityCountering a Brute Force Attack
Detecting the attack Of course, before we fight a brute force attack, we must first detect it. Specialists from the International Institute...
-
 260Data Security
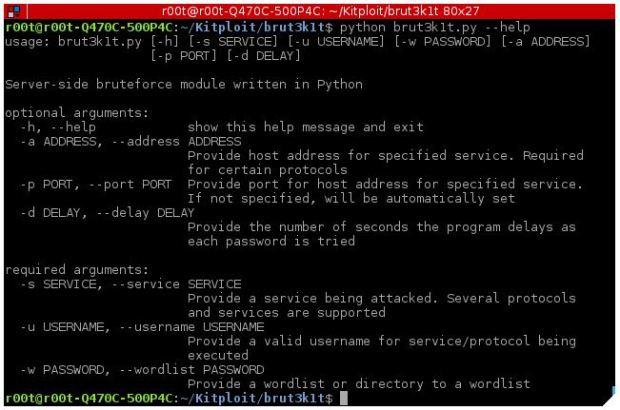
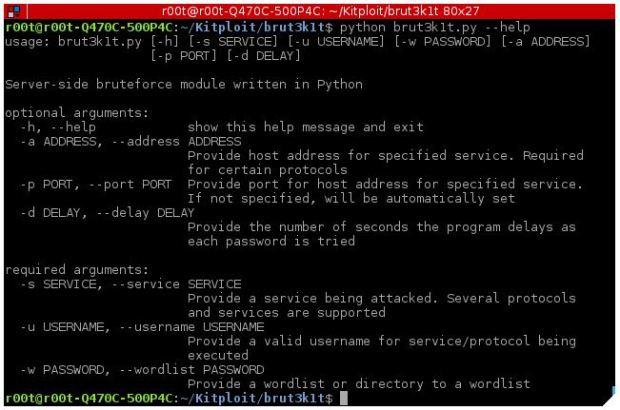
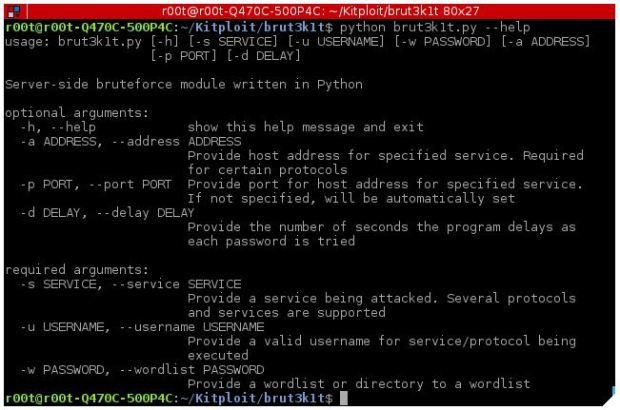
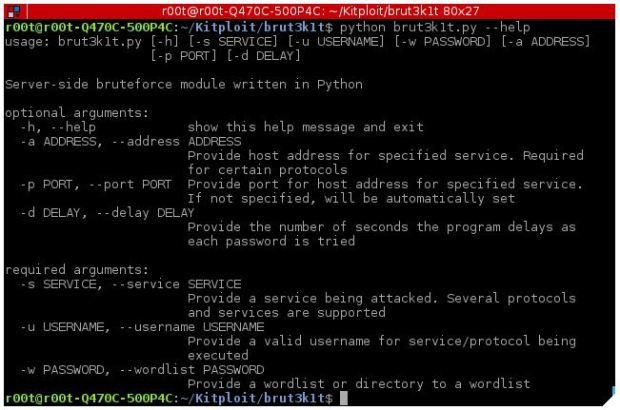
260Data SecurityTool to perform brute force attacks on ssh, smtp, facebook and Instagram- brut3k1t
As an introduction, brut3k1t is a bruteforce module on the server side that supports dictionary attacks for various protocols, information security experts say. Some...
