Search results for "Nmap"
-
 2.0KMalware
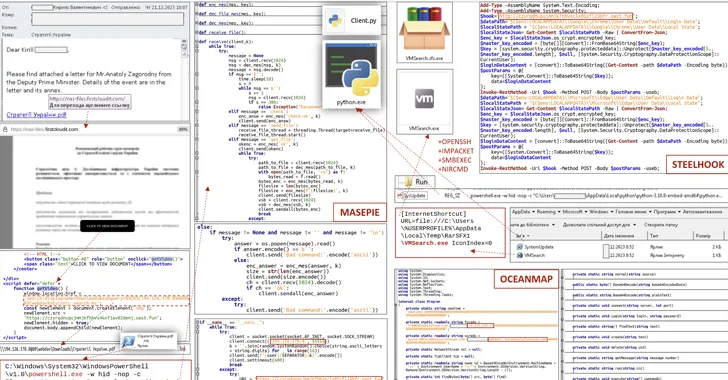
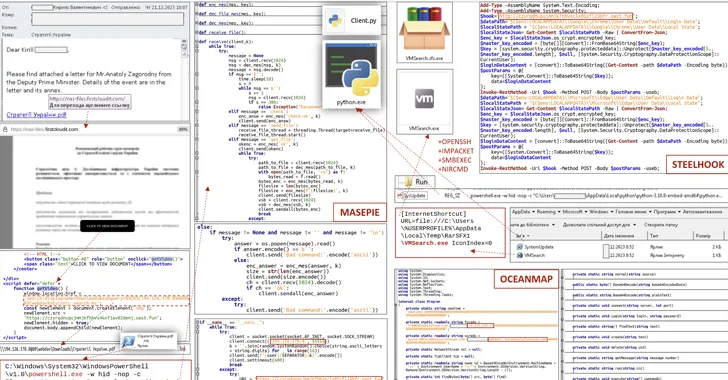
2.0KMalwareCERT-UA Uncovers New Malware Wave Distributing OCEANMAP, MASEPIE, STEELHOOK
The Computer Emergency Response Team of Ukraine (CERT-UA) has warned of a new phishing campaign orchestrated by the Russia-linked APT28 group to...
-
 4.3KHackers Repository
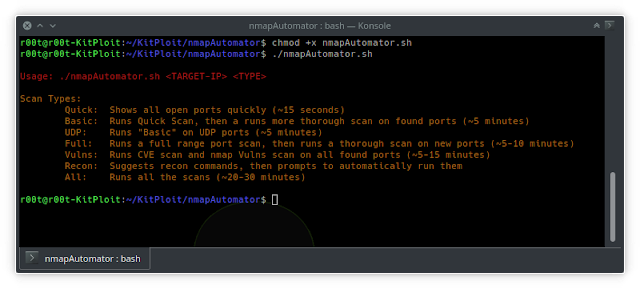
4.3KHackers RepositorynmapAutomator – Tool To Automate All Of The Process Of Recon/Enumeration
nmapAutomatorA script that you can run in the background! SummaryThe main goal for this script is to automate all of the process...
