Search results for "Payload"
-
 3.1KMalware
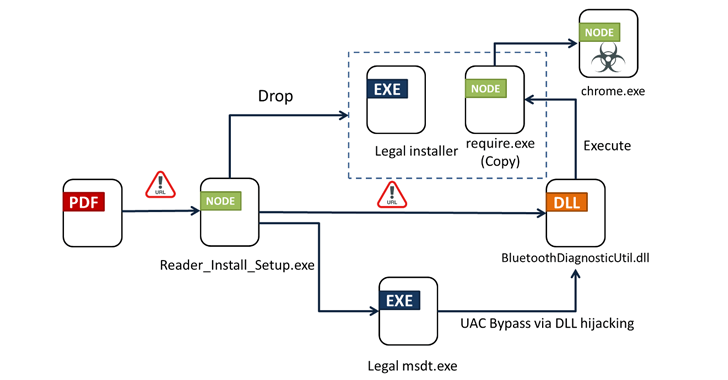
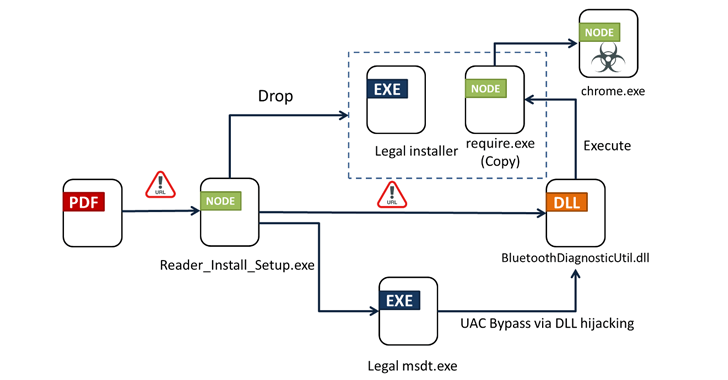
3.1KMalwareFrom PDFs to Payload: Bogus Adobe Acrobat Reader Installers Distribute Byakugan Malware
Bogus installers for Adobe Acrobat Reader are being used to distribute a new multi-functional malware dubbed Byakugan. The starting point of the...
-

 4.3KVulnerabilities
4.3KVulnerabilitiesSystemBC Malware’s C2 Server Analysis Exposes Payload Delivery Tricks
Cybersecurity researchers have shed light on the command-and-control (C2) server workings of a known malware family called SystemBC. “SystemBC can be purchased...
-
 4.1KMalware
4.1KMalwareAtomic Stealer Gets an Upgrade – Targeting Mac Users with Encrypted Payload
Cybersecurity researchers have identified an updated version of a macOS information stealer called Atomic (or AMOS), indicating that the threat actors behind...
-
 1.1KCyber Attack
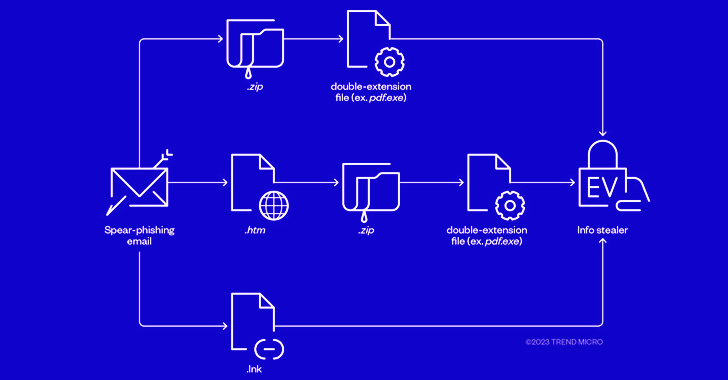
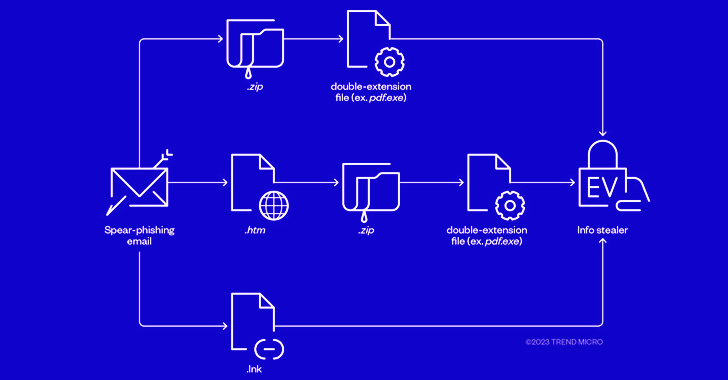
1.1KCyber AttackCybercriminals Combine Phishing and EV Certificates to Deliver Ransomware Payloads
The threat actors behind RedLine and Vidar information stealers have been observed pivoting to ransomware through phishing campaigns that spread initial payloads...
