Search results for "Packet"
-
 2.2KCyber Attack
2.2KCyber AttackNew BlackCat Ransomware Variant Adopts Advanced Impacket and RemCom Tools
Microsoft on Thursday disclosed that it found a new version of the BlackCat ransomware (aka ALPHV and Noberus) that embeds tools like...
-

 1.0KVulnerabilities
1.0KVulnerabilitiesJust few malicious packets allow to take control of Centos Web Panel 7 servers. Exploit PoC for RCE flaw published.
Control Web Panel, which was formerly known as CentOS Web Panel and comes in both free and paid versions, is a web...
-

 4.3KDDOS
4.3KDDOSLargest DDoS Attack Ever – 659.6 Million Packets Per Second
In the past few weeks, an organization in Eastern Europe has been the victim of the biggest DDoS attack that the continent...
-
Malware
New Linux Rootkit Malware ‘Syslogk’ Triggers Backdoors With Magic Packets
In order to conceal malicious processes, a new Linux rootkit malware dubbed, ‘Syslogk’ has been hacking computers by using specially crafted “magic...
-
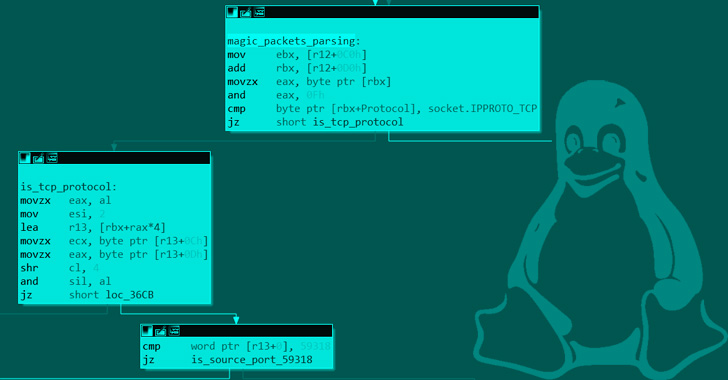
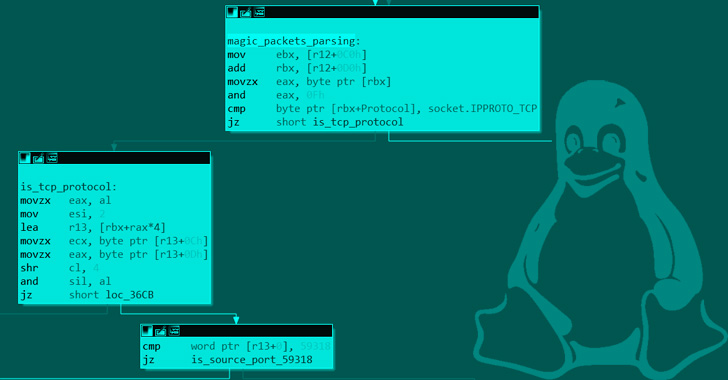 1.1KMalware
1.1KMalwareNew Syslogk Linux Rootkit Lets Attackers Remotely Command It Using “Magic Packets”
A new covert Linux kernel rootkit named Syslogk has been spotted under development in the wild and cloaking a malicious payload that...
