Search results for "Incident Response"
-

 2.3KCyber Attack
2.3KCyber AttackLearn How to Build an Incident Response Playbook Against Scattered Spider in Real-Time
In the tumultuous landscape of cybersecurity, the year 2023 left an indelible mark with the brazen exploits of the Scattered Spider threat...
-

 2.4KTutorials
2.4KTutorialsHow to collect only valid evidence during forensic investigation and incident response processes instead of creating images of system memory
The cybersecurity community understands as cyber forensics the procedures and methodological techniques to identify, collect, preserve, extract, interpret, document and present the...
-
 748Hack Tools
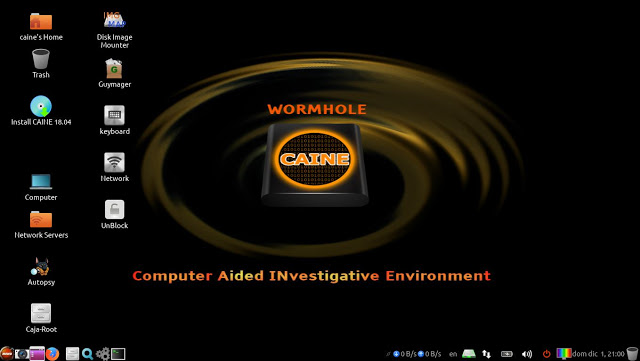
748Hack ToolsCAINE 11 – GNU/Linux Live Distribution For Digital Forensics Project, Windows Side Forensics And Incident Response
CAINE (Computer Aided INvestigative Environment) is an Italian GNU/Linux live distribution created as a Digital Forensics project. Currently, the project manager is Nanni Bassetti...
-
 1.2KTutorials
1.2KTutorialsDigital forensics tools for Windows 10 Forensics and incident response
Windows is the most common operating system. There are many organizations who prefer windows OS. Windows is also most targeted operating system...
-
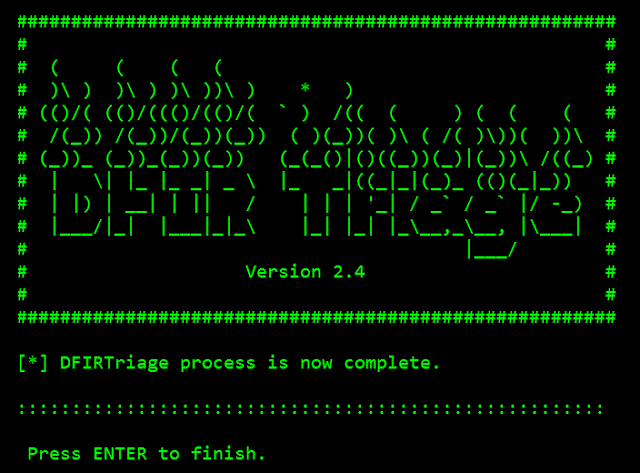
 2.4KHack Tools
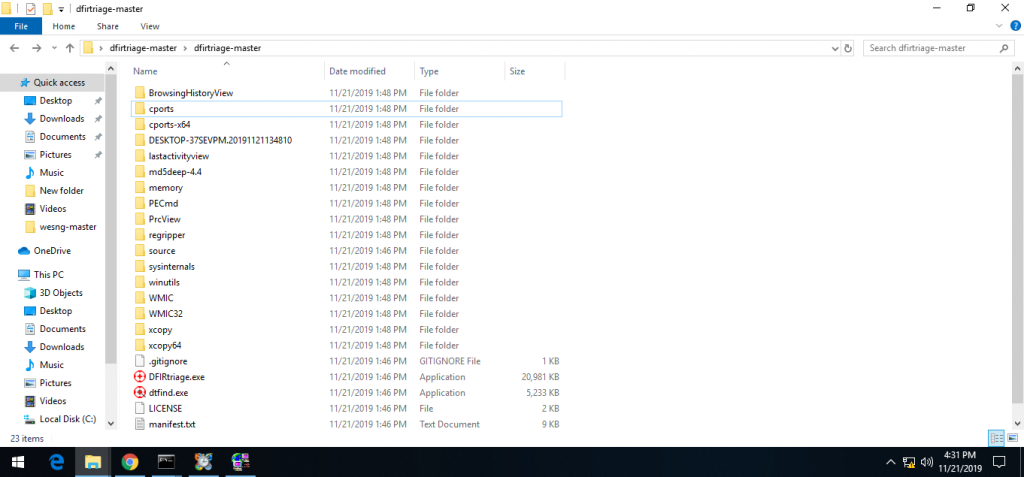
2.4KHack ToolsDFIRtriage – Digital Forensic Acquisition Tool For Windows Based Incident Response
DFIRtriage is a tool intended to provide Incident Responders with rapid host data. Written in Python, the code has been compiled to...
-