-
 2.8KMalware
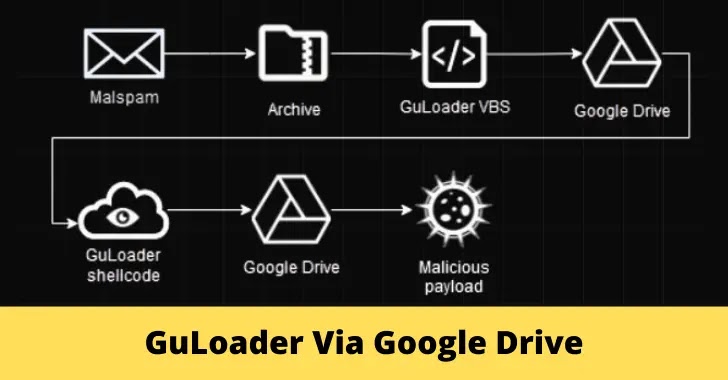
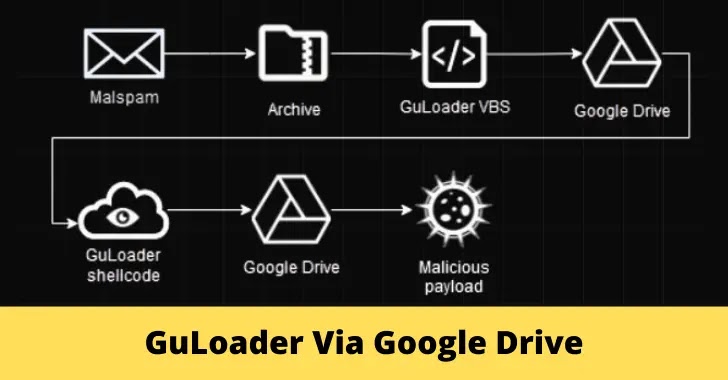
2.8KMalwareFully Encrypted GuLoader Uses Google Drive to Download Payloads
Antivirus products continuously advance to combat evolving threats, prompting malware developers to create new bypassing techniques like “packing” and “crypting,” GuLoader is...
