Search results for "EXIST"
-

 3.4KNews
3.4KNewsThe children’s smartwatches exist vulnerability that discloses GPS smartwatches
Security company Rapid7 has disclosed security vulnerabilities in three children’s smartwatches sold on Amazon. These three children’s smartwatches are the GreaSmart, the...
-

 2.5KNews
2.5KNewsSpot The Difference: There Exists Fake AirPods Pro For Just $95
As Apple products are accustomed to being expensive and off-limits for many, there are companies that tend to release its rip-offs for...
-

 552Reviews
552ReviewsAre OnePlus 7T’s Features Good Enough For Its Existence?
It’s been almost six years since OnePlus entered the mobile market, and it’s safe to say it changed the notion that smartphones...
-

 315News
315NewsWill Facebook’s Libra Coins Exist Soon? Ask Congress
For many years, Facebook literally ignored the existence of cryptocurrency as a potential business which the social media giant can engage with....
-
 313Tutorials
313TutorialsSolution to spamming, Check any Unknown Email ID existence
Email spamming is most common from last 10-20 years. There are many individual or groups of attackers who spread malicious content by...
-

 290News
290NewsAI Creates Fake Humans That Never Existed In The Real World
Nothing is scarier than the headline ‘AI Creates Fake Humans’. I am afraid that this headline is no longer a fantasy. We...
-

 240Articles
240ArticlesCynet is offering unhappy competitors’ customers a refund for the time remaining on existing contracts
Cynet goes head-to-head with CrowdStrike, DarkTrace, Cylance, Carbon Black & Symantec, offering their unhappy customers a refund for the time remaining on...
-

 284Geek
284GeekThese people don’t exist – They were created by tech using Artificial Intelligence
Artificial intelligence is increasingly advanced and has entered more and more areas, even in the most unexpected and sensitive issues for society...
-

 205Malware
205MalwareHackers Use Hijacked Email Address To Send Malware as a Reply to Existing Email Thread
A new more sophisticated phishing campaign uses hijacked email accounts to deliver malware as a part of the response to the existing...
-

 229News
229NewsDo Not Ignore the Existence of Cyber Attacks
Do you understand what is a real cyber attack and how to prepare yourself in case it happens? Every day cyber attacks...
-

 240Geek
240GeekOpen Source Turns 20 Years Old: How This Term Came Into Existence?
When Netscape released the source code for its Netscape Communicator web browser 20 years ago, a discussion was sparked in the developer...
-

