Search results for "HoneyPot"
-
 4.9KCyber Crime
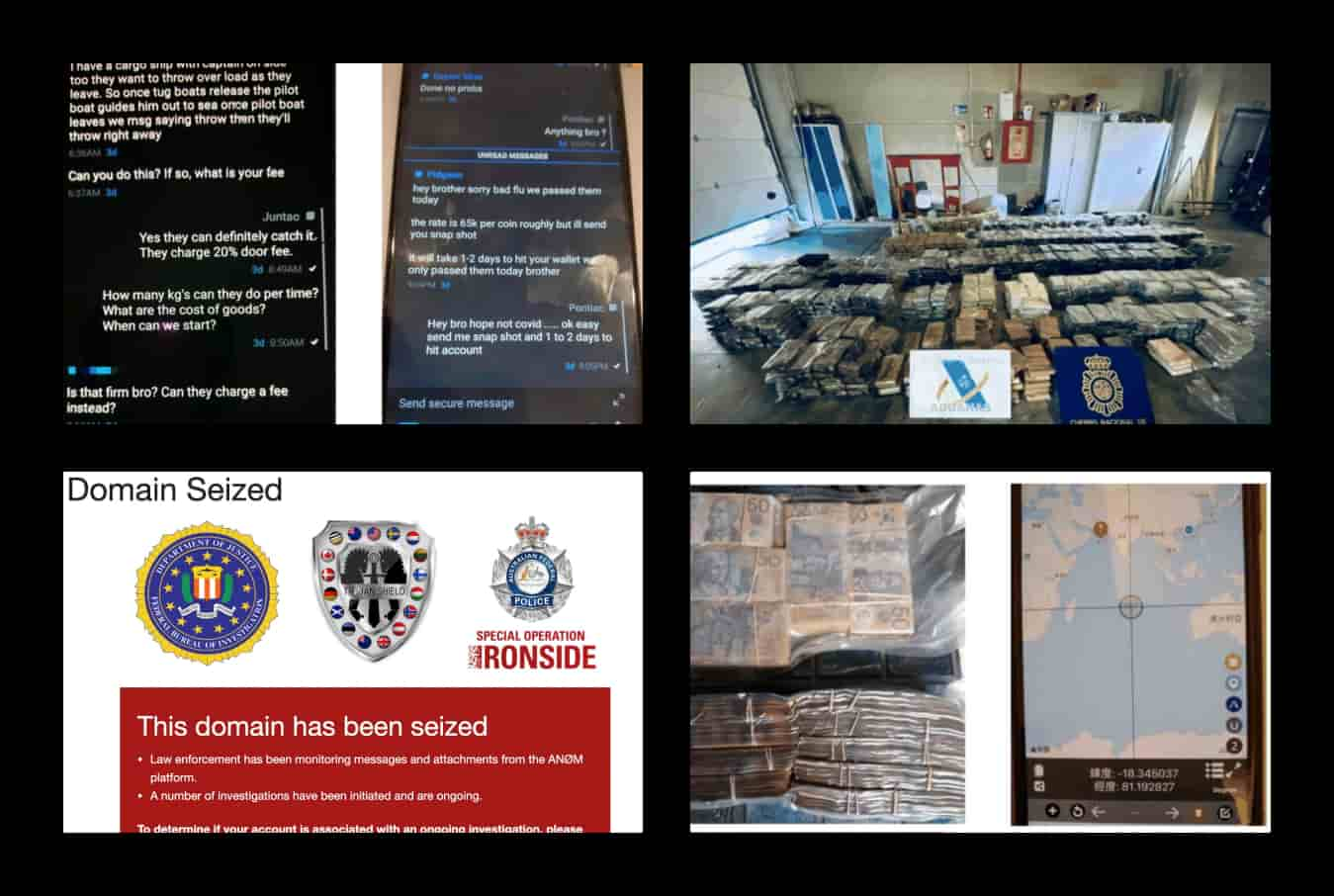
4.9KCyber Crime800+ criminals arrested after FBI turned Anom app into honeypot
Generally, agencies crack messages or seize an already available encrypted communication platform to keep track of cybercriminals. Two such examples would be...
-
 2.9KMobile Security
2.9KMobile SecurityHosTaGe – Low Interaction Mobile Honeypot
HosTaGe is a lightweight, low-interaction, portable, and generic honeypot for mobile devices that aims on the detection of malicious, wireless network...