-
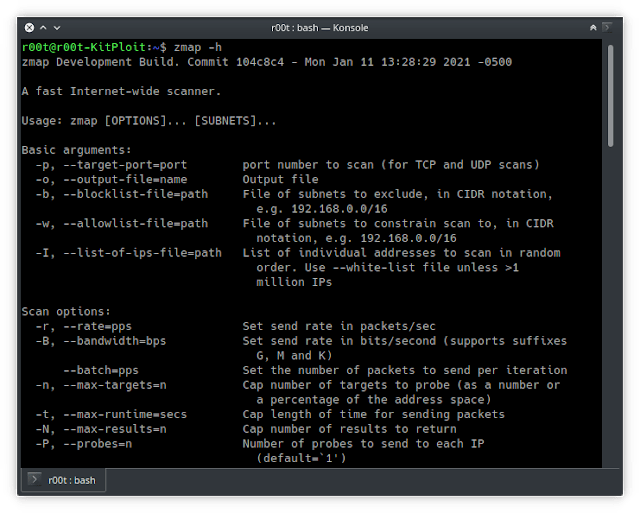
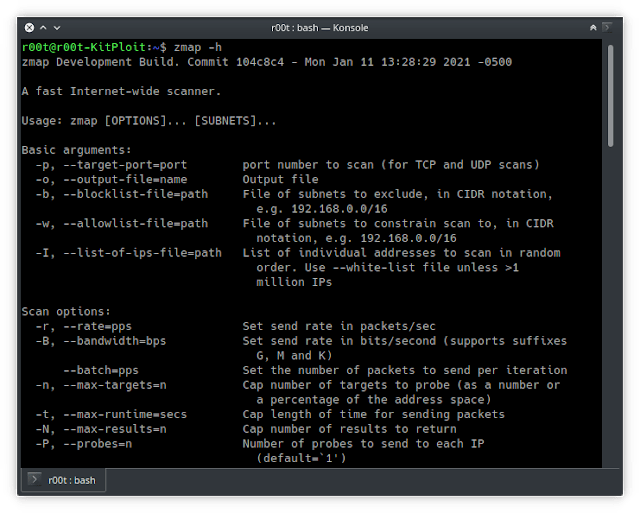 3.6KNetwork Tools
3.6KNetwork ToolsZmap – Single Packet Network Scanner Designed For Internet-wide Network Surveys
ZMap is a fast single packet network scanner designed for Internet-wide network surveys. On a typical desktop computer with a gigabit...
-
 416Data Breach
416Data BreachHow Hackers Breach Your Corporate Network? – Prevention Packet Guide
