Search results for "Stealth"
-

 768Malware
768MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
A new information stealer has been found leveraging Lua bytecode for added stealth and sophistication, findings from McAfee Labs reveal. The cybersecurity...
-
 4.2KMalware
4.2KMalwareChina-linked Hackers Deploy New ‘UNAPIMON’ Malware for Stealthy Operations
A threat activity cluster tracked as Earth Freybug has been observed using a new malware called UNAPIMON to fly under the radar....
-

 1.4KData Security
1.4KData SecuritySource Code Gone Missing: Microsoft Baffled by Stealthy Hack
In a significant cybersecurity incident, Russian state-backed hackers gained access to some of Microsoft’s core software systems. This breach, first disclosed in...
-

 1.6KMalware
1.6KMalwareAlert: New Stealthy “RustDoor” Backdoor Targeting Apple macOS Devices
Apple macOS users are the target of a new Rust-based backdoor that has been operating under the radar since November 2023. The...
-
 3.6KMalware
3.6KMalwareStealthy Zardoor Backdoor Targets Saudi Islamic Charity Organization
An unnamed Islamic non-profit organization in Saudi Arabia has been targeted as part of a stealthy cyber espionage campaign designed to drop...
-

 2.8KMalware
2.8KMalwareSyrian Hackers Distributing Stealthy C#-Based Silver RAT to Cybercriminals
Threat actors operating under the name Anonymous Arabic have released a remote access trojan (RAT) called Silver RAT that’s equipped to bypass...
-
 1.6KMalware
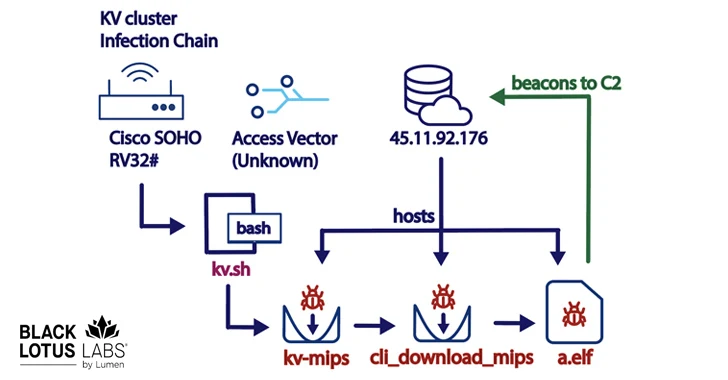
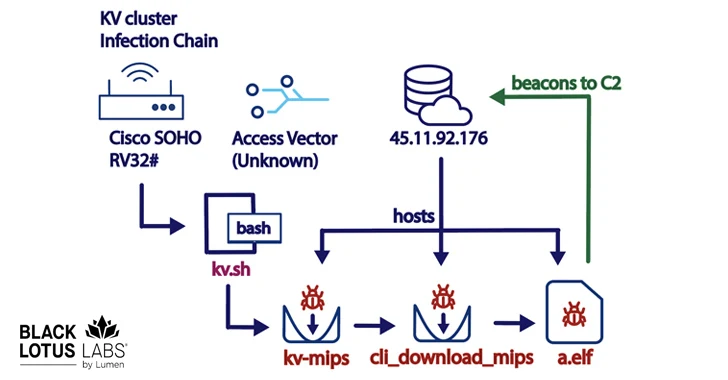
1.6KMalwareNew KV-Botnet Targeting Cisco, DrayTek, and Fortinet Devices for Stealthy Attacks
A new botnet consisting of firewalls and routers from Cisco, DrayTek, Fortinet, and NETGEAR is being used as a covert data transfer...
-
 3.2KVulnerabilities
3.2KVulnerabilitiesNew Stealthy ‘Krasue’ Linux Trojan Targeting Telecom Firms in Thailand
A previously unknown Linux remote access trojan called Krasue has been observed targeting telecom companies in Thailand by threat actors to main...
-

