Search results for "Fingerprinting"
-

 4.1KVulnerabilities
4.1KVulnerabilitiesCritical vulnerability in Slack allows fingerprinting attacks on users
Cybersecurity specialists report the detection of a security flaw in the file sharing feature in Slack whose exploitation would allow threat actors...
-

 468Malware
468MalwareESET discovers Attor, a spy platform with curious GSM fingerprinting
ESET researchers discover a previously unreported cyberespionage platform used in targeted attacks against diplomatic missions and governmental institutions, and privacy-concerned users
-

 511Data Breach
511Data BreachBiometric Security Platform Data Breach Leaked Millions of Users Facial Recognition & Fingerprinting Data
Security researchers discovered the biggest data breach in Biometric Security Platform BioStar 2 that leaks millions of users facial recognition records, fingerprints,...
-

 363News
363NewsTor’s Anti-Fingerprinting Technique ‘Letterboxing’ Coming To Firefox 67
Once again, Mozilla has taken a leaf out of Tor browser’s handbook with the introduction of user anti-fingerprinting technique in Firefox 67...
-

 364Data Security
364Data SecurityUpcoming Firefox version to offer fingerprinting & cryptomining protection
There is very good news for Mozilla Firefox users. After improving the user experience with tracking protection function offering content blocking features...
-

 327Reviews
327ReviewsOnePlus 6T Review: Upping The Game With In-Display Fingerprinting
Back then, 2014 to be precise, OnePlus was a newbie, only to rule the mid-to-high segment in the mobile world after a...
-
 229Information Gathering
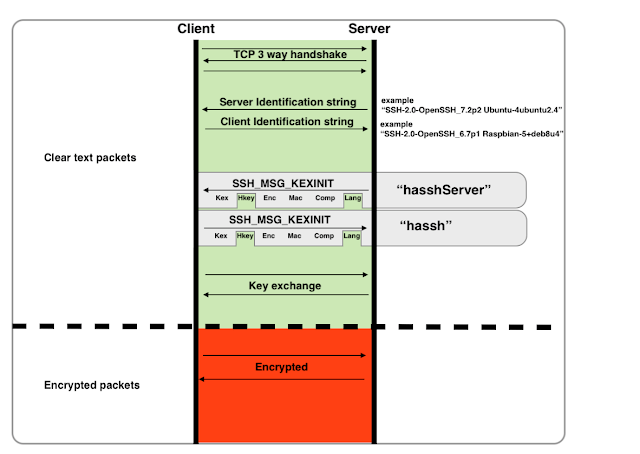
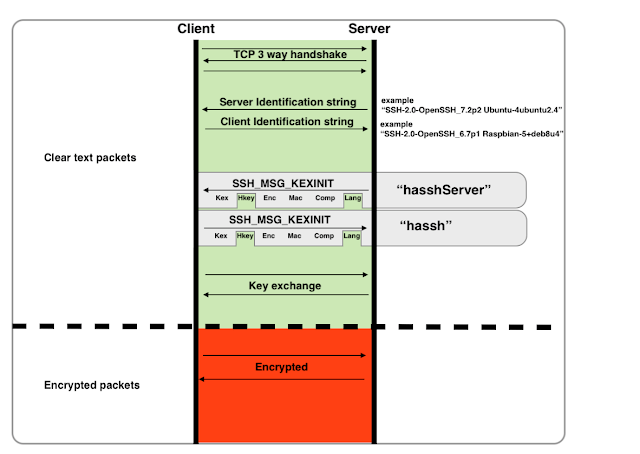
229Information GatheringHASSH – A Network Fingerprinting Standard Which Can Be Used To Identify Specific Client And Server SSH Implementations
“HASSH” is a network fingerprinting standard which can be used to identify specific Client and Server SSH implementations. The fingerprints can be...
-

 265Information Gathering
265Information GatheringScannerl – The Modular Distributed Fingerprinting Engine
Scannerl is a modular distributed fingerprinting engine implemented by Kudelski Security. Scannerl can fingerprint thousands of targets on a single host, but...
-