We are living in the era of the digital economy where companies are collecting and storing tons of valuable customer data on...
-

 4.5KData Security
4.5KData SecurityWhat Is Deep Packet Inspection and How Does It Work?
Also known as DPI, deep packet inspection is a kind of packet filtering that evaluates the data and header of a packet...
-
 306Tutorials
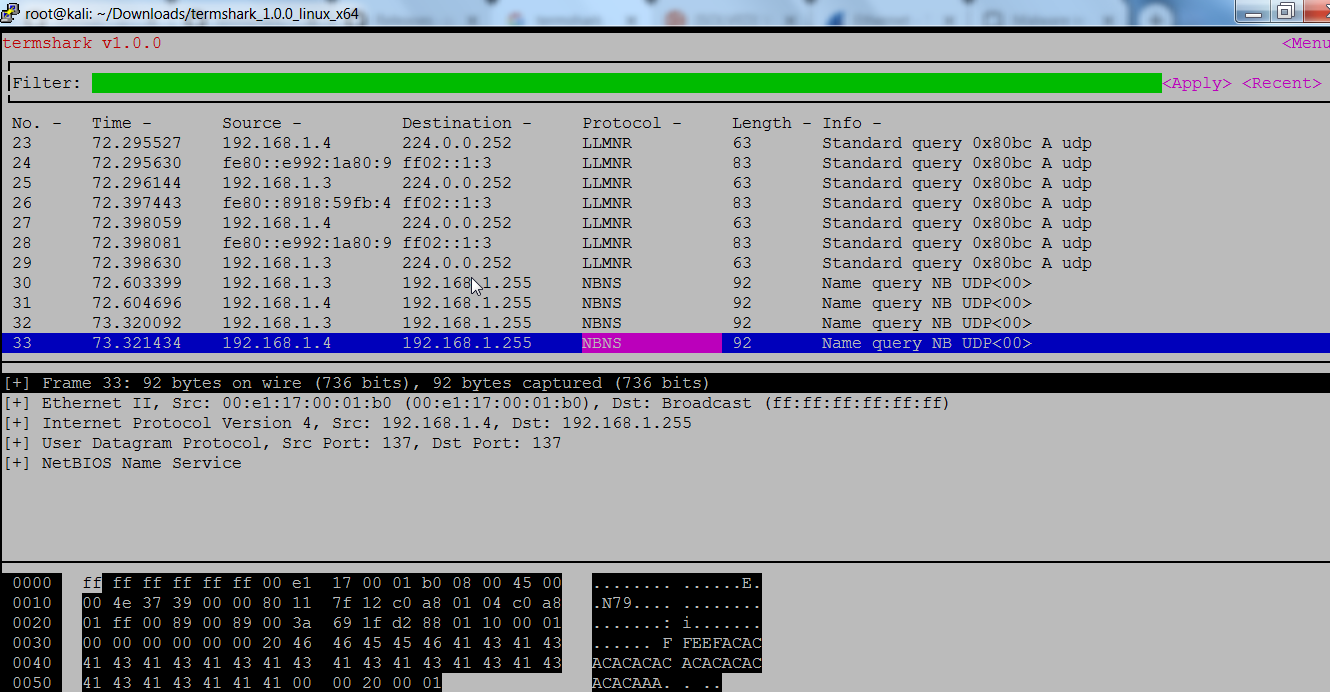
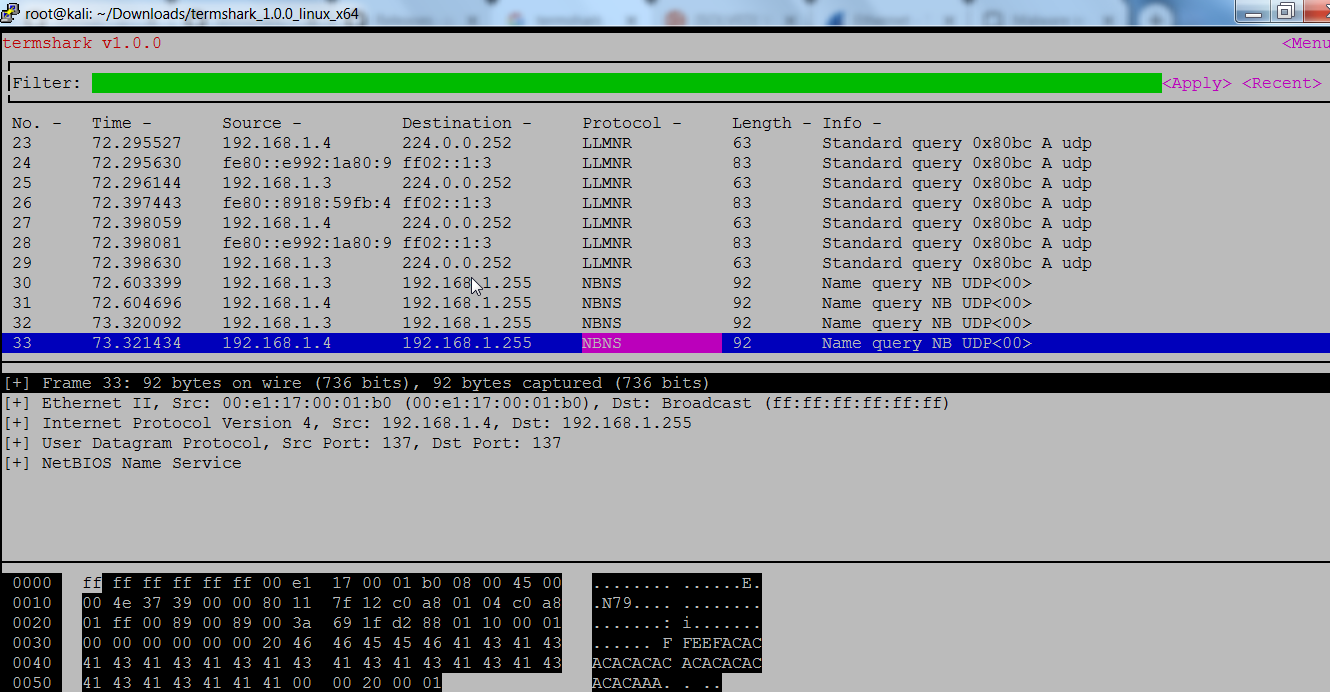
306TutorialsLight weight Packets Analyzer is here!
