Search results for "Embedded"
-

 4.8KMalware
4.8KMalwareNew RAT malware evades detection using JavaScript code embedded in HTML receipt files instead of downloading an ISO file from remote servers
Cybersecurity specialists report the detection of a new phishing campaign dedicated to the delivery of the AsyncRAT Trojan hidden in an HTML...
-
 2.7KDDOS
2.7KDDOS14 New Vulnerabilities Uncovered In Linux Powered Embedded Devices
On Tuesday 14, the cybersecurity researchers of Claroty and JFrog have detected 14 new vulnerabilities in the BusyBox Linux utility. BusyBox is...
-

 3.8KVulnerabilities
3.8KVulnerabilities25 BadAlloc vulnerabilities affects BlackBerry QNX RTOS used by over 195 million vehicles and embedded systems in different industries. Patch quickly
In a security report, BlackBerry announced that its QNX Real Time Operating System (RTOS) is affected by a vulnerability known as BadAlloc....
-
 412Exploitation
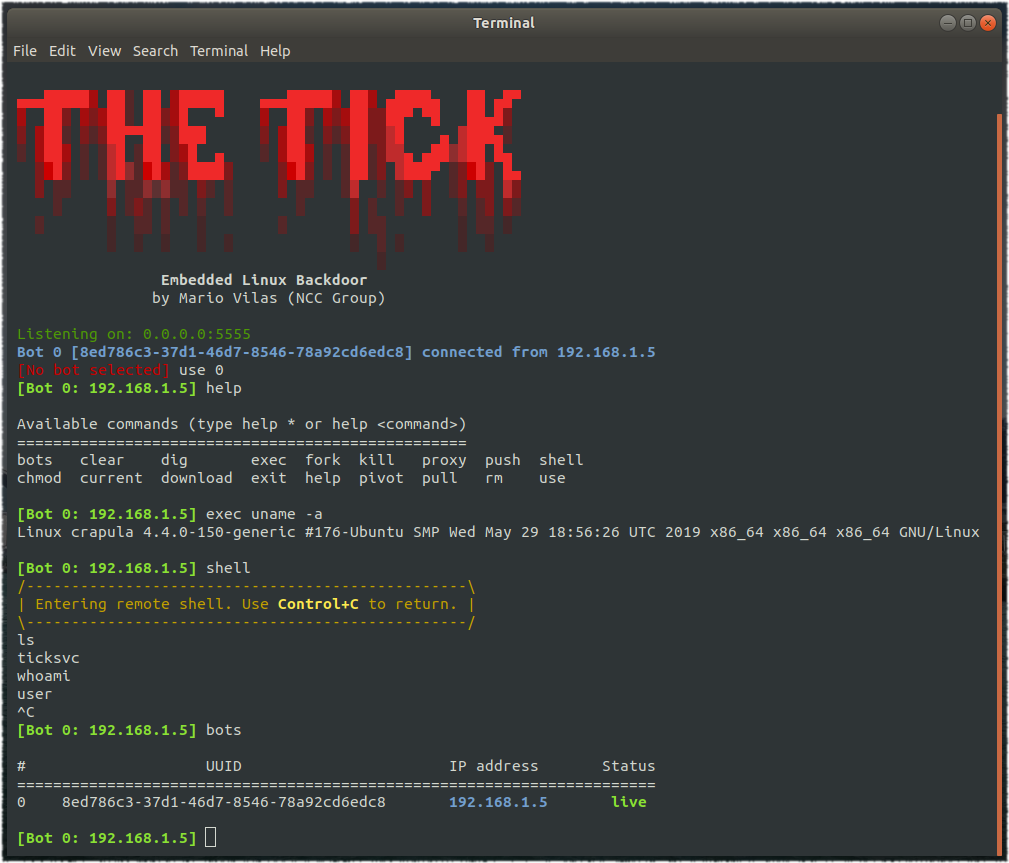
412ExploitationTheTick – A simple embedded Linux backdoor
A simple embedded Linux backdoor. Compiling The Tick depends only on libcurl, so make sure you have the corresponding development package. For...
-

 280News
280NewsGoogle to Block Sign-ins from Embedded Browser Frameworks
In a bid to improve its phishing protections and to protect users from MITM attacks, Google has come up with a new...
-
 271News
271NewsGoogle To Ban Embedded Browser Logins To Stop Man-In-The-Middle Attacks
Google will ban logins from embedded browser frameworks, starting June 2019. The reason is the increased risk of phishing hacks using the...
-