 289Information Gathering
289Information GatheringPlecost – WordPress Fingerprinting Tool
Plecost is a vulnerability fingerprinting and vulnerability finder for WordPress blog engine. Installation Using Pypi: > python3 -m pip install plecost Remember...
-
 250Information Gathering
250Information GatheringScannerl – Modular Distributed Fingerprinting Engine
Scannerl is a modular distributed fingerprinting engine implemented by Kudelski Security. Scannerl can fingerprint thousands of targets on a single host, but can...
-
 227Vulnerabilities
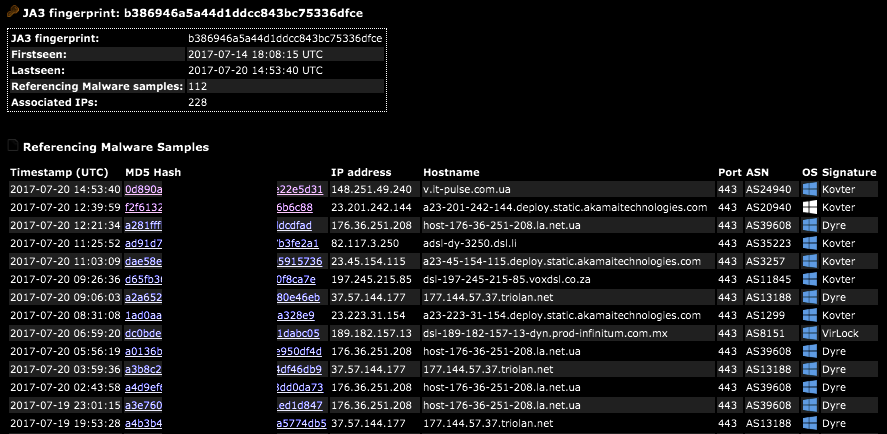
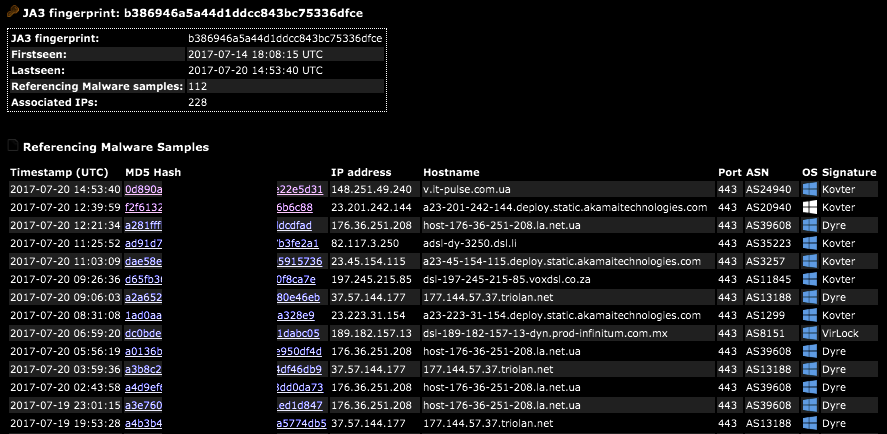
227VulnerabilitiesSSL/TLS Client Fingerprinting for Malware Detection
