Search results for "Dynamic"
-

 4.6KMalware
4.6KMalwareEvasive QBot Malware Leverages Short-lived Residential IPs for Dynamic Attacks
An analysis of the “evasive and tenacious” malware known as QBot has revealed that 25% of its command-and-control (C2) servers are merely...
-
 1.4KData Security
1.4KData SecurityDon’t open emails from Microsoft Dynamics 365. Threat actors are exploiting its flaws to send phishing emails with legitimate Microsoft links
Microsoft’s Dynamics 365 Customer Voice is a software that is primarily used to collect customer feedback.It may be utilized to gather data...
-

 2.4KGeek
2.4KGeekWhy You Should Use Dynamic QR Code Generator
We cannot argue that proof of authenticity gives more credibility. To make your brand more authentic, you need to have a dynamic...
-
 3.2KHack Tools
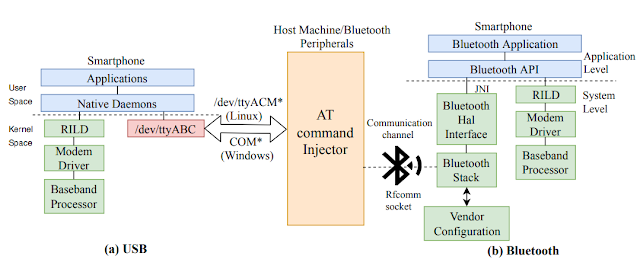
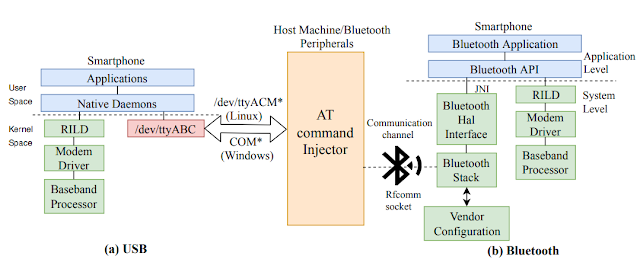
3.2KHack ToolsATFuzzer – Dynamic Analysis Of AT Interface For Android Smartphones
“Opening Pandora’s Box through ATFuzzer: Dynamic Analysis of AT Interface for Android Smartphones” is accepted to the 35th Annual Computer Security Applications...
-
 4.0KHack Tools
4.0KHack Toolsfunction tracer: analyze a binary file with dynamic instrumentation
