Search results for "Malware Analysis"
-
 2.9KInfosec
2.9KInfosecBest Malware Analysis Tools List For Security Researchers & Malware Analyst 2023
Malware analysis tools are highly essential for Security Professionals who always need to learn many tools, techniques, and concepts to analyze sophisticated...
-

 4.2KMalware
4.2KMalwareHow to Build a Custom Malware Analysis Sandbox
Before hunting malware, every researcher needs to find a system where to analyze it. There are several ways to do it: build...
-

 2.7KMalware
2.7KMalwareHow Malware Analysis Helps You Detect Reused Malware code
The fight against malware has taken another angle. Cybersecurity experts found a way to detect reused malware, improving malware analysis. In this...
-
 1.2KTutorials
1.2KTutorialsTop 6 remote access Trojans (RAT) used by Russian hackers. Which one is the best as per malware analysis experts?
Remote access Trojans (RATs) are one of the most popular hacking tools, as they allow attackers to remotely control a compromised system....
-
 3.8KMalware
3.8KMalwareCertified Malware Analyst – Exploit Development, Expert Malware Analysis & Reverse Engineering
Certified Malware Analyst: In 2020, sophisticated Cyber attacks keep on increasing by APT threats that target most of the enterprise-level networks and...
-
 5.4KHack Tools
5.4KHack ToolsAttack Monitor – Endpoint Detection And Malware Analysis Software
Attack Monitor is Python application written to enhance security monitoring capabilites of Windows 7/2008 (and all later versions) workstations/servers and to automate...
-

 425Malware
425MalwareA Complete Malware Analysis Tutorials, Cheatsheet & Tools list for Security Professionals
Analysing the malware to breakdown its function and infection routine is a kind of tough job. here we describing the complete Malware...
-

 1.7KMalware
1.7KMalwareUnderstanding What Is Malware Analysis
What is malware analysis? This is the process involved in studying and learning how a particular malware works and what it can...
-

 1.7KMalware
1.7KMalwareAutomated Malware Analysis in the Cloud
Cybercriminals execute malware attacks using different attack vectors and using different methods. The number of malware strains is increasing in an unprecedented...
-

 2.0KMalware
2.0KMalwareStatic Malware Analysis Vs Dynamic Malware Analysis
Malware Analysis: An Introduction Cybercriminals are turning more sophisticated and innovative, new and advanced varieties of malware are coming up and malware...
-

 219Malware Analysis
219Malware AnalysisMalboxes: Builds malware analysis Windows VMs
Malboxes is a tool to streamline and simplify the creation and management of virtual machines used for malware analysis. Building analysis machines...
-
 226Articles
226ArticlesAI-Powered Online Automated Malware Analysis Platform
Looking for an automated malware analysis software? Something like a 1-click solution that doesn’t require any installation or configuration…a platform that...
-
 246Reverse Engineering
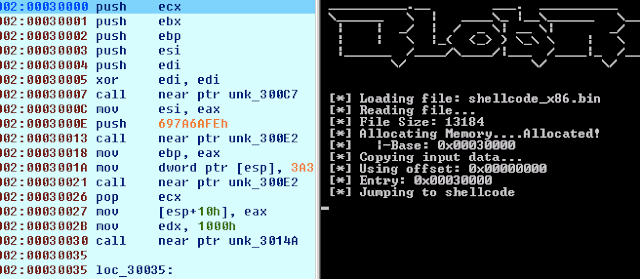
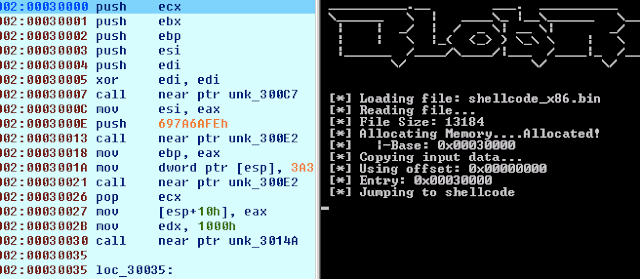
246Reverse EngineeringBlobRunner – Quickly Debug Shellcode Extracted During Malware Analysis
BlobRunner is a simple tool to quickly debug shellcode extracted during malware analysis. BlobRunner allocates memory for the target file and jumps...
-

 275Android Hacking
275Android HackingCuckooDroid – Automated Android Malware Analysis
CuckooDroid is an extension of Cuckoo Sandbox the Open Source software for automating analysis of suspicious files. CuckooDroid brigs to cuckoo the...
-

 238Malware Analysis
238Malware AnalysisProcDOT – Visual Malware Analysis
There are plenty of tools for behavioral malware analysis. The defacto standard ones, though, are Sysinternals’s Process Monitor (also known as Procmon)...
-
 261Vulnerability Analysis
261Vulnerability AnalysisDroidefense – Advance Android Malware Analysis Framework
Droidefense (originally named atom: analysis through observation machine)* is the codename for android apps/malware analysis/reversing tool. It was built focused on security...
-

 276Reverse Engineering
276Reverse EngineeringPortEx – Java library to analyse Portable Executable files with a special focus on malware analysis and PE malformation robustness
PortEx is a Java library for static malware analysis of Portable Executable files. Its focus is on PE malformation robustness, and anomaly...
-
 203Malware
203MalwareAssemblyline – Canada’s CSE intelligence Agency releases its malware analysis tool
Canada’s Communications Security Establishment (CSE) intel agency has released the source code for one of its malware analysis tools dubbed Assemblyline. The...
-

 222Malware
222MalwareCSE CybSec ZLAB Malware Analysis Report: NotPetya
I’m proud to share with you the first report produced by Z-Lab, the Malware Lab launched by the company CSE CybSec. Enjoy...
-

 404Malware Analysis
404Malware AnalysisFLARE VM – a fully customizable, Windows-based security distribution for malware analysis, incident response & penetration testing
FLARE VM is the first of its kind freely available and open sourced Windows-based security distribution designed for reverse engineers, malware analysts,...
-

 329Malware Analysis
329Malware AnalysisMalware Analysis Tools and Cheat list
A large number of computer intrusions involve some form of malicious software (malware), which finds its way to the victim’s workstation or...