 2.3KPrivacy
2.3KPrivacyThe Five Incident Response Steps
It is important to remember that implementing incident response steps is a process and not an isolated event. For a truly successful...
-

 2.0KLeaks
2.0KLeaksBuilding Your Incident Response Team
In order for an organization to properly respond to a breach or incident, they need to have a proper incident response team....
-
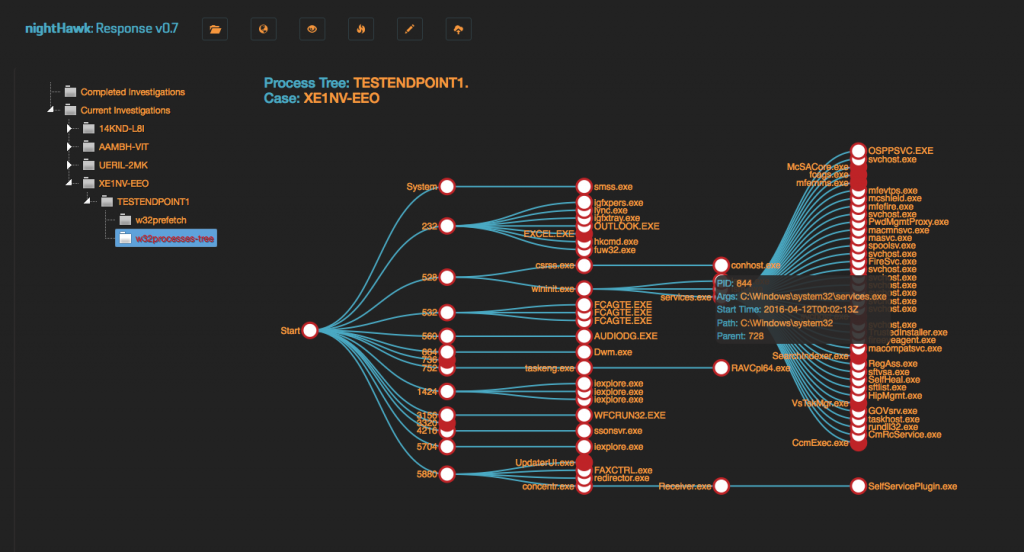
 358Incident Response
358Incident ResponsenightHawkResponse – Incident Response Framework
nightHawkResponse is a custom built application for asynchronus forensic data presentation on an Elasticsearch backend. This application is designed to ingest a...
-
 331Computer Forensics
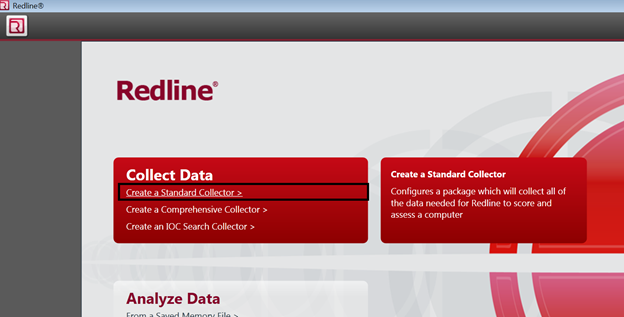
331Computer ForensicsRedline – Digital Forensics and Incident Response Framework
Redline provides host investigative capabilities to users to find signs of malicious activity through memory and file analysis and the development of...
-

