Search results for "Man-in-the-Middle"
-
 3.1KTutorials
3.1KTutorialsThe best 6 MiTM (Man-in-The-Middle) attack tools that every ethical hacker should have
Man-in-The-Middle (MiTM) attacks are one of the most popular hacking techniques nowadays, and occur when a third party arbitrarily breaks into an...
-
 2.8KMan-In-The-Middle
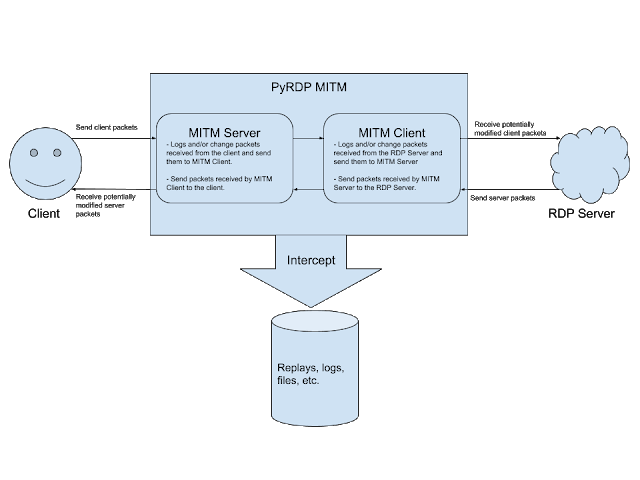
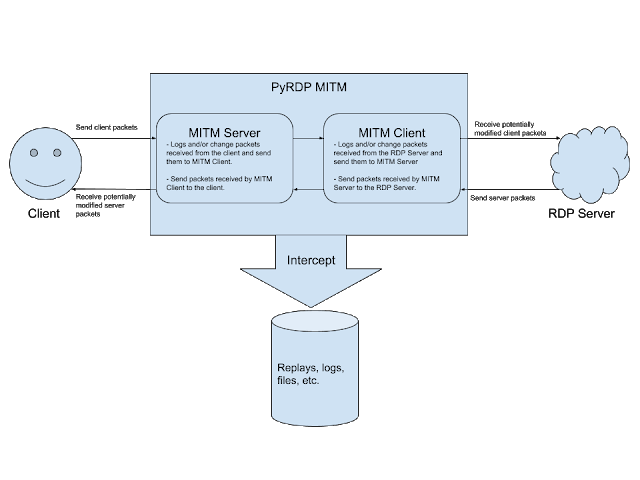
2.8KMan-In-The-MiddlePyrdp – RDP Man-In-The-Middle And Library For Python3
PyRDP is a Python 3 Remote Desktop Protocol (RDP) Man-in-the-Middle (MITM) and library. It features a few tools: RDP Man-in-the-Middle Logs...
-

 245Malware
245MalwareHackers Distribute PLEAD Malware through Supply-chain and man-in-the-middle Attack
Security researchers a new malware campaign that delivers Plead malware by abusing legitimate software that developed by ASUS Cloud Corporation. The PLEAD...
-
 269News
269NewsGoogle To Ban Embedded Browser Logins To Stop Man-In-The-Middle Attacks
Google will ban logins from embedded browser frameworks, starting June 2019. The reason is the increased risk of phishing hacks using the...
-

 3.7KCyber Attack
3.7KCyber AttackMan-in-the-Middle (MITM) Attacks: An Introduction
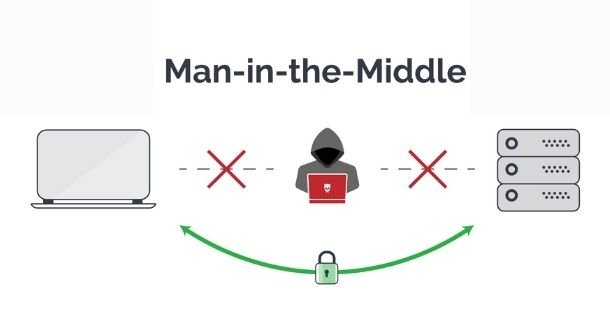
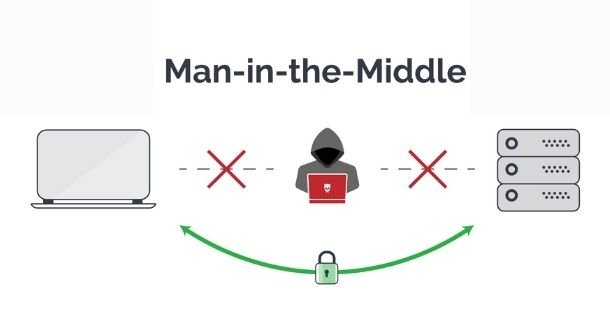
What is a Man-in-the-Middle (MITM) Attacks – Definition MITM attack refers to the kind of cyberattack in which an attacker eavesdrops on...
