Search results for "Cyber"
-

 1.5KMalware
1.5KMalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
The recently uncovered cyber espionage campaign targeting perimeter network devices from several vendors, including Cisco, may have been the work of China-linked...
-

 2.8KData Breach
2.8KData BreachHow to Make Your Employees Your First Line of Cyber Defense
There’s a natural human desire to avoid threatening scenarios. The irony, of course, is if you hope to attain any semblance of...
-

 3.1KMalware
3.1KMalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
Cybersecurity researchers have discovered a targeted operation against Ukraine that has been found leveraging a nearly seven-year-old flaw in Microsoft Office to...
-

 1.2KMalware
1.2KMalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
The U.S. Treasury Department’s Office of Foreign Assets Control (OFAC) on Monday sanctioned two firms and four individuals for their involvement in...
-

 1.4KData Breach
1.4KData BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
Cybersecurity breaches can be devastating for both individuals and businesses alike. While many people tend to focus on understanding how and why...
-

 1.4KVulnerabilities
1.4KVulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
Between crossovers – Do threat actors play dirty or desperate? In our dataset of over 11,000 victim organizations that have experienced a...
-

 889Malware
889MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
Microsoft has revealed that North Korea-linked state-sponsored cyber actors have begun to use artificial intelligence (AI) to make their operations more effective...
-

 1.2KMalware
1.2KMalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
The infamous cybercrime syndicate known as FIN7 has been linked to a spear-phishing campaign targeting the U.S. automotive industry to deliver a...
-

 2.9KCyber Attack
2.9KCyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
The U.S. Treasury Department’s Office of Foreign Assets Control (OFAC) on Friday announced sanctions against an official associated with Hamas for his...
-

 3.9KMalware
3.9KMalwareCybercriminals Targeting Latin America with Sophisticated Phishing Scheme
A new phishing campaign has set its eyes on the Latin American region to deliver malicious payloads to Windows systems. “The phishing...
-

 791Vulnerabilities
791VulnerabilitiesConsiderations for Operational Technology Cybersecurity
Operational Technology (OT) refers to the hardware and software used to change, monitor, or control the enterprise’s physical devices, processes, and events....
-

 3.9KVulnerabilities
3.9KVulnerabilitiesU.S. Cyber Safety Board Slams Microsoft Over Breach by China-Based Hackers
The U.S. Cyber Safety Review Board (CSRB) has criticized Microsoft for a series of security lapses that led to the breach of...
-
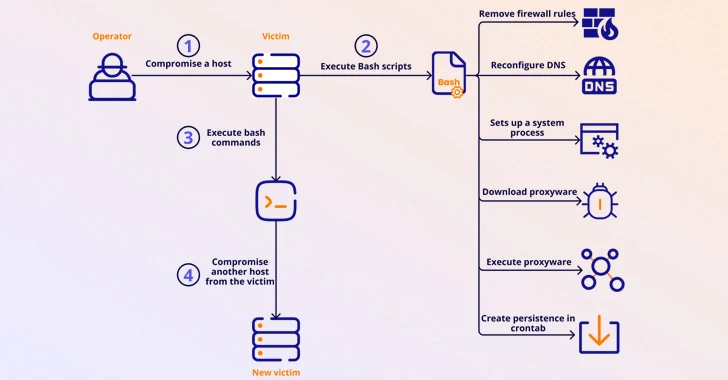
 503Malware
503MalwareMalicious Apps Caught Secretly Turning Android Phones into Proxies for Cybercriminals
Several malicious Android apps that turn mobile devices running the operating system into residential proxies (RESIPs) for other threat actors have been...
-

 2.2KVulnerabilities
2.2KVulnerabilitiesLinux Version of DinodasRAT Spotted in Cyber Attacks Across Several Countries
A Linux version of a multi-platform backdoor called DinodasRAT has been detected in the wild targeting China, Taiwan, Turkey, and Uzbekistan, new...
-

 1.7KMalware
1.7KMalwareFinland Blames Chinese Hacking Group APT31 for Parliament Cyber Attack
The Police of Finland (aka Poliisi) has formally accused a Chinese nation-state actor tracked as APT31 for orchestrating a cyber attack targeting...
-

