Search results for "Registry"
-
 1.2KData Security
1.2KData SecurityEasily hack into Azure Bastion and Azure Container Registry via XSS vulnerabilities
Microsoft Azure Bastion and Azure Container Registry have each been found to have one potentially “dangerous” security flaw that, if taken advantage...
-
 2.1KMalware
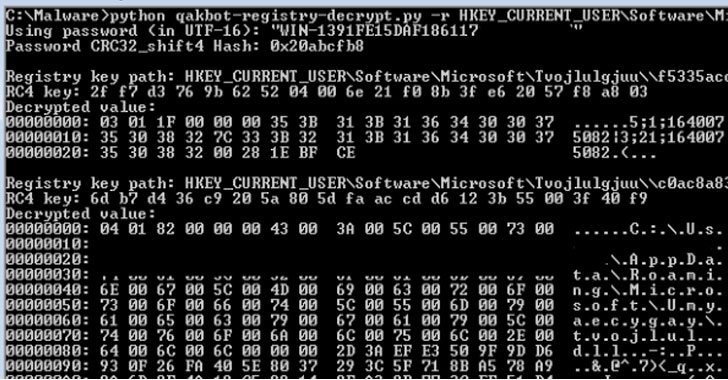
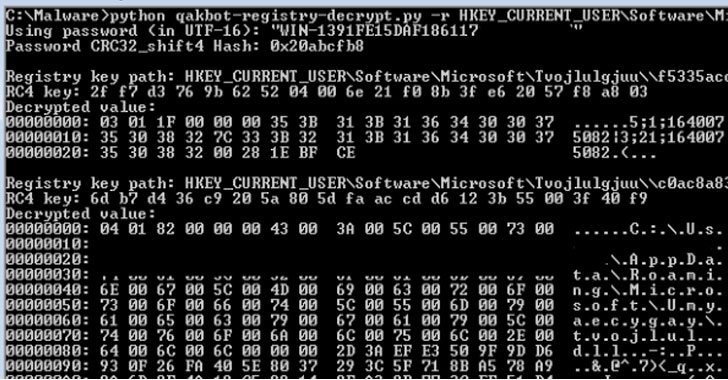
2.1KMalwareResearchers Decrypted Qakbot Banking Trojan’s Encrypted Registry Keys
Cybersecurity researchers have decoded the mechanism by which the versatile Qakbot banking trojan handles the insertion of encrypted configuration data into the...
-

 627Malware
627MalwareBeware!! Hackers Hide Fileless Malware “DarkWatchman” In The Windows Registry
A new malware with highly-capable JavaScript RAT, which is paired with a C# keylogger has been discovered by the security analysts at...
-

 1.4KMalware
1.4KMalwareDarkWatchman: This advanced fileless malware only writes data in Windows Registry thus can’t be detected by security solutions
Prevailion security specialists report that a newly identified spear phishing campaign is distributing a new remote access Trojan (RAT) capable of manipulating...
-
 2.7KMalware
2.7KMalwareNew Fileless Malware Uses Windows Registry as Storage to Evade Detection
A new JavaScript-based remote access Trojan (RAT) propagated via a social engineering campaign has been observed employing sneaky “fileless” techniques as part...
-
 4.0KHack Tools
4.0KHack ToolsSharpHide – Tool To Create Hidden Registry Keys
Just a nice persistence trick to confuse DFIR investigation. Uses NtSetValueKey native API to create a hidden (null terminated) registry key. This...