There are many tools used in by network administrator to scan network. Continuous network scanning is done to check if any malicious...
-
 227News
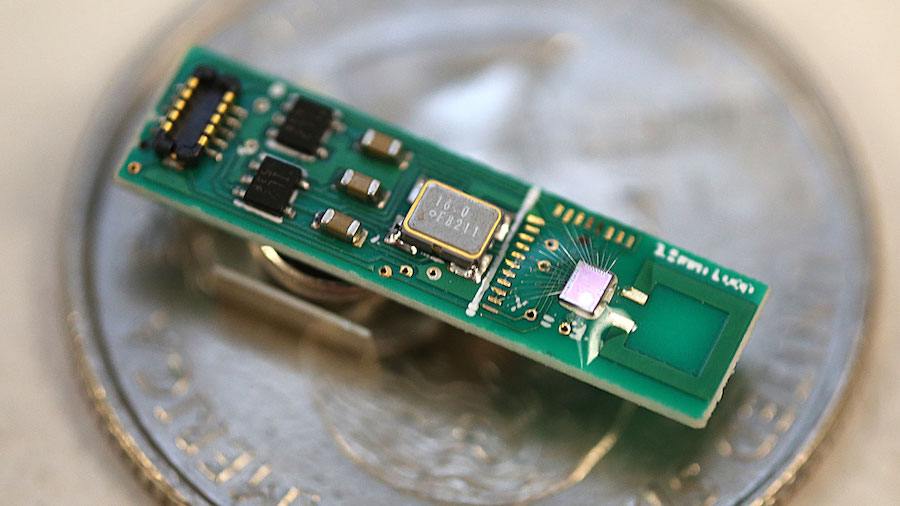
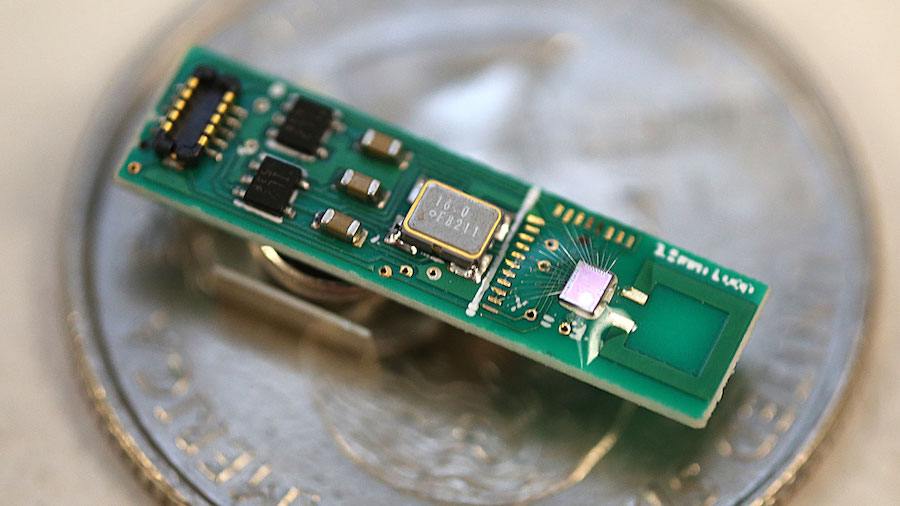
227NewsFirst Millimeter-sized Bluetooth Chip Invented To Send Low-Energy Data Packets
We are surrounded by Bluetooth radio signals and most of the devices that we see around — smartphones, wireless computer networks, and wireless...
