Search results for "Secrets"
-

 644Vulnerabilities
644VulnerabilitiesPython’s PyPI Reveals Its Secrets
GitGuardian is famous for its annual State of Secrets Sprawl report. In their 2023 report, they found over 10 million exposed passwords,...
-

 2.6KData Breach
2.6KData BreachMicrosoft Confirms Russian Hackers Stole Source Code, Some Customer Secrets
Microsoft on Friday revealed that the Kremlin-backed threat actor known as Midnight Blizzard (aka APT29 or Cozy Bear) managed to gain access...
-
 3.2KData Breach
3.2KData BreachEx-Google Engineer Arrested for Stealing AI Technology Secrets for China
The U.S. Department of Justice (DoJ) announced the indictment of a 38-year-old Chinese national and a California resident for allegedly stealing proprietary...
-
 4.9KVulnerabilities
4.9KVulnerabilitiesThree Tips to Protect Your Secrets from AI Accidents
Last year, the Open Worldwide Application Security Project (OWASP) published multiple versions of the “OWASP Top 10 For Large Language Models,” reaching...
-

 1.6KMalware
1.6KMalwareNS-STEALER Uses Discord Bots to Exfiltrate Your Secrets from Popular Browsers
Cybersecurity researchers have discovered a new Java-based “sophisticated” information stealer that uses a Discord bot to exfiltrate sensitive data from compromised hosts....
-

 2.4KVulnerabilities
2.4KVulnerabilitiesExposed Secrets are Everywhere. Here’s How to Tackle Them
Picture this: you stumble upon a concealed secret within your company’s source code. Instantly, a wave of panic hits as you grasp...
-

 816Data Breach
816Data BreachTell Me Your Secrets Without Telling Me Your Secrets
The title of this article probably sounds like the caption to a meme. Instead, this is an actual problem GitGuardian’s engineers had...
-

 3.4KIncidents
3.4KIncidentsMore than 770 million records available through the Travis CI API: Anyone can extract tokens, secrets, and other credentials associated with services like GitHub, AWS, and Docker Hub
Software development and testing platform Travis CI confirmed the second incident of exposing its users’ data in less than a year. On...
-
 2.7KData Breach
2.7KData BreachHow Secrets Lurking in Source Code Lead to Major Breaches
If one word could sum up the 2021 infosecurity year (well, actually three), it would be these: “supply chain attack”. A software...
-
 4.7KMalware
4.7KMalwareExperts Expose Secrets of Conti Ransomware Group That Made 25 Million from Victims
The clearnet and dark web payment portals operated by the Conti ransomware group have gone down in what appears to be an...
-
 2.3KVulnerabilities
2.3KVulnerabilitiesMicrosoft Edge Bug Could’ve Let Hackers Steal Your Secrets for Any Site
Microsoft last week rolled out updates for the Edge browser with fixes for two security issues, one of which concerns a security...
-

 4.5KIncidents
4.5KIncidentsWill Apple pay the $50 million USD ransom to the world’s richest hacker for not publishing its secrets this May 1st?
REvil ransomware operators disclosed that they have information related to some of Apple’s upcoming releases, and even threaten to disclose it if...
-
 4.2KMobile Security
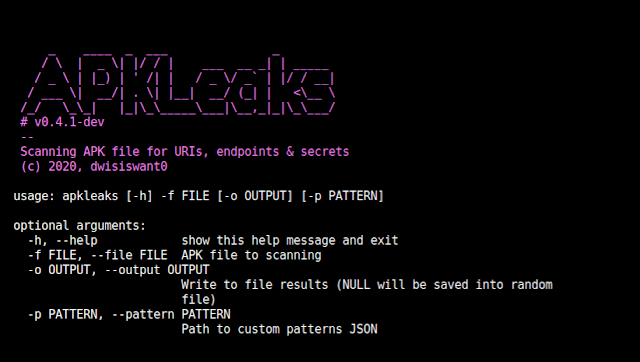
4.2KMobile SecurityApkLeaks – Scanning APK File For URIs, Endpoints And Secrets
Scanning APK file for URIs, endpoints & secrets. Installation To install apkLeaks, simply: $ git clone https://github.com/dwisiswant0/apkleaks $ cd apkleaks/ $...
-
 2.8KMalware
2.8KMalwareXDSpy: Stealing government secrets since 2011
ESET researchers uncover a new APT group that has been stealing sensitive documents from several governments in Eastern Europe and the Balkans...
-

 2.1KIncidents
2.1KIncidentsBMW was hacked; potential trading secrets leaking
Currently any company can become a victim of a cyberattack. According to cybersecurity specialists, automobile company BMW detected and monitored a hacker...
-
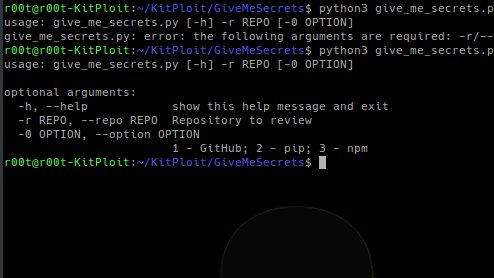
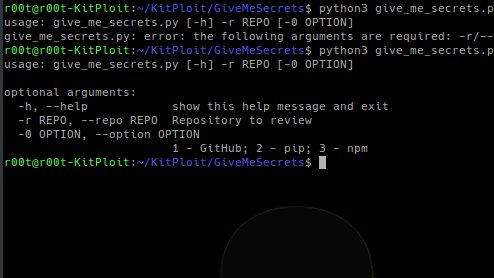 410Information Gathering
410Information GatheringGiveMeSecrets – Get Sensitive Information From A Given Repository
Use regular expressions to get sensitive information from a given repository (GitHub, pip or npm). Dependencies You only need to have...
-

 272News
272News2 Students ‘Almost Hacked’ Donald Trump’s Tax Secrets
Various attempts are made on a regular basis to break the tight security that’s used to protect political leaders and steal their...
-
 405News
405NewsEdward Snowden To Reveal ‘Why He Leaked’ NSA Secrets
Edward Snowden, the former CIA agent and NSA contractor who leaked troves of secret documents in 2013, has written a memoir that...
-

 330News
330NewsWatching Porn In Incognito? Google, Facebook Still Know Your Secrets: Study
When it comes to whether or not a user is being tracked on the web, the answer is yes, and this even...
-

 490Lists
490ListsGoogle Photos Unlimited Storage On Pixel: 8 Secrets You Didn’t Know
One of the perks of having a Pixel device is that you can upload unlimited photos and videos to Google’s cloud via...
-
 408Tutorials
408TutorialsBest forensic tools to hide secrets passwords and recover files
Steganography is common term which is used in hiding or encrypting any personal information. The information can be anything which you don’t...