-
 2.2KHack Tools
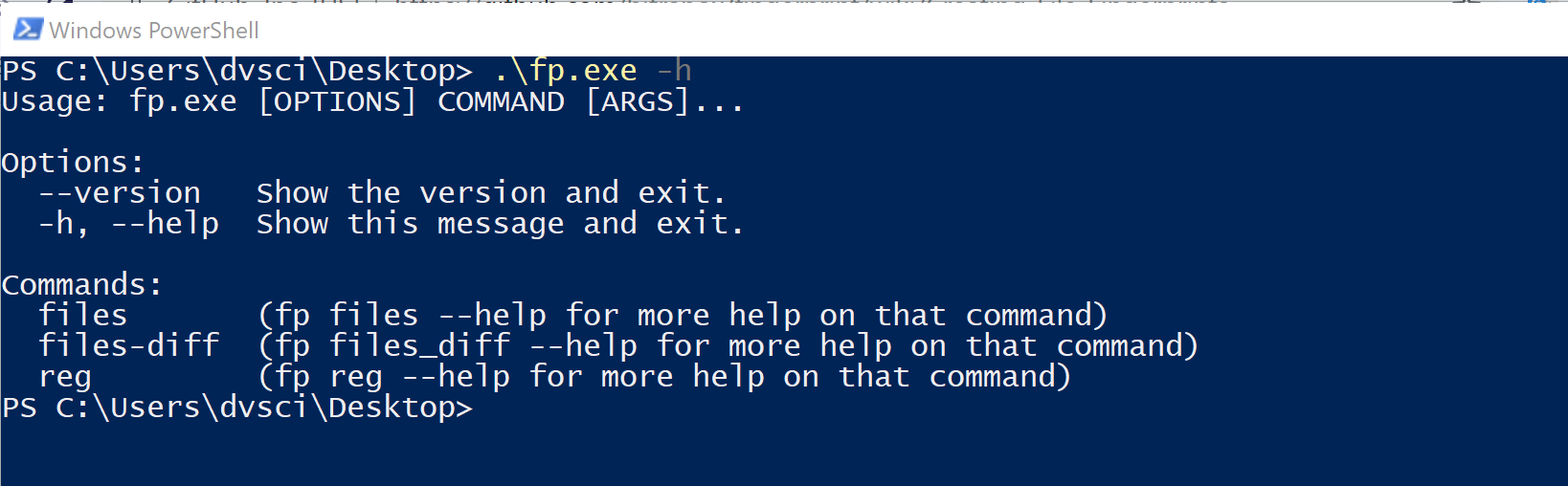
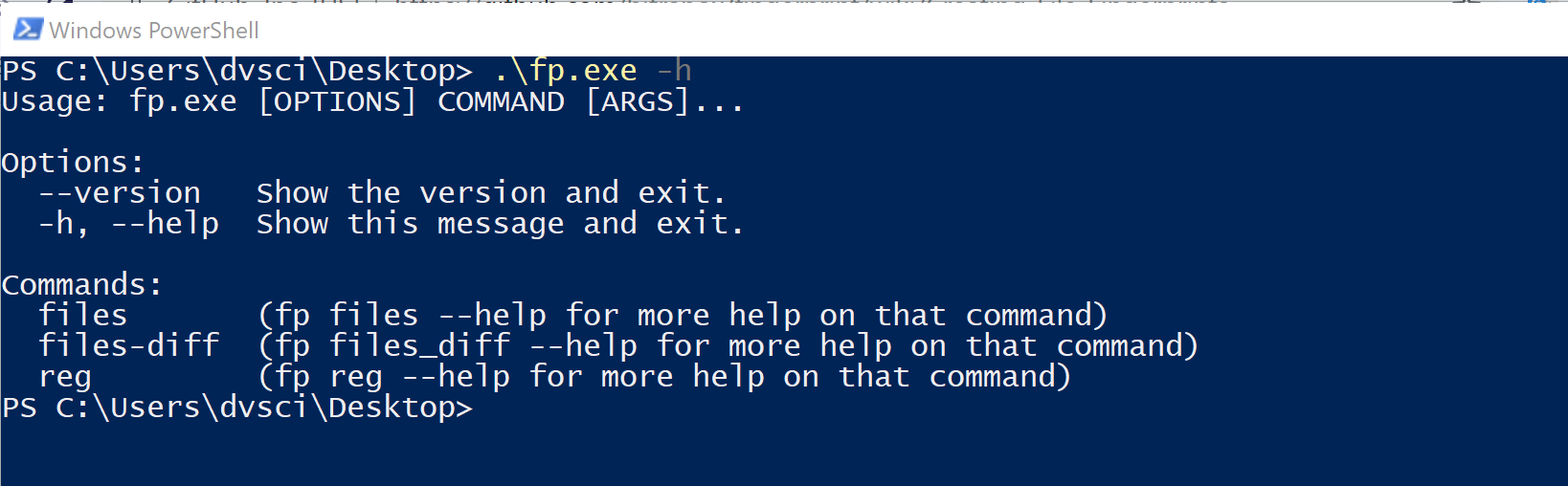
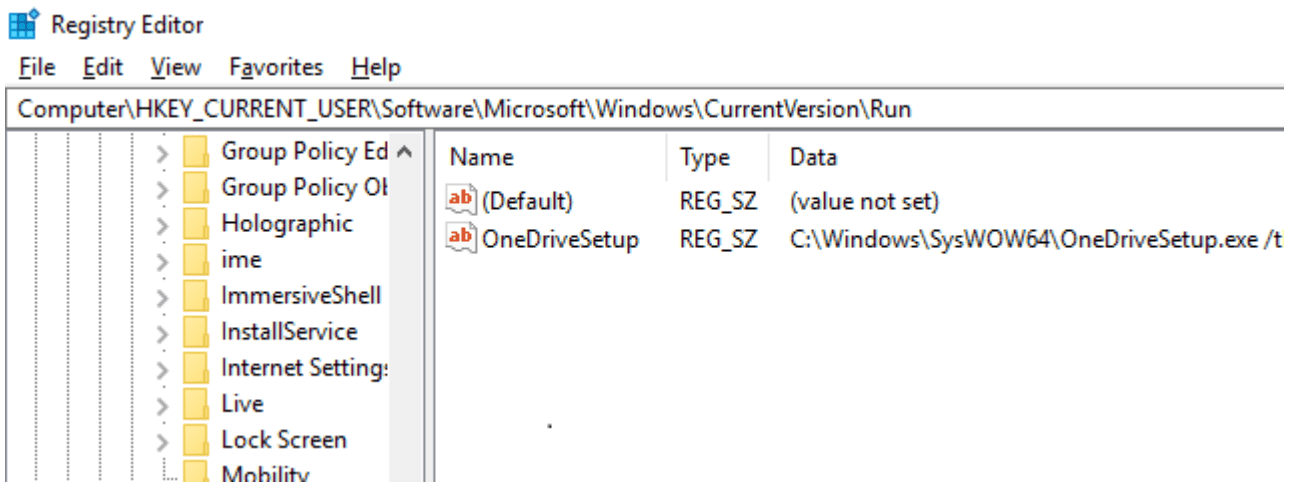
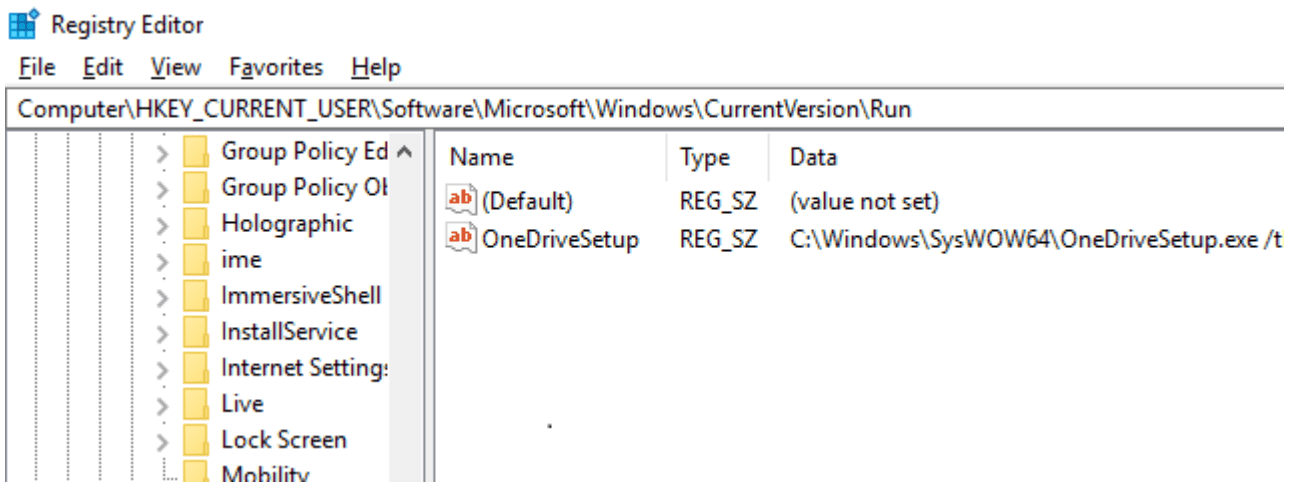
2.2KHack Toolsfingerprint: Monitoring Registry and File Changes in Windows
fingerprint Monitoring Registry and File Changes in Windows – forensic analytics for windows registry and files “fingerprint” records the state of a...
-
 4.9KHack Tools
4.9KHack ToolsSharpHide: Tool to create hidden registry keys
SharpHide Just a nice persistence trick to confuse DFIR investigation. Uses NtSetValueKey native API to create a hidden (null-terminated) registry key. This...
-
 386News
386NewsMicrosoft Explains Why 800 Million Windows 10 Users Can’t Auto Backup Registry