 321Geek
321GeekHackers are digging into Microsoft Word flaw that existed for last 17 year
Cybercriminals are successfully exploiting a vulnerability present in Microsoft Office Equation Editor for the past 17 years for distributing malware. It is a backdoor...
-
 251Hacked
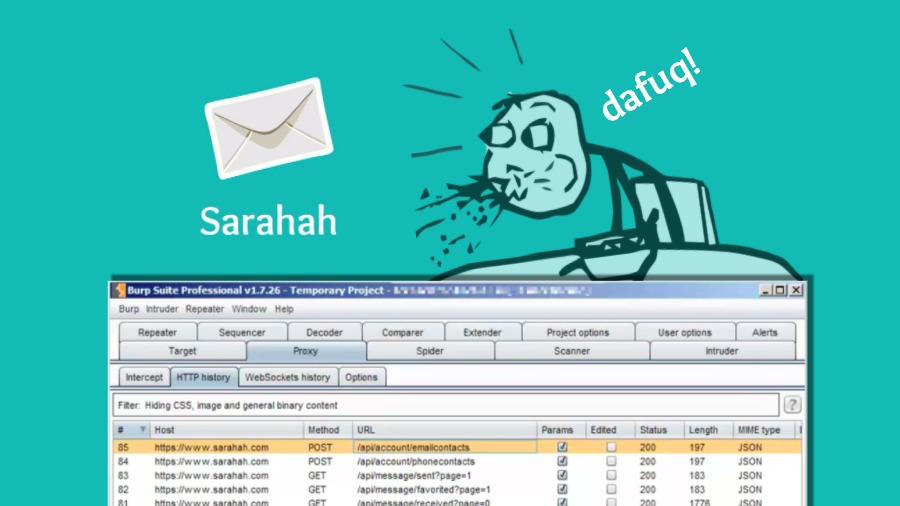
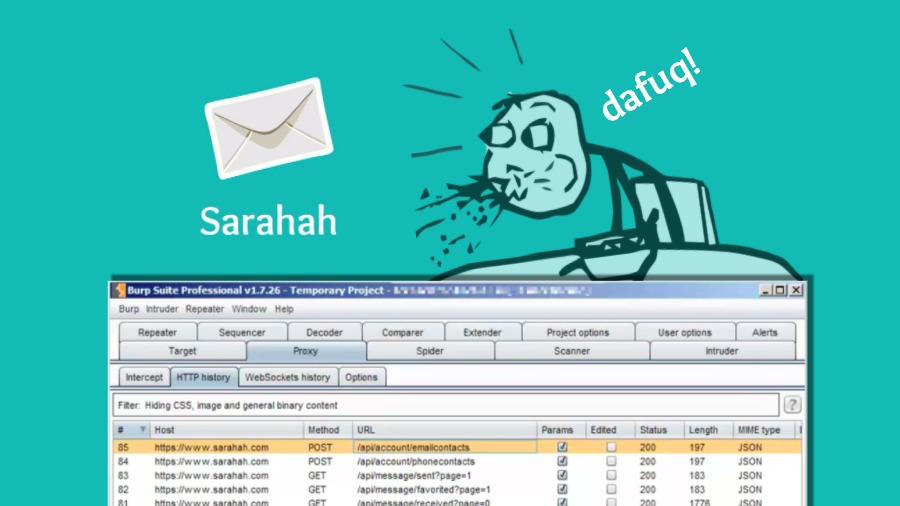
251HackedSarahah App Keeps Uploading Your Email And Phone Contacts For A Feature That Doesn’t Exist
Short Bytes: The anonymous feedback app Sarahah has been in controversies since its popularity exploded. After the allegations of cyber bullying, a...
-
 228Hackers Repository
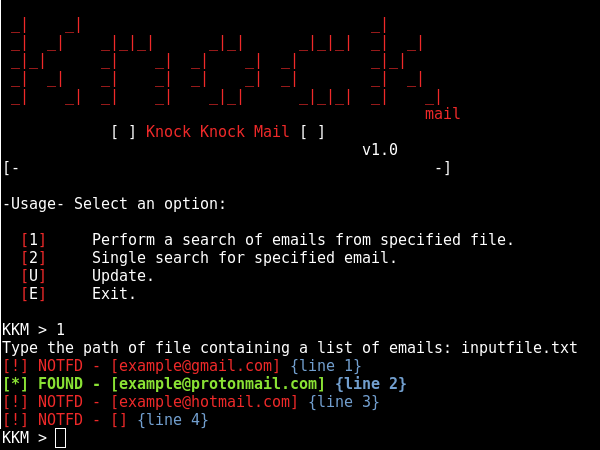
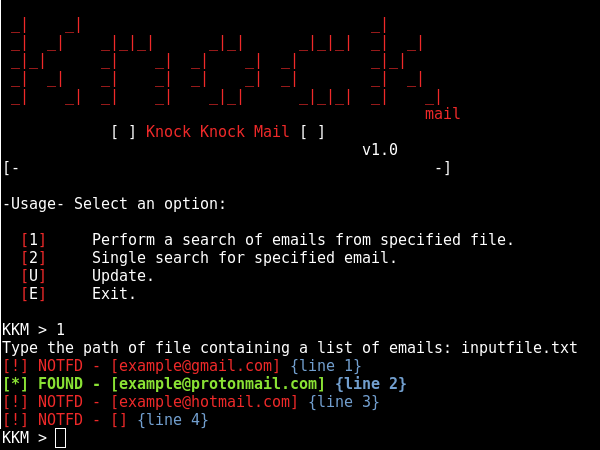
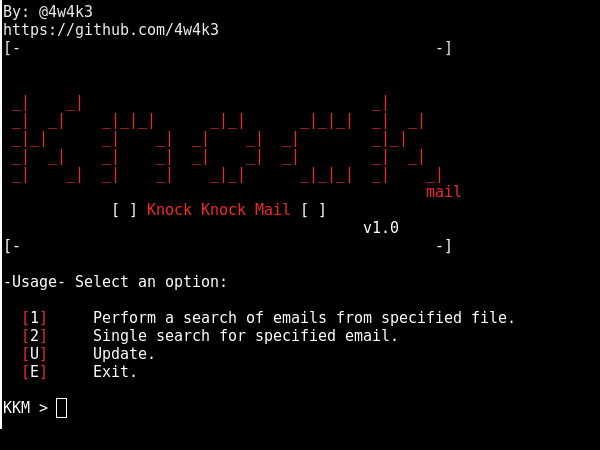
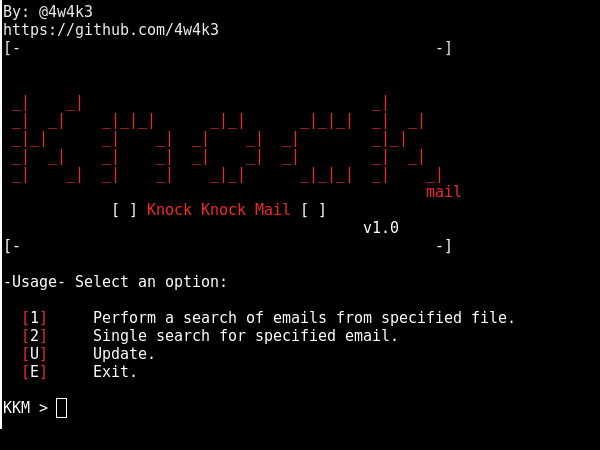
228Hackers RepositoryKnockMail – Verify if email exists
KnockMail Verify if email exists Copyright 2017 KnockMail Written by: * Alisson Moretto – 4w4k3 Twitter: @4w4k3Official Cloning: git clone https://github.com/4w4k3/KnockMail.git Running:...
-
 316Information Gathering
316Information GatheringKnockMail – Verify if an Email exists
Knockmail performs a search of emails from a specified txt file and verifies whether its a valid email address. Cloning: git clone...
-