 219News
219NewsMicrosoft Patents Touch Sensor Embedded Fabrics For Surface Devices
According to a patent application, Microsoft’s next-gen Surface devices might include smart fabrics on the back, that would offer standard functionality like...
-

 274Hacking Tools
274Hacking ToolsRoutersploit – A Free Framework for Exploiting Embedded Devices
Routersploit is an open source framework used for exploiting vulnerabilities in embedded devices like routers. Routersploit is loaded with various modules that...
-
 203Vulnerabilities
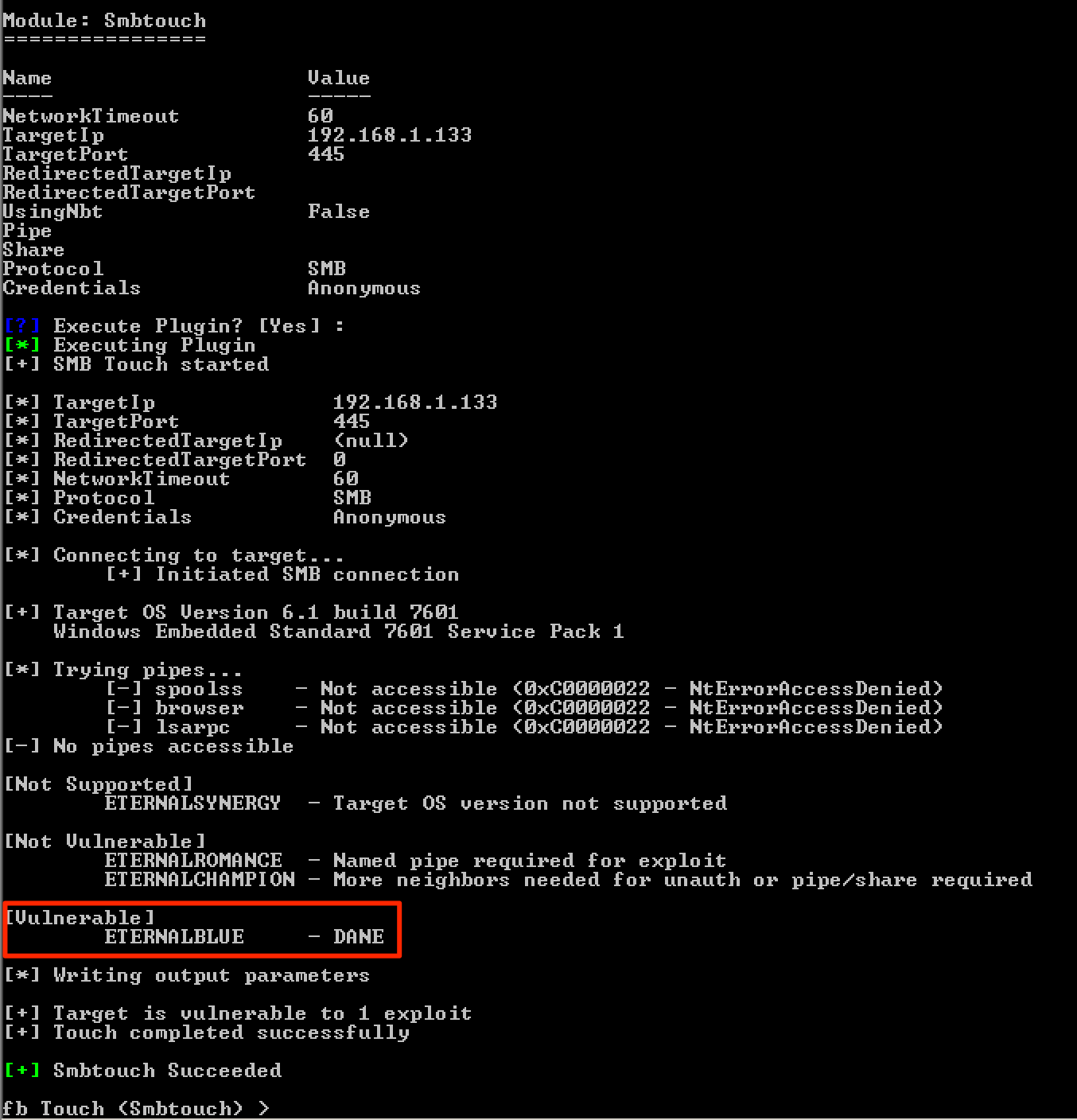
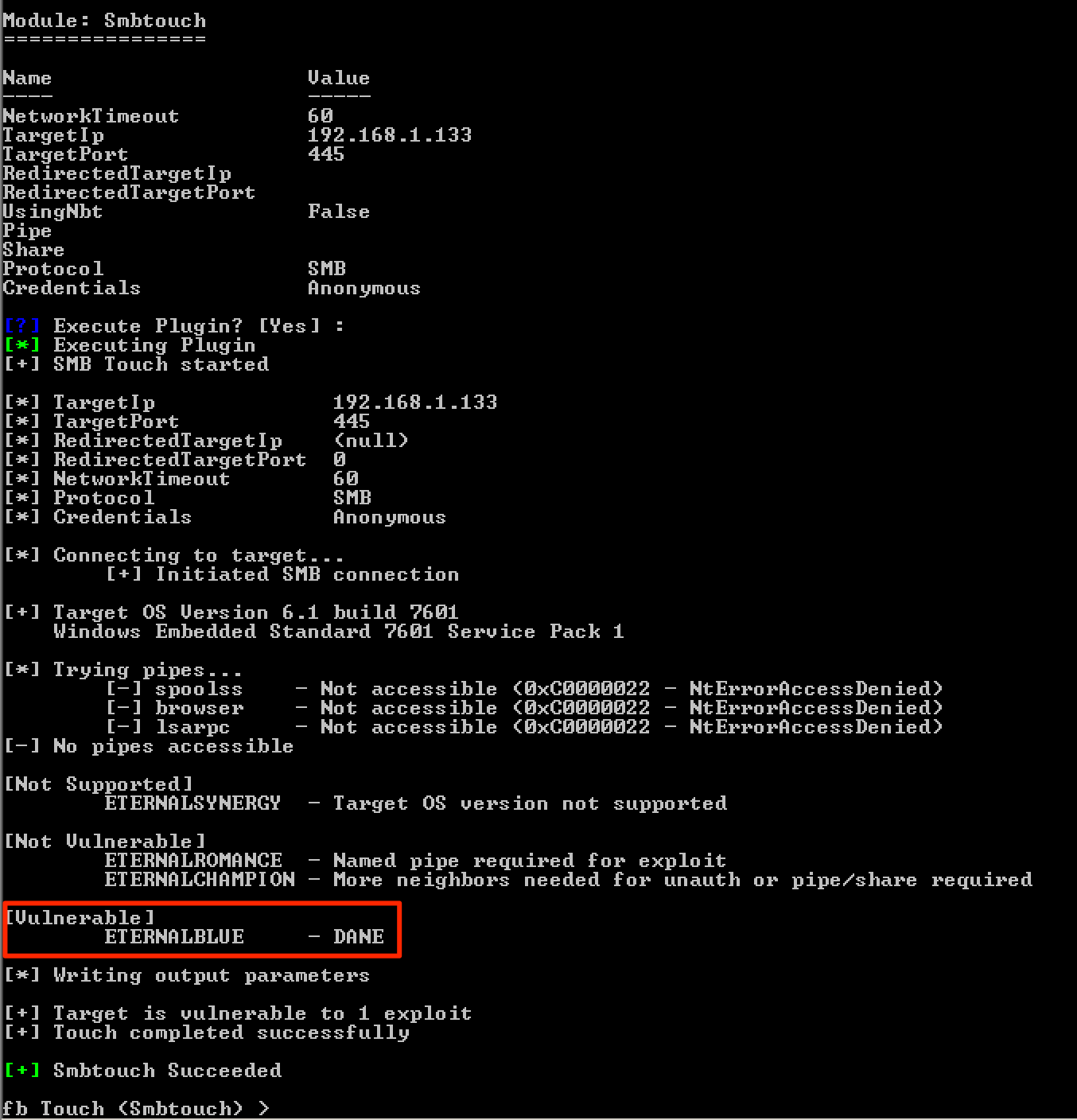
203VulnerabilitiesPatching DoublePulsar to Exploit Windows Embedded Machines
During one of my engagements, I discovered some Windows devices that were affected by the MS17-010vulnerability. One of these devices caught my attention...
-