-
 3.7KExploitation Tools
3.7KExploitation ToolsSnare – Super Next Generation Advanced Reactive honEypot
snare – Super Next generation Advanced Reactive honEypot Super Next generation Advanced Reactive honEypot About SNARE is a web application honeypot...
-
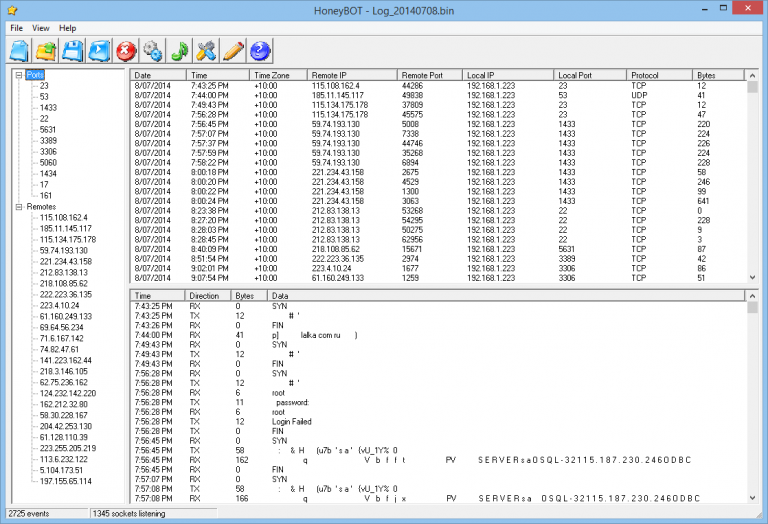
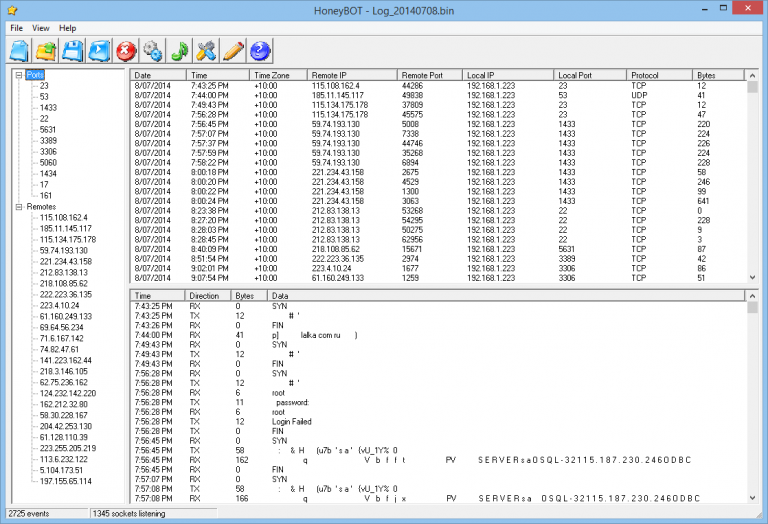 243Honeypot
243HoneypotHoneyBOT – Windows Medium Interaction Honeypot
Honeypot creates a safe environment to capture and interact with unsolicited and often malicious traffic on a network. HoneyBOT is an easy...
-

 253Hack Tools
253Hack ToolsCanaryTokens – Implant Honeypots in your Network
Network breaches happen. From mega-corps, to governments. From unsuspecting grandmas to well known security pros. This is (kinda) excusable. What isn’t excusable,...
-

 352Hack Tools
352Hack ToolsKippo – SSH Honeypot
Kippo is a medium interaction SSH honeypot designed to log brute force attacks and, most importantly, the entire shell interaction performed by...