-
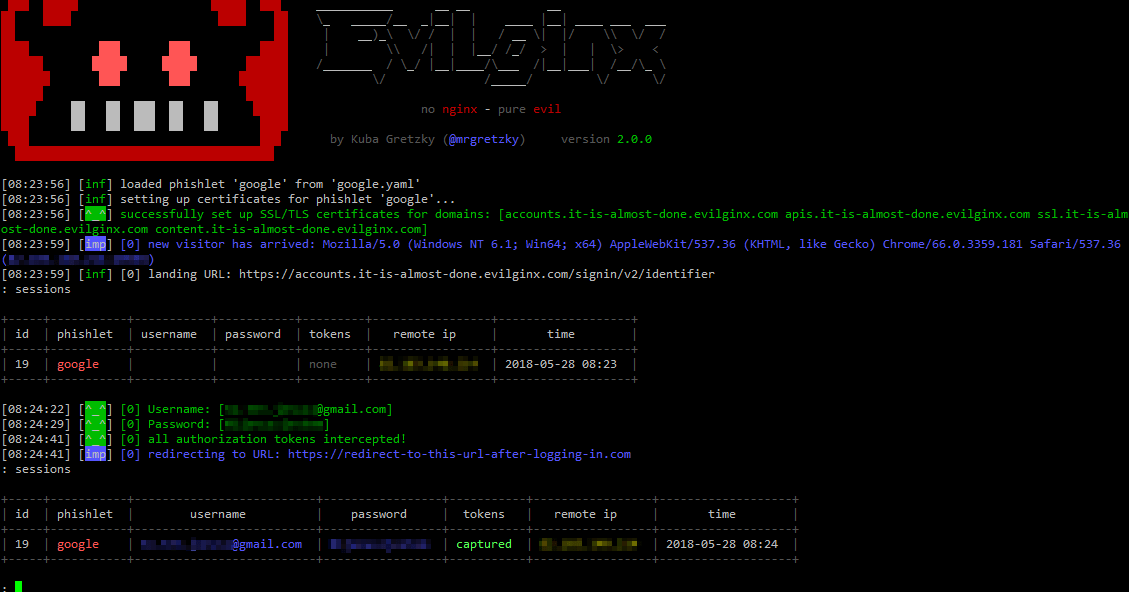
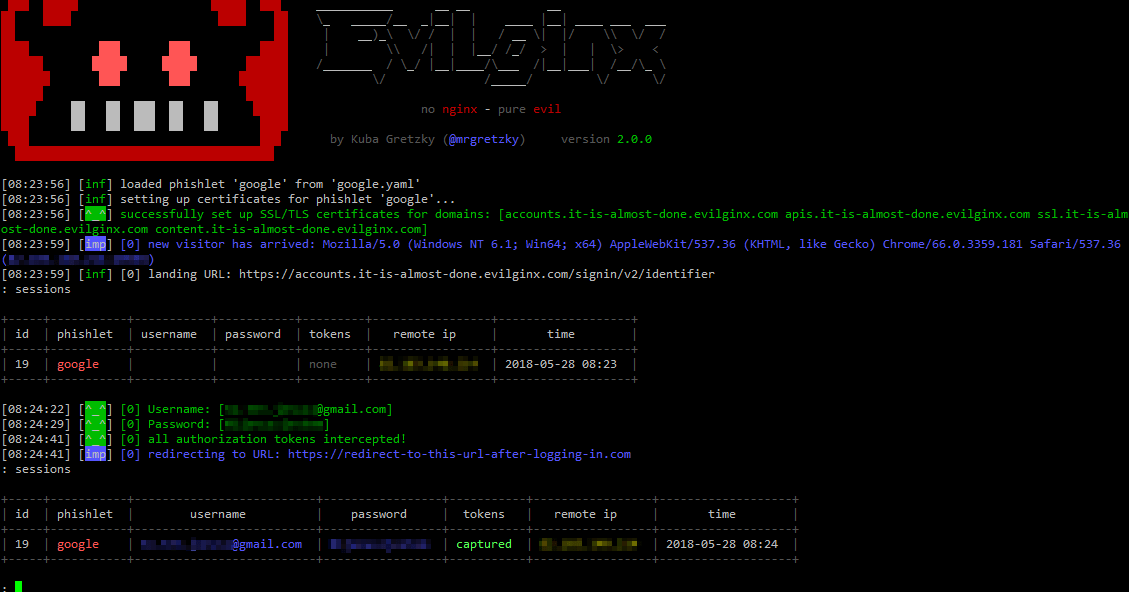 541Exploitation Tools
541Exploitation ToolsEvilginx v2.0 – Standalone Man-In-The-Middle Attack Framework Used For Phishing Login Credentials Along With Session Cookies, Allowing For The Bypass Of 2-Factor Authentication
evilginx2 is a man-in-the-middle attack framework used for phishing login credentials along with session cookies, which in turn allows to bypass 2-factor...
-

 282Man-In-The-Middle
282Man-In-The-MiddleBtleJuice Framework – Bluetooth Smart (LE) Man-in-the-Middle Framework
BtleJuice is a complete framework to perform Man-in-the-Middle attacks on Bluetooth Smart devices (also known as Bluetooth Low Energy). It is composed...
