Search results for "Obfuscation"
-

 2.5KMalware
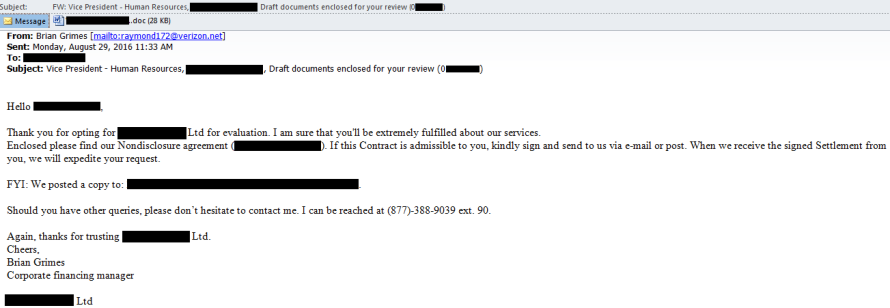
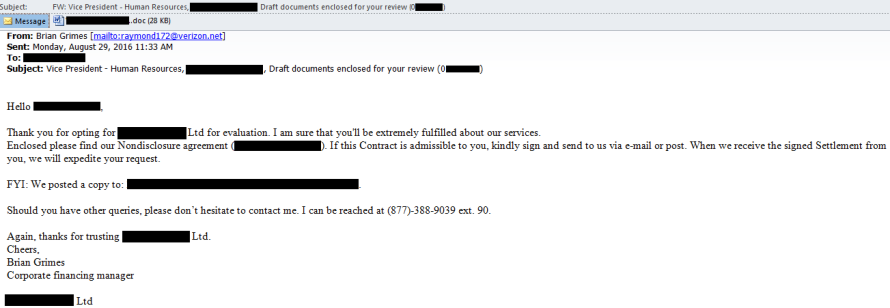
2.5KMalwareAttackers Using Obfuscation Tools to Deliver Multi-Stage Malware via Invoice Phishing
Cybersecurity researchers have discovered an intricate multi-stage attack that leverages invoice-themed phishing decoys to deliver a wide range of malware such as...
-
 2.6KMalware
2.6KMalwareGootkit Malware Continues to Evolve with New Components and Obfuscations
The threat actors associated with the Gootkit malware have made “notable changes” to their toolset, adding new components and obfuscations to their...
-

 2.4KMalware
2.4KMalwareExperts Detail Virtual Machine Used by Wslink Malware Loader for Obfuscation
Cybersecurity researchers have shed more light on a malicious loader that runs as a server and executes received modules in memory, laying...
-

 4.0KData Security
4.0KData SecurityNew phishing technique uses advanced obfuscation and Telegram channels to evade detection. Hackers can easily bypass your firewall
The specialized team FireEye Email Security has published a report on the detection of multiple phishing campaigns in which operators use source...
-