-
 3.7KMalware
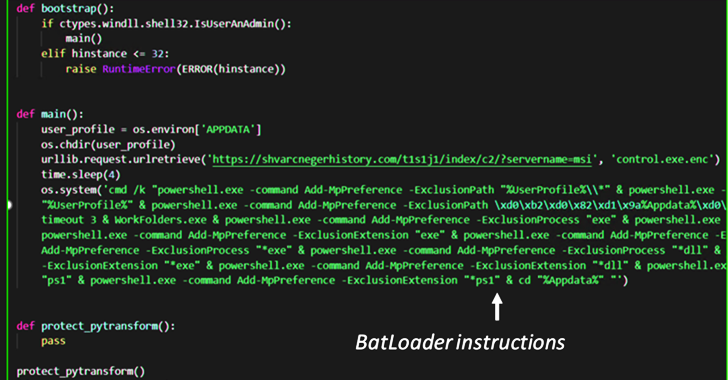
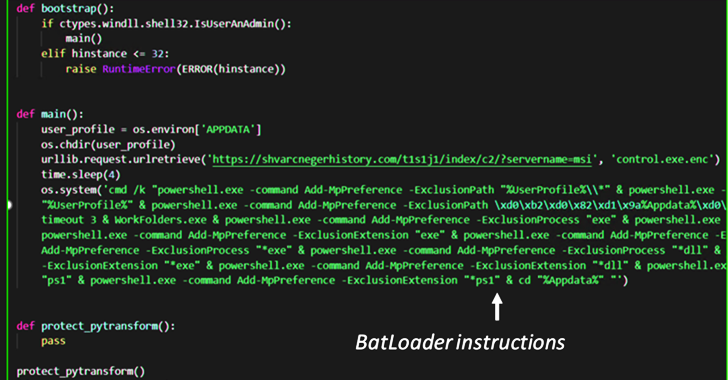
3.7KMalwareBATLOADER Malware Uses Google Ads to Deliver Vidar Stealer and Ursnif Payloads
The malware downloader known as BATLOADER has been observed abusing Google Ads to deliver secondary payloads like Vidar Stealer and Ursnif. According...
-
 4.0KMalware
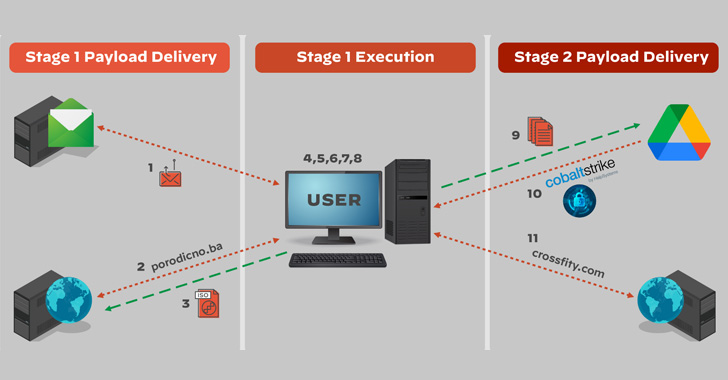
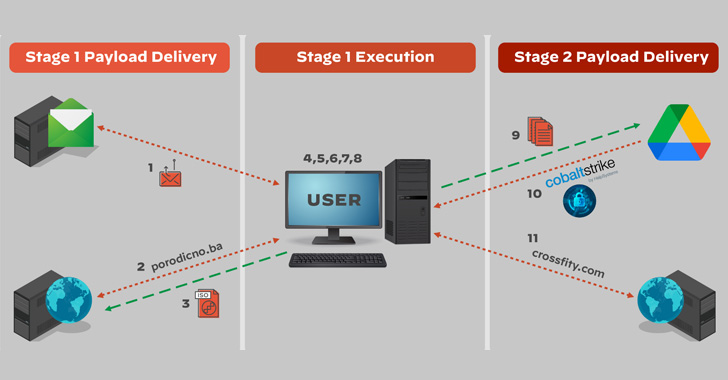
4.0KMalwareRussian Hackers Using DropBox and Google Drive to Drop Malicious Payloads
The Russian state-sponsored hacking collective known as APT29 has been attributed to a new phishing campaign that takes advantage of legitimate cloud...