-

 349Vulnerabilities
349VulnerabilitiesMan-in-the-middle flaw left smartphone banking apps vulnerable
A flaw in certificate pinning exposed customers of a number of high-profile banks to man-in-the-middle attacks on both iOS and Android devices....
-

 276Man-In-The-Middle
276Man-In-The-Middleratched – Transparent Man-in-the-Middle TLS Proxy
ratched is a Man-in-the-Middle (MitM) proxy that specifically intercepts TLS connections. It is intended to be used in conjunction with the Linux...
-
 204Hackers Repository
204Hackers RepositorySSL Kill – Forced Man-In-The-Middle HTTPs-Avoiding Transparent Proxy
SSL Kill – Forced Man-In-The-Middle HTTPs-Avoiding Transparent Proxy SSL Kill is a forced man-in-the-middle transparent proxy that modifies HTTP requests and responses...
-
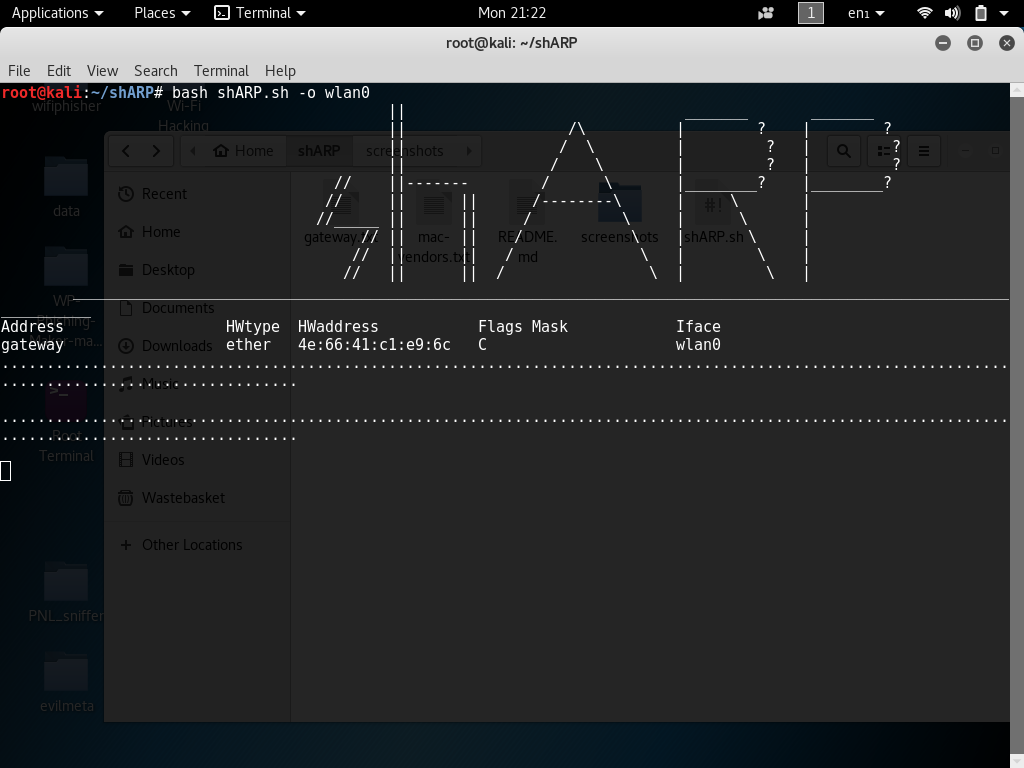
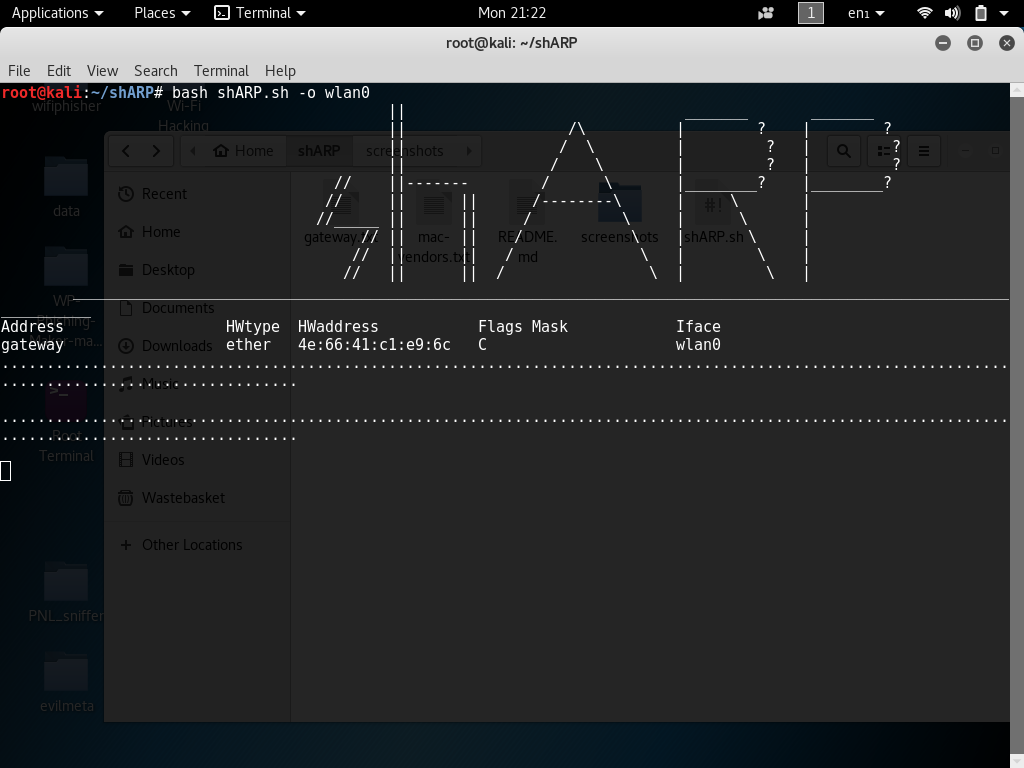 210Hackers Repository
210Hackers RepositoryPrevent Man-In-The-Middle Attacks, ARP-spoofing using shARP
Prevent Man-In-The-Middle Attacks, ARP-spoofing using shARP ARP spoofing is a type of MiTM (Man-in-the-middle) attack it may allow an attacker to intercept...
-

 241Cyber Events
241Cyber EventsChina’s Outlook email faced man-in-the-middle attack
Outlook email users of China faced an outage over the weekend, possibly a victim of man-in-the-middle attack, according to media reports. Chinese...






