Search results for "Discovery"
-

 5.1KVulnerabilities
5.1KVulnerabilitiesImplementing Risk-Based Vulnerability Discovery and Remediation
In this day and age, vulnerabilities in software and systems pose a considerable danger to businesses, which is why it is essential...
-
 261Information Gathering
261Information GatheringArjun v1.1 – HTTP Parameter Discovery Suite
Features Multi-threading 3 modes of detection Regex powered heuristic scanning Huge list of 3370 parameter names Usage Note: Arjun doesn’t work with...
-
Information Gathering
Hackertarget – Tools And Network Intelligence To Help Organizations With Attack Surface Discovery
Use open source tools and network intelligence to help organizations with attack surface discovery and identification of security vulnerabilities. Identification of an...
-
 289Hacking Tools
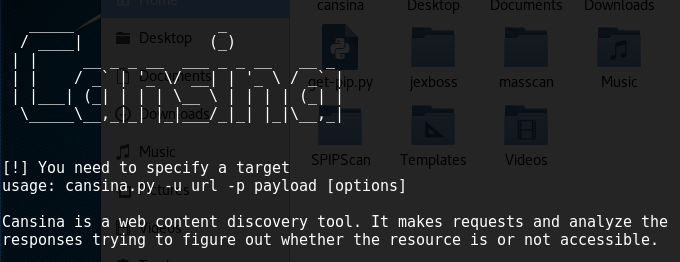
289Hacking ToolsCansina – Open Source Hidden Content Discovery Tool
Reconnaissance is one of the first steps to conduct within a pen test engagement. During this stage, information is gathered using different...
-

 293Hacking Tools
293Hacking ToolsSqlmap – Free Tool for SQL Injection Discovery And Exploitation