-
 4.4KHack Tools
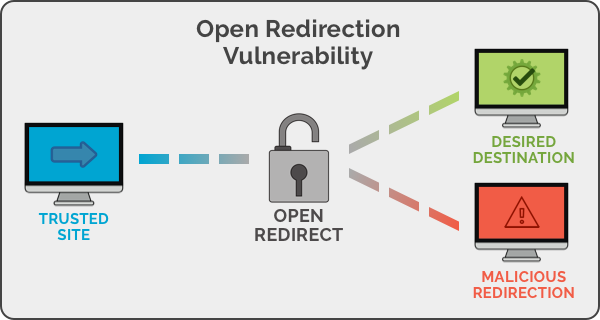
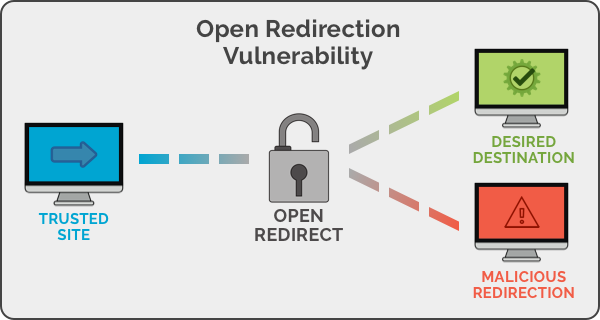
4.4KHack ToolsOpen Redirect Payload List
Unvalidated redirects and forwards are possible when a web application accepts untrusted input that could cause the web application to redirect the...
-

 1.5KHack Tools
1.5KHack ToolsCAPE – Malware Configuration And Payload Extraction
CAPE is a malware sandbox. It is derived from Cuckoo and is designed to automate the process of malware analysis with the...
-
 491Hack Tools
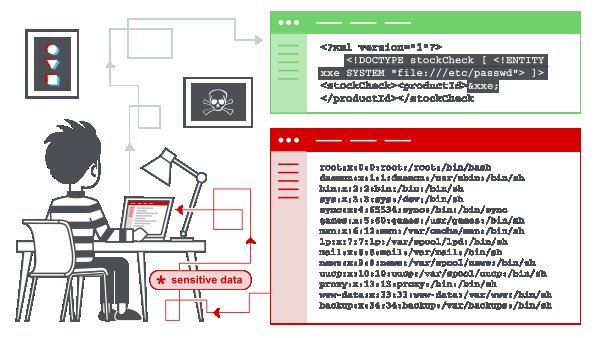
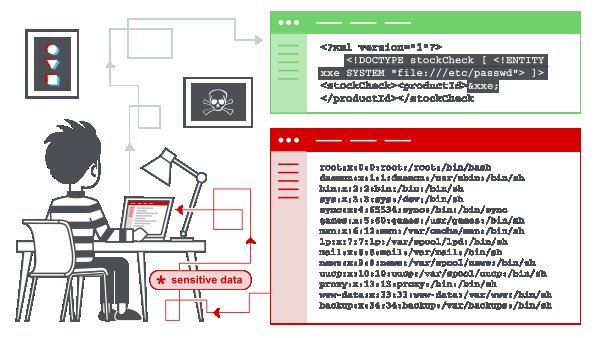
491Hack ToolsXML External Entity (XXE) Injection Payload List
In this section, we’ll explain what XML external entity injection is, describe some common examples, explain how to find and exploit various...
-
 2.2KHack Tools
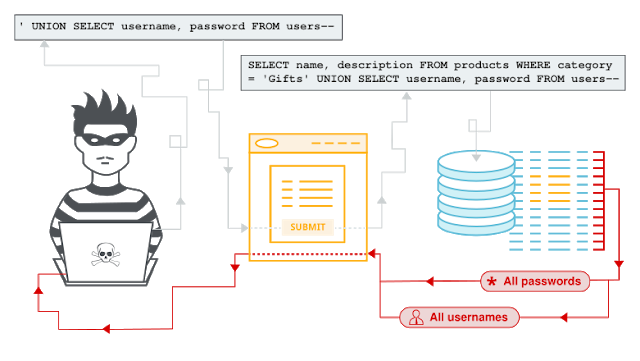
2.2KHack ToolsSQL Injection Payload List
SQL InjectionIn this section, we’ll explain what SQL injection is, describe some common examples, explain how to find and exploit various kinds...