 223Hack Tools
223Hack ToolsAMIRA – Automated Malware Incident Response & Analysis
AMIRA is a service for automatically running the analysis on the OSXCollector output files. The automated analysis is performed via OSXCollector Output...
-
 319Incident Response
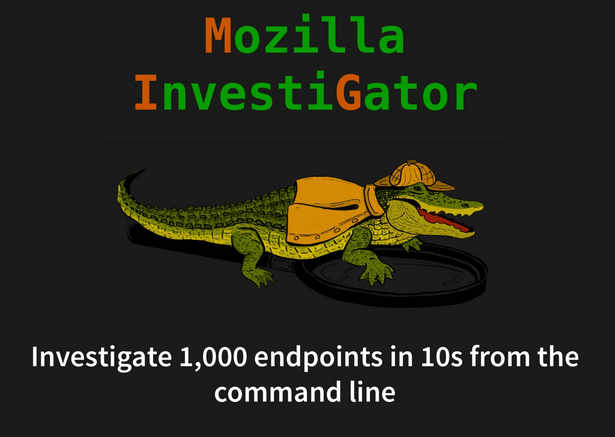
319Incident ResponseMIG – Real-time Incident Response and Investigation Platform
Mozilla Investigator MIG is a platform to perform investigative surgery on remote endpoints. It enables investigators to obtain information from large numbers...
-

 476Hack Tools
476Hack ToolsMost Important Cyber Incident Response Tools List for Security Professionals
Cyber Incident Response Tools are more often used by security industries to test the vulnerabilities and provide an emergency incident response to...
-

 269Pentest Linux Distributions
269Pentest Linux DistributionsCAINE 10.0 – GNU/Linux Live Distribution For Digital Forensics Project, Windows Side Forensics And Incident Response
CAINE (Computer Aided INvestigative Environment) is an Italian GNU/Linux live distribution created as a Digital Forensics project. Currently, the project manager is Nanni Bassetti...
-

 318Computer Forensics
318Computer ForensicsLoki – Simple IOC and Incident Response Scanner
Loki is a free and simple IOC (Indicators of Compromise) scanner, a complete rewrite of main analysis modules of the APT Scanner...
-
 295Forensics Tools
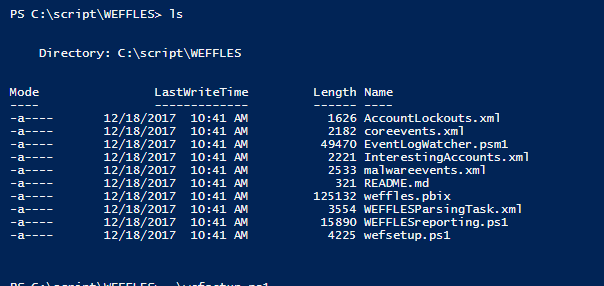
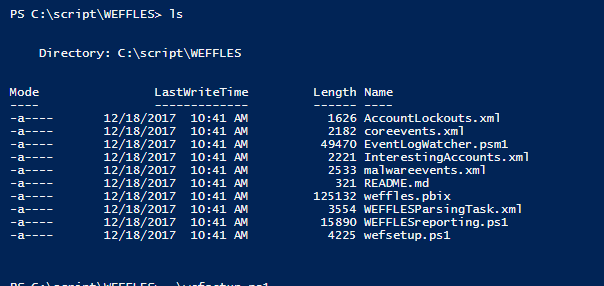
295Forensics Toolsweffles – Threat Hunting/Incident Response Console with Windows Event Forwarding and PowerBI.
WEFFLES is designed to be small and lightweight, both for speed of getting something deployed during an Incident Response and also for...
-

 409Malware Analysis
409Malware AnalysisFLARE VM – a fully customizable, Windows-based security distribution for malware analysis, incident response & penetration testing
FLARE VM is the first of its kind freely available and open sourced Windows-based security distribution designed for reverse engineers, malware analysts,...
-
 273Incident Response
273Incident ResponseCyphon – Open Source Incident Management & Response Platform
Cyphon is a big data platform that aggregates, standardizes, and enhances data for easier analysis. Many businesses rely on emails to manage...