 274Incidents
274IncidentsWhat happened after the US moved to chip-embedded payment cards?
Card-Not-Present fraud is still a problem, however. The US began its transition to chip-based credit cards in earnest in October 2015, after...
-
 321Cryptocurrency
321CryptocurrencyHackers Spreading Cryptocurrency Mining scripts via videos that Embedded in MS Office Word Documents
Microsoft word documents abused by Cryptocurrency Mining script embedded phishing Videos and victims tricked into watching an “innocent” video that leads to performing a...
-

 338Geek
338GeekGoogle might block embedded cryptocurrency mining with new Chrome feature
Google Aims to Put an End to Secret Cryptojacking by Making In-Browser Permissions Necessary. In-browser cryptocurrency mining has become the latest obsession...
-

 264Malware
264MalwareBeware: Malicious Payload “Hworm” Dropped Through Embedded Youtube Video’s
A Malware called Hworm Performing multiple Attacks including steal passwords from Firefox, Opera, and Chrome browsers, ability to log keystrokes, kill running...
-
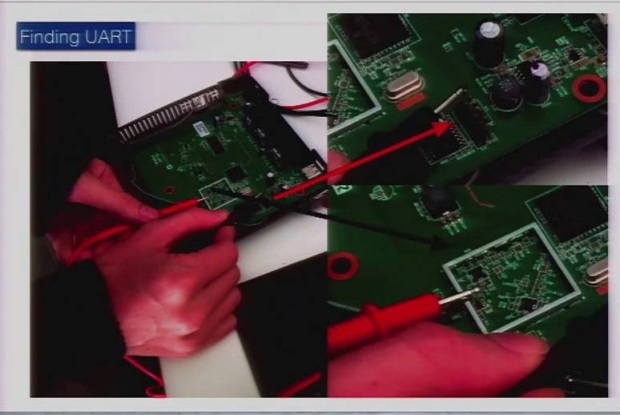
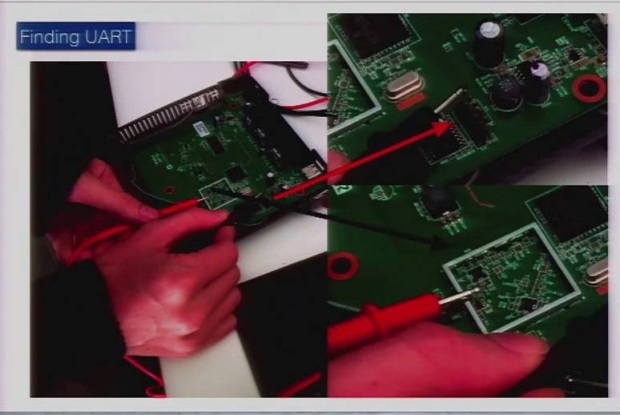 211Data Security
211Data SecurityReversing and Exploiting Embedded Devices (Walking the software and hardware stack)
As technology matures and microprocessors are becoming cheap we are starting to see a trend of products that are now ?smart.? The...
-
 201Malware
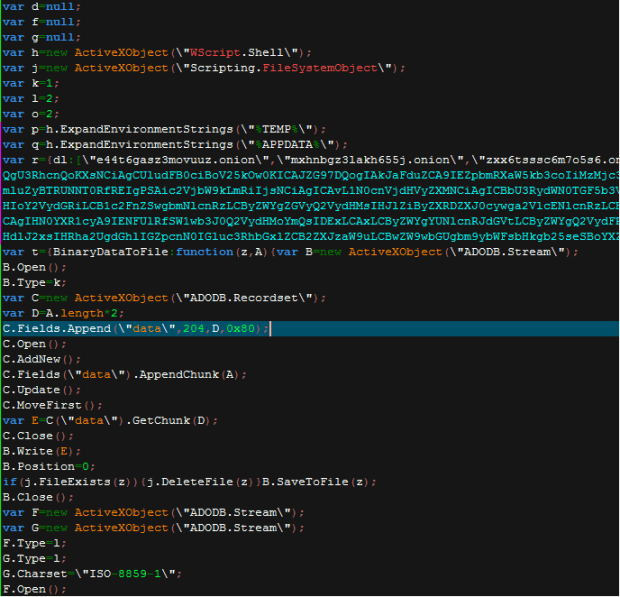
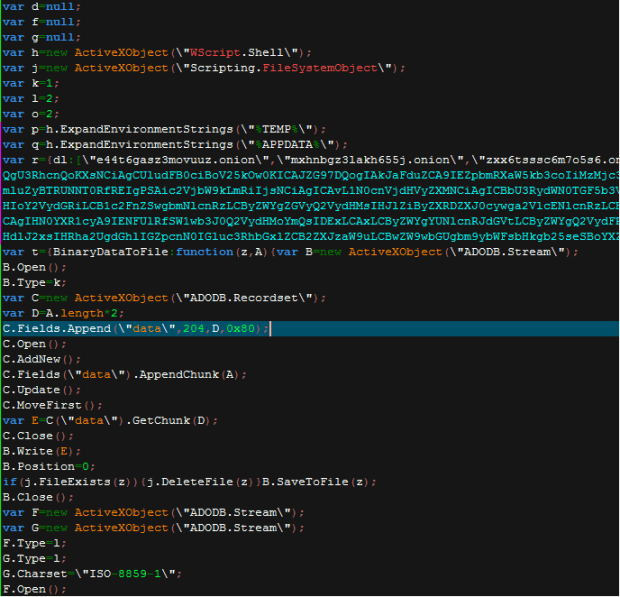
201MalwareLocky now using Embedded RSA Key instead of contacting Command & Control Servers