-
 426Honeypot
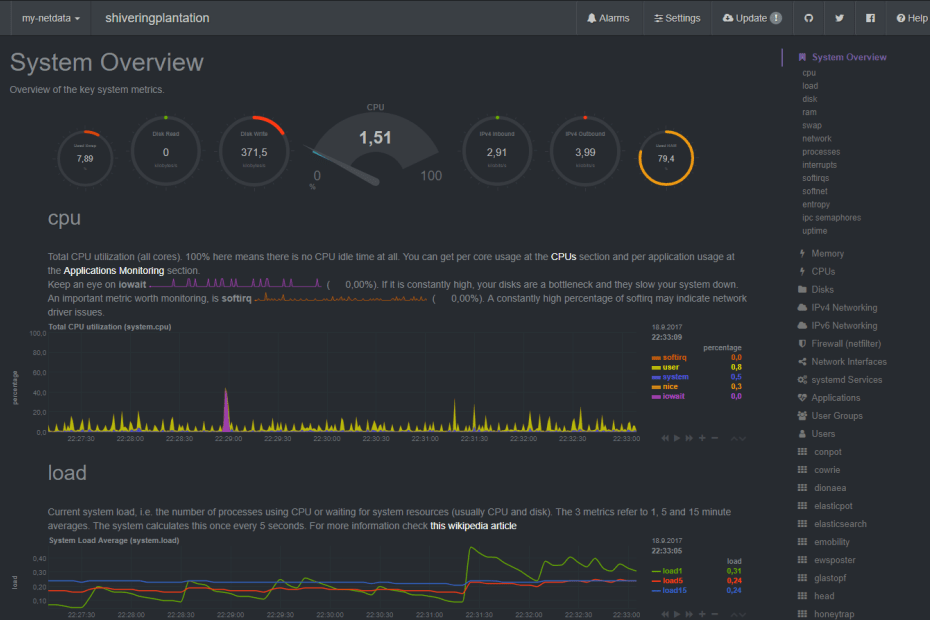
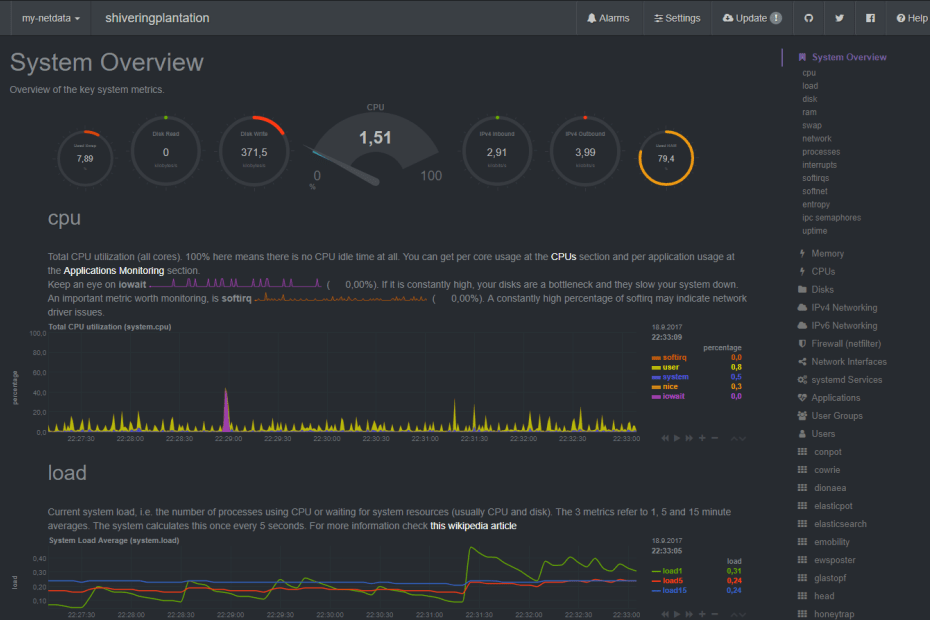
426HoneypotT-Pot Linux – Multi Honeypot Platform
T-Pot is based on debian. The honeypot daemons as well as other support components being used have been paravirtualized using docker. This...
-

 256Tutorials
256Tutorialshoneypot: Use it for catching hackers
Nowdays internal & external networks are not secure, explain ethical hacking researchers. That’s why various security policies are implemented on networking level...
-

 253Exploitation Tools
253Exploitation ToolsHoneyPy – A Low To Medium Interaction Honeypot
A low interaction honeypot with the capability to be more of a medium interaction honeypot. HoneyPy is written in Python2 and is...
-
 375Honeypot
375HoneypotT-Pot – Multi Honeypot Platform
T-Pot is based on Ubuntu Server 16.10 LTS. The honeypot daemons as well as other support components being used have been paravirtualized using...