functrace – A function tracer functrace is a tool that helps to analyze a binary file with dynamic instrumentation using DynamoRIO (http://dynamorio.org/). These are some...
-
 382Reverse Engineering
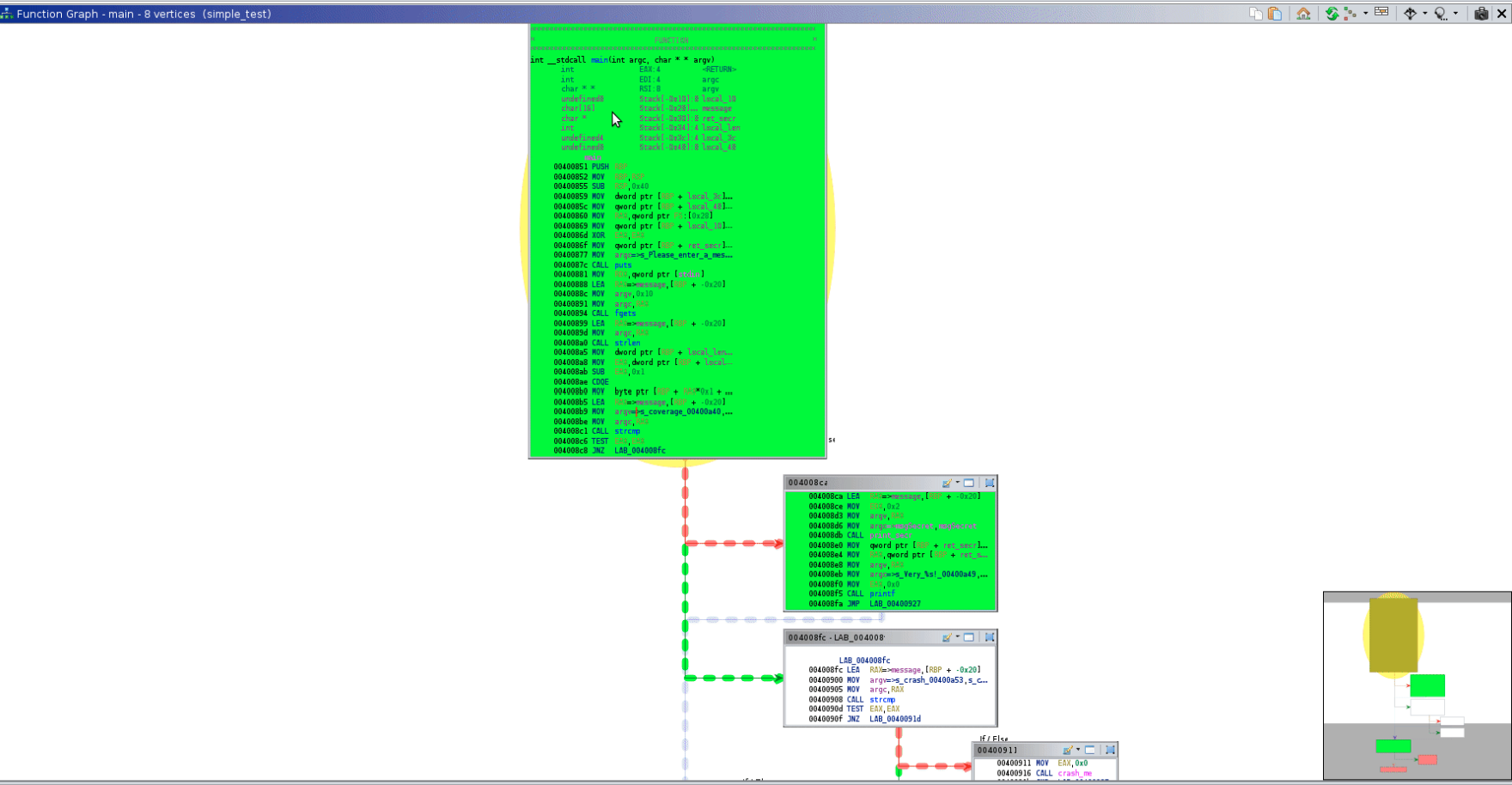
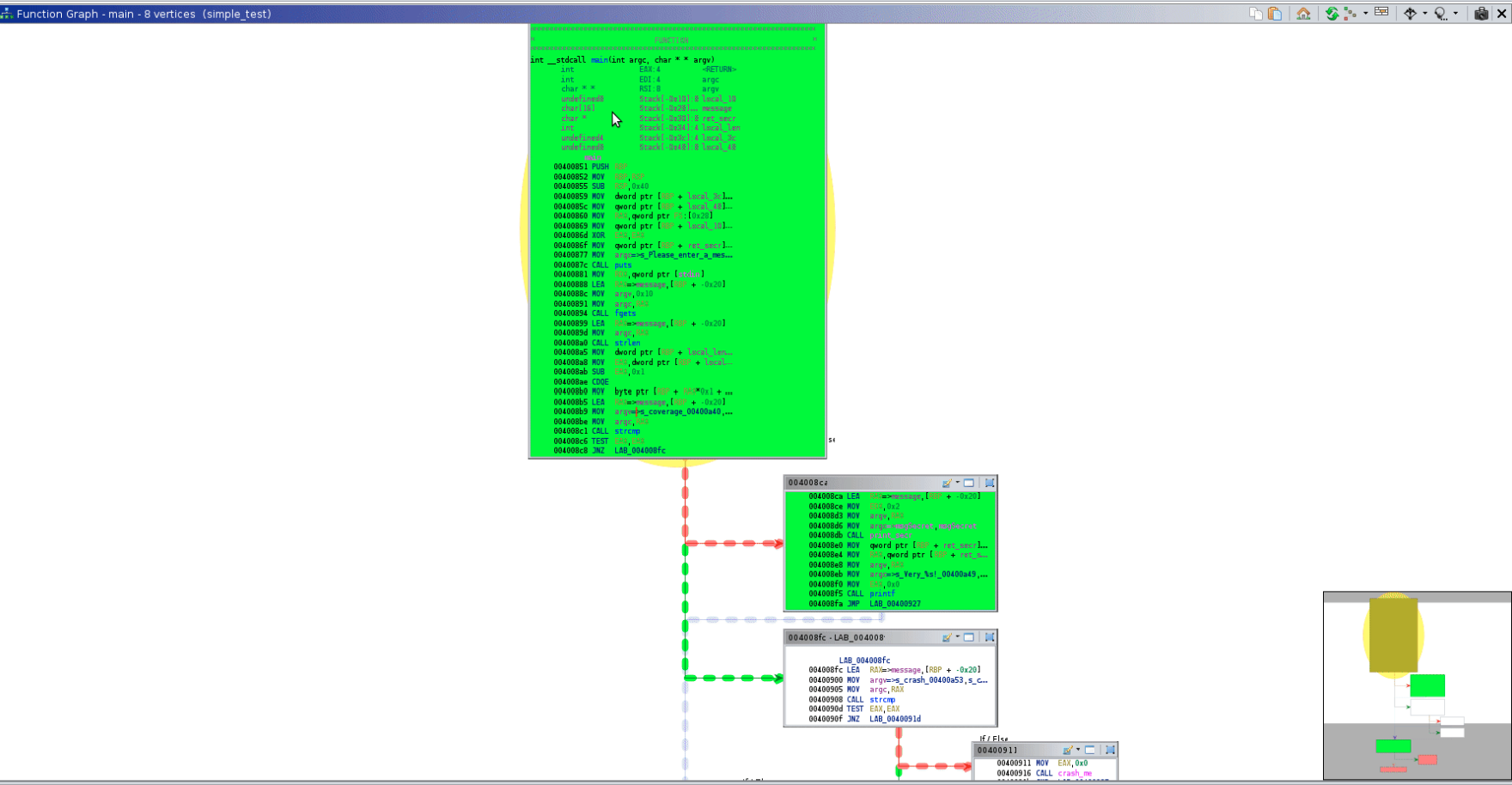
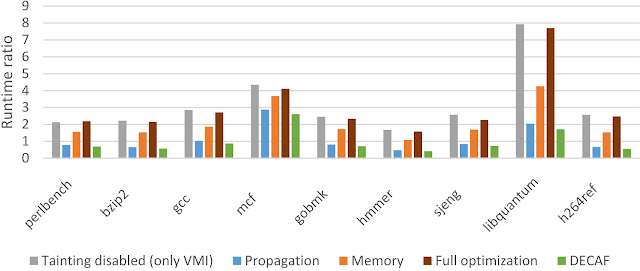
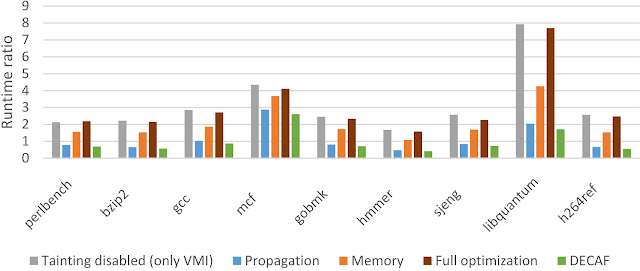
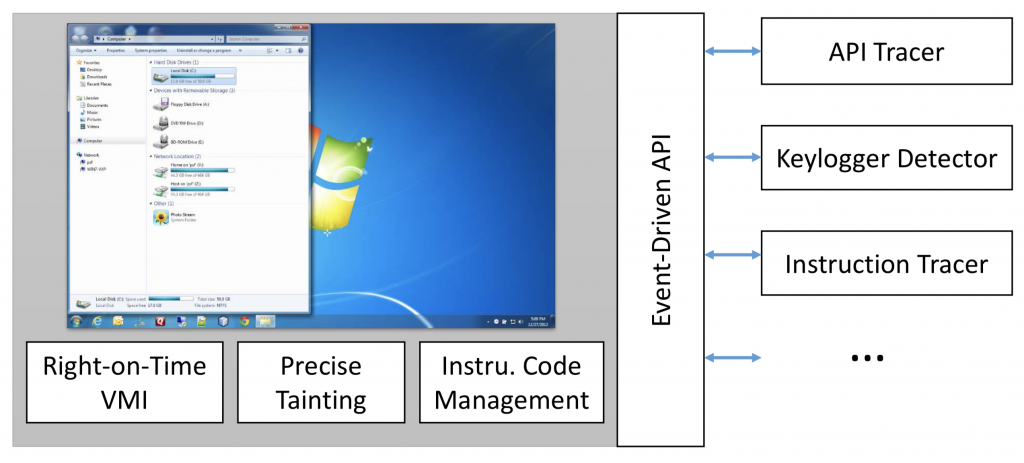
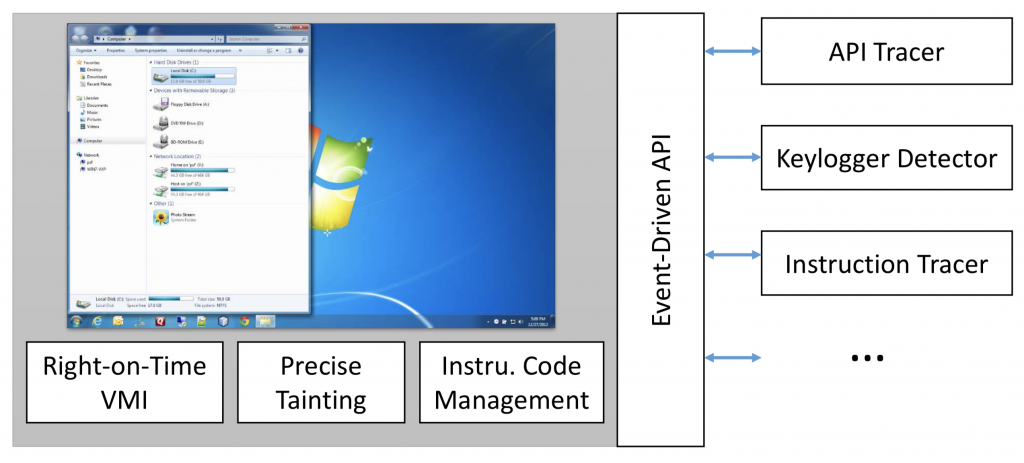
382Reverse EngineeringDECAF – Short for Dynamic Executable Code Analysis Framework
DECAF++, the new version of DECAF, taint analysis is around 2X faster making it the fastest, to the best of our...
-
 286Binary Analysis
286Binary AnalysisDECAF – Dynamic Executable Code Analysis Framework
DECAF (short for Dynamic Executable Code Analysis Framework) is a binary analysis platform based on QEMU. DECAF++ DECAF++, the new version of...
-

 2.0KMalware
2.0KMalwareStatic Malware Analysis Vs Dynamic Malware Analysis
Malware Analysis: An Introduction Cybercriminals are turning more sophisticated and innovative, new and advanced varieties of malware are coming up and malware...
-

 272Binary Analysis
272Binary AnalysisManticore – Dynamic Binary Analysis Tool
Manticore is a prototyping tool for dynamic binary analysis, with support for symbolic execution, taint analysis, and binary instrumentation. Manticore comes with...