 3.3KMalware
3.3KMalwareStantinko’s new cryptominer features unique obfuscation techniques
ESET researchers bring to light unique obfuscation techniques discovered in the course of analyzing a new cryptomining module distributed by the Stantinko...
-
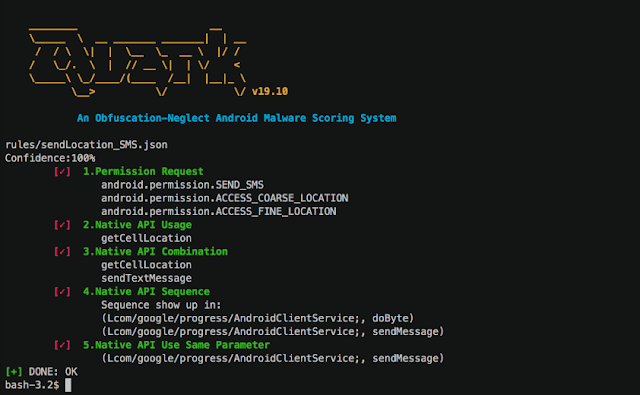
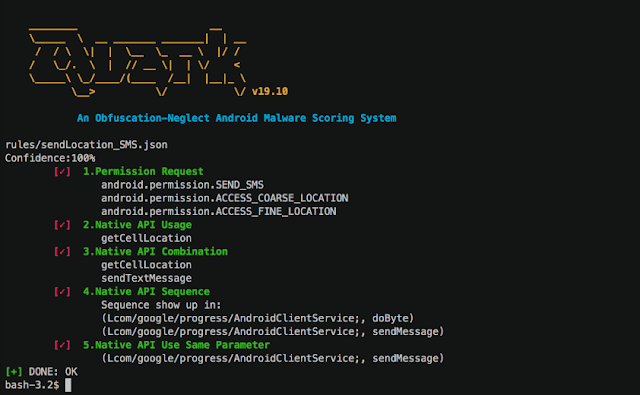 4.0KHackers Repository
4.0KHackers RepositoryQuark-Engine – An Obfuscation-Neglect Android Malware Scoring System
An Obfuscation-Neglect Android Malware Scoring System ConceptsAndroid malware analysis engine is not a new story. Every antivirus company has their own secrets...
-
 4.1KInfosec
4.1KInfosecMacro Pack – Automatize Obfuscation and Generation of Malicious Office Documents
Malware delivery trends change every day. For the last few years, we have observed various hacker groups like ( APT12 to Turla...
-

 134News
134NewsObfuscation of Source Code of Phishing Messages Through Web Open Font Format, Growing in the Wild
Threat actors want to maintain anonymity in their operations, especially in the art of virus development and phishing expedition. They continue to...
-
 271Malware
271MalwareMost Advanced Backdoor Obfuscation and Evasion Technique That used by Hackers
Cybercriminals are using the most sophisticated techniques to bypass the security controls in various organization such as IT, medical, manufacturing industries, energy...
-

 188Ransomware
188RansomwareMagniber Ransomware Improves Its Obfuscation Techniques and Expands to Other Asian Countries
Magniber ransomware emerges again leveraging various obfuscation techniques and with refined source codes. The most famous and long-running browser exploitation toolkit Magnitude...
-

 251Evasion & Obfuscation
251Evasion & ObfuscationhideNsneak – An Attack Obfuscation Framework
This application assists in managing attack infrastructure for penetration testers by providing an interface to rapidly deploy, manage, and take down various...
-

 294Infosec
294InfosecHackers Increasing the use of “Command Line Evasion and Obfuscation” to Spread Advance Level Threats
Advance level threats are increasing day by day and attackers using more Sophisticated Techniques to bypass the Detection. Evasion and obfuscation technique...
-
 214Malware
214MalwareFakeBank Malware Layered Obfuscation Technique Replace a Default SMS App to Stealing Highly Sensitive Data
A New persistent malware family called FakeBank spreading across Russian speaking nations and targetting Russian banks with sophisticated Obfuscation technique to steal...
-

 234Exploitation Tools
234Exploitation Toolsmacro_pack – Automatize Obfuscation and Generation of MS Office Documents
The macro_pack is a tool used to automatize obfuscation and generation of MS Office documents for pentest, demo, and social engineering assessments....
-
 169Malware
169MalwareJava Malware “jRAT” Evolving with Highly Obfuscation Patterns
Java Based Remote Access Trojan Called “jRAT” Rapidly Evolving with Advanced Capabilities and Targeting Many Organization Sensitive information that spreading with Highly...
-
 218Data Security
218Data SecurityDiscovery of a New Nymaim Malware Variant Employing Advanced Delivery, Obfuscation and Blacklisting methods
Verint’s Cyber Research team has discovered an unknown variant of the Nymaim malware family, a group of threats that are also capable...
-

 180Malware
180MalwareNymaim – obfuscation chronicles
We look at malware delivered by a campaign that has infected thousands of websites around the world - and the various control...






