Search results for "Scan"
-
 4.0KMalware
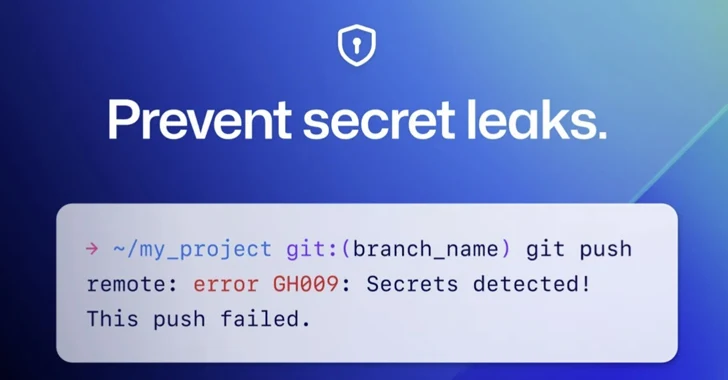
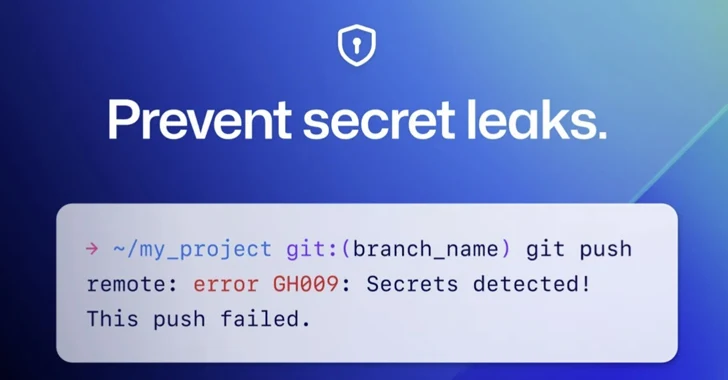
4.0KMalwareGitHub Rolls Out Default Secret Scanning Push Protection for Public Repositories
GitHub on Thursday announced that it’s enabling secret scanning push protection by default for all pushes to public repositories. “This means that...
-

 3.5KLeaks
3.5KLeaksHow To Scan a QR Code On iPhone
The iPhone offers multiple ways of scanning QR codes, but the quickest and easiest method is using its built-in camera app. Open...
-

 235Data Security
235Data SecurityFree Citrix ADC Zero-Day Scanner Tool allows discovering CVE-2023-3519 vulnerable servers
In the past, Citrix was found to have a Zero-Day vulnerability in its Citrix NetScaler Application Delivery Controller (ADC), which made it...
-
 1.7KMalware
1.7KMalwareMalicious Apps Use Sneaky Versioning Technique to Bypass Google Play Store Scanners
Threat actors are leveraging a technique called versioning to evade Google Play Store’s malware detections and target Android users. “Campaigns using versioning...
-

 3.2KData Breach
3.2KData Breach10 Best Vulnerability Scanner Tools For Penetration Testing – 2023
A Vulnerability Scanner Tools is one of the essential tools in IT departments Since vulnerabilities pop up every day and thus leaving...
-
 4.8KMalware
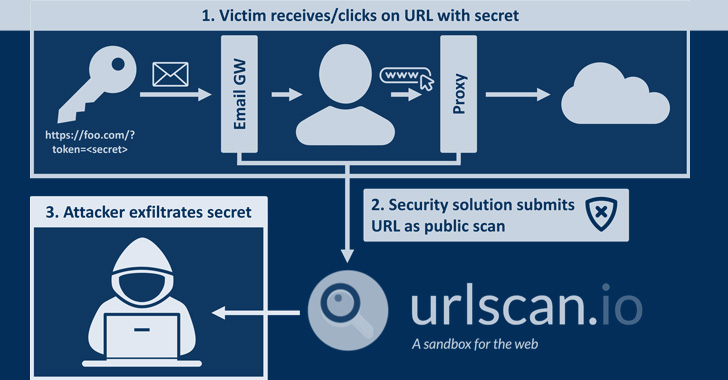
4.8KMalwareExperts Find URLScan Security Scanner Inadvertently Leaks Sensitive URLs and Data
Security researchers are warning of “a trove of sensitive information” leaking through urlscan.io, a website scanner for suspicious and malicious URLs. “Sensitive...
-

 1.9KData Security
1.9KData SecurityAvast open sources two great YARA tools. YaraNG a YARA Scanner and YLS a YARA Development Environment
A well-known tool in the security sector for classifying and identifying malware samples is YARA. Avast just gave the open-source community two...
-

