Search results for "History"
-
 3.8KRansomware
3.8KRansomwareRorschach – Fastest Encryption Ransomware Ever Found in Ransomware History
Researchers from Checkpoint found a new and previously unknown ransomware variant dubbed “Rorschach” with highly sophisticated features that target U.S. companies. Rorschach...
-

 5.5KData Security
5.5KData SecurityThe biggest crypto scam in Instagram history
Jason Sallman is a cryptocurrency investment advisor who enjoys considerable popularity on social media, primarily Instagram, where he has nearly 40,000 followers....
-

 5.1KIncidents
5.1KIncidents20TB torrents containing every NFT on the Internet available for download. Biggest NFT theft of the history
Bad news for digital art tokens owners. This weekend, Australian user Geoffrey Huntley put online a website in which he assures that...
-

 1.5KDDOS
1.5KDDOSNew Mēris Botnet Hits Yandex Search Engine With 21.8 Million RPS – Biggest DDoS Attack on Yandex History
Recently, it has been reported that Yandex was experiencing a massive DDoS attack from the Mēris botnet. this attack was denominated as...
-

 1.0KIncidents
1.0KIncidentsMore than a billion personal records leaked. The biggest data breach in history
Data breaches have become routine, although each new reported incident seems to more seriously affect a larger number of users. Data protection...
-

 5.4KData Security
5.4KData Security2019 will be known as the year with the most cyberattacks in history
Information security experts anticipate that the balance in cybersecurity by the end of 2019 will be disastrous. According to figures collected up...
-

 390Data Breach
390Data BreachIT Firm Manager Arrested in the Biggest Data Breach Case of Ecuador’s History
Ecuador officials have arrested the general manager of IT consulting firm Novaestrat after the personal details of almost the entire population of...
-

 410Vulnerabilities
410VulnerabilitiesNew vulnerability in Kaspersky antivirus makes browsing history of millions of people public
Antivirus solutions are one of the basic protection tools for computer users; however, this software is not safe from flaws that alter...
-

 289Data Breach
289Data BreachRussia’s Secret Intelligence Agency Hacked – One of the Largest Hack in the Russian Secret Service History
Hackers compromised the Russian Federal Security Service (FSB) servers where they gained access to 7.5 terabytes of data from a major FSB contractor named...
-

 455News
455NewsHow To Auto-Delete Google’s ‘Location History’ Tracking Data?
Back in May 2019, Google promised that it would let you auto-delete the web activity and location history it collects through your...
-