-
 3.3KHacking Tools
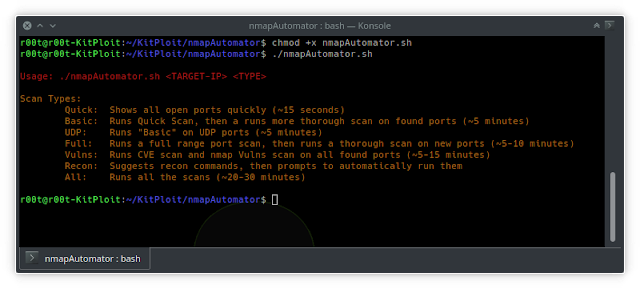
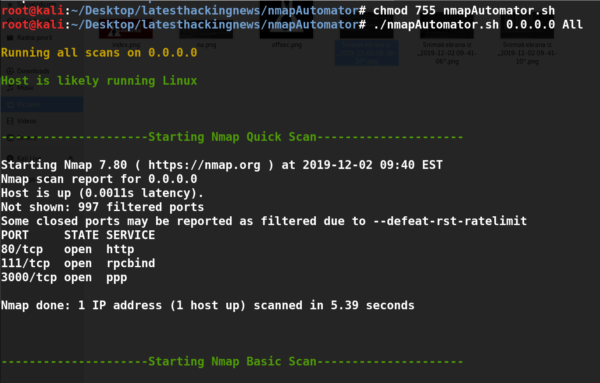
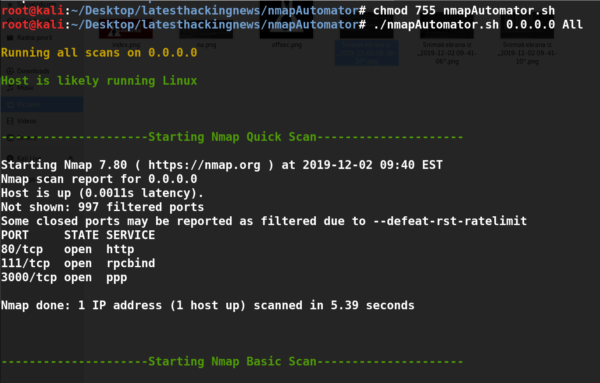
3.3KHacking ToolsNmap Automator – a tool I used during OSCP for simple recon
Nmap Automator is a great tool for initial port scans of a given ip address. It automates the scan techniques which I...
-
 1.4KHack Tools
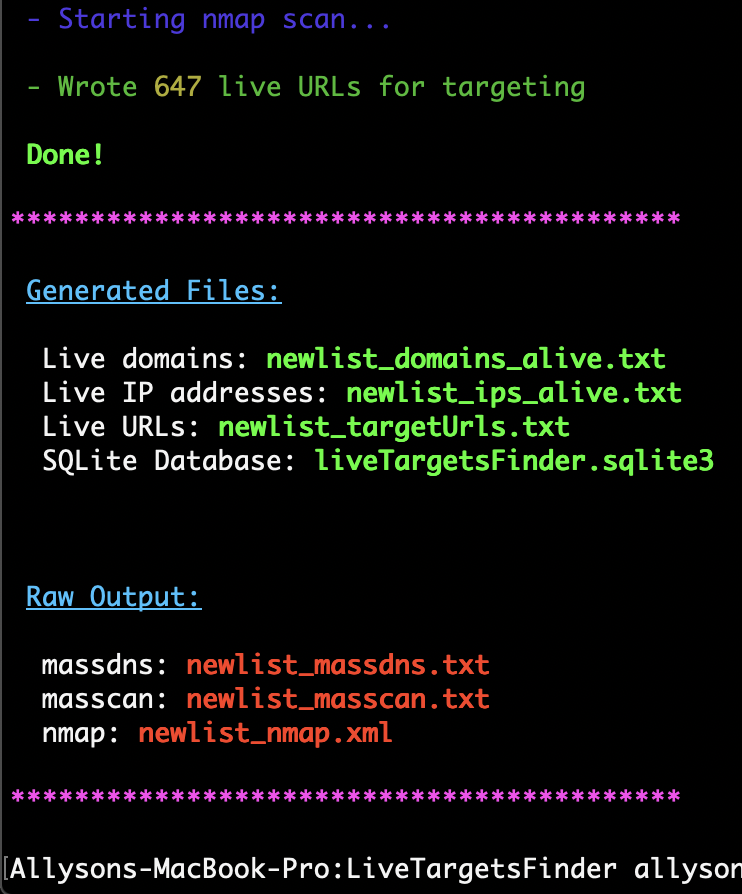
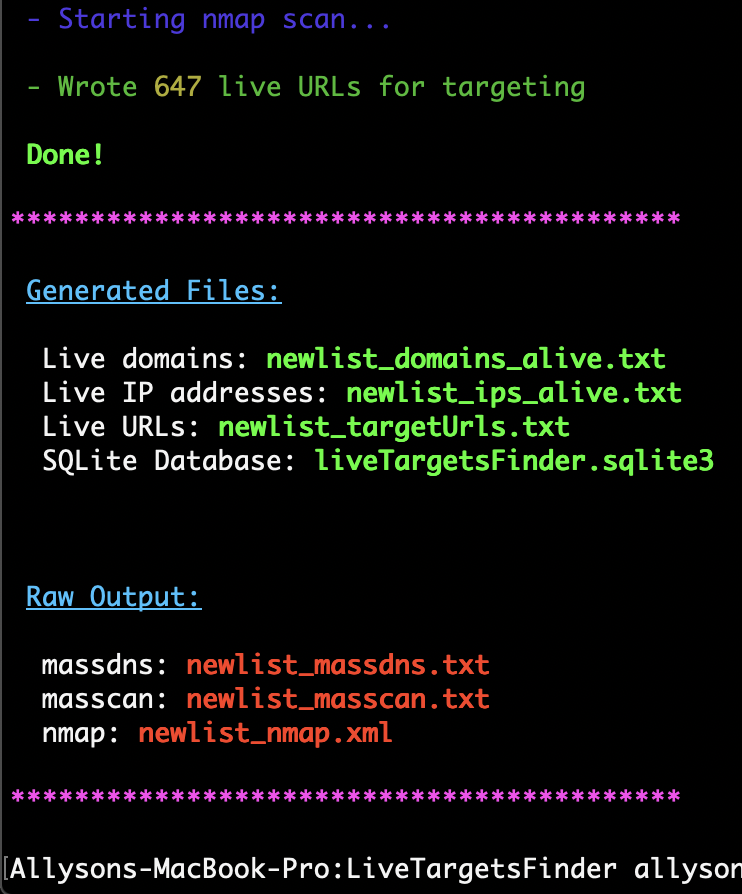
1.4KHack ToolsLiveTargetsFinder: automating the usage of MassDNS, Masscan and nmap to filter out unreachable hosts
LiveTargetsFinder Generates lists of live hosts and URLs for targeting, automating the usage of Massdns, Masscan, and nmap to filter out unreachable...
-

 5.3KHack Tools
5.3KHack ToolsVscan – Vulnerability Scanner Tool Using Nmap And Nse Scripts
vulnerability scanner tool is using nmap and nse scripts to find vulnerabilitiesThis tool puts an additional value into vulnerability scanning with nmap....
-

 341Hack Tools
341Hack ToolsTrigmap – Wrapper for Nmap to Automate the Pentest
Trigmap is a wrapper for Nmap. You can use it to easily start Nmap scan and especially to collect informations into a...