 586Malware
586MalwareLogoFAIL: UEFI Vulnerabilities Expose Devices to Stealth Malware Attacks
The Unified Extensible Firmware Interface (UEFI) code from various independent firmware/BIOS vendors (IBVs) has been found vulnerable to potential attacks through high-impact...
-
 1.4KMalware
1.4KMalwareHow hrserver.dll stealthy webshell can mimic Google’s Web Traffic to hide and compromise networks
In a striking revelation shaking the cybersecurity world, researchers have unearthed a sophisticated web shell, dubbed ‘HrServ,’ hidden within a seemingly innocuous...
-

 5.0KCyber Attack
5.0KCyber AttackStealthy Kamran Spyware Targeting Urdu-speaking Users in Gilgit-Baltistan
Urdu-speaking readers of a regional news website that caters to the Gilgit-Baltistan region have likely emerged as a target of a watering...
-
 4.5KMalware
4.5KMalwareYoroTrooper: Researchers Warn of Kazakhstan’s Stealthy Cyber Espionage Group
A relatively new threat actor known as YoroTrooper is likely made up of operators originating from Kazakhstan. The assessment, which comes from...
-

 340Malware
340MalwareSilent Predator Unveiled: Decoding WebWyrm Stealthy Malware affecting 50 countries
Deciphering Webwyrm: An In-Depth Analysis of the Pervasive Malware Threatening Global Cybersecurity In the intricate landscape of global cybersecurity, Webwyrm malware has...
-
 4.6KMalware
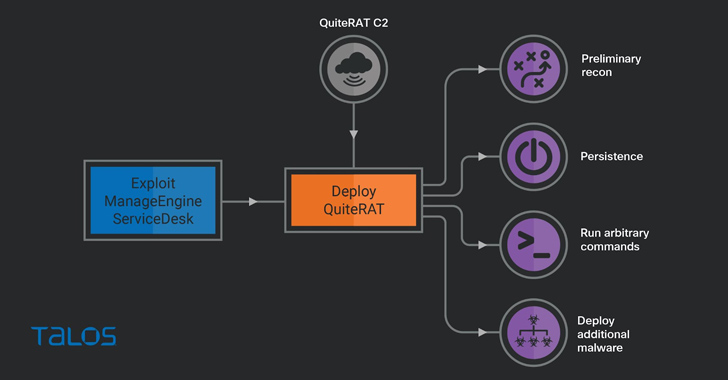
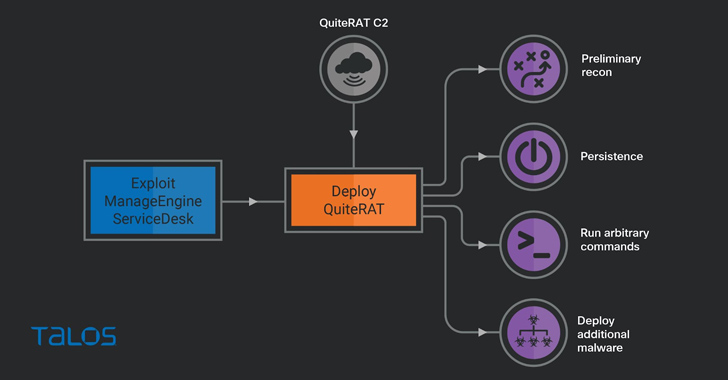
4.6KMalwareLazarus Group Exploits Critical Zoho ManageEngine Flaw to Deploy Stealthy QuiteRAT Malware
The North Korea-linked threat actor known as Lazarus Group has been observed exploiting a now-patched critical security flaw impacting Zoho ManageEngine ServiceDesk...
-
 3.3KMalware
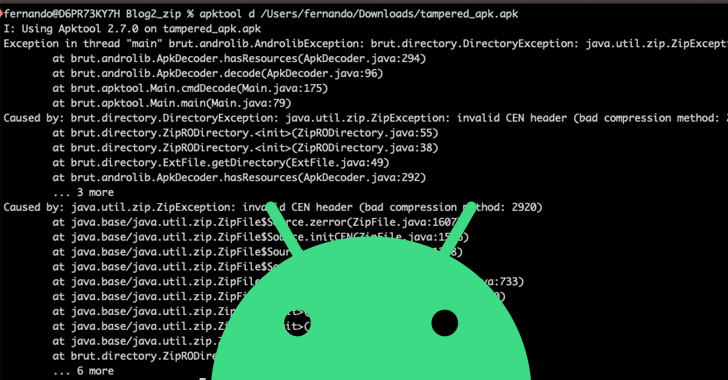
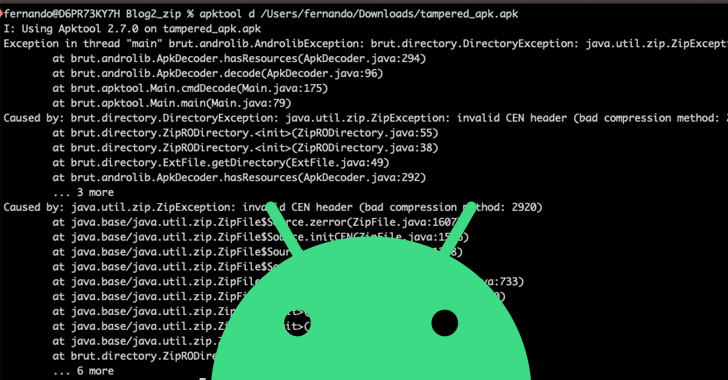
3.3KMalwareThousands of Android Malware Apps Using Stealthy APK Compression to Evade Detection
Threat actors are using Android Package (APK) files with unknown or unsupported compression methods to elude malware analysis. That’s according to findings...
-
 886Vulnerabilities
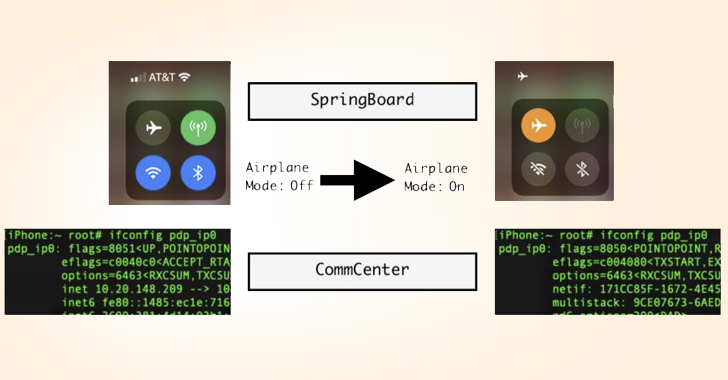
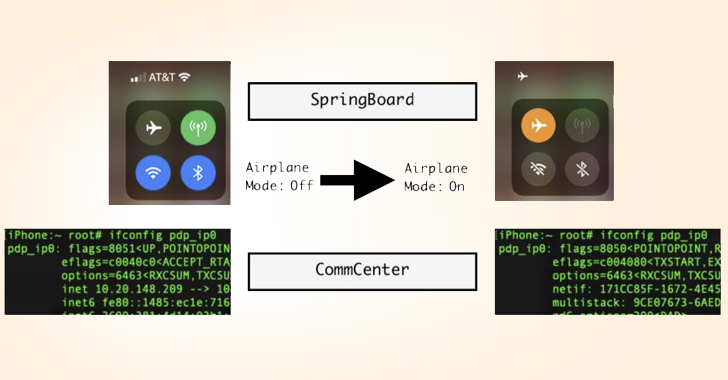
886VulnerabilitiesNew Apple iOS 16 Exploit Enables Stealthy Cellular Access Under Fake Airplane Mode
Cybersecurity researchers have documented a novel post-exploit persistence technique on iOS 16 that could be abused to fly under the radar and...
-