 738Malware
738Malware4 Most Memorable Botnet In History
What is Botnets? Botnets are artificial networks created by malware, which can be controlled by the virus author remotely. Here in Hackercombat.com,...
-
 289Data Security
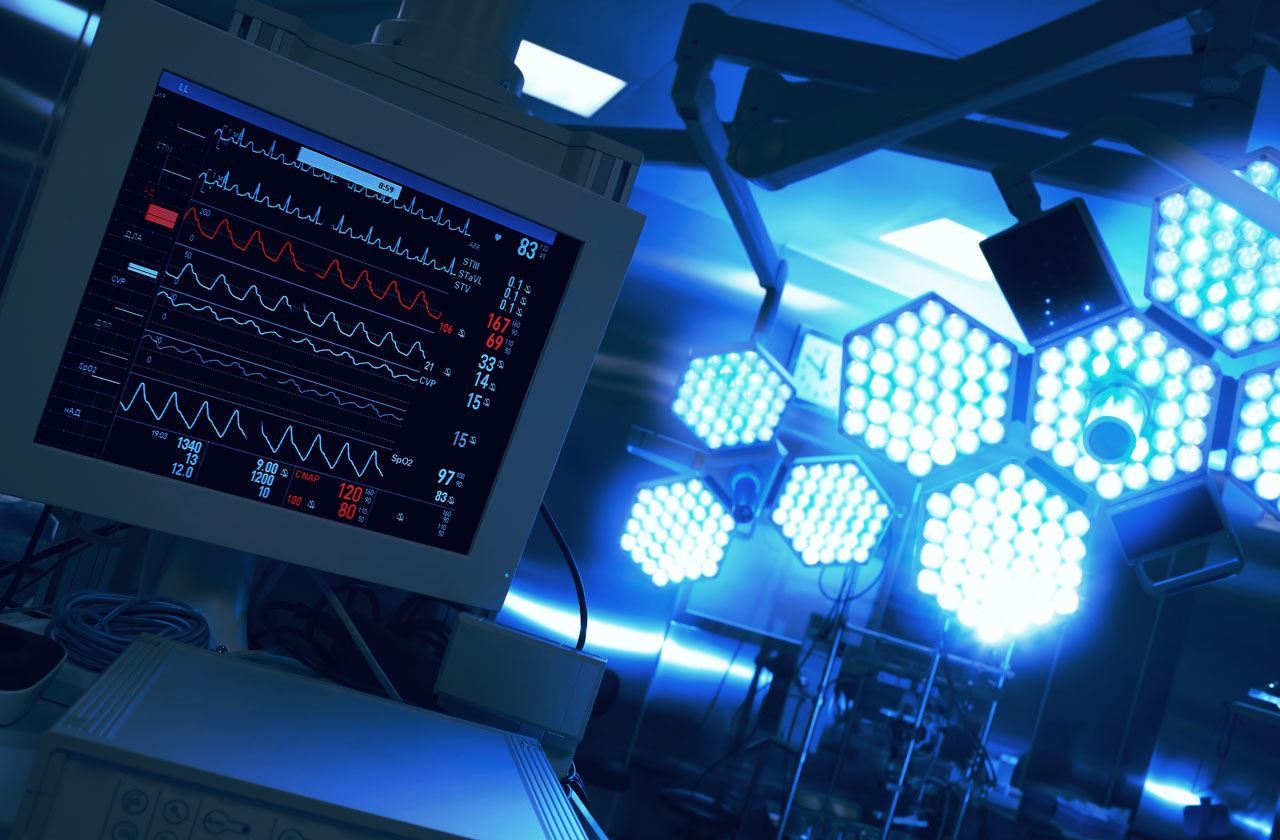
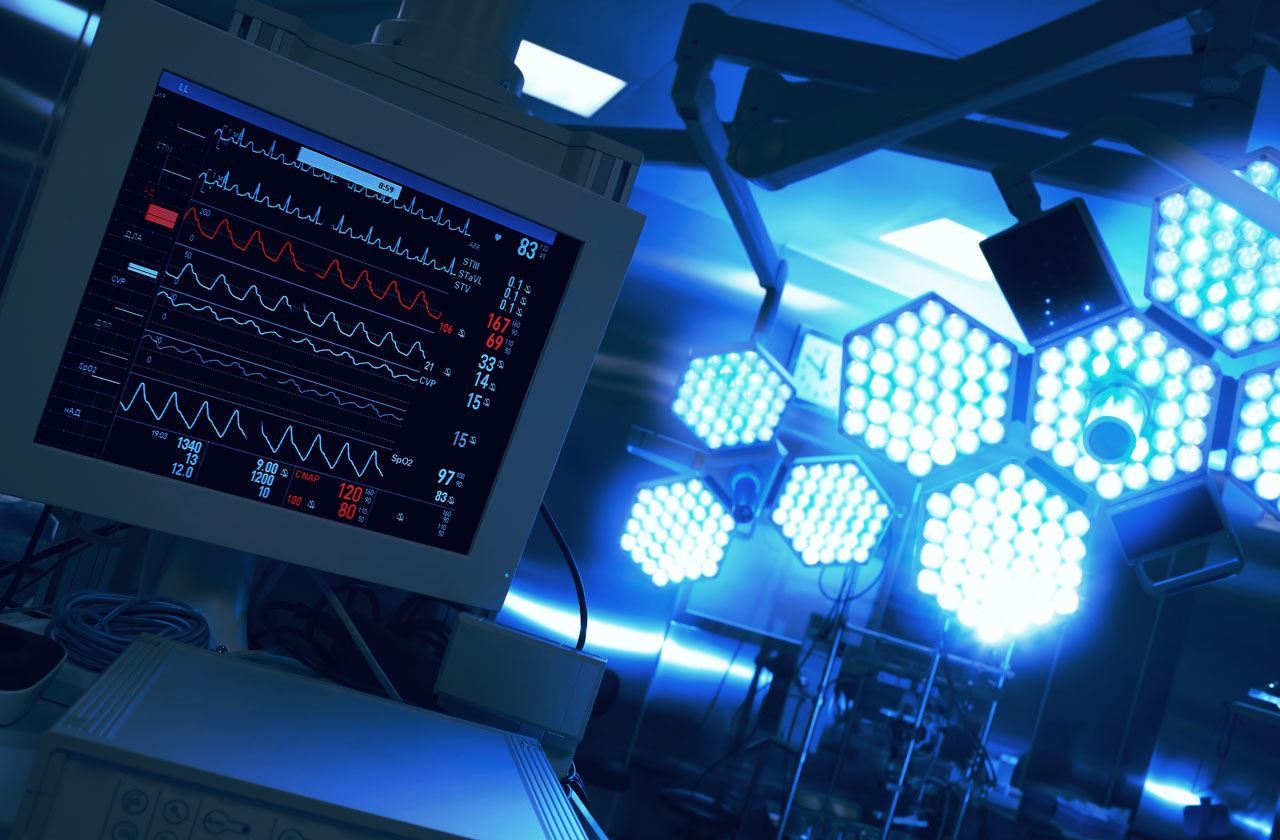
289Data SecurityWhy are hackers interested in people’s medical history?
A few days ago, information security specialists reported a massive data breach in American Medical Collections Agency (AMCA) that affected nearly 20...
-

