Search results for "Certificates"
-
 1.1KCyber Attack
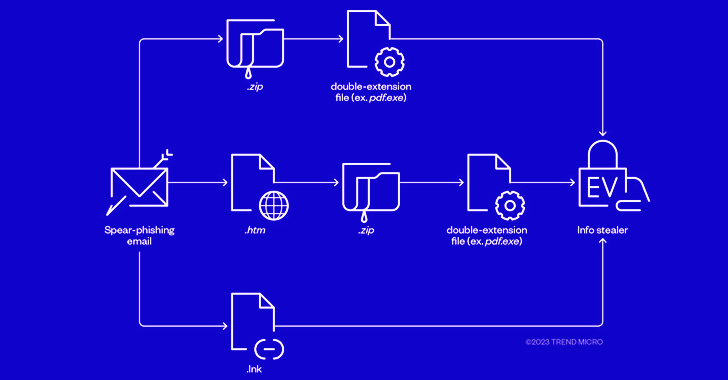
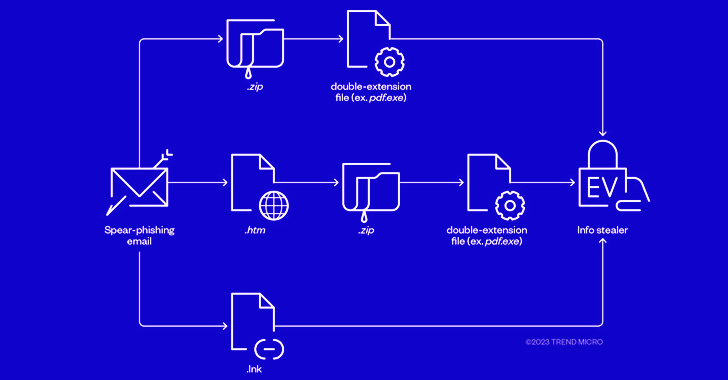
1.1KCyber AttackCybercriminals Combine Phishing and EV Certificates to Deliver Ransomware Payloads
The threat actors behind RedLine and Vidar information stealers have been observed pivoting to ransomware through phishing campaigns that spread initial payloads...
-

 3.6KData Breach
3.6KData BreachGitHub Breach – Hackers Stole Code Signing Certificates From Repositories
GitHub announced that it suffered a security breach in which unauthorized individuals obtained access to specific development and release planning repositories and...
-
 3.1KIncidents
3.1KIncidentsGitHub hacked again, GitHub Desktop and Atom repositories certificates stolen
GitHub discovered illegal access to a collection of repositories on December 7, 2022. These repositories were used in the design and development...
-
 986Data Security
986Data SecurityBad news! The platform certificates of many phone manufactures have been hacked. These are used to sign trusted apps on Android phones. Now these certificates are being used to certify malicious Android applications
Platform certificates, also known as platform keys, are used by OEM Android device makers to certify the core ROM images of their...
-

 2.8KIncidents
2.8KIncidentsCritical vulnerability in Java allows forgery of certificates, signatures, WebAuthn messages and evade authentication mechanisms: Update immediately
Some versions of Java are affected by a critical vulnerability in the Elliptic Curve Digital Signature Algorithm (ECDSA) signature validation that would...
-
 1.5KCyber Attack
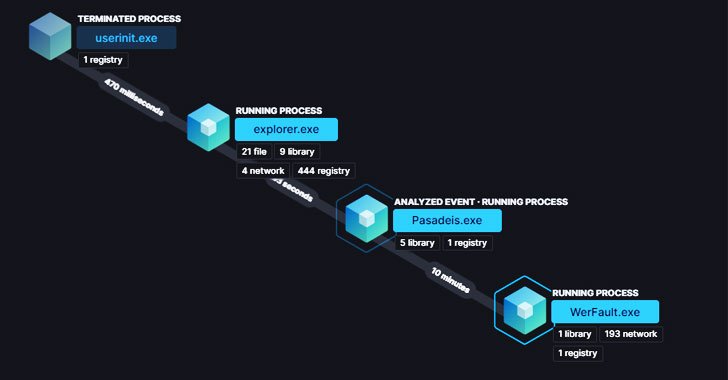
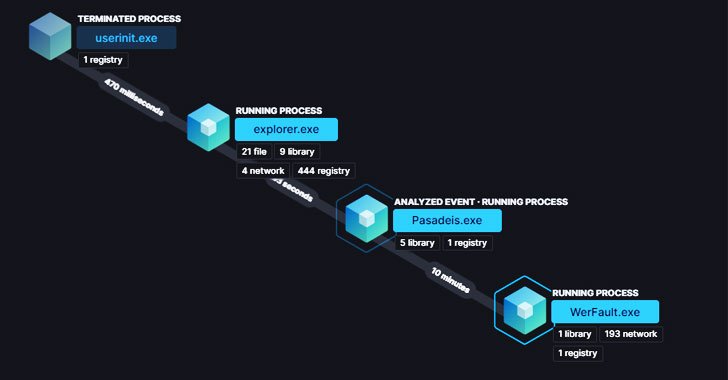
1.5KCyber AttackNew BLISTER Malware Using Code Signing Certificates to Evade Detection
Cybersecurity researchers have disclosed details of an evasive malware campaign that makes use of valid code signing certificates to sneak past security...
-