 3.3KMalware
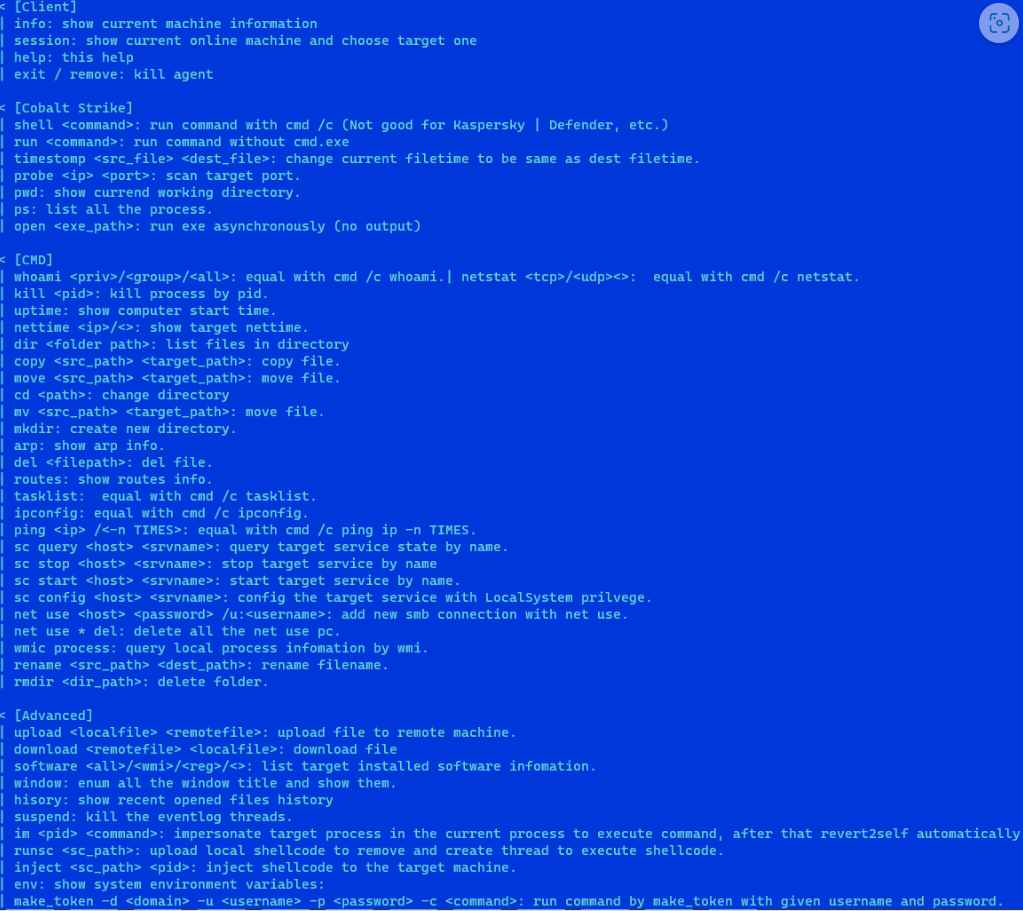
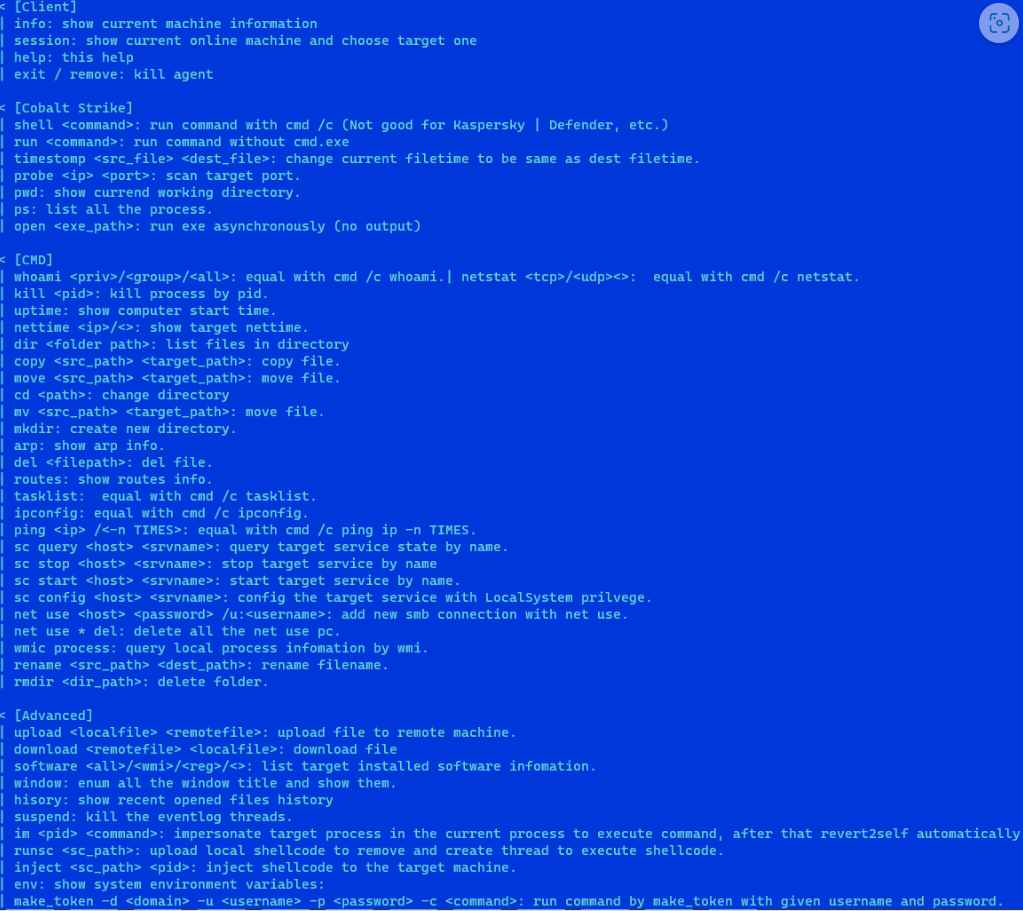
3.3KMalwareFIN8 Revamped Hacking Toolkit with New Stealthy Attack Features
Syssphinx (aka FIN8) is a financially motivated cyber-crime group deploying revamped sardonic backdoor to deliver Noberus ransomware. This group has been active since...
-