Sqlmap is an open source tool used to test the SQL injection vulnerabilities within web applications. The tool requires Python 2.6.x and...
-
 334Information Gathering
334Information GatheringSubFinder – A Subdomain Discovery Tool That Discovers Valid Subdomains For Websites
SubFinder is a subdomain discovery tool that discovers valid subdomains for websites by using passive online sources. It has a simple modular...
-

 259Sql Injection
259Sql InjectionSleuthQL – SQL Injection Discovery Tool
SleuthQL is a python3 script to identify parameters and values that contain SQL-like syntax. Once identified, SleuthQL will then insert SQLMap identifiers...
-

 305News
305NewsSecurity Discovery: 1st Kotlin-Based Malware In Google Play Store
Cyber security researchers have reportedly discovered what they think is the first Krotin-based malware affecting the Android OS. The discovery has been...
-

 277News
277NewsDiscovery of new snooping tool in Android devices
The lethal form of surveillance tools meant for Android spyware is something that comes uncovered. These kinds of spyware are equipped with...
-
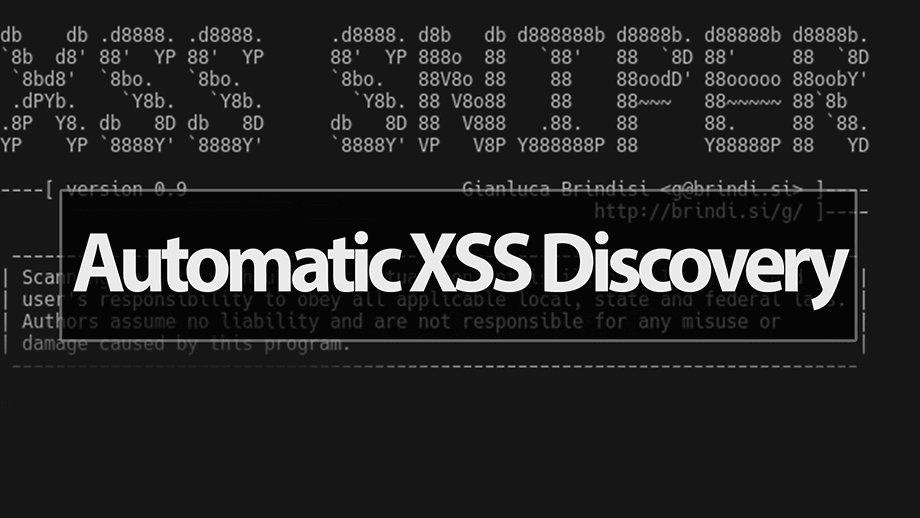
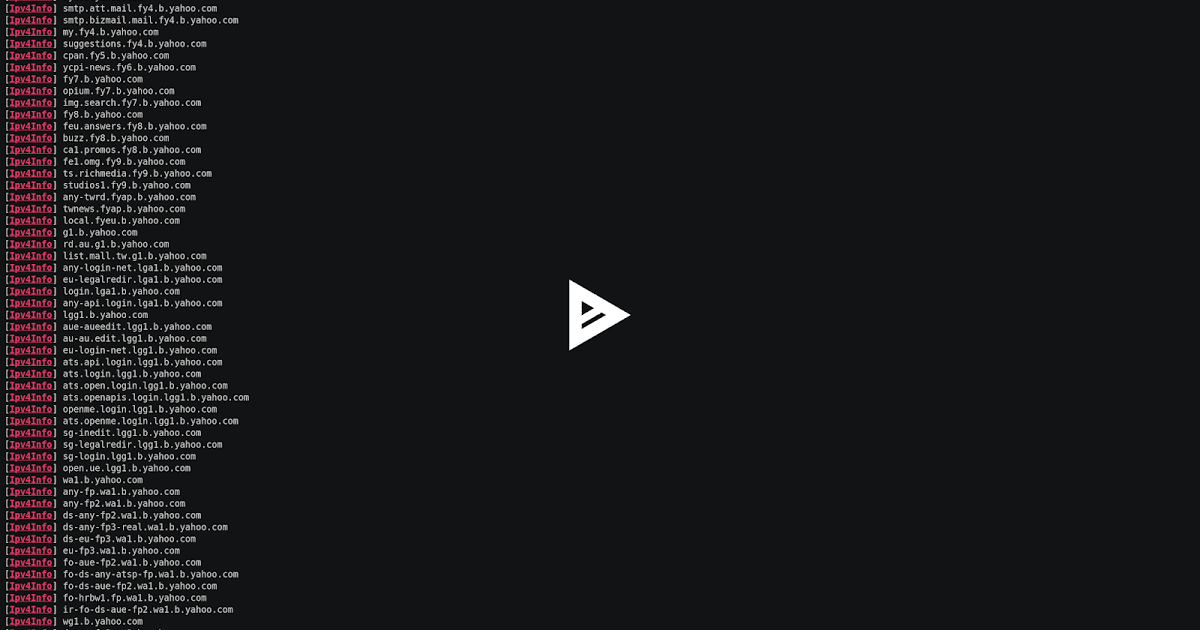
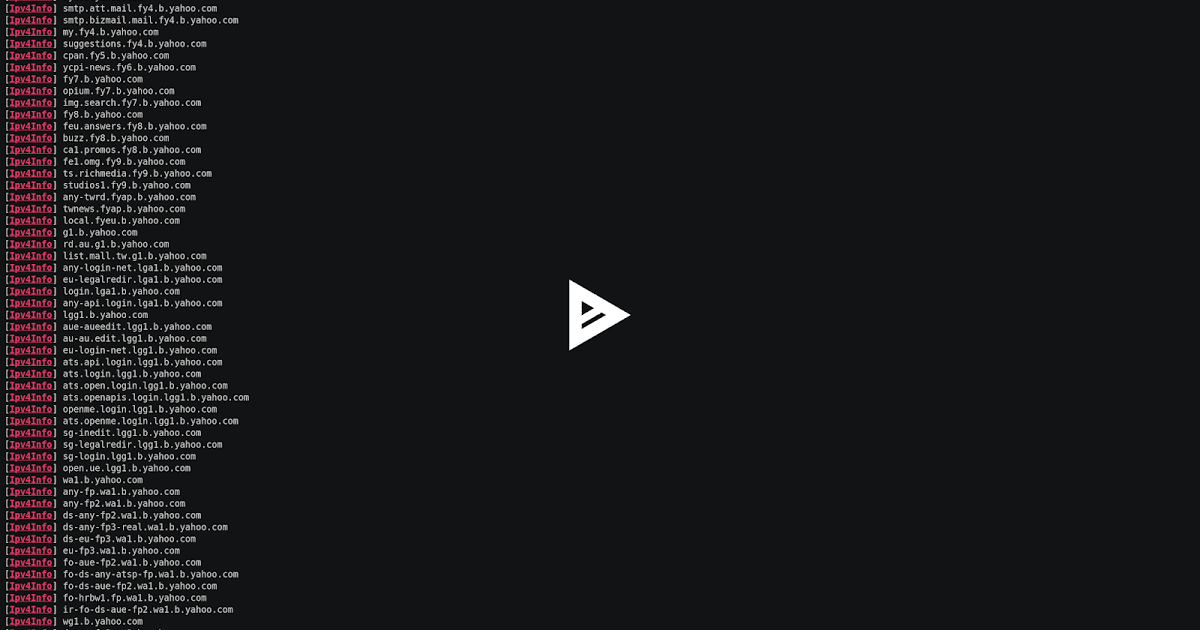
 268Video Tutorials
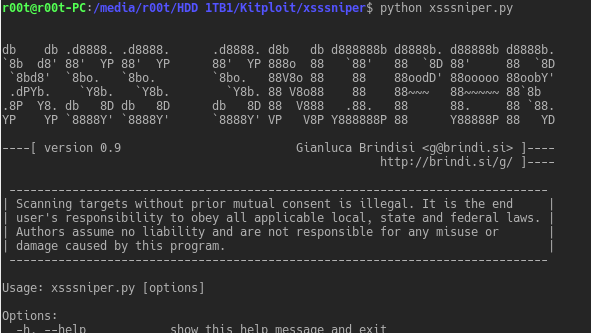