-

 4.3KHack Tools
4.3KHack ToolsRFI/LFI Payload List
As with many exploits, remote and local file inclusions are only a problem at the end of the encoding. Of course it...
-
 1.7KNews
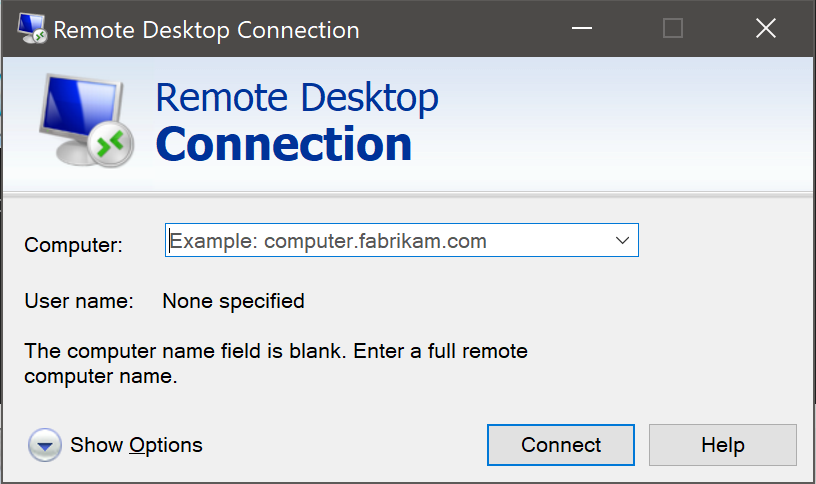
1.7KNewsMicrosoft warns users: “BlueKeep exploit will likely be used to deliver payloads more impactful and damaging than coin miners”
Microsoft’s security team believes that a more destructive BlueKeep attack is coming, and urges users and companies to install application patches in...
-
 3.4KHack Tools
3.4KHack ToolsDonut – Generates X86, X64, Or AMD64+x86 Position-Independent Shellcode That Loads .NET Assemblies, PE Files, And Other Windows Payloads From Memory
Donut generates x86 or x64 shellcode from VBScript, JScript, EXE, DLL (including .NET Assemblies) files. This shellcode can be injected into an...
-

 533Steganography
533SteganographyPixload – Image Payload Creating and Injecting tools