 271News
271NewsMicrosoft Wanted To Create History With UWP; Now It’s Turning Back
The UWP is dead. That’s what the internet and various reports have started to say about the platform. In addition to many...
-

 330News
330NewsGoogle Helps Identify Crime Suspects Using Location History
Google, by using the location data in devices, helps identify suspects of crimes in many instances of criminal investigation. Google keeps tracking...
-

 226News
226NewsCops Are Increasingly Using Google’s Location History Data To Nab Criminals
A New York Times report has revealed that federal agencies and cops use Google’s location history data trove to keep an eye...
-
 239Vulnerabilities
239VulnerabilitiesGoogle Photos Vulnerability Allows Hackers To Track Location History
A vulnerability exists with the web version of Google photos allows malicious websites to extract the photos metadata information. Google photos will...
-

 904DDOS
904DDOSFacebook Suffers Biggest Ever Outage in its History
Facebook, which has suffered the biggest ever outage in its history, is struggling to deal with it. The partial outage that affected...
-

 272News
272NewsGoogle Maps Will Bring A Feature To Automatically Delete Location History
Back at CES 2019, Google introduced a couple of features for its Maps app, and it appears we are most likely to...
-

 307Vulnerabilities
307VulnerabilitiesSafari vulnerability allows stealing your browsing history
To exploit the vulnerability, attackers need physical access to the computer, as well as installing a malicious application Network security and ethical...
-

 216Malware
216MalwareNew Unpatched macOS Flaw Allow Hackers to Spy on Safari Browser History
Security Researcher discovered a vulnerability in macOS Mojave let malware apps bypass the privacy protection and read the safari browser web history....
-

 187Articles
187ArticlesNew Unpatched macOS Flaw Lets Apps Spy On Your Safari Browsing History
A new security vulnerability has been discovered in the latest version of Apple’s macOS Mojave that could allow a malicious application to...