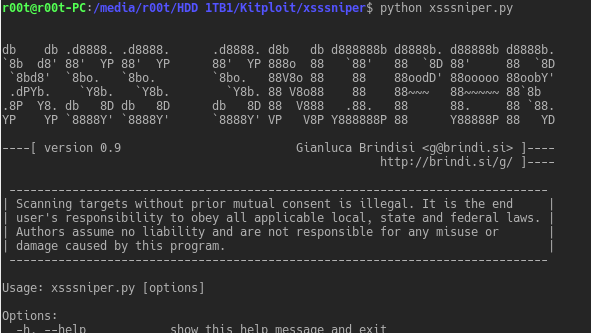
268Video TutorialsXSSSNIPER – An Automatic XSS Discovery Tool – Kali Linux 2017.3
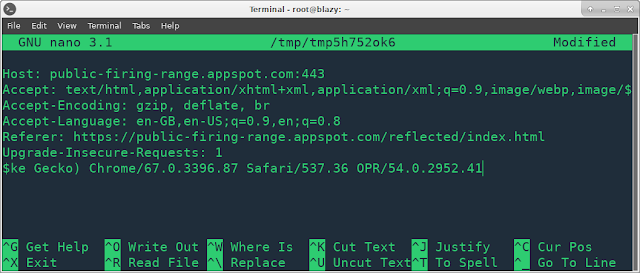
xsssniper is an handy xss discovery tool with mass scanning functionalities. Usage: Usage: xsssniper.py [options] Options: -h, --help show this help message...
-
 272Exploitation Tools
272Exploitation ToolsXSSSNIPER – An Automatic XSS Discovery Tool
XSSSNIPER is an handy xss discovery tool with mass scanning functionalities. Usage: Usage: xsssniper.py [options] Options: -h, --help show this help message...
-

 238Vulnerability Analysis
238Vulnerability AnalysisACLight – PowerShell Script for Advanced Discovery of Privileged Accounts (includes Shadow Admins)
ACLight is a tool for discovering privileged accounts through advanced ACLs (Access Lists) analysis. It includes the discovery of Shadow Admins in...
-
 215Vulnerabilities
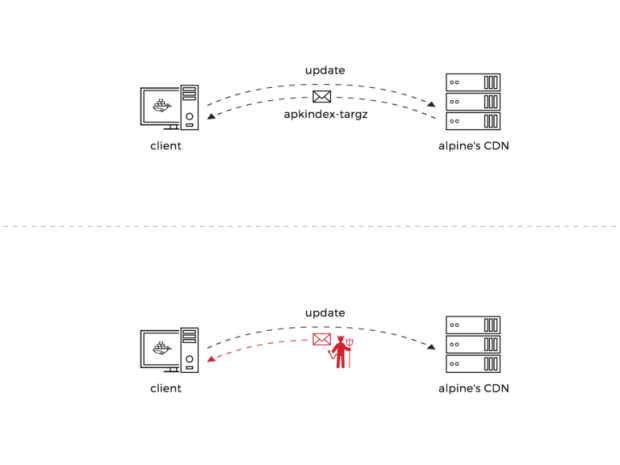
215VulnerabilitiesAlpine Linux: From vulnerability discovery to code execution (Pt 1 of 2)
I recently uncovered two critical vulnerabilities in Alpine Linux’s package manager, assigned CVE-2017-9669 and CVE-2017-9671. These vulnerabilities could potentially lead to an...
