Search results for "Reporting"
-

 2.3KIncidents
2.3KIncidentsIndia relaxes cyber security incidents reporting rules and says new rules apply to MNCs
Cybersecurity agencies in India are slightly relaxing their controversial and complex requirements for reporting on information security incidents, although they reaffirm that...
-
 3.9KMalware
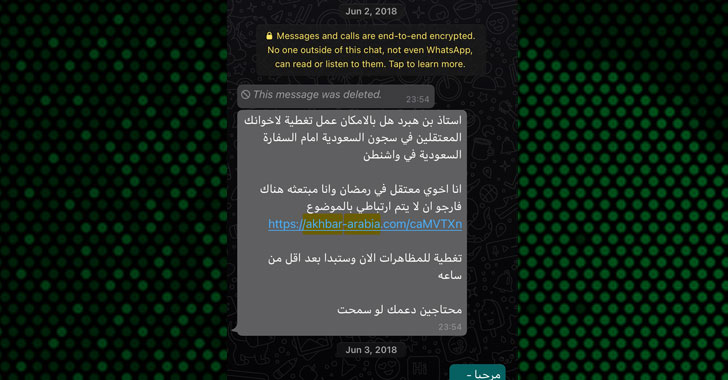
3.9KMalwareNYT Journalist Repeatedly Hacked with Pegasus after Reporting on Saudi Arabia
The iPhone of New York Times journalist Ben Hubbard was repeatedly hacked with NSO Group’s Pegasus spyware tool over a three-year period...
-

 413Vulnerabilities
413VulnerabilitiesFacebook Now Pays Hackers for Reporting Security Bugs in 3rd-Party Apps
Following a series of security mishaps and data abuse through its social media platform, Facebook today expanding its bug bounty program in...
-
 487Data Security
487Data SecurityZerodium to pay up to $2.5 million for reporting 0-day Android exploits
Zero-Day Android exploits are now more valuable then iOS exploits. The infosec and premium zero-day acquisition platform Zerodium known for selling zero-day...
-

 416Data Security
416Data SecurityBiggest credit reporting firm pays $700M USD data breach fine
Data protection specialists say that, after two years, business advisory firm Equifax has reached an agreement with U.S. government agencies to pay...
-

 343Geek
343GeekHacker gets $30,000 for reporting hack Instagram account flaw
The flaw allowed anyone with knowledge of brute force attack to hack Instagram accounts without raising any suspicion. How to hack Instagram...
-
 297Vulnerability Scanners
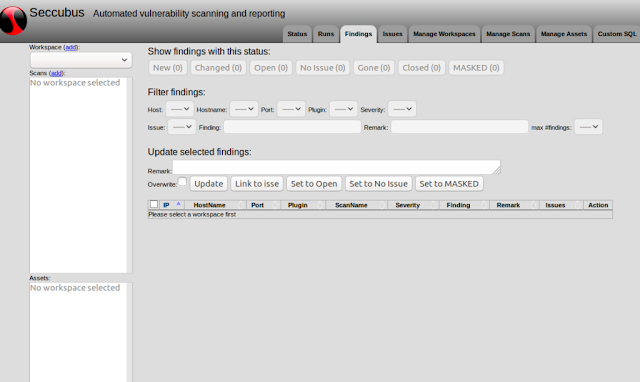
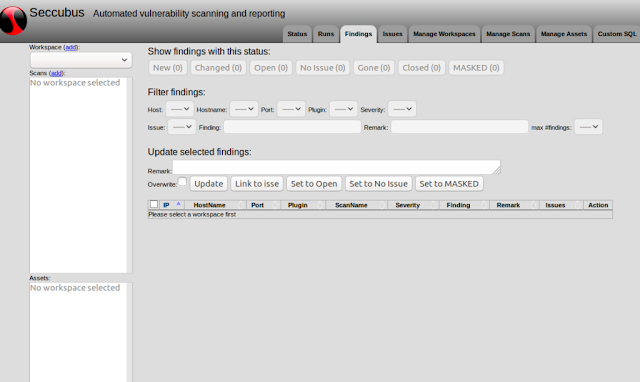
297Vulnerability ScannersSeccubus – Automated Vulnerability Scanning, Reporting And Analysis Tool
Seccubus automates regular vulnerability scans with various tools and aids security people in the fast analysis of its output, both on the...
-