 2.2KVulnerabilities
2.2KVulnerabilitiesTwo Chinese APT Groups Ramp Up Cyber Espionage Against ASEAN Countries
Two China-linked advanced persistent threat (APT) groups have been observed targeting entities and member countries affiliated with the Association of Southeast Asian...
-
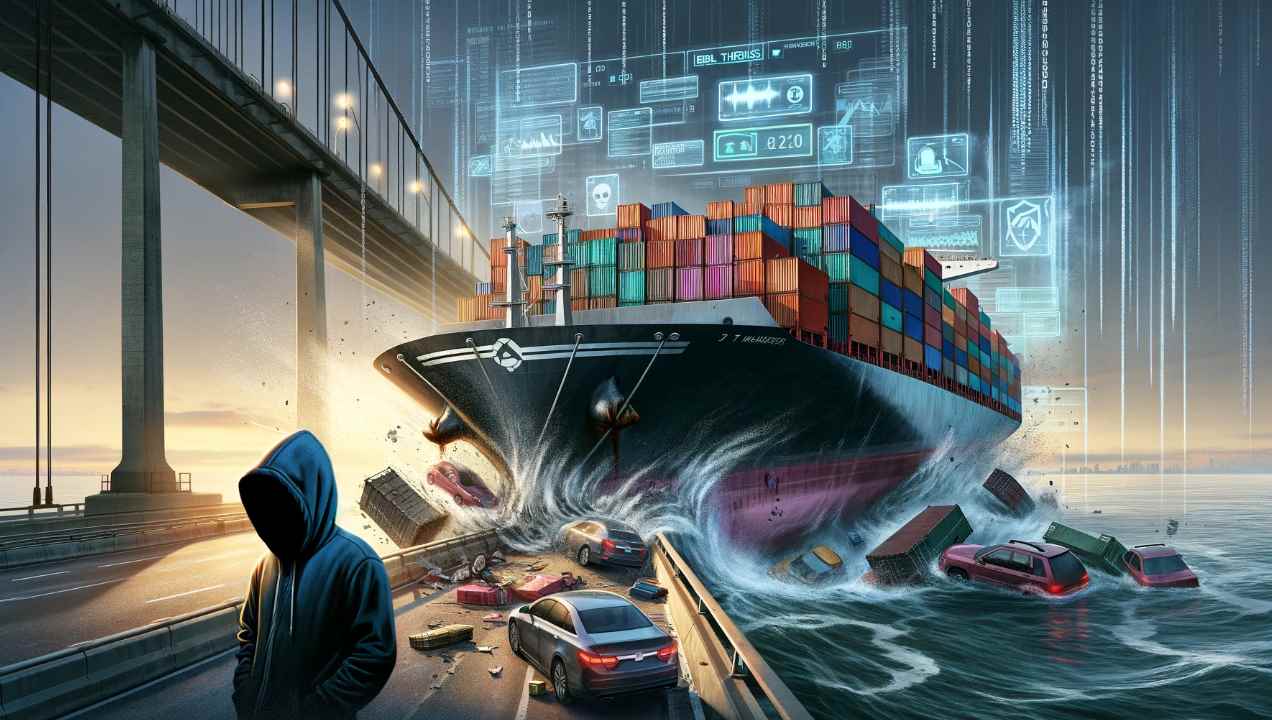
 4.5KData Security
4.5KData SecuritySocial Media Conspiracy Theory: Was the Baltimore Bridge Collision a Result of Cyber Attack?
On an unexpected Tuesday, the collision of a container ship with the Francis Scott Key Bridge in Baltimore not only disrupted the...
-

 1.2KMalware
1.2KMalwareU.S. Charges 7 Chinese Nationals in Major 14-Year Cyber Espionage Operation
The U.S. Department of Justice (DoJ) on Monday unsealed indictments against seven Chinese nationals for their involvement in a hacking group that...
-
 1.7KMalware
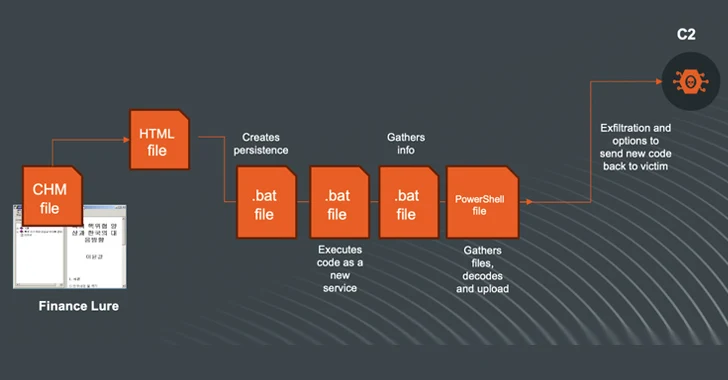
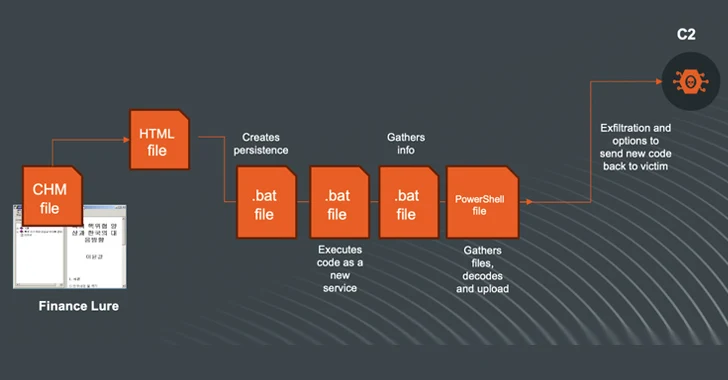
1.7KMalwareN. Korea-linked Kimsuky Shifts to Compiled HTML Help Files in Ongoing Cyberattacks
The North Korea-linked threat actor known as Kimsuky (aka Black Banshee, Emerald Sleet, or Springtail) has been observed shifting its tactics, leveraging...
-

 1.4KVulnerabilities
1.4KVulnerabilitiesAPIs Drive the Majority of Internet Traffic and Cybercriminals are Taking Advantage
Application programming interfaces (APIs) are the connective tissue behind digital modernization, helping applications and databases exchange data more effectively. The State of...
-
 1.6KMalware
1.6KMalwareFrom Deepfakes to Malware: AI’s Expanding Role in Cyber Attacks
Large language models (LLMs) powering artificial intelligence (AI) tools today could be exploited to develop self-augmenting malware capable of bypassing YARA rules....






