Search results for "Management"
-

 3.6KData Security
3.6KData SecurityHack-Proof Your Cloud: The Step-by-Step Continuous Threat Exposure Management CTEM Strategy for AWS & AZURE
Continuous Threat Exposure Management (CTEM) is an evolving cybersecurity practice focused on identifying, assessing, prioritizing, and addressing security weaknesses and vulnerabilities in...
-

 2.5KVulnerabilities
2.5KVulnerabilitiesSuperusers Need Super Protection: How to Bridge Privileged Access Management and Identity Management
Traditional perimeter-based security has become costly and ineffective. As a result, communications security between people, systems, and networks is more important than...
-
 869Data Breach
869Data BreachThis Free Solution Provides Essential Third-Party Risk Management for SaaS
Wing Security recently announced that basic third-party risk assessment is now available as a free product. But it raises the questions of...
-

 458Vulnerabilities
458Vulnerabilities3 Challenges in Building a Continuous Threat Exposure Management (CTEM) Program and How to Beat Them
If you’re a cybersecurity professional, you’re likely familiar with the sea of acronyms our industry is obsessed with. From CNAPP, to CWPP,...
-

 1.1KData Security
1.1KData SecurityEasily hack into Azure internal workloads & API using Azure API Management service flaws
The Azure API Management service is a platform that is completely managed and offers businesses the ability to design, administer, protect, and...
-

 3.7KVulnerabilities
3.7KVulnerabilitiesGoogle Launches New Cybersecurity Initiatives to Strengthen Vulnerability Management
Google on Thursday outlined a set of initiatives aimed at improving the vulnerability management ecosystem and establishing greater transparency measures around exploitation....
-

 295Data Security
295Data Security5 best practices for securing identity and access management (IAM) systems
The term “identity and access management,” or “IAM,” refers to a framework of corporate procedures, regulations, and technology that support the management...
-

 3.2KVulnerabilities
3.2KVulnerabilitiesUnpatched Security Flaws Disclosed in Multiple Document Management Systems
Multiple unpatched security flaws have been disclosed in open source and freemium Document Management System (DMS) offerings from four vendors LogicalDOC, Mayan,...
-

 626Vulnerabilities
626VulnerabilitiesAtlassian’s Jira Service Management Found Vulnerable to Critical Vulnerability
Atlassian has released fixes to resolve a critical security flaw in Jira Service Management Server and Data Center that could be abused...
-

 1.3KVulnerabilities
1.3KVulnerabilitiesSERIOUS PRIVILEGES ESCALATION VULNERABILITY IN SYMANTEC PRIVILEGED ACCESS MANAGEMENT
Protecting sensitive organizational credentials, limiting privileged user access, actively imposing security policies, and monitoring and recording privileged user behavior across virtual, cloud,...
-

 937Cyber Attack
937Cyber AttackInfra Used in Cisco Hack Also Targeted Workforce Management Solution
The attack infrastructure used to target Cisco in the May 2022 incident was also employed against an attempted compromise of an unnamed...
-

 1.4KVulnerabilities
1.4KVulnerabilitiesOver a Dozen Flaws Found in Siemens’ Industrial Network Management System
Cybersecurity researchers have disclosed details about 15 security flaws in Siemens SINEC network management system (NMS), some of which could be chained...
-

 2.1KVulnerabilities
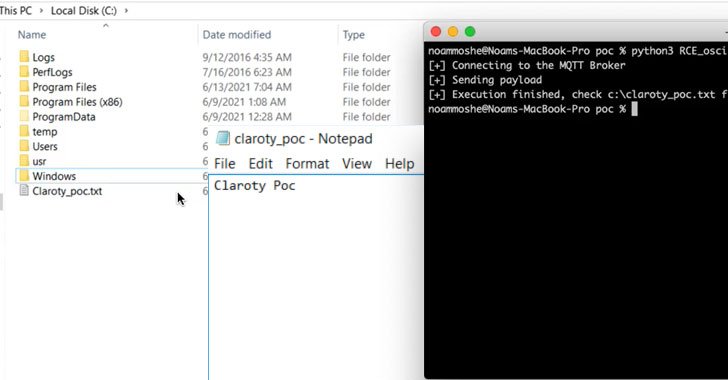
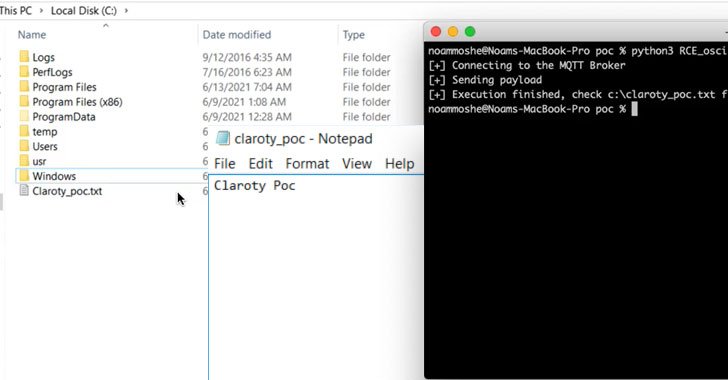
2.1KVulnerabilitiesExploitation code for CVE-2022-1388 available: Critical remote code execution vulnerability in F5 Network management tools
A few days ago, the security teams of F5 Networks reported the correction of more than 50 vulnerabilities in various versions of...
-
 3.7KVulnerabilities
3.7KVulnerabilitiesCritical Security Flaws Reported in Moxa MXview Network Management Software
Technical details have been disclosed regarding a number of security vulnerabilities affecting Moxa’s MXview web-based network management system, some of which could...
-

 870Vulnerabilities
870VulnerabilitiesCritical vulnerabilities in MXview network management software; Moxa users should update as soon as possible
Moxa users will need to upgrade MXview to versions greater than 3.2.4 in order to address five vulnerabilities in the web-based network...
-

 2.7KData Breach
2.7KData BreachHow Attack Surface Management Preempts Cyberattacks
The wide-ranging adoption of cloud facilities and the subsequent mushrooming of organizations’ networks, combined with the recent migration to remote work, had...
-

 565Vulnerabilities
565VulnerabilitiesPrivilege escalation flaw in Cisco Unified Contact Center Management Portal
Cybersecurity specialists reported the finding of a critical vulnerability affecting Cisco Unified Contact Center Management Portal (Unified CCMP). According to the report,...
-

 3.9KCyber Events
3.9KCyber EventsTop workforce management firm Kronos hit by ransomware attack
Kronos has taken down its private cloud services and advises customers to use “alternative business continuity protocols” while the company is working...
-

 4.2KCyber Attack
4.2KCyber AttackHow Extended Security Posture Management Optimizes Your Security Stack
As a CISO, one of the most challenging questions to answer is “How well are we protected right now?” Between the acceleration...
-
 2.8KNews
2.8KNewsMicrosoft’s Loop Project Management Software
Microsoft has been developing a project collaboration solution for enterprise projects. The Loop app is now accessible to Microsoft 365 commercial customers. ...
-

 2.4KData Security
2.4KData SecurityWiFi software management firm exposed millions of users’ data
Brazil-based WiFi management software firm WSpot exposed extensive details of high-profile firms and millions of customers. WSpot provides software to let businesses...