-

 404Incidents
404IncidentsNorthern Irish Parliament Hit by Brute Force Attack
The email service at the Northern Ireland Parliament, Stormont has been hit by a brute force attack allowing unknown attackers to access...
-
 206Incidents
206IncidentsCrowbar: A tool to perform brute force attacks on different services
Crowbar is a tool that is specifically developed to perform brute force attacks during pentesting tests. This tool applies brute force attacks...
-
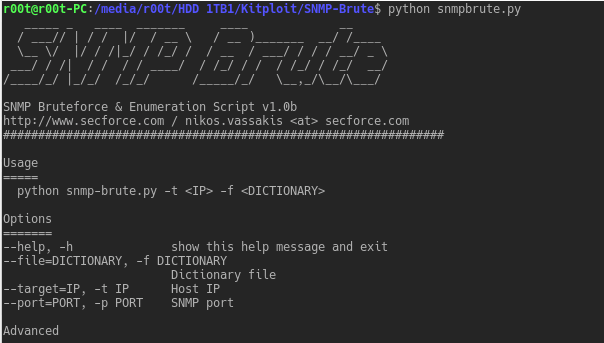
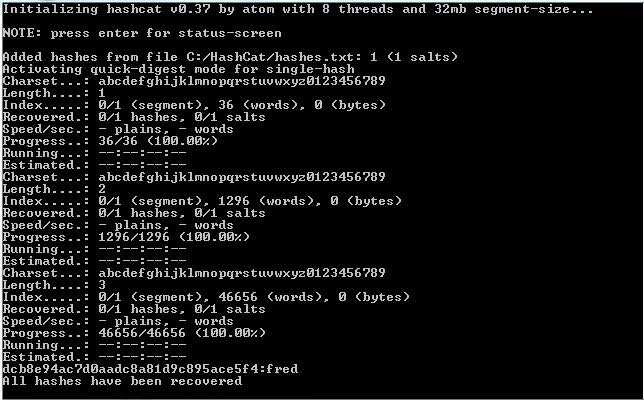
 302Password Attacks
302Password AttacksSNMP-Brute – Fast SNMP brute force, enumeration, CISCO config downloader and password cracking script
SNMP brute force, enumeration, CISCO config downloader and password cracking script. Listens for any responses to the brute force community strings, effectively...
-
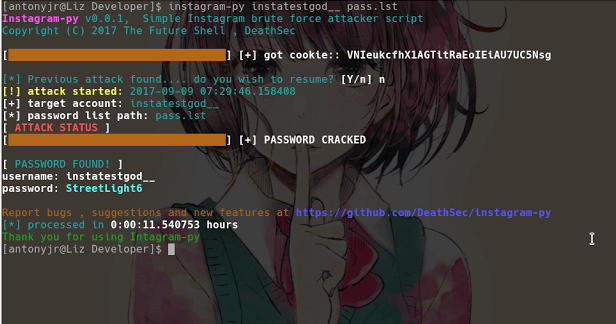
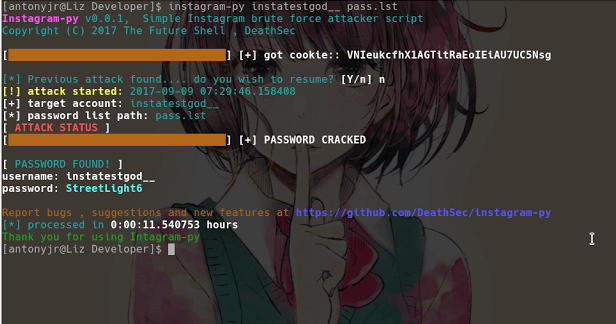 242Exploitation Tools
242Exploitation ToolsInstagram-Py – Simple Instagram Brute Force Script
Instagram-Py is a simple python script to perform basic brute force attack against Instagram , this script can bypass login limiting on...