 373Android Hacking
373Android HackingKwetza – Python script to inject existing Android applications with a Meterpreter payload
Kwetza is a tool that allows you to infect an existing Android application with a Meterpreter payload. What does it do? Kwetza...
-

 290Geek
290GeekGoogle Discloses Critical Existing Bug in Internet Explorer and Edge
It is evident that Google does not like Microsoft, but it is also a fact that Microsoft is lazy at fixing critical vulnerabilities...
-
 299Lists
299Lists21 Weird Apple Products You Never Knew Existed
Apple did various product experiments in its early years. They tried their clothing lines and some limited stuff. But many people don’t...
-

 247Lists
247Lists5 Sci-Fi Technologies You Didn’t Know Already Exist Around You
Short Bytes: Most of us think that science fiction (Sci-Fi) is only confined to movies, books, and people’s imagination. But within the...
-
 214Malware
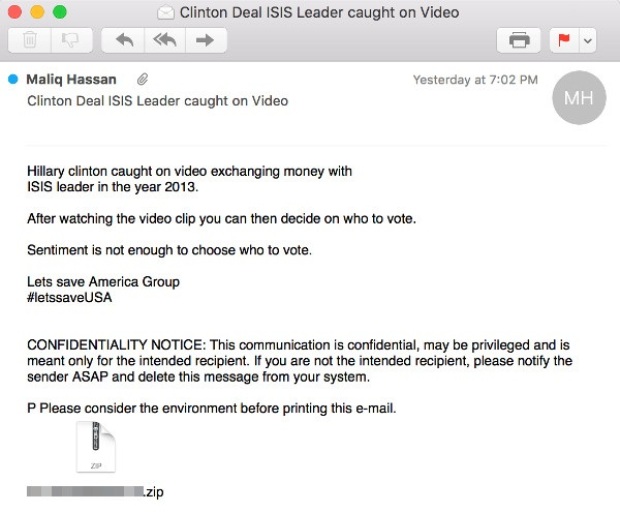
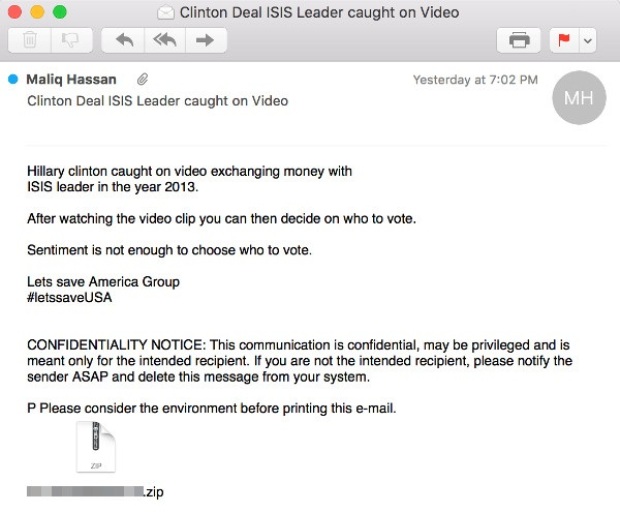
214MalwareNon-existent video involving Hillary Clinton and ISIS leader used as bait in malicious spam
Malicious attachment contains Adwind cross-platform remote access Trojan. Cybercriminals are using clickbait, promising a video showing Democratic Party presidential nominee Hillary Clinton exchanging...
-

 274Geek
274GeekBackdoor on Your Smartphone Already Exists — Explained
Though the FBI has already hacked into the iPhone of suspected San Bernardino shooter Syed Rizwan Farook, there’s something missing — Mr. Kokumai, President of...