-
 328Information Gathering
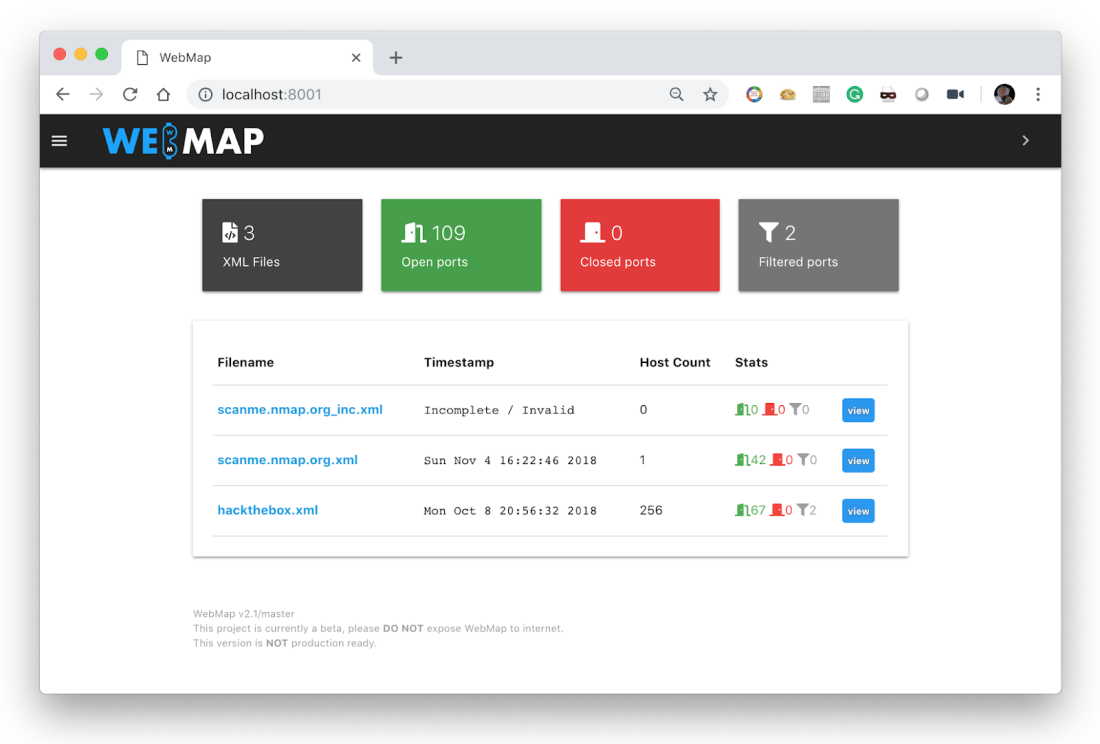
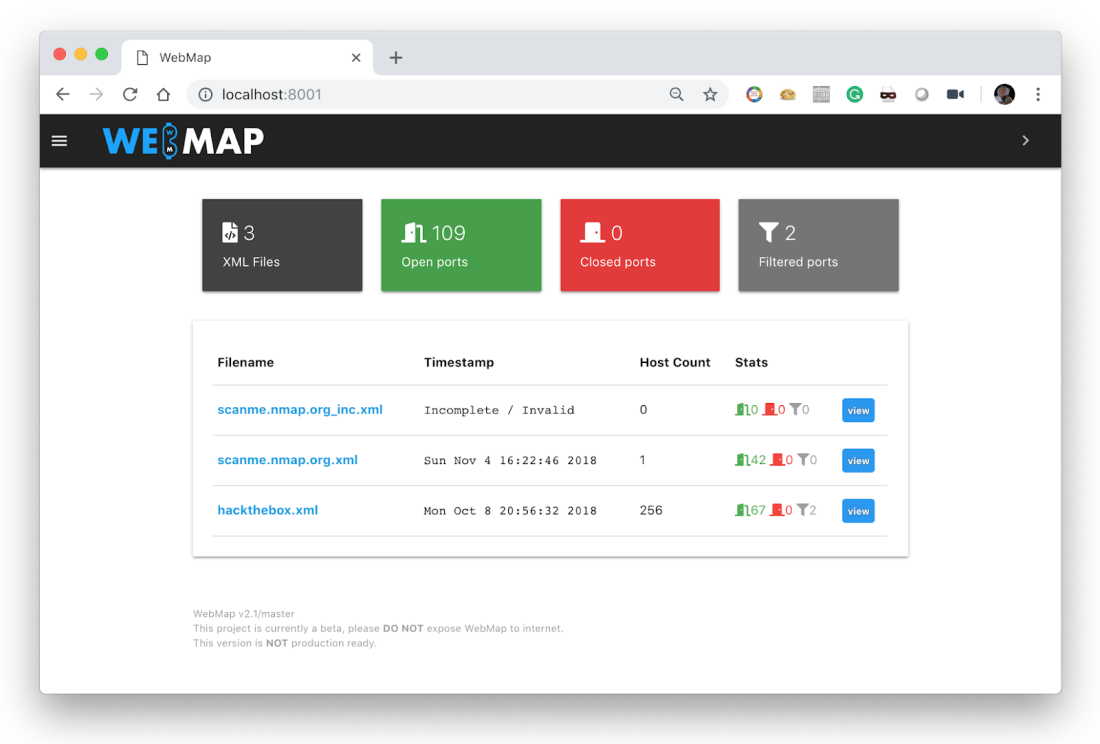
328Information GatheringWebMap – Nmap Web Dashboard And Reporting
A Web Dashbord for Nmap XML Report Usage You should use this with docker, just by sending this command: $ mkdir /tmp/webmap...