 253Cyber Crime
253Cyber CrimeEthical hacker may get 8 years in prison for reporting flaws in Magyar Telekom
Hungary’s Prosecution Service has accused an ethical hacker and computer specialist of infiltrating the Magyar Telekom database. The office found him involved...
-

 269Data Security
269Data SecurityFacebook will pay you $40k USD for reporting bug
The social network would pay up to $40k USD for reporting errors that allow a single account takeover In the middle...
-
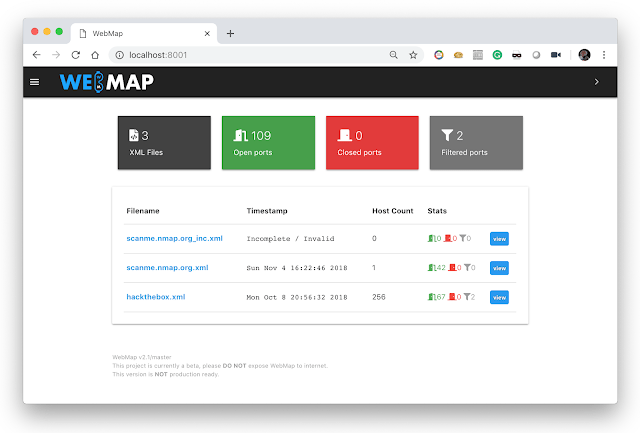
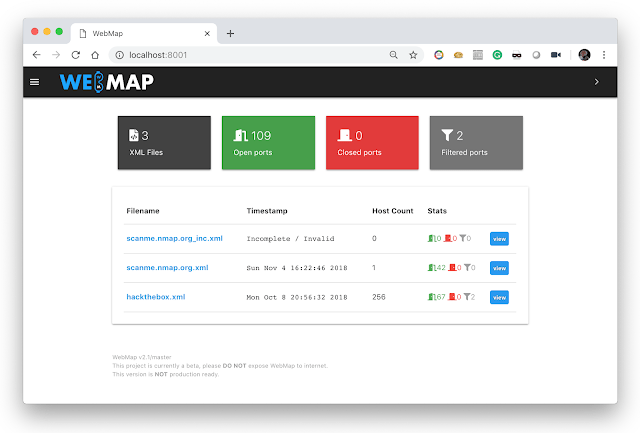 328Information Gathering
328Information GatheringWebMap – Nmap Web Dashboard And Reporting
A Web Dashbord for Nmap XML Report Usage You should use this with docker, just by sending this command: $ mkdir /tmp/webmap...
-
 316Geek
316GeekMicrosoft bug bounty program: $250k for reporting Meltdown & Spectre type flaws
The bug bounty program will remain open until December 31st, 2018. Recently, the identification of serious CPU flaws called Spectre and Meltdown shook...
-

 215Vulnerabilities
215VulnerabilitiesVulnerability Reporting Delays by China
According to an information security firm, China is attempting to cover up inexplicable delays in public reporting of high-risk software security holes...
-