-
 265Hack Tools
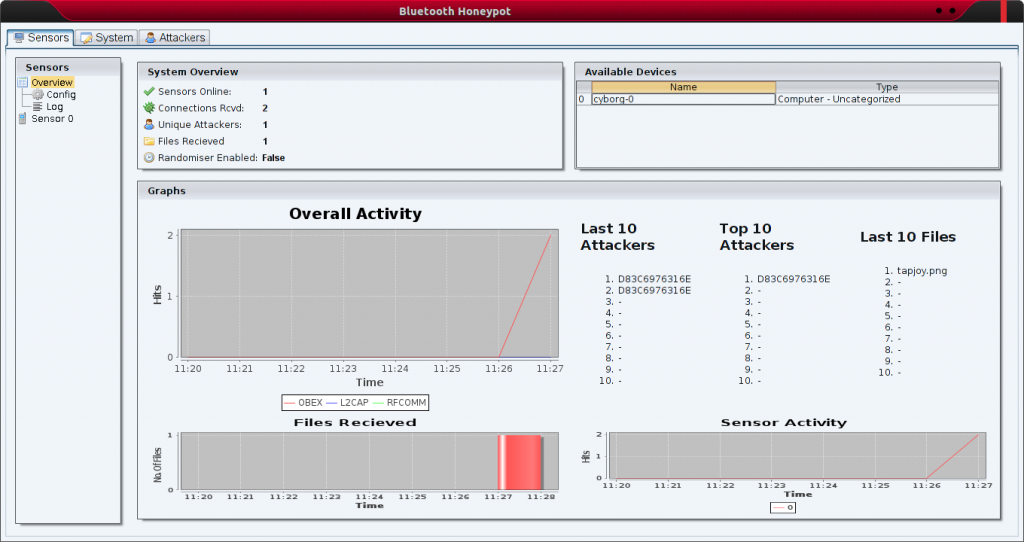
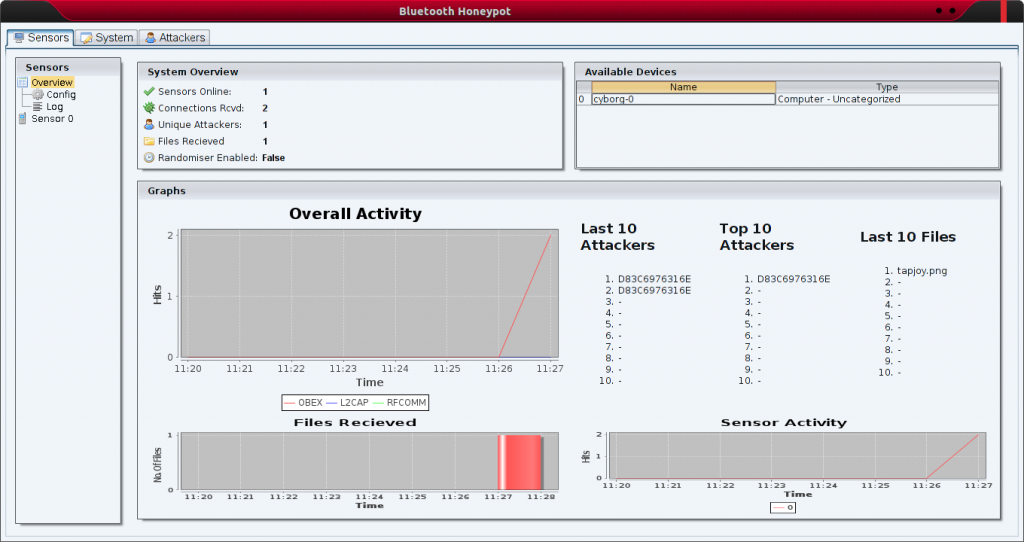
265Hack ToolsBluepot – Bluetooth Honeypot
Bluepot was a third year university project attempting to implement a fully functional Bluetooth Honeypot. A piece of software designed to accept...
