Search results for "Scripts"
-

 2.0KMalware
2.0KMalwareHackers Deliver HotRat as Hidden Scripts in cracked software
The use of illegal software has been under circulation ever since there have been torrents and cracked software. Recent reports show that...
-
 4.6KMalware
4.6KMalwareBeware of the New ‘Blank Image’ Attack that Hides Malicious Scripts in Image Files
Avanan researchers have seen a new attack dubbed “Blank Image” spreading throughout the globe wherein hackers include blank images in HTML attachments....
-
 1.1KMalware
1.1KMalwareLyceum Hackers Stealing Credentials Windows By Deploy Keylogger Using PowerShell Scripts & .NET RAT
The Lyceum threat group (aka Hexane) again initiated an attack, but this time they have a weird variant of a remote-access trojan...
-
 2.9KHackers Repository
2.9KHackers RepositoryWindowsFirewallRuleset: Windows firewall ruleset powershell scripts
Windows Firewall Ruleset Windows firewall rules organized into individual powershell scripts according to: Rule group Traffic direction IP version (IPv4 / IPv6)...
-

 2.2KHack Tools
2.2KHack ToolsRE:TERNAL – Repo Containing Docker-Compose Files And Setup Scripts Without Having To Clone The Individual Reternal Components
RE:TERNAL is a centralised purple team simulation platform. Reternal uses agents installed on a simulation network to execute various known red-teaming techniques...
-

 1.4KHack Tools
1.4KHack ToolsDetectionLab – Vagrant And Packer Scripts To Build A Lab Environment Complete With Security Tooling And Logging Best Practices
DetectionLab is tested weekly on Saturdays via a scheduled CircleCI workflow to ensure that builds are passing. PurposeThis lab has been designed...
-

 5.3KHack Tools
5.3KHack ToolsVscan – Vulnerability Scanner Tool Using Nmap And Nse Scripts
vulnerability scanner tool is using nmap and nse scripts to find vulnerabilitiesThis tool puts an additional value into vulnerability scanning with nmap....
-
 426Exploitation Tools
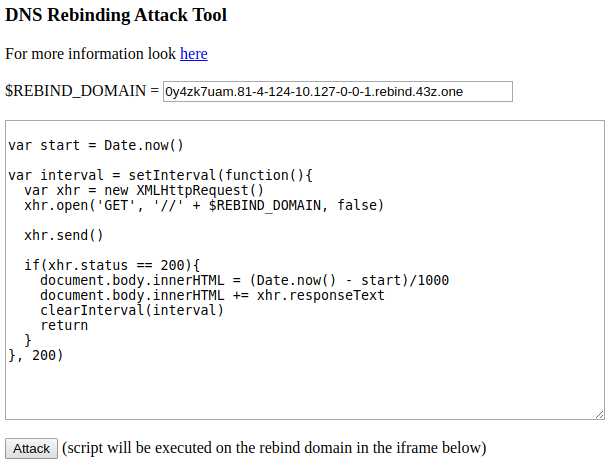
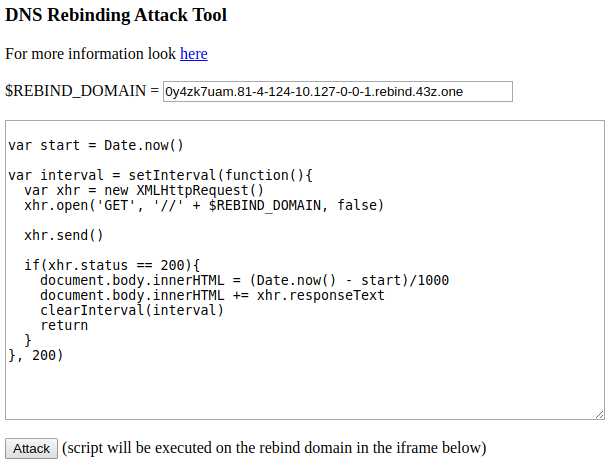
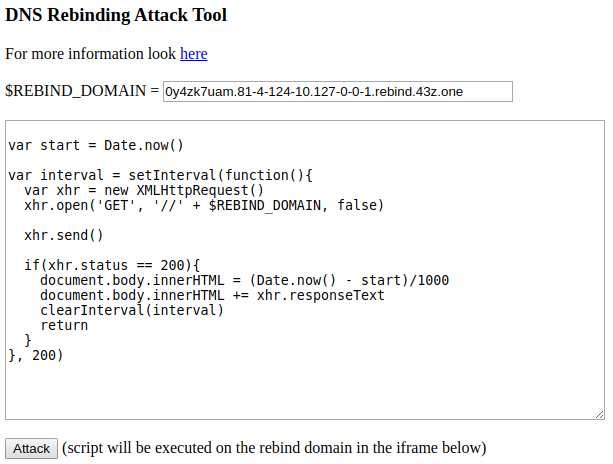
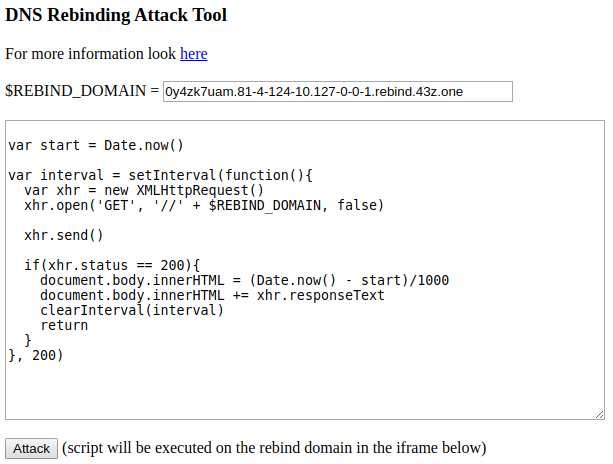
426Exploitation ToolsDNS Rebinding – DNS Rebind Tool With Custom Scripts
Inspired by @tavisio This project is meant to be an All-in-one Toolkit to test further DNS rebinding attacks and my take...
-
 371Exploitation
371ExploitationDNS Rebinding Tool – DNS Rebind Tool With Custom Scripts
This project is meant to be an All-in-one Toolkit to test further DNS rebinding attacks and my take on understanding these kind...
-