 4.5KIncidents
4.5KIncidentsHackers encrypt the vaccination certificates of the Brazilian population with ransomware
A hacking group calling itself Lapsus$ Group claims to have encrypted with ransomware and stolen some 50 TB of information from Brazil’s...
-

 5.2KIncidents
5.2KIncidentsAdministrators of 35 Telegram channels arrested for selling fake COVID-19 vaccination certificates
Italian authorities, in collaboration with cybersecurity specialists, reported the dismantling of a cybercriminal group dedicated to a scam related to the preparation...
-

 1.3KIncidents
1.3KIncidentsBooming business in India: Fake death and birth certificates. Hackers get into government websites to generate 800 fake birth and death certificates
Authorities in the Indian state of Haryana have announced the arrest of two individuals accused of falsifying hundreds of birth and death...
-

 2.6KIncidents
2.6KIncidentsHitler, Mickey Mouse and SpongeBob got COVID-19 vaccination? Valid vaccination certificates generated by hacking the European vaccination passport system
Law enforcement agencies in the European Union are investigating the theft of a private key used by health authorities to issue and...
-

 2.4KData Security
2.4KData Security5 WordPress Security Solutions with Free SSL Certificates
Security vulnerabilities are inevitable but one can avoid them by securing applications. In this article, we are listing 5 popular WordPress security...
-

 2.7KVulnerabilities
2.7KVulnerabilitiesResearchers discover technique that allows bypassing Let’s Encrypt domain validation and allows fake SSL certificates
Researcher Haya Shulman of the Fraunhofer Institute for Secure Information Technology in Germany reported the discovery of a critical vulnerability in Let’s...
-

 1.4KData Security
1.4KData SecurityIndian city birth and death registration website hacked; 1.4 million fake certificates were issued
During an investigation related to the issuance of a fake death certificate, local authorities in India discovered that the official platforms of...
-

 281Privacy
281PrivacyTarget Big retailers Over 100,000 fake domains with fraudulent TLS certificates
Venafi has discovered over 100,000 typosquatted domains with legitimate TLS certificates that appear to be aimed at large traders, a company that...
-
 364Data Breach
364Data BreachImperva Hacked – Email addresses, API keys & SSL certificates of WAF Customers Exposed
Imperva, one of the leading cyber-security firm disclosed a data breach that impacts the customers’ data of Cloud Web Application Firewall (WAF)....
-

 352Data Security
352Data SecurityWill other countries follow Kazakhstan in forcing users to install certificates for HTTPS interception?
Experts from multiple digital forensics firms report that the Kazakhstan government has begun intercepting all HTTPS traffic detected within its territory. Internet...
-

 300News
300NewsFederal Websites Shutdown Due to Expired Security certificates
The public in the United States will no longer be able to access several Federal websites due to their expired HTTPS certificates....
-

 377News
377NewsMisconfigured Tor sites using SSL certificates exposing public IP addresses
Tor is a browser known to keep the IP addresses of its users private and confidential due to which users can surf...
-

 390Incidents
390IncidentsStolen D-Link certificates used to sign password stealing malware
It wasn’t the IP camera software that we thought Recently hackers stole code signature certificates from D-Link and other Taiwan-based manufacturer of...
-

 449Malware
449MalwareCertificates stolen from Taiwanese tech‑companies misused in Plead malware campaign
D-Link and Changing Information Technologies code-signing certificates stolen and abused by highly skilled cyberespionage group focused on East Asia, particularly Taiwan
-
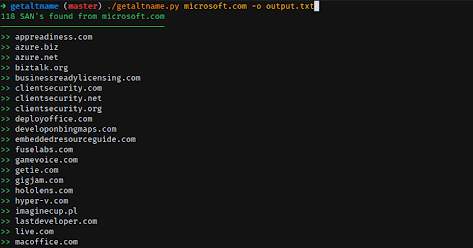
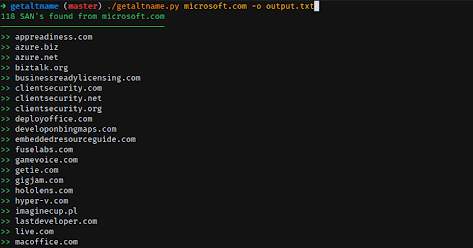 252Information Gathering
252Information GatheringGetAltName – Get Subject Alt Name From SSL Certificates
GetAltName it’s a little script that can extract Subject Alt Names for SSL Certificates directly from HTTPS web sites which can provide...