-
 204Data Security
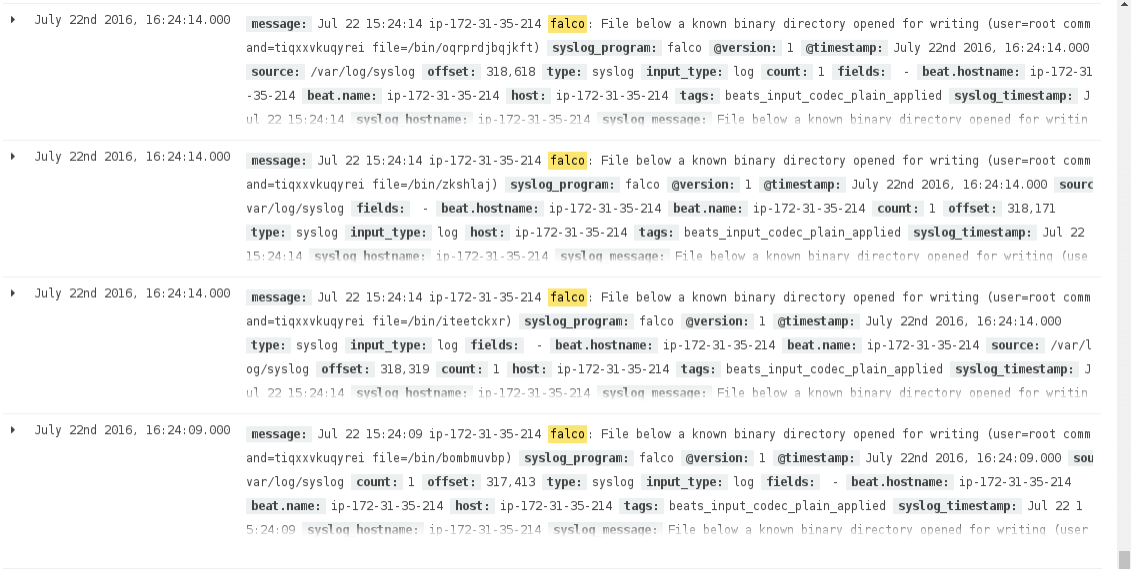
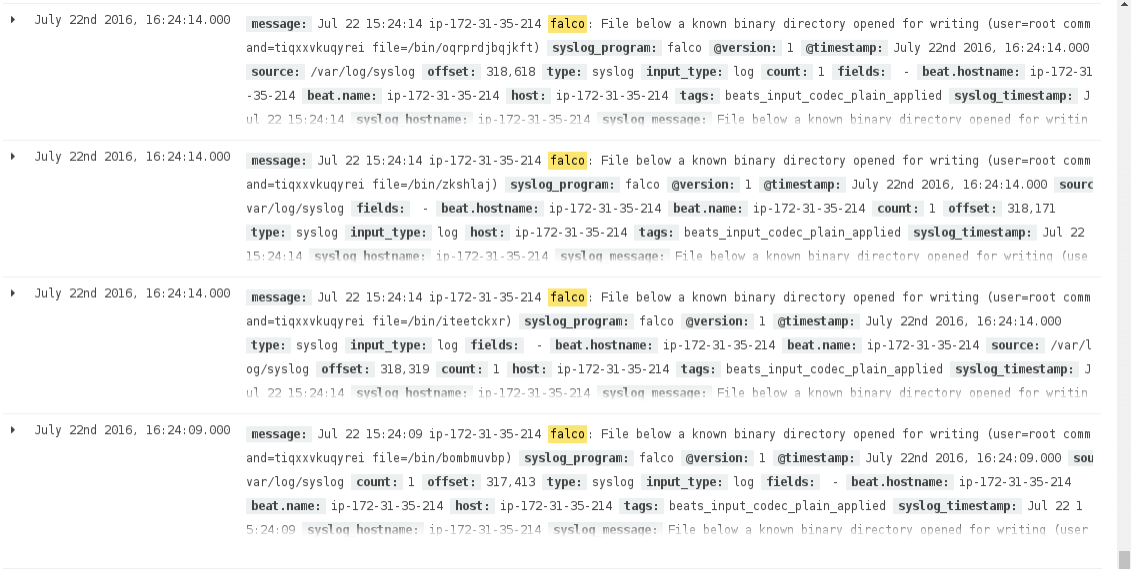
204Data SecurityHigh Interaction Honeypots with Sysdig and Falco
As well as doing training, challenges and shadowing engagements, MWR interns conduct research projects into a range of areas. The purpose of this...
-
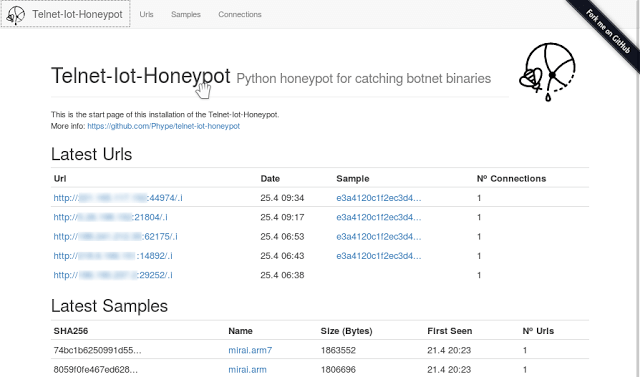
 232Exploitation Tools
232Exploitation ToolsTelnet IoT Honeypot – Python Telnet Honeypot For Catching Botnet Binaries
This project implements a python telnet server trying to act as a honeypot for IoT Malware which spreads over horribly insecure default...
