Search results for "Proof Of Concept"
-

 997Vulnerabilities
997VulnerabilitiesCVE-2021-1810: Vulnerability in macOS allows bypassing Gatekeeper feature. Proof of concept available
Security researcher Rasmus Sten published a proof of concept (PoC) code to exploit a critical vulnerability in macOS Gatekeeper updated a few...
-

 195Vulnerability Analysis
195Vulnerability AnalysisMeltdown Exploit Proof of Concept
Speculative optimizations execute code in a non-secure manner leaving data traces in microarchitecture such as cache. Refer to the paper by Lipp...
-
 322Malware
322MalwareUsing n1n3 to Simulate an Evasive Fileless Malware – Proof Of Concept
Fileless malware are types of malicious code used in cyber attacks that don’t use files to launch the attack and carry on...
-
 267Articles
267ArticlesProof of Concept Code for WPA2 Krack Attack has been released
Security researchers have discovered several key management vulnerabilities in the core of Wi-Fi Protected Access II (WPA2) protocol that could allow an...
-
 212Hackers Repository
212Hackers RepositoryWebRTC can leak your IP address even if your behind a VPN Part 2 (Proof of Concept)
Welcome back in the last article (WebRTC can leak your IP address even if your behind a VPN). we talked a little about...
-

 1.5KVulnerabilities
1.5KVulnerabilitiesProof-of-Concept Exploit Released for Progress Software OpenEdge Vulnerability
Technical specifics and a proof-of-concept (PoC) exploit have been made available for a recently disclosed critical security flaw in Progress Software OpenEdge...
-

 3.4KData Security
3.4KData SecurityA proof-of-concept (PoC) exploit code released for critical privilege elevation vulnerability CVE-2022-37969 (CVSS score: 7.8) affecting Windows 10 & 11
The Windows Common Log File System (CLFS) Driver has an elevation of privilege vulnerability identified as CVE-2022-37969 (CVSS score: 7.8). For reporting...
-
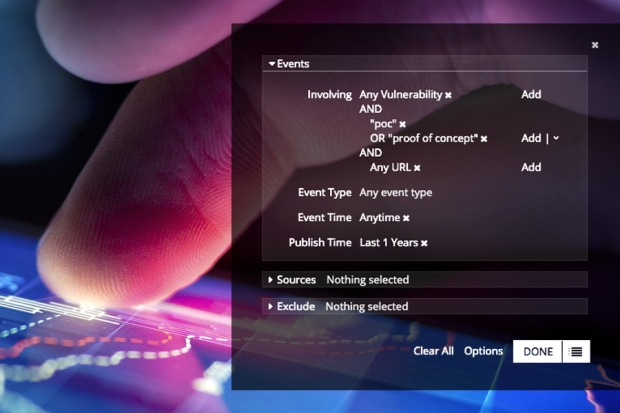
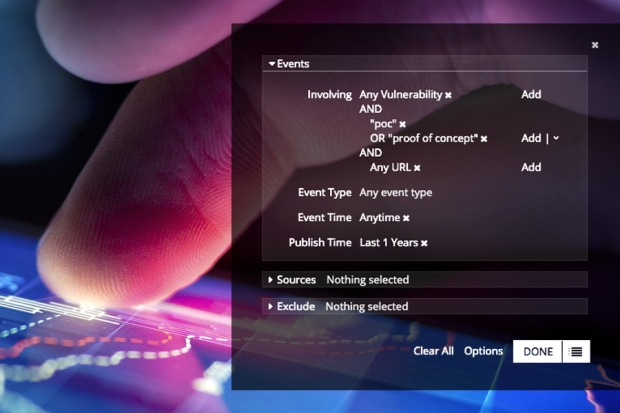 286Data Security
286Data SecurityProve It: The Rapid Rise of 12,000 Shared Proof-of-Concept Exploits
Recorded Future’s real-time threat intelligence product allows analysts access to hundreds of thousands of sources that are normalized, organized, and searchable for...
-

 451Privacy
451PrivacyWhatsApp privacy is ‘broken,’ reveals proof‑of‑concept hack
WhatsApp's privacy settings are "broken" and can be bypassed by downloading a simple bit of software, claims the Dutch developer behind proof-of-concept...
-

 299Banking
299BankingDutch University unveils ‘fraud proof’ credit card concept
A Dutch university has reportedly made great steps towards making the dream of a 'fraud-proof' credit card a reality by utilizing quantum...






