Search results for "Encryption"
-

 4.4KVulnerabilities
4.4KVulnerabilitiesNew “GoFetch” Vulnerability in Apple M-Series Chips Leaks Secret Encryption Keys
A new security shortcoming discovered in Apple M-series chips could be exploited to extract secret keys used during cryptographic operations. Dubbed GoFetch,...
-

 2.9KMalware
2.9KMalwareKasseika Ransomware Using BYOVD Trick to Disarm Security Pre-Encryption
The ransomware group known as Kasseika has become the latest to leverage the Bring Your Own Vulnerable Driver (BYOVD) attack to disarm...
-

 1.1KData Breach
1.1KData BreachRemote Encryption Attacks Surge: How One Vulnerable Device Can Spell Disaster
Ransomware groups are increasingly switching to remote encryption in their attacks, marking a new escalation in tactics adopted by financially motivated actors...
-

 4.4KData Security
4.4KData SecurityRazor gaming company source code, encryption keys, database and network credentials hacked
Following a buyer on a hackers’ forum offering stolen data for US$100,000 (S$134,898) in bitcoin on Saturday, it is believed that gaming...
-

 1.6KData Security
1.6KData SecurityUK government new bill proposes to remove encryption from WhatsApp and Signal
WhatsApp, owned by Meta, has threatened to quit the United Kingdom in the event that the government adopts the Online Safety Bill,...
-
 3.8KRansomware
3.8KRansomwareRorschach – Fastest Encryption Ransomware Ever Found in Ransomware History
Researchers from Checkpoint found a new and previously unknown ransomware variant dubbed “Rorschach” with highly sophisticated features that target U.S. companies. Rorschach...
-

 5.0KCyber Attack
5.0KCyber AttackLinux Variant of Clop Ransomware Spotted, But Uses Faulty Encryption Algorithm
The first-ever Linux variant of the Clop ransomware has been detected in the wild, but with a faulty encryption algorithm that has...
-
 3.2KMalware
3.2KMalwareVice Society Ransomware Attackers Adopt Robust Encryption Methods
The Vice Society ransomware actors have switched to yet another custom ransomware payload in their recent attacks aimed at a variety of...
-

 4.6KData Security
4.6KData SecurityMessage Encryption (OME) used by Office 365 can easily be broken to read encrypted emails via MiTM
The message encryption system employed by Microsoft in Office 365 has a system vulnerabilities, according to a warning from the Finnish cybersecurity...
-
 1.3KVulnerabilities
1.3KVulnerabilitiesResearchers Say Microsoft Office 365 Uses Broken Email Encryption to Secure Messages
New research has disclosed what’s being called a security vulnerability in Microsoft 365 that could be exploited to infer message contents due...
-
 4.8KMalware
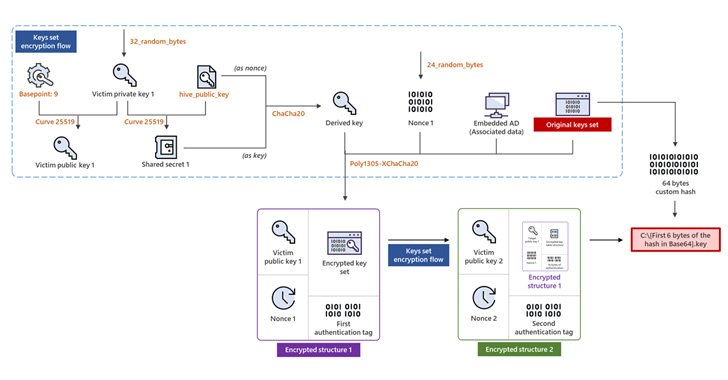
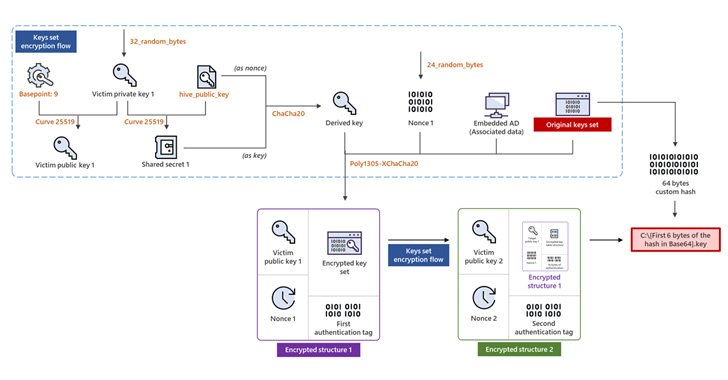
4.8KMalwareHive Ransomware Upgrades to Rust for More Sophisticated Encryption Method
The operators of the Hive ransomware-as-a-service (RaaS) scheme have overhauled their file-encrypting software to fully migrate to Rust and adopt a more...
-

 1.6KVulnerabilities
1.6KVulnerabilitiesTwo critical command injection vulnerabilities in Fujitsu cloud storage system allow remote encryption or deletion of files
Two bugs in the web interface of a Fujitsu cloud storage system would allow authenticated threat actors to read, write, and even...
-

 833Leaks
833LeaksVulnerabilities That Allow Hijacking of Most Ransomware to Prevent File Encryption
A cyber-attack is a malicious attack undertaken by cybercriminals against single or numerous computers, computer systems, networks, or infrastructures utilizing one or...
-

 2.0KMalware
2.0KMalwareResearcher finds DLL hijacking vulnerability in Conti, REvil, LockBit, Black Basta, BitLocker, and AvosLocker ransomware variants that could prevent file encryption
A researcher has detected a critical vulnerability in some of the most common malware and ransomware variants today and whose exploitation would...
-

 3.4KVulnerabilities
3.4KVulnerabilitiesVulnerability in next-generation homomorphic encryption allows data to be stolen even while encrypted
Cybersecurity specialists report the detection of a critical vulnerability in homomorphic encryption, one of the most advanced security technologies today. According to...
-
 4.9KData Security
4.9KData SecurityErrors in the encryption process allow victims of Hive ransomware to recover their information without paying a single dollar to hackers
A bug in the Hive ransomware encryption algorithm would allow victims to recover their information without having to negotiate with hackers. This...
-

 2.4KRansomware
2.4KRansomwareA New Ransomware Dubbed BlackCocaine Uses AES & RSA Encryption Methods
Recently, an Indian IT company that is specialized in the Banking and Financial Services sector, Nucleus Software has suffered a security breach...
-
 2.7KData Security
2.7KData SecurityRemove the DarkSide ransomware encryption with this free tool
Bitdefender’s cybersecurity specialists have released a free tool to remove the encryption provoked by the DarkSide ransomware, allowing victims to recover their...
-

 3.1KPrivacy
3.1KPrivacyZoom to begin rolling out end‑to‑end encryption
The videoconferencing platform is making the feature available to users of both free and paid tiers
-
 1.5KPrivacy
1.5KPrivacyHow encryption can help protect your sensitive data
Here’s how encryption can help keep your data safe from prying eyes – even if your device is stolen or your cloud...
-

 3.1KNews
3.1KNewsKr00k Attack: New Wifi Encryption Vulnerability Affects Over Billion Devices
Cybersecurity researchers today discovered a new high-risk hardware vulnerability named kr00k or Kr00k Attack that is present in widely used Wi-Fi chips...