-
 189Hack Tools
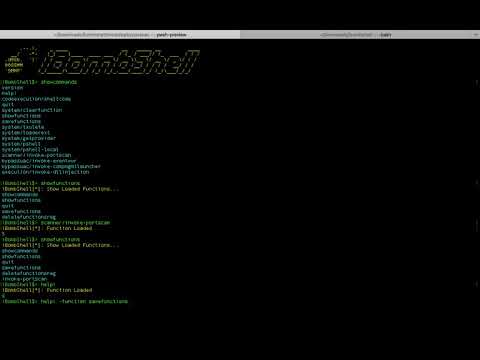
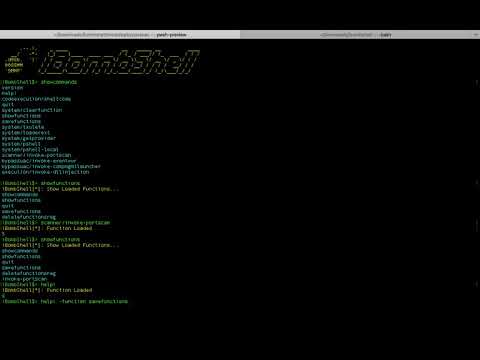
189Hack Toolsibombshell – Dynamic Remote Shell
ibombshell is a tool written in Powershell that allows you to have a prompt