 193Cyber Crime
193Cyber CrimeUS rules on reporting cybersecurity flaws set to change according to source
Cyber vulnerability hoarding? The US government publishes its Vulnerabilities Equities Policy (VEP) and describes the process by which cyber flaws found by...
-
 230Hacked
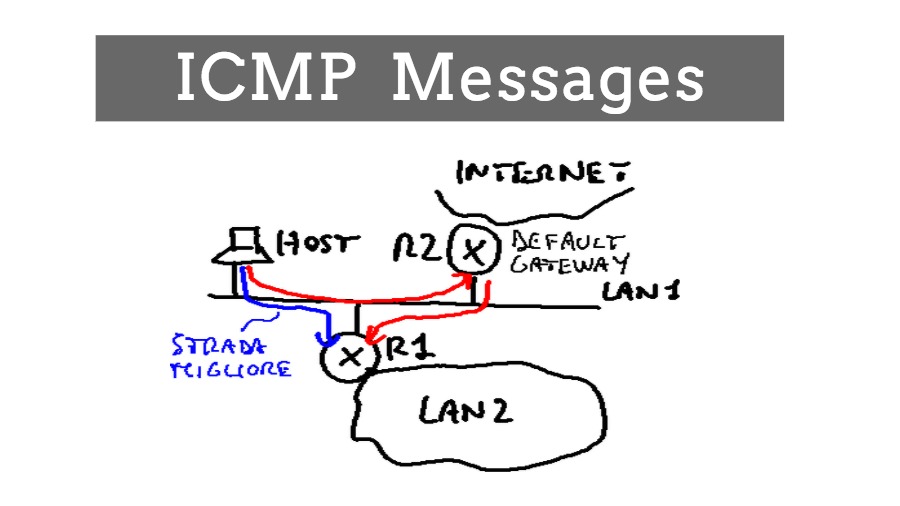
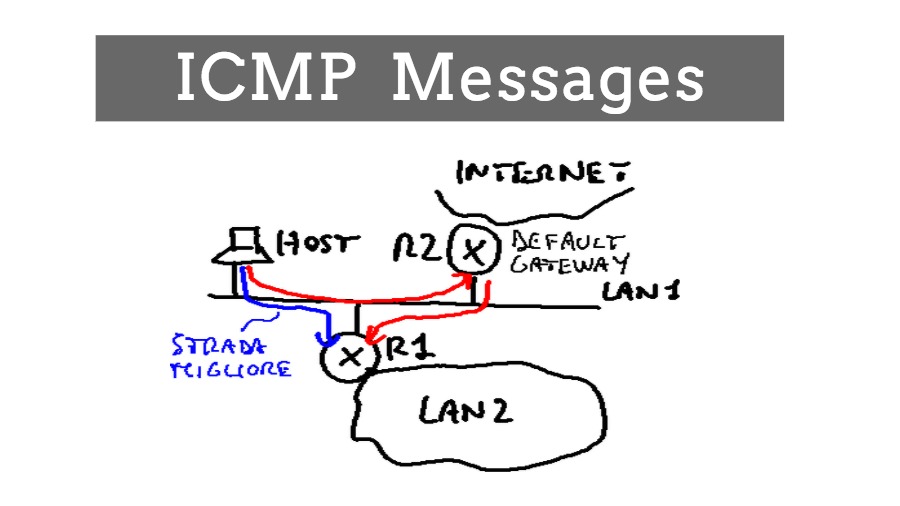
230HackedICMP: Error Reporting And Query Fetching Messages
There are so many protocols out there in the computer networks world which focus on the QoS and improving data transmission quality...
-

