Search results for "Exploiting"
-

 3.3KVulnerabilities
3.3KVulnerabilitiesWebinar: Learn How to Stop Hackers from Exploiting Hidden Identity Weaknesses
We all know passwords and firewalls are important, but what about the invisible threats lurking beneath the surface of your systems? Identity...
-

 964Malware
964MalwareTheMoon Botnet Resurfaces, Exploiting EoL Devices to Power Criminal Proxy
A botnet previously considered to be rendered inert has been observed enslaving end-of-life (EoL) small home/small office (SOHO) routers and IoT devices...
-

 3.0KMalware
3.0KMalwareBianLian Threat Actors Exploiting JetBrains TeamCity Flaws in Ransomware Attacks
The threat actors behind the BianLian ransomware have been observed exploiting security flaws in JetBrains TeamCity software to conduct their extortion-only attacks....
-

 3.9KMalware
3.9KMalwareHow Cybercriminals are Exploiting India’s UPI for Money Laundering Operations
Cybercriminals are using a network of hired money mules in India using an Android-based application to orchestrate a massive money laundering scheme....
-
 147Malware
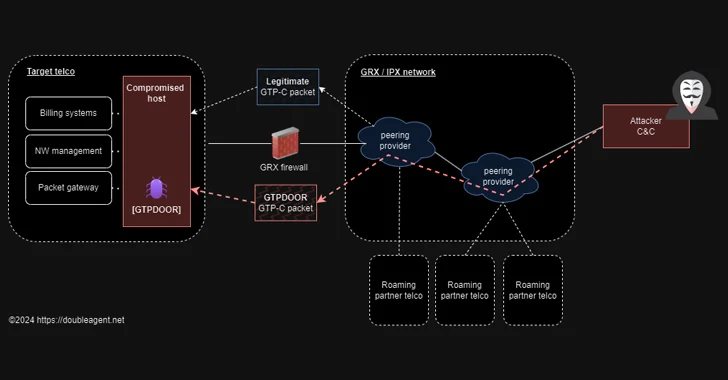
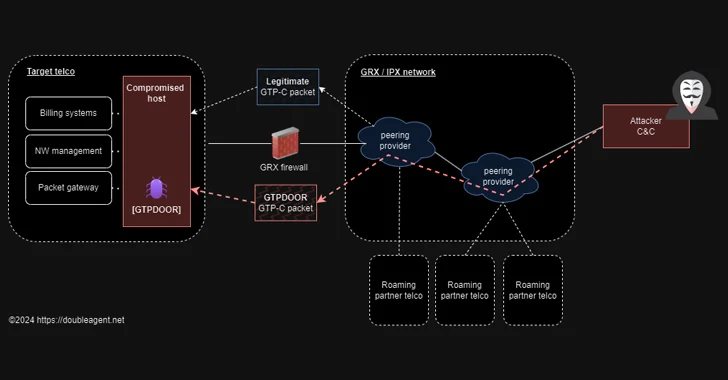
147MalwareGTPDOOR Linux Malware Targets Telecoms, Exploiting GPRS Roaming Networks
Threat hunters have discovered a new Linux malware called GTPDOOR that’s designed to be deployed in telecom networks that are adjacent to...
-

 2.3KVulnerabilities
2.3KVulnerabilitiesChinese Hackers Exploiting Ivanti VPN Flaws to Deploy New Malware
At least two different suspected China-linked cyber espionage clusters, tracked as UNC5325 and UNC3886, have been attributed to the exploitation of security...
-

 1.5KMalware
1.5KMalwareNew Mispadu Banking Trojan Exploiting Windows SmartScreen Flaw
The threat actors behind the Mispadu banking Trojan have become the latest to exploit a now-patched Windows SmartScreen security bypass flaw to...
-
 1.9KMalware
1.9KMalwareWarning: New Malware Emerges in Attacks Exploiting Ivanti VPN Vulnerabilities
Google-owned Mandiant said it identified new malware employed by a China-nexus espionage threat actor known as UNC5221 and other threat groups during...
-