-
 242Data Security
242Data SecurityWebMap – A web dashboard for Nmap XML report
Use You should use this with docker. According to digital forensics specialists from the International Institute of Cyber Security, all you have...
-
 322Exploitation Tools
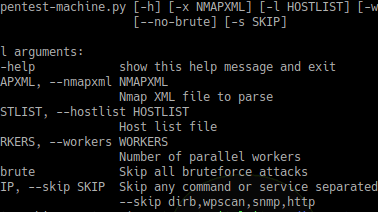
322Exploitation ToolsPentest-Machine – Automates Some Pentest Jobs Via Nmap Xml File
Automates some pentesting work via an nmap XML file. As soon as each command finishes it writes its output to the terminal...
-

 283How To
283How ToNmap-bootstrap-xsl Hack Creates Visually Appealing Nmap Scan Reports : Interview With Its Creator, Andreas Hontzia
As the title itself states, nmap-xsl-bootstrap, a brand-new utility or, better to say an Nmap hack, that helps in beautifying the regular...
-
 295Information Gathering
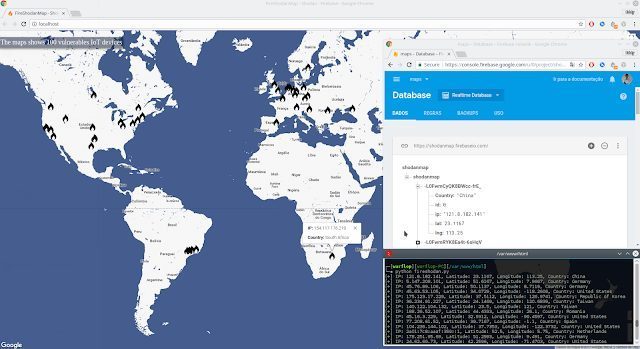
295Information GatheringFireShodanMap – A Realtime Map That Integrates Firebase, Google Maps And Shodan
FireShodanMap is a Realtime map that integrates Firebase and Shodan. A search is carried out using Shodan searching vulnerable devices and they...
-
 199Information Gathering
199Information GatheringNmap 7.70 Released With Better OS Detection, 9 new NSE scripts and Much More
Nmap (“Network Mapper”) is a free and open source utility for network discovery and security auditing. Many systems and network administrators also find...
-
 201Information Gathering
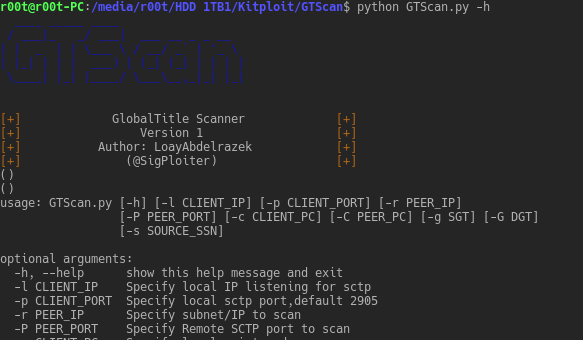
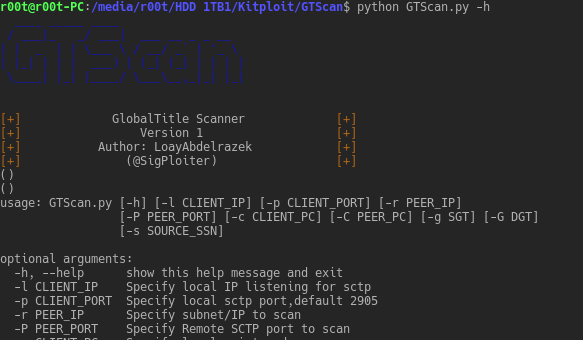
201Information GatheringGTScan – The Nmap Scanner for Telecom
The Nmap Scanner for Telco. With the current focus on telecom security, there used tools in day to day IT side penetration...