If you’re a Windows user, chances are quite less you haven’t opened Windows Registry after tweaking some values just the way a...
-
 284News
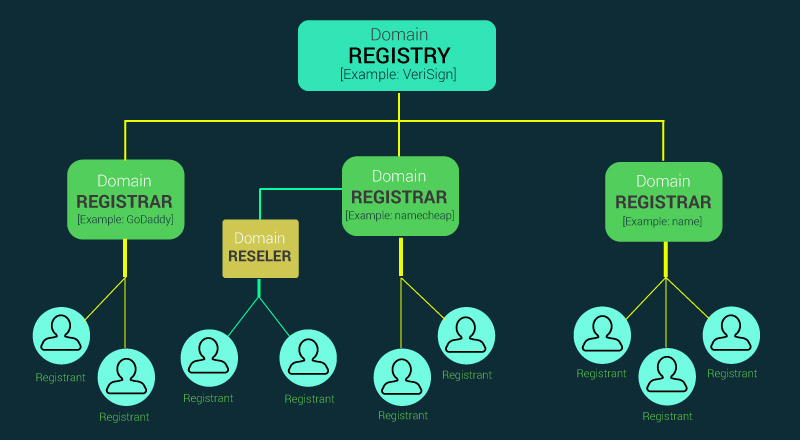
284NewsDomain Name Hierarchy (Registry vs Registrar)
Domain registration and management involves multiple parties with different roles, like Registry, Registrar, Reseller & Registrant (Domain Name Hierarchy). On top of...
-
 246Incidents
246IncidentsSimple Registry Hacks Bypass Windows Digital Signature, Opening Gates For Malicious Code
Windows Digital Signature check is a mechanism included in Microsoft Windows to make sure that the software or driver you’re trying to...
-

 312Malware
312MalwareFileless malware that uses PowerShell scripts from Window’s registry leading to Click Fraud Malware Campaign
Nowadays Hackers Distributing Advanced Fileless Malware with Evasion capabilities which are very Difficult to Detect. These types of malware sit in the...
-

 122Cyber Crime
122Cyber CrimeMalicious registry keys: Reflective injection
In recent months, we have started to receive various reports about suspicious and malicious registry keys that had been created on users’...
-

 235Lists
235ListsTop 10 Free Registry Cleaners For Microsoft Windows PC
Short Bytes: Registry Cleaners are the software which does the job of removing outdated registry entries from Windows registry. These registry entries...