Set of tools for creating/injecting payload into images. Useful references for better understanding of pixload and its use-cases: Bypassing CSP using polyglot...
-
 403Exploitation Tools
403Exploitation ToolsPixload – Image Payload Creating/Injecting Tools
Set of tools for creating/injecting payload into images. Useful references for better understanding of pixload and its use-cases: Bypassing CSP using polyglot JPEGs...
-
 257Payloads
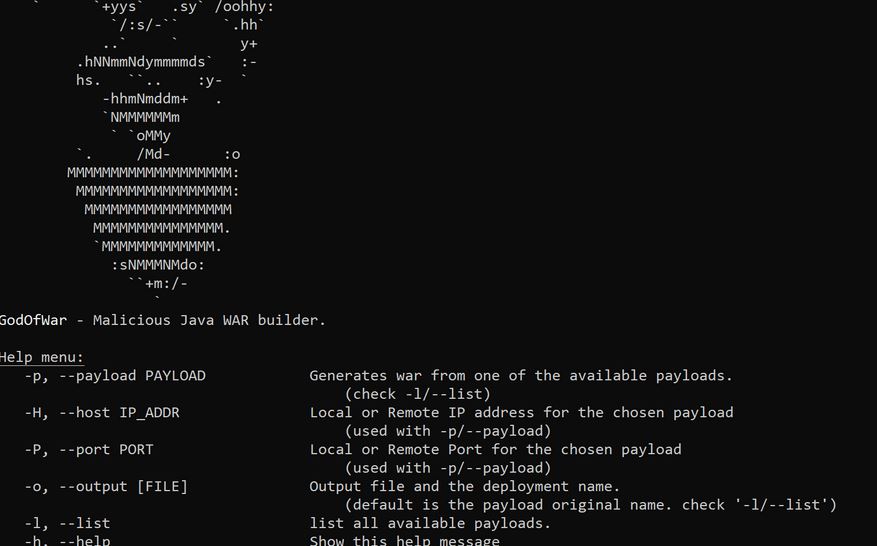
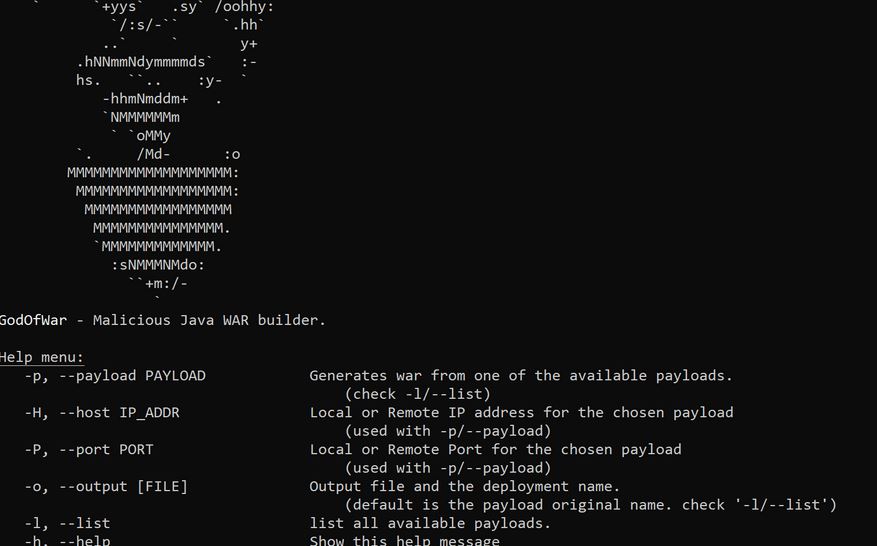
257PayloadsGodOfWar – Malicious Java WAR builder with built-in payloads
A command-line tool to generate war payloads for penetration testing / red teaming purposes, written in ruby. Features Preexisting payloads. (try -l/--list)...
-
 237Hack Tools
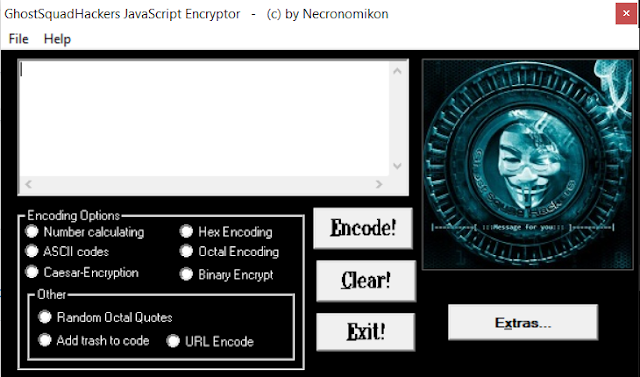
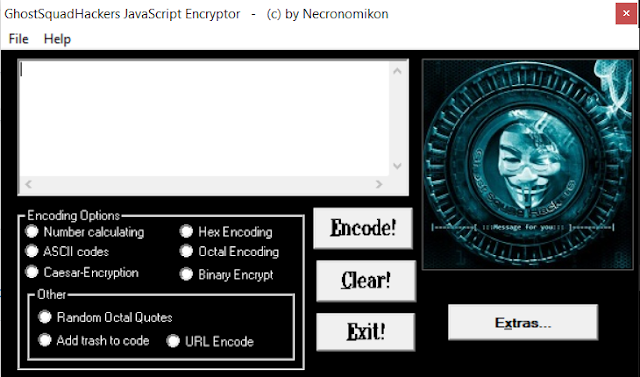
237Hack ToolsGhostSquadHackers – Encrypt/Encode Your Javascript Payloads
This tool is meant to encode and encrypt your javascript code/payloads. Features Number Calculating ASCII codes Caeser-Encryption Hex Encoding Octal encoding Binary...