-
 323Network Tools
323Network ToolsJustniffer – Network TCP Packet Sniffer
Justniffer is a network protocol analyzer that captures network traffic and produces logs in a customized way, can emulate Apache web server...
-
 221Network Tools
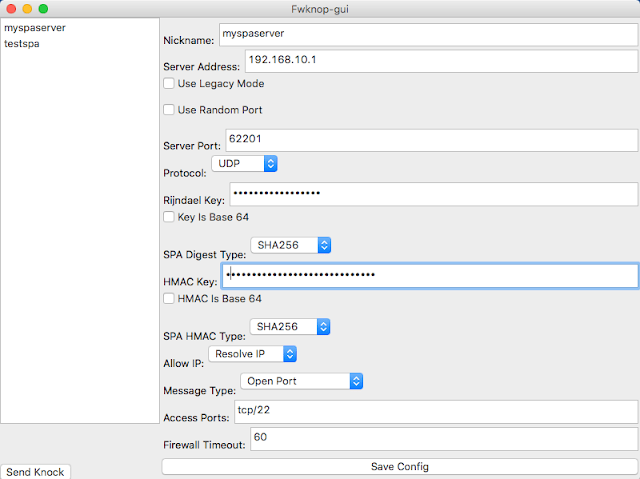
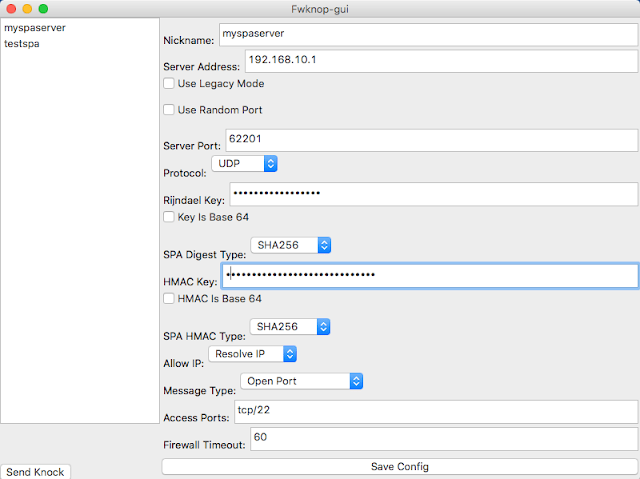
221Network ToolsFwknop – Single Packet Authorization & Port Knocking
fwknop implements an authorization scheme known as Single Packet Authorization (SPA) for strong service concealment. SPA requires only a single packet which...
-

 345DDOS
345DDOSDDoS Attack Unleashed – 500 Million packets-per-second
DDoS attacks are launched aiming to exhaust the resources of network, application or service so that the legitimate users unable to access...
-
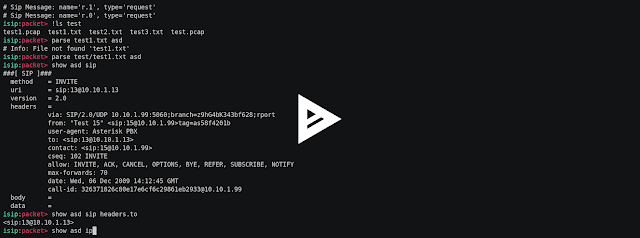
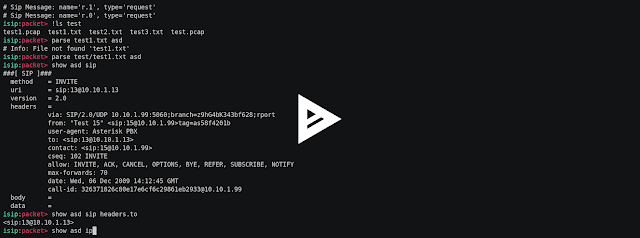 348Man-In-The-Middle
348Man-In-The-MiddleIsip – Interactive Sip Toolkit For Packet Manipulations, Sniffing, Man In The Middle Attacks, Fuzzing, Simulating Of Dos Attacks
Interactive sip toolkit for packet manipulations, sniffing, man in the middle attacks, fuzzing, simulating of dos attacks. Video Setup git clone https://github.com/halitalptekin/isip.git...
