Search results for "Cloud"
-

 1.0KVulnerabilities
1.0KVulnerabilitiesAndroxGh0st Malware Targets Laravel Apps to Steal Cloud Credentials
Cybersecurity researchers have shed light on a tool referred to as AndroxGh0st that’s used to target Laravel applications and steal sensitive data....
-

 3.6KData Security
3.6KData SecurityHack-Proof Your Cloud: The Step-by-Step Continuous Threat Exposure Management CTEM Strategy for AWS & AZURE
Continuous Threat Exposure Management (CTEM) is an evolving cybersecurity practice focused on identifying, assessing, prioritizing, and addressing security weaknesses and vulnerabilities in...
-
 4.8KCyber Attack
4.8KCyber AttackBanking Trojans Target Latin America and Europe Through Google Cloud Run
Cybersecurity researchers are warning about a spike in email phishing campaigns that are weaponizing the Google Cloud Run service to deliver various...
-

 1.9KMalware
1.9KMalwareCloudzy Elevates Cybersecurity: Integrating Insights from Recorded Future to Revolutionize Cloud Security
Cloudzy, a prominent cloud infrastructure provider, proudly announces a significant enhancement in its cybersecurity landscape. This breakthrough has been achieved through a...
-

 2.5KData Breach
2.5KData BreachCloudflare Breach: Nation-State Hackers Access Source Code and Internal Docs
Cloudflare has revealed that it was the target of a likely nation-state attack in which the threat actor leveraged stolen credentials to...
-
 2.2KData Breach
2.2KData Breach29-Year-Old Ukrainian Cryptojacking Kingpin Arrested for Exploiting Cloud Services
A 29-year-old Ukrainian national has been arrested in connection with running a “sophisticated cryptojacking scheme,” netting them over $2 million (€1.8 million)...
-

 2.2KLeaks
2.2KLeaksHow To Access Your Photos On iCloud
iCloud can be an easy and secure way to back up photos and videos, but accessing those files across devices may prove...
-
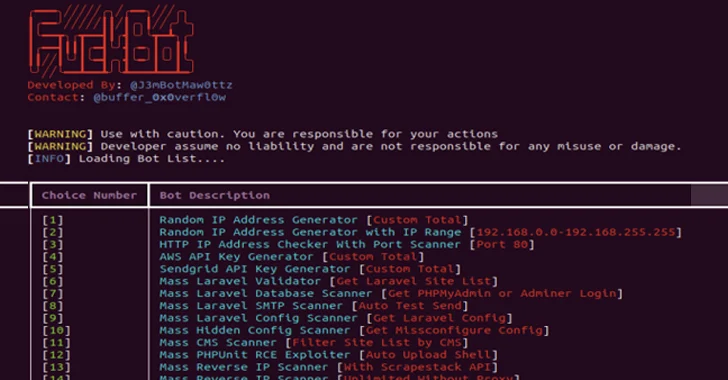
 525Malware
525MalwareNew Python-based FBot Hacking Toolkit Aims at Cloud and SaaS Platforms
A new Python-based hacking tool called FBot has been uncovered targeting web servers, cloud services, content management systems (CMS), and SaaS platforms...
-

 3.2KVulnerabilities
3.2KVulnerabilitiesGoogle Cloud Resolves Privilege Escalation Flaw Impacting Kubernetes Service
Google Cloud has addressed a medium-severity security flaw in its platform that could be abused by an attacker who already has access...
-
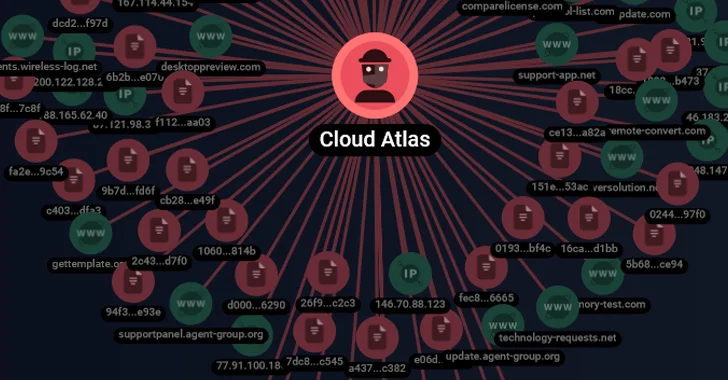
 834Malware
834MalwareCloud Atlas’ Spear-Phishing Attacks Target Russian Agro and Research Companies
The threat actor referred to as Cloud Atlas has been linked to a set of spear-phishing attacks on Russian enterprises. Targets included...
-

 2.3KVulnerabilities
2.3KVulnerabilitiesWarning: 3 Critical Vulnerabilities Expose ownCloud Users to Data Breaches
The maintainers of the open-source file-sharing software ownCloud have warned of three critical security flaws that could be exploited to disclose sensitive...
-