-
 300Honeypot
300HoneypotHoneyDrive – A Honeypot Linux Distribution
HoneyDrive is a Xubuntu-based open-source and premier honeypot bundle Linux operating system. It is a pre-configured honeypot system in a virtual hard disk drive (VMDK...
-
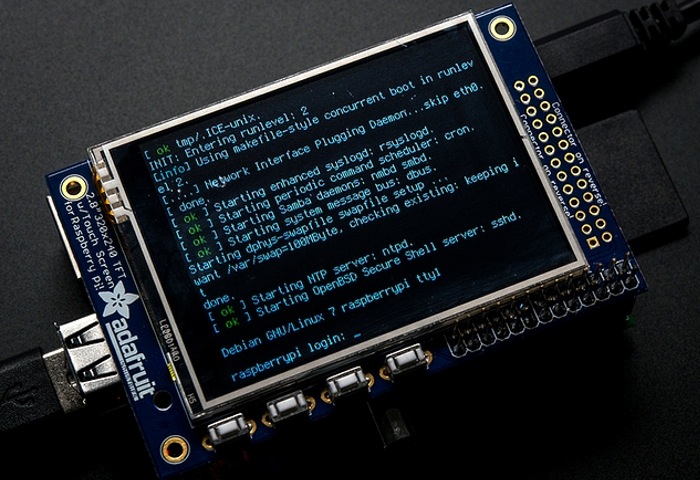
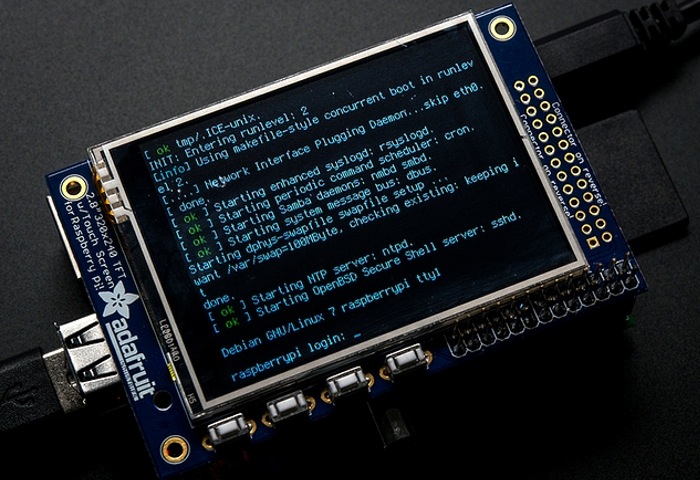 227Honeypot
227HoneypotHoneyPi – Build your own reliable Honeypot
It is astonishingly easy as an attacker to move around on most networks undetected. Let’s face it, unless your organization is big...
-
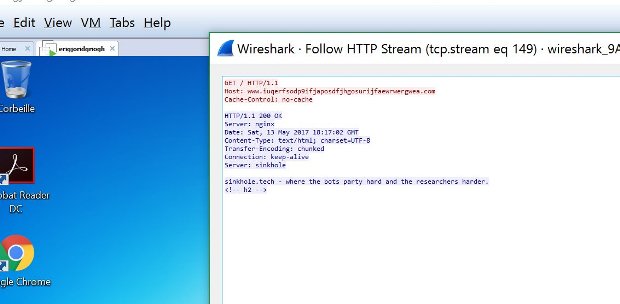
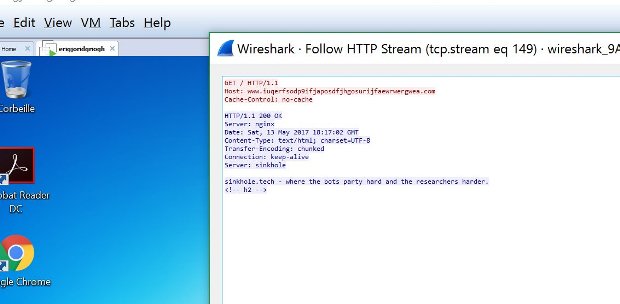 213Malware
213MalwareHoneypot Server Gets Infected with WannaCry Ransomware 6 Times in 90 Minutes
The WannaCry ransomware — also known as WCry, Wana Decrypt0r, WannaCrypt, and WanaCrypt0r — infected a honeypot server made to look like...
-

 364Hacked
364HackedTor Honeypot: How to Hack True Identity of Tor Users
Tor is a free software that is widely used by people to protect their identity and avoid network surveillance. The Onion Router...