-
 238Vulnerabilities
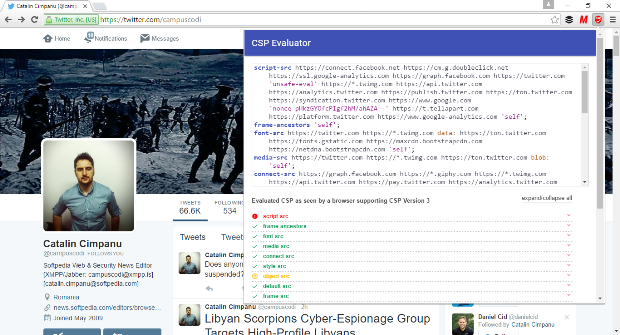
238VulnerabilitiesGoogle Releases Two Chrome Extensions for XSS Discovery and Mitigation
Google says it paid over $1.2 million just for XSS bugs. Google released two new tools called CSP Evaluator and CSP Mitigator...
-
 218Data Security
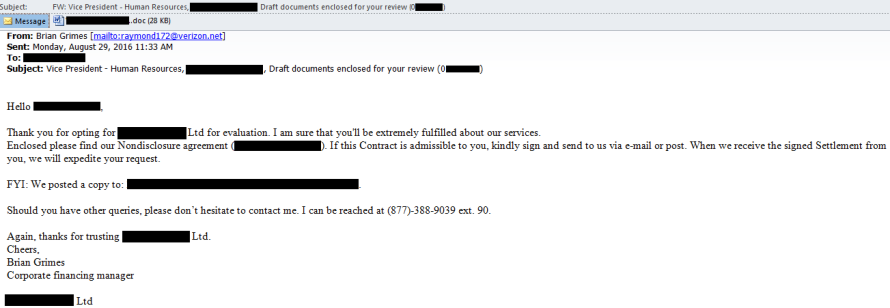
218Data SecurityDiscovery of a New Nymaim Malware Variant Employing Advanced Delivery, Obfuscation and Blacklisting methods
Verint’s Cyber Research team has discovered an unknown variant of the Nymaim malware family, a group of threats that are also capable...
-
 213Malware
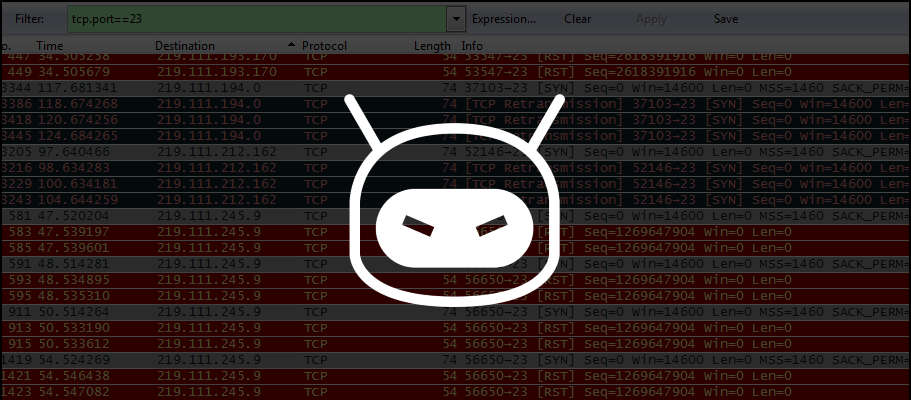
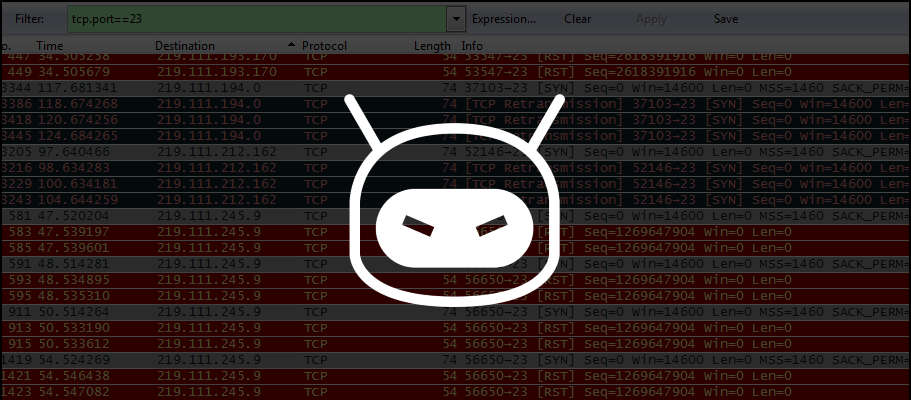
213MalwareProblems Reappear for IoT Devices Owners with Discovery of New DDoS Trojan
Security researchers discovers IRCTelnet malware. A new malware family written by what appears to be an experienced coder is aiming for Linux-based...