-
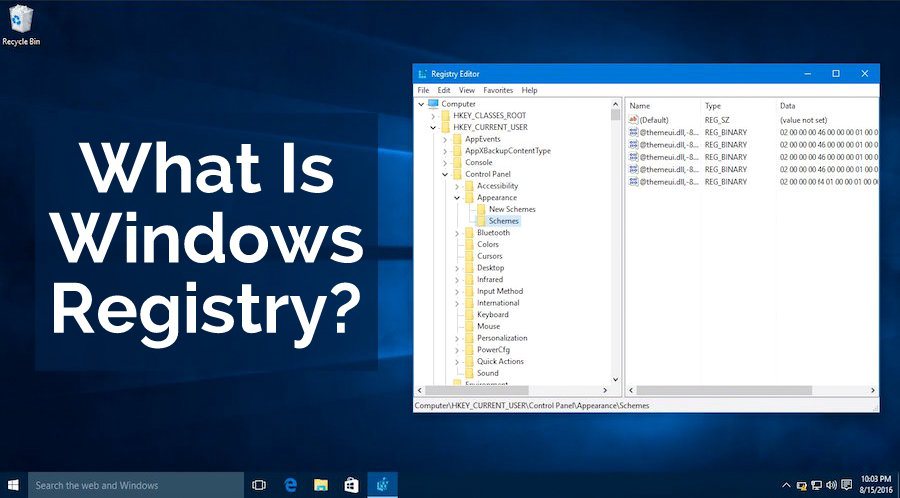
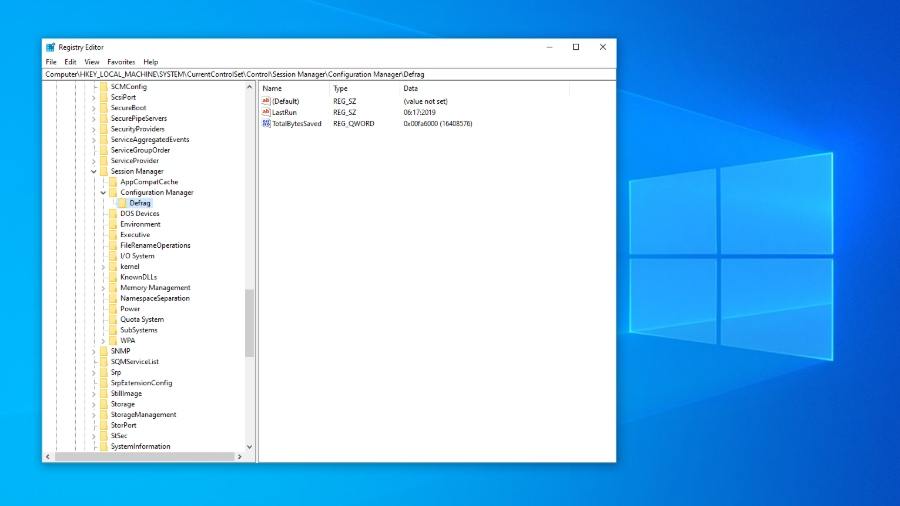
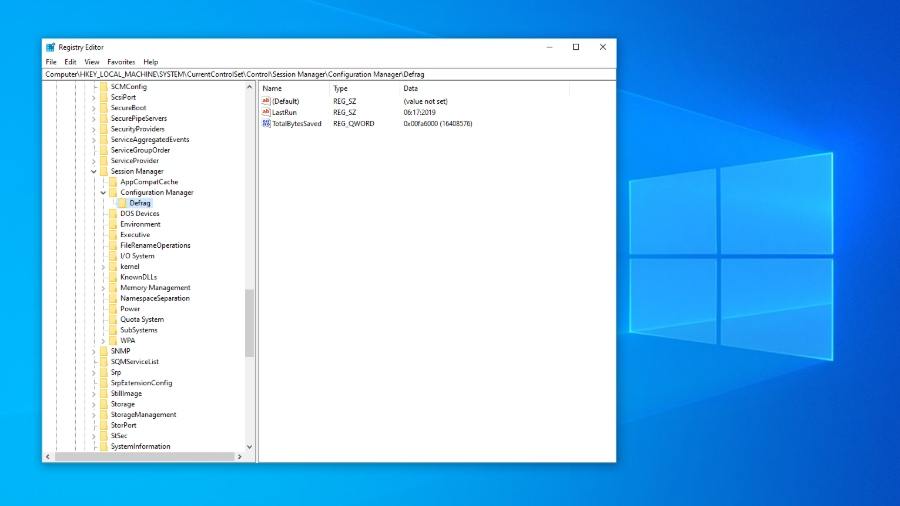
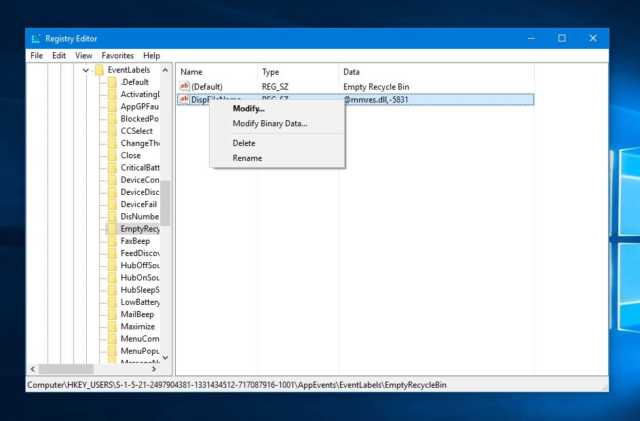
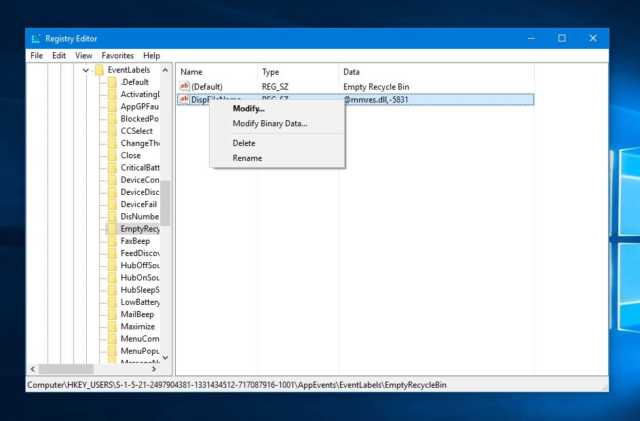
 285How To
285How ToWhat Is Windows Registry And How To Use It — Everything Explained
Short Bytes: The Windows Registry could be considered a big collection of all the details about your computer. It has information about...
-
 424How To
424How ToHow To Find Windows Product Key Using CMD, PowerShell, And Windows Registry
Short Bytes: If you are willing to reinstall your Windows operating system, it’s possible that you’ll be stuck at some point due...
-
 169Data Security
169Data SecurityAmerican Samoa Domain Registry Was Exposing Client Data Since the Mid-1990s
Flaw allowed anyone to edit & take control over .as domains. A British security researcher that goes online only by the name of...
-

 293Geek
293GeekWindows Registry now Providing Shelter to Destructive Kovter Malware
Kovter Trojan can hide in Windows registry and does not need to be stored on the computer’s hard drive- claims Symantec —...
-
 148Data Security
148Data SecurityKovter Malware Now Lives Solely in the Windows Registry
Symantec’s researchers have discovered a new version of the Kovter trojan, which now mimics the Poweliks malware and is able to live...
-

 240Scams
240ScamsFTC issues record $7.5m fine for calls to U.S. veterans on Do Not Call Registry
A telemarketing company has been hit with a $7.5m fine for repeatedly contacting people on the Do Not Call Registry - the...