-
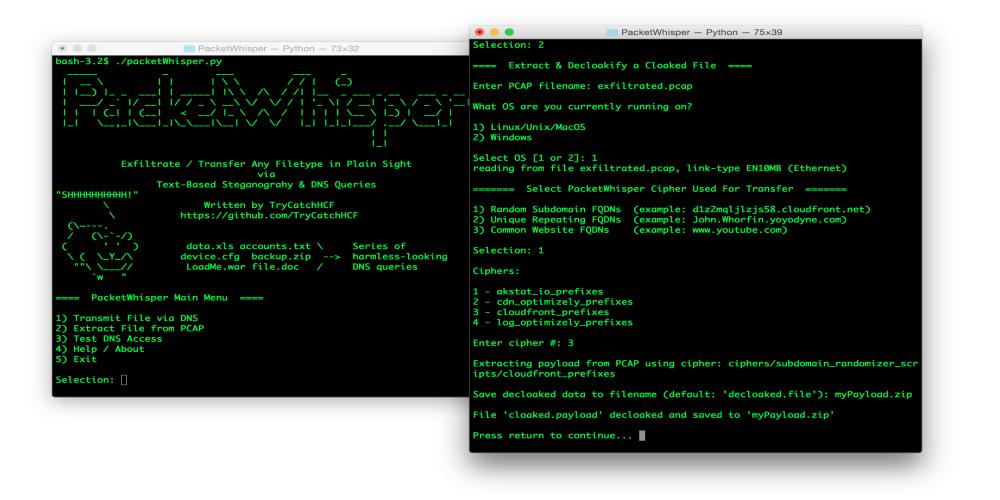
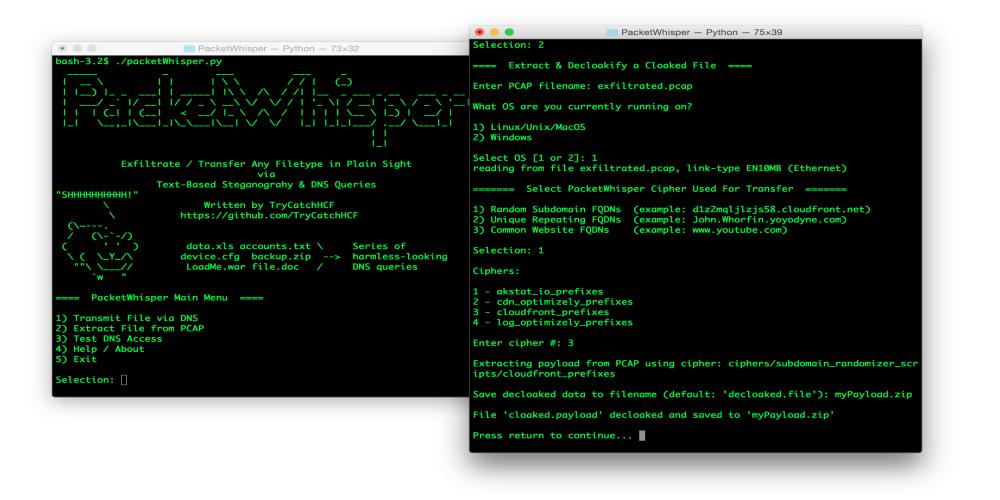 225Hack Tools
225Hack ToolsPacketWhisper Exfiltration Toolset
PacketWhisper – Stealthily Transfer Data & Defeat Attribution Using DNS Queries & Text-Based Steganography, without the need for attacker-controlled Name Servers or...
-

 354MITM
354MITMTcpflow – To Monitor, Capture & Dump Packets
Tcpflow is a TCP/IP Demultiplexer. Tcpflow is used to record traffic mainly between 2 hosts although it can be used to monitor...