at any time with post-exploitation functionalities (and in...
-
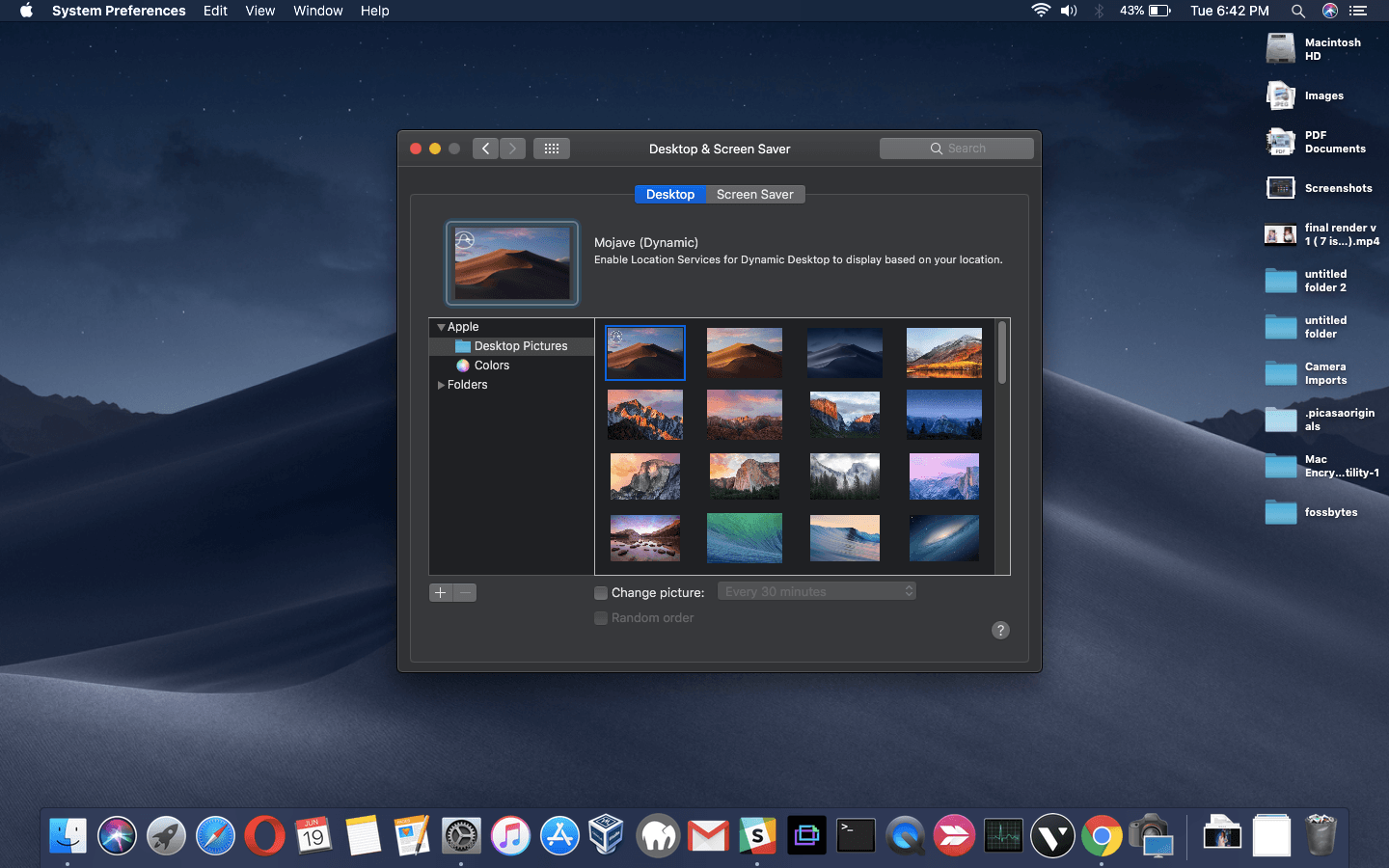
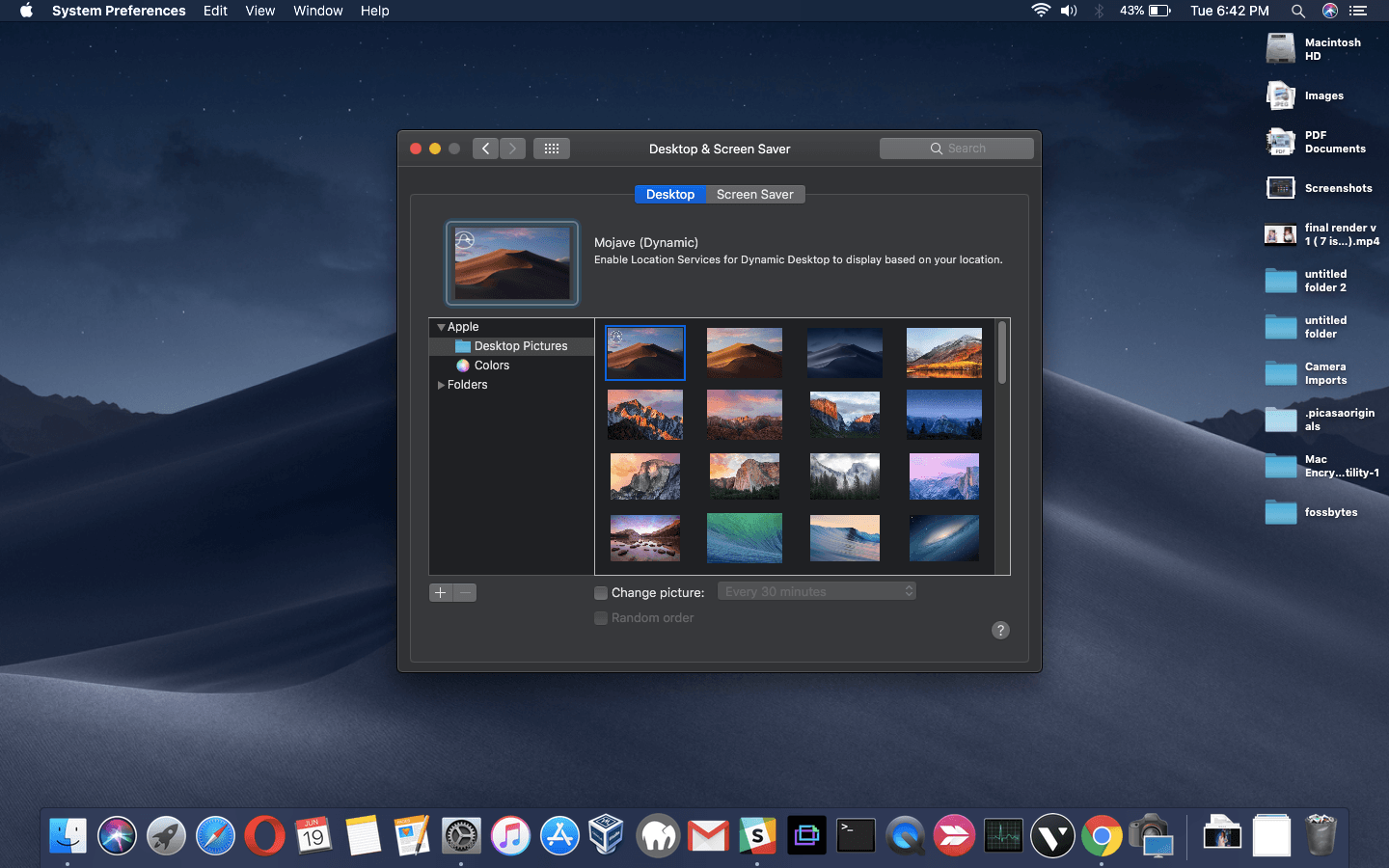 401How To
401How ToHow To Use MacOS Mojave’s Dynamic Desktop On Windows 10?