A JA3 hash represents the fingerprint of an SSL/TLS client application as detected via a network sensor or device, such as Bro...
-
 307Hacked
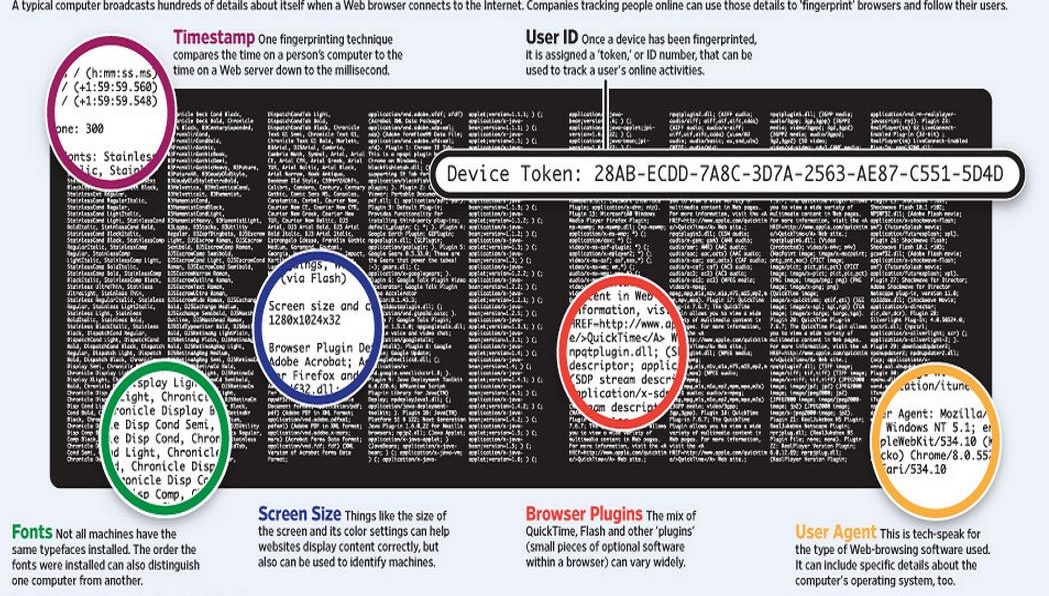
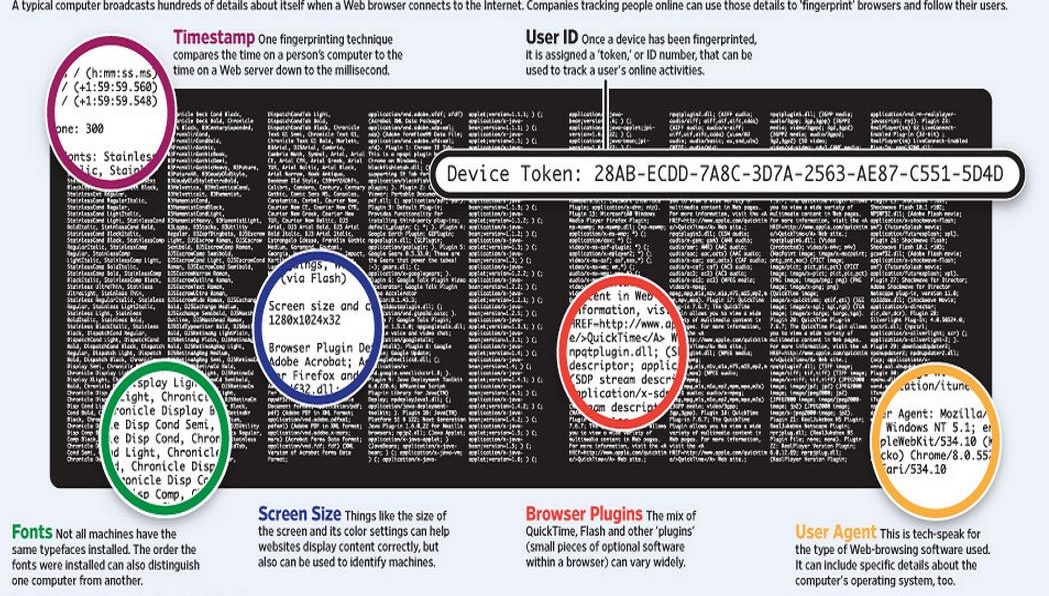
307HackedWhat is Traffic Fingerprinting and How it is Used to Attack Tor Network
Short Bytes: Traffic fingerprinting is a technique used to sniff the web traffic by analyzing the data packets’ flow pattern- without removing...
-
Malware
Open Source Malware Fingerprinting – Free Tool
In my ever-widening circle of anti-cybercrime methodology this particular approach to attribution of the criminals looting the free world makes me particularly...