According to security researcher Timothy Davies, a new version of the Locky Ransomware, aka Zepto, has been circulating since around the September 5th 2016 that...
-
 240Data Security
240Data SecurityDouble-click me not: Malicious proxy settings in OLE Embedded Script
Attackers have been using social engineering to avoid the increasing costs of exploitation due to the significant hardening and exploit mitigations investments...
-
 214Incidents
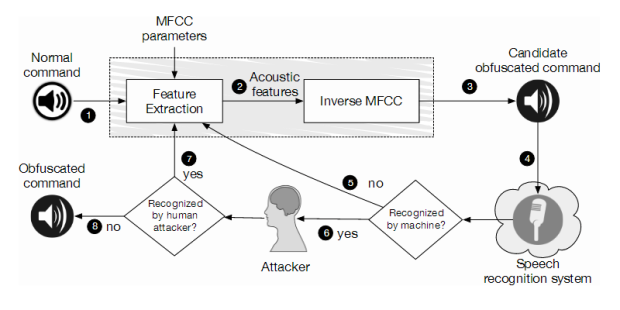
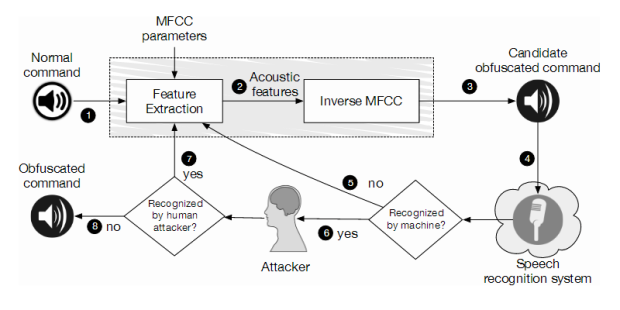
214IncidentsHidden Voice Commands Embedded in YouTube Videos Can Hijack Your Smartphone
Some attacks are hard to spot even by human subjects. A series of distorted voice commands surreptitiously hidden in YouTube videos can force...
-
 212Data Security
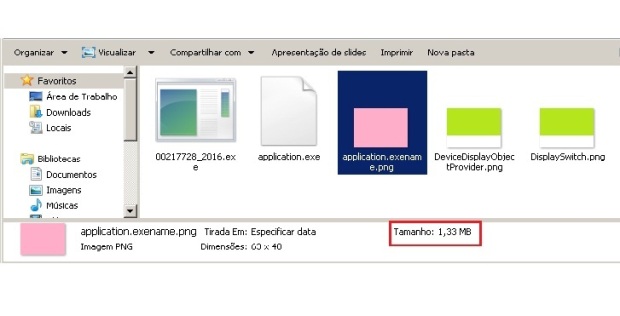
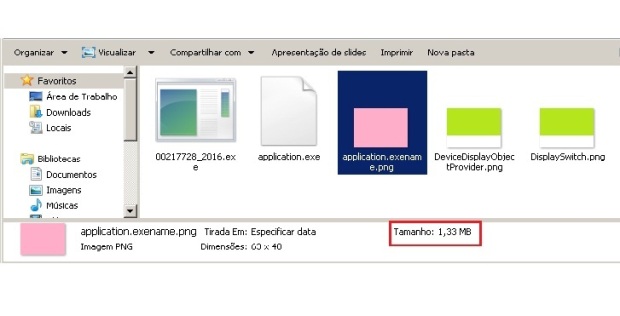
212Data SecurityPNG Embedded – Malicious payload hidden in a PNG file
One of the most complex tasks for the cybercriminals is to ensure their malicious code goes undetected by antivirus and achieves its...
-

 236Data Security
236Data SecurityEmbedded Devices Share, Reuse Private SSH Keys, HTTPs Certificates
Researchers have found that thousands of Internet gateways, routers, modems and other embedded devices share cryptographic keys and certificates, exposing millions of...
-

 382Data Security
382Data SecurityBanking Malware Delivered via Macro in PDF Embedded Word Document
Delivering banking malware through Microsoft Word documents has been a less common method. However, it is currently being used for spreading malicious...