-

 389Vulnerabilities
389VulnerabilitiesCreate Windows 10 FUD (Fully Undetectable) payload
Windows shell is what, every hacker loves. There are various Windows payloads are designed to bypass Windows OS security mechanism. According to...
-
 264Hack Tools
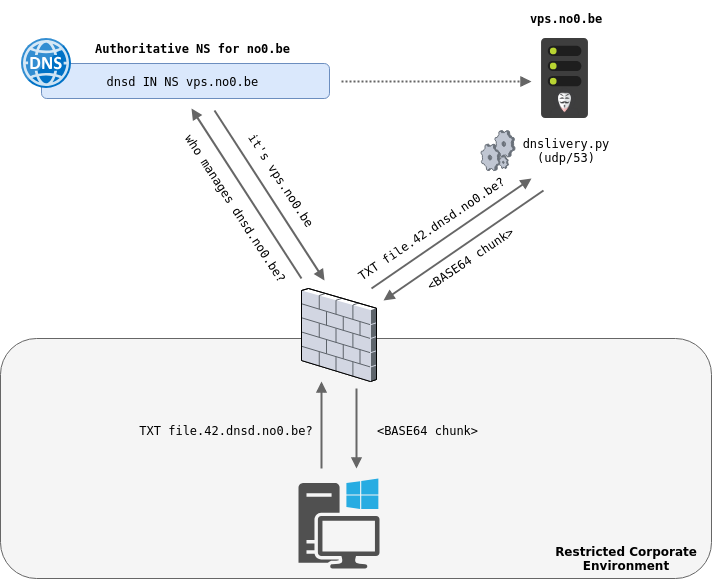
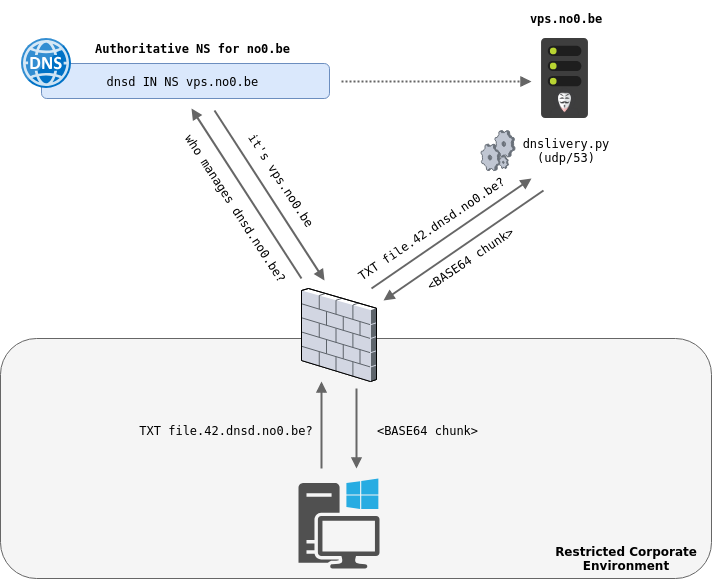
264Hack ToolsDNSlivery – Files and Payloads Delivery Over DNS
DNSlivery allows to deliver files to a target using DNS as the transport protocol and has been inspired by PowerDNS and Joff...
-
 281Malware
281MalwareChinese Hackers Infect Over 50,000 Windows MS-SQL and PHPMyAdmin Servers Worldwide with 20 Different Payloads
A new China-based campaign dubbed Nansh0u targets Windows MS-SQL and PHPMyAdmin servers worldwide. The attack campaign primarily targets servers belonging to the...