 3.7KVulnerabilities
3.7KVulnerabilitiesWhy Vulnerability Scanning is Critical for SOC 2
SOC 2 may be a voluntary standard, but for today’s security-conscious business, it’s a minimal requirement when considering a SaaS provider. Compliance...
-

 823Malware
823MalwareChinese Hackers Used ScanBox Framework in Recent Cyber Espionage Attacks
A months-long cyber espionage campaign undertaken by a Chinese nation-state group targeted several entities with reconnaissance malware so as to glean information...
-
 1.8KVulnerabilities
1.8KVulnerabilitiesCritical RCE Vulnerability in Google’s VirusTotal Platform Let Attackers Scans Capabilities
There is a security vulnerability in the VirusTotal platform that has been discovered by researchers, and it has the potential to be...
-

 2.6KScams
2.6KScamsThink before you scan: How fraudsters can exploit QR codes to steal money
QR codes are all the rage and scammers have taken notice. Look out for dangers lurking behind those little black-and-white squares.
-

 1.7KCyber Crime
1.7KCyber CrimeGoogle Declares Prizes for Tsunami Security Scanner Add-ons
Earlier this week, in a statement, Google declared that it is issuing cash payouts to persons who help the company increase the...
-

 4.7KSurveillance
4.7KSurveillanceApple’s neuralMatch tool will scan iPhones for child abuse content
Apple has developed a system dubbed neuralMatch to locate child sexual abuse material/CSAM, and for now, it will scan iPhones of users...
-

 2.5KVulnerabilities
2.5KVulnerabilitiesCybercriminals are scanning servers for the Microsoft Exchange ProxyShell RCE vulnerabilities after technical details presented at the Black Hat
Researchers report the detection of multiple attempts to exploit ProxyShell, a set of remote code execution flaws in Microsoft Exchange disclosed during...
-

 1.7KTutorials
1.7KTutorialsFind Firewall & CDN used a website during Pentest with VXSCAN
Information gathering phase shows how an pentester should prepare for his next phases. Because in this phase pentester have to collect information...
-

 4.3KMalware
4.3KMalwareMalicious Android App Posed As QR Scanner To Launch Joker Malware That Steals SMS Data
Researchers uncovered a new wave of Android malware campaign ” Joker” which posed as a QR scanner to target Android users. Joker...
-
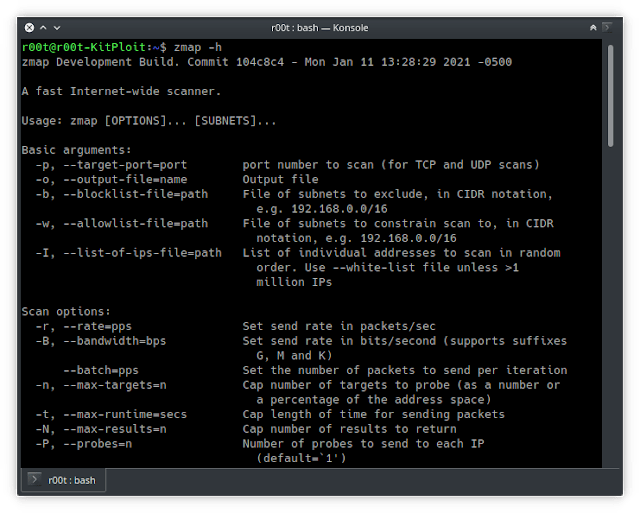
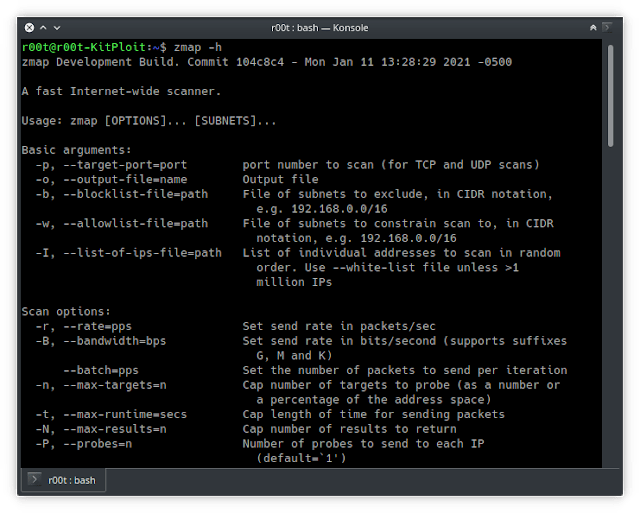 3.6KNetwork Tools
3.6KNetwork ToolsZmap – Single Packet Network Scanner Designed For Internet-wide Network Surveys
ZMap is a fast single packet network scanner designed for Internet-wide network surveys. On a typical desktop computer with a gigabit...
-
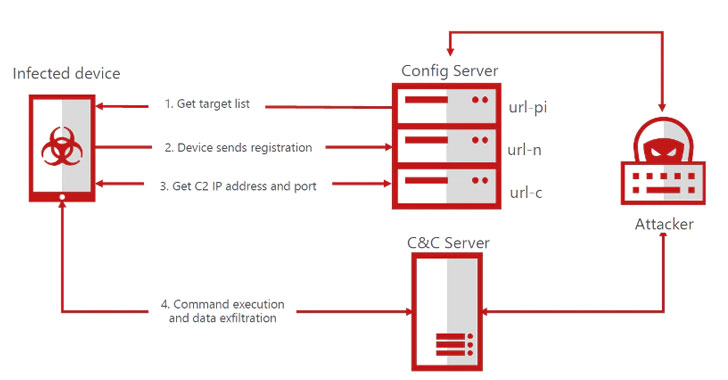
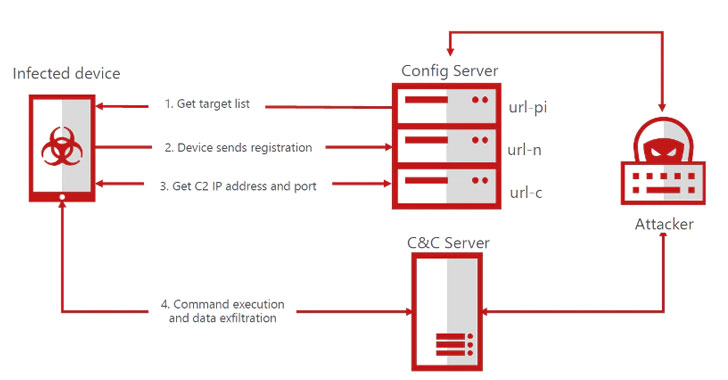 1.5KMalware
1.5KMalwareBRATA Malware Poses as Android Security Scanners on Google Play Store
A new set of malicious Android apps have been caught posing as app security scanners on the official Play Store to distribute...
-