 3.7KVulnerabilities
3.7KVulnerabilitiesHackers Exploiting Ivanti VPN Flaws to Deploy KrustyLoader Malware
A pair of recently disclosed zero-day flaws in Ivanti Connect Secure (ICS) virtual private network (VPN) devices have been exploited to deliver...
-
 3.6KData Security
3.6KData SecurityHow to steal Windows password via Outlook email exploiting vulnerabilities in Windows Performance Analyzer (WPA) and File Explorer
Varonis Threat Labs has uncovered a significant vulnerability in Microsoft Outlook (CVE-2023-35636) that allows attackers to access NTLM v2 hashed passwords. This...
-
 2.2KData Breach
2.2KData Breach29-Year-Old Ukrainian Cryptojacking Kingpin Arrested for Exploiting Cloud Services
A 29-year-old Ukrainian national has been arrested in connection with running a “sophisticated cryptojacking scheme,” netting them over $2 million (€1.8 million)...
-
 2.0KVulnerabilities
2.0KVulnerabilitiesHackers Exploiting MS Excel Vulnerability to Spread Agent Tesla Malware
Attackers are weaponizing an old Microsoft Office vulnerability as part of phishing campaigns to distribute a strain of malware called Agent Tesla....
-

 558Malware
558Malware8220 Gang Exploiting Oracle WebLogic Server Vulnerability to Spread Malware
The threat actors associated with the 8220 Gang have been observed exploiting a high-severity flaw in Oracle WebLogic Server to propagate their...
-
 949Vulnerabilities
949VulnerabilitiesHacking the Human Mind: Exploiting Vulnerabilities in the ‘First Line of Cyber Defense’
Humans are complex beings with consciousness, emotions, and the capacity to act based on thoughts. In the ever-evolving realm of cybersecurity, humans...
-

 5.0KVulnerabilities
5.0KVulnerabilitiesMicrosoft Warns of Kremlin-Backed APT28 Exploiting Critical Outlook Vulnerability
Microsoft on Monday said it detected Kremlin-backed nation-state activity exploiting a now-patched critical security flaw in its Outlook email service to gain...
-

 1.6KVulnerabilities
1.6KVulnerabilitiesGoTitan Botnet Spotted Exploiting Recent Apache ActiveMQ Vulnerability
The recently disclosed critical security flaw impacting Apache ActiveMQ is being actively exploited by threat actors to distribute a new Go-based botnet...
-

 2.1KVulnerabilities
2.1KVulnerabilitiesZero-Day Alert: Google Chrome Under Active Attack, Exploiting New Vulnerability
Google has rolled out security updates to fix seven security issues in its Chrome browser, including a zero-day that has come under...
-

 4.1KVulnerabilities
4.1KVulnerabilitiesMirai-based Botnet Exploiting Zero-Day Bugs in Routers and NVRs for Massive DDoS Attacks
An active malware campaign is leveraging two zero-day vulnerabilities with remote code execution (RCE) functionality to rope routers and video recorders into...
-

 3.0KVulnerabilities
3.0KVulnerabilitiesLockBit Ransomware Exploiting Critical Citrix Bleed Vulnerability to Break In
Multiple threat actors, including LockBit ransomware affiliates, are actively exploiting a recently disclosed critical security flaw in Citrix NetScaler application delivery control...
-

 878Vulnerabilities
878VulnerabilitiesExperts Uncover DarkCasino: New Emerging APT Threat Exploiting WinRAR Flaw
A hacking group that leveraged a recently disclosed security flaw in the WinRAR software as a zero-day has now been categorized as...
-

 2.6KVulnerabilities
2.6KVulnerabilitiesSideCopy Exploiting WinRAR Flaw in Attacks Targeting Indian Government Entities
The Pakistan-linked threat actor known as SideCopy has been observed leveraging the recent WinRAR security vulnerability in its attacks targeting Indian government...