 3.1KVulnerabilities
3.1KVulnerabilitiesDiscover 2023’s Cloud Security Strategies in Our Upcoming Webinar – Secure Your Spot
In 2023, the cloud isn’t just a technology—it’s a battleground. Zenbleed, Kubernetes attacks, and sophisticated APTs are just the tip of the...
-

 1.7KData Security
1.7KData SecurityYour Google Cloud Security Might Be at Risk. Hacking GCP via Google Workspace flaw
In a startling revelation, Bitdefender, a leading cybersecurity firm, has disclosed a series of sophisticated attack methods that could significantly impact users...
-
 342Vulnerabilities
342VulnerabilitiesUrgent: VMware Warns of Unpatched Critical Cloud Director Vulnerability
VMware is warning of a critical and unpatched security flaw in Cloud Director that could be exploited by a malicious actor to...
-
 208Data Security
208Data SecurityAzure CLI stores credentials in plaintext in logs. A easy technique to hack cloud environments
CVE-2023-36052 is a critical security vulnerability in the Azure Command-Line Interface (CLI), a tool for managing Azure resources. This vulnerability, reported by...
-

 4.4KData Security
4.4KData SecurityHackers’ new favorite: CVE-2023-4911 targeting Debian, Ubuntu and Fedrora servers in the Cloud
CVE-2023-4911 is a serious security vulnerability within the GNU C Library (glibc), specifically in the dynamic loader ld.so, associated with the processing...
-

 2.2KData Breach
2.2KData BreachKinsing Actors Exploiting Recent Linux Flaw to Breach Cloud Environments
The threat actors linked to Kinsing have been observed attempting to exploit the recently disclosed Linux privilege escalation flaw called Looney Tunables...
-
 4.1KVulnerabilities
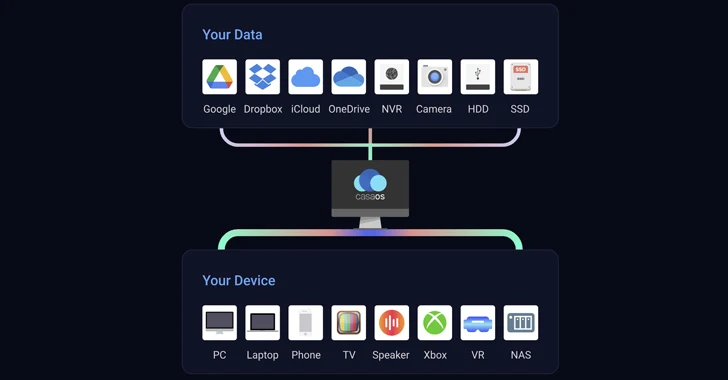
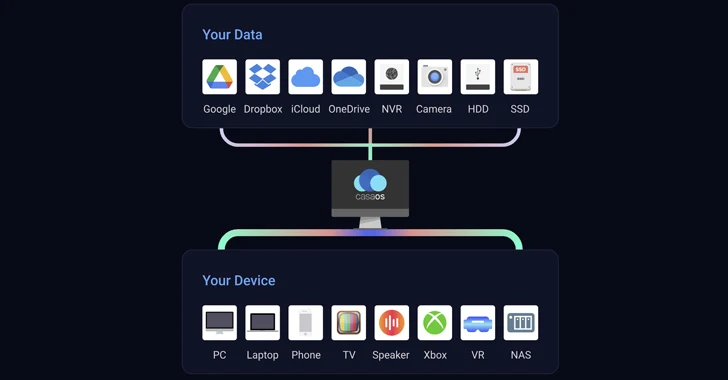
4.1KVulnerabilitiesCritical Vulnerabilities Uncovered in Open Source CasaOS Cloud Software
Two critical security flaws discovered in the open-source CasaOS personal cloud software could be successfully exploited by attackers to achieve arbitrary code...
-

 2.5KCyber Attack
2.5KCyber AttackLUCR-3: Scattered Spider Getting SaaS-y in the Cloud
LUCR-3 overlaps with groups such as Scattered Spider, Oktapus, UNC3944, and STORM-0875 and is a financially motivated attacker that leverages the Identity...
-
 3.7KTutorials
3.7KTutorialsAzure cloud security tutorial series – Chapter 4 [Establish VNet Peering]
Objective In the last chapter we saw on how to add resource to a VNet now in this chapter we will see...
-
 216Tutorials
216TutorialsAzure cloud security tutorial series – Chapter 3 [Add resource to VNet]
Overview In the last chapter (Azure cloud security tutorial series – Chapter 2 [Virtual Network]) we saw on how to create VNet...