 1.9KInformation Gathering
1.9KInformation GatheringRadareEye – Scan Nearby devices [BLE, Bluetooth And Wifi]
A tool made for specially scanning nearby devices[BLE,Bluetooth & Wifi] and execute our given command on our system when the target...
-
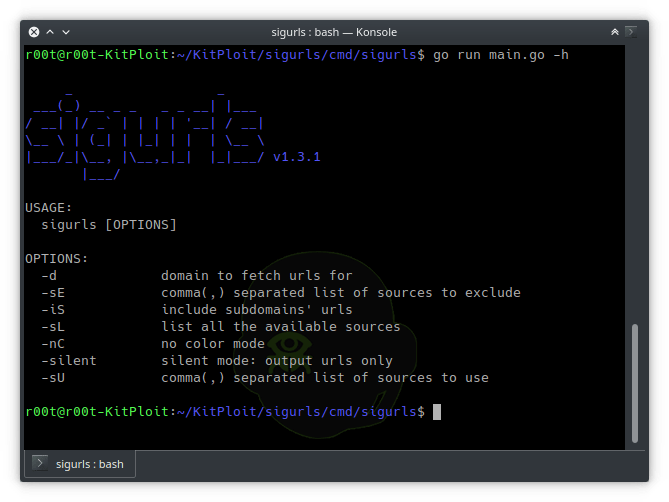
 5.0KInformation Gathering
5.0KInformation GatheringSigurls – Fetch URLs From AlienVault’s OTX, Common Crawl, URLScan
sigurls is a reconnaissance tool, it fetches URLs from AlienVault’s OTX, Common Crawl, URLScan, Github and the Wayback Machine. Usage To...
-
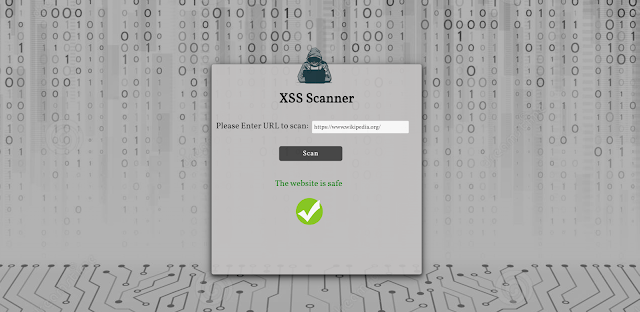
 3.9KWeb Application Security
3.9KWeb Application SecurityXSS-Scanner – XSS Scanner That Detects Cross-Site Scripting Vulns
Cross-Site Scripting (XSS) is one of the most well known web application vulnerabilities. It even has a dedicated chapter in the...