 315Data Breach
315Data BreachPizza Hut Hacked – Users Reporting Fraudulent Transactions on their Cards
Pizza Hut hacked and some of its clients who utilized the fast food chain’s website and application were influenced by the data...
-
 305Reporting
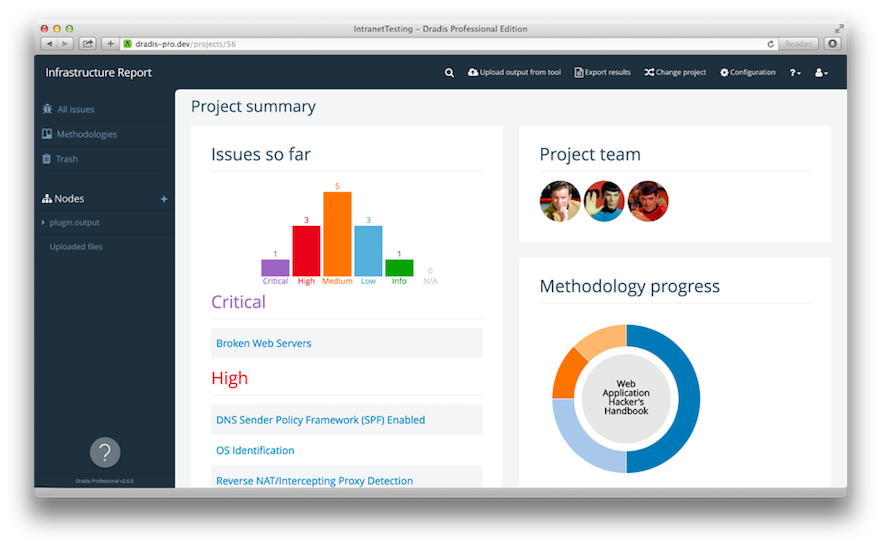
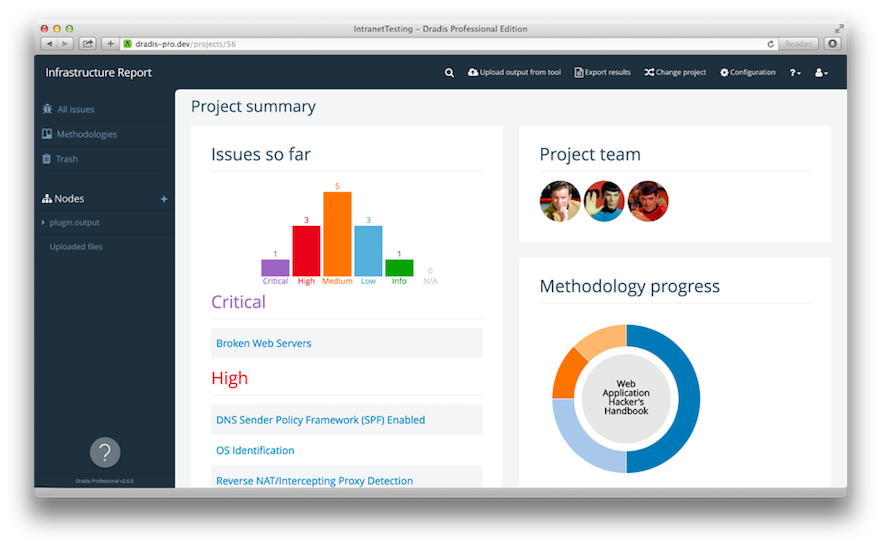
305ReportingDradis Framework – Collaboration and reporting for IT Security teams
Dradis is an open-source collaboration framework, tailored to InfoSec teams. Goals Share the information effectively. Easy to use, easy to be adopted....
-

 310Geek
310GeekGet $1M for reporting zero-day flaws in Tor to “help Govt fight crime”
Usually, a bug bounty program helps companies secure their software and products from zero day vulnerabilities that can cause massive damage if cyber...
-

 287News
287NewsCredit Reporting Firm Equifax Hacked; SSNs of 143M Americans Stolen
Another day, another data breach but this one will haunt the targeted customers for a long time. Equifax, a consumer credit reporting...
-

 225Malware
225MalwareFBI: Victims Aren’t Reporting Ransomware Attacks
Despite being an expanding threat, ransomware infections are rarely reported to law enforcement agencies, according to conclusions from the 2016 Internet Crime...
-

 206Geek
206GeekGoogle will Now Pay Hackers $200,000 for Reporting Bugs in Android
The search engine and tech giant Google has now increased the reward for finding bugs in Android OS to $200,000. Stepping up...
-

 241How To
241How ToLUNAR – Lockdown UNix Auditing and Reporting
It can perform a lockdown. Unlike some other scripts it has the capability to backout changes. Files are backed up using cpio...