Whenever a big feature arrives on a platform some developers want to bring it to other platforms. The case of macOS Mojave...
-

 258Hack Tools
258Hack ToolsWhonow DNS Server – Dynamic DNS Rebinding
A malicious DNS server for executing DNS Rebinding attacks on the fly. whonow lets you specify DNS responses and rebind rules dynamically using domain requests themselves. #...
-
 263Reverse Engineering
263Reverse EngineeringQBDI – QuarkslaB Dynamic binary Instrumentation
QuarkslaB Dynamic binary Instrumentation (QBDI) is a modular, cross-platform and cross-architecture DBI framework. It aims to support Linux, macOS, Android, iOS and...
-
 247Web Application Security
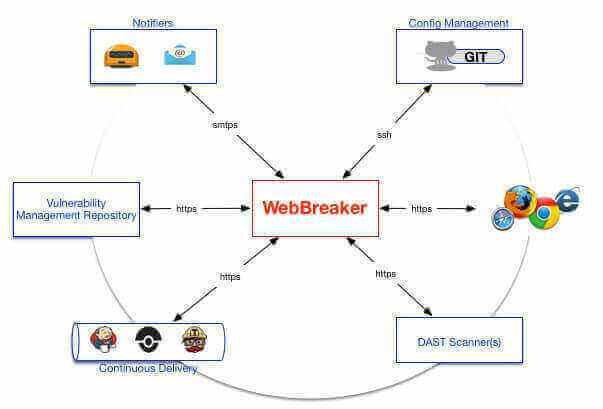
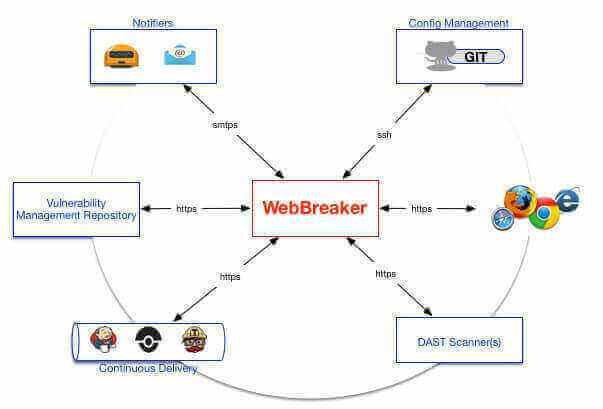
247Web Application SecurityWebBreaker – Dynamic Application Security Test Orchestration (DASTO)
Build functional security testing, into your software development and release cycles! WebBreaker provides the capabilities to automate and centrally manage Dynamic Application...
-
 452Vulnerabilities
452Vulnerabilities6 Critical RCE and Buffer Overflow Vulnerabilities in IBM Informix Dynamic Server and Informix Open Admin Tool
IBM Informix Dynamic Server and Informix Open Admin Tool contains 6 Critical Vulnerabilities including RCE and a Buffer overflow in HEAP. IBM Informix...
-
 283Opinion
283OpinionBetter Mac Testing: Static versus Dynamic Testing
Dynamic or on-access Mac testing of AV products is problematical with samples for which Apple has implemented signature detection.
-

 216Cyber Crime
216Cyber CrimeThe Dynamic Duo for Securing your Android: Common Sense and Security Software
On Thursday, September 12, Duo Security, a young-but-respected vendor of two-factor authentication devices, announced the preliminary results of a study of over...