 320Hack Tools
320Hack ToolsRed Team Powershell Scripts
Various PowerShell scripts that may be useful during a red team exercise. The repo includes the following scripts: Red Team Powershell Scripts...
-

 261Malware
261MalwareHackers Abuse Windows Installer MSI to Execute Malicious JavaScript, VBScript, PowerShell Scripts to Drop Malware
Hackers use malicious MSI files that download and execute malicious files that could bypass traditional security solutions. The dropped malware is capable...
-
 226Hacking Tools
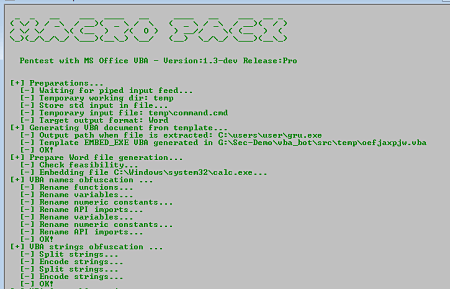
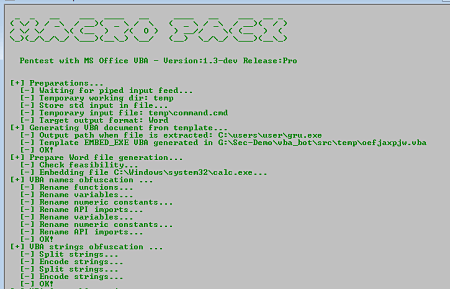
226Hacking ToolsMacro_Pack – Open Source tool for obfuscating MS documents and VBS scripts
The macro_pack is a tool for automating obfuscation in an MS document or VBS script format It’s perfect for security professionals who...
-

 332Data Security
332Data SecurityCryptomining scripts will be blocked in upcoming versions of Firefox browser
In all the future versions of the Firefox web browser, cryptojacking malware will be blocked. Mozilla, the company behind Firefox browser, announced...
-
 325Malware
325MalwareHackers Launch Olympic Destroyer Malware to Attack Financial Organizations using Obfuscated Scripts to Evade Detection
Olympic Destroyer Malware raised again through weaponized documents and currently targeting various Financial Organization with upgraded capabilities and evade the detection of...
-

 203Hackers Repository
203Hackers RepositoryBackdoorMan – Toolkit that helps you find malicious PHP scripts and shells
BackdoorMan BackdoorMan is a toolkit that helps you find malicious, hidden and suspicious PHP scripts and shells in a chosen destination. Description...
-

 219Firewall
219FirewallBlock All Domains That Serve Ads, Tracking Scripts and Malware: hBlock
Improve your security and privacy by blocking ads, tracking and malware domains. This POSIX-compliant shell script, designed for Unix-like systems, gets a list...
-
 198Information Gathering
198Information GatheringNmap 7.70 Released With Better OS Detection, 9 new NSE scripts and Much More
Nmap (“Network Mapper”) is a free and open source utility for network discovery and security auditing. Many systems and network administrators also find...
-
 319Cryptocurrency
319CryptocurrencyHackers Spreading Cryptocurrency Mining scripts via videos that Embedded in MS Office Word Documents
Microsoft word documents abused by Cryptocurrency Mining script embedded phishing Videos and victims tricked into watching an “innocent” video that leads to performing a...
-

 285Tricks & How To's
285Tricks & How To'sBuild Your Own IPsec VPN Server: Auto Setup Scripts
Set up your own IPsec VPN server in just a few minutes, with both IPsec/L2TP and Cisco IPsec on Ubuntu, Debian and...
-
 188Hack Tools
188Hack ToolsShellCheck – Static Analysis Tool for Shell Scripts
ShellCheck is a static analysis tool that gives warnings and suggestions for bash/sh shell scripts. How To Use ShellCheck There are a number...
-

 219Hack Tools
219Hack ToolsInvoke-PSImage – Tool to Embed Powershell Scripts in PNG Image Pixels
Invoke-PSImage takes a PowerShell script and embeds the bytes of the script into the pixels of a PNG image. It generates a...