-
 207Information Gathering
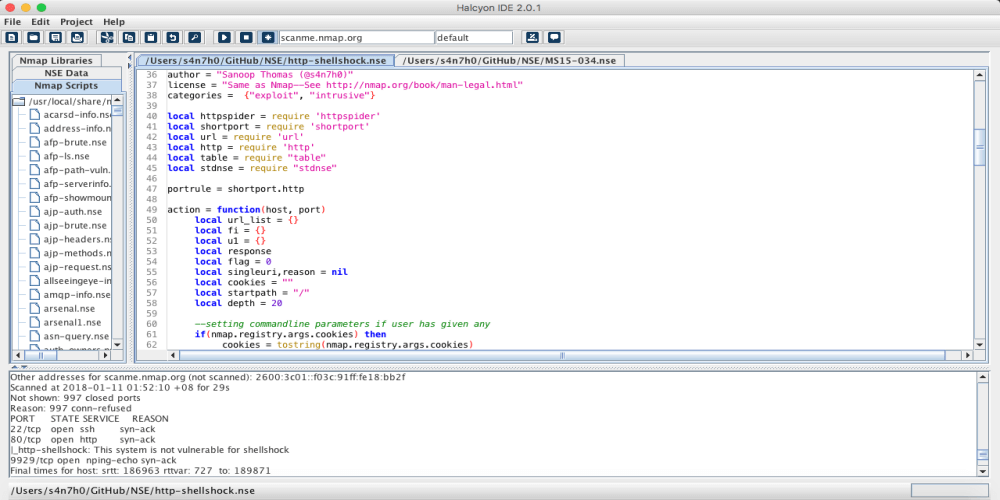
207Information GatheringHalcyon – NSE Nmap Script Development IDE
Halcyon IDE lets you quickly and easily develop scripts for performing advanced scans on applications and infrastructures with a range from recon to...
-

 314Enumeration
314EnumerationOnion Map – Onion Service nMap Scanner
Use nmap to scan hidden “onion” services on the Tor network. Minimal image based on alpine, using proxychains to wrap nmap. Tor...
-
 208Exploitation Tools
208Exploitation ToolsBruteSpray v1.6.0 – Brute-Forcing from Nmap output (Automatically attempts default creds on found services)
BruteSpray takes nmap GNMAP/XML output and automatically brute-forces services with default credentials using Medusa. BruteSpray can even find non-standard ports by using...
-

 206Hack Tools
206Hack ToolsVulscan – nMap Vulnerability Scanner
Vulscan is a module which enhances nmap to a vulnerability scanner. The nmap option -sV enables version detection per service which is...
-

 193Hack Tools
193Hack ToolsBruteSpray – Brute-Forcing from Nmap
BruteSpray takes nmap GNMAP/XML output and automatically brute-forces services with default credentials using Medusa. BruteSpray can even find non-standard ports by using...
-
 211How To
211How ToHow to Perform Open Port Scanning and OS Detection Using Nmap
Today in this tutorial we will have a look at how we can use Nmap (Which stands for Network Mapper )in Kali...
-

 232How To
232How ToHow to Use Zenmap – Nmap Network Scanning Tool in Windows
Running Nmap on Windows is not as difficult or problematic as it was in the past. Nmap is supported on Windows 7...
-
How To
How to Scan Live Hosts With Nmap
Live hosts detection is a very important tool for every penetration tester and ethical hacking. In this tutorial we are going to...