-
 260Network Tools
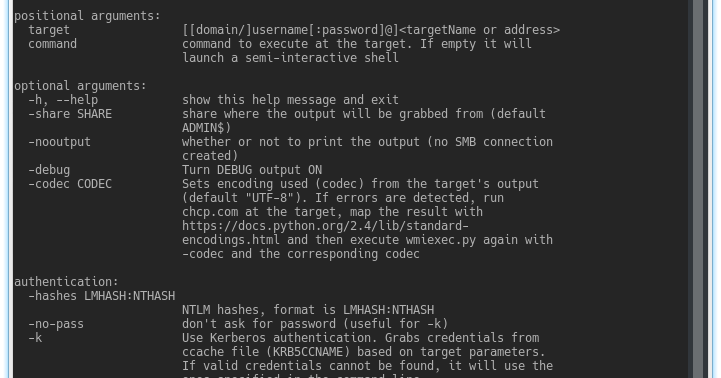
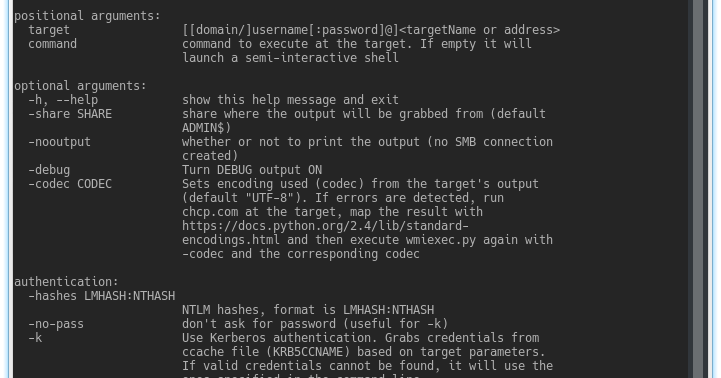
260Network ToolsImpacket – Collection Of Python Classes For Working With Network Protocols
Impacket is a collection of Python classes for working with network protocols. Impacket is focused on providing low-level programmatic access to the...
-
 254Incidents
254IncidentsThrowhammer the New Way to Launch Rowhammer Attacks via Network Packets
A team of researchers from Vrije University in Amsterdam and the University of Cyprus found a way to launch Rowhammer attacks through...
-

 299Packet Manipulation
299Packet ManipulationPolymorph – Real-time Network Packet Manipulation Framework
Polymoprh is a framework written in the Python3 programming language that allows the modification of network packets in real time, providing maximum...
-
Vulnerability Analysis
CyberScan – Tool To Analyse Packets, Decoding , Scanning Ports, And Geolocation
CyberScan is an open source penetration testing tool that can analyse packets , decoding , scanning ports, pinging and geolocation of an...
-
 268Incidents
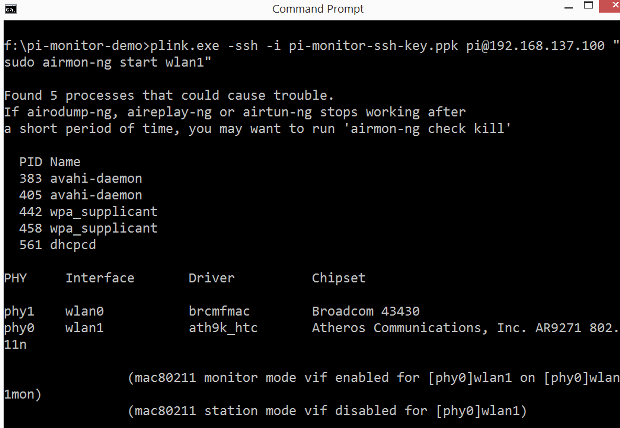
268IncidentsWi-Fi packet sniffing / monitoring on Windows using Raspberry Pi – inspired by Wimonitor
Wimonitor is a wonderful product from Hacker Arsenal that saves pentesters the hassle of having to configure VMs, carry compatible wireless cards that...