 2.1KMalware
2.1KMalwareScarCruft Hackers Exploit Ably Service for Stealthy Wiretapping Attacks
The North Korean threat actor known as ScarCruft has been observed using an information-stealing malware with previously undocumented wiretapping features as well...
-

 3.8KMalware
3.8KMalwareNew Zero-Click Hack Targets iOS Users with Stealthy Root-Privilege Malware
A previously unknown advanced persistent threat (APT) is targeting iOS devices as part of a sophisticated and long-running mobile campaign dubbed Operation...
-

 1.9KMalware
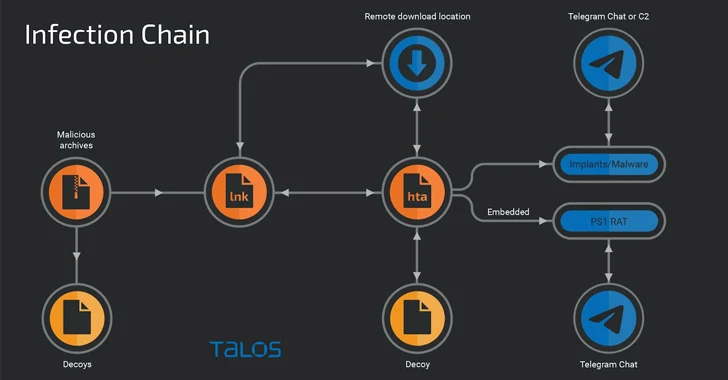
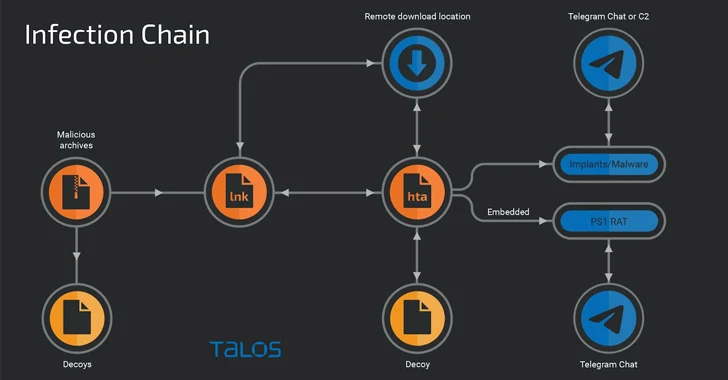
1.9KMalwareHackers Use Weaponized DOCX File to Deploy Stealthy Malware
CERT-UA has identified and addressed a cyber attack on the government information systems of Ukrainian governmental state bodies. Through investigation, it was...
-

 4.3KMalware
4.3KMalwareNew Stealthy Variant of Linux Backdoor BPFDoor Emerges from the Shadows
A previously undocumented and mostly undetected variant of a Linux backdoor called BPFDoor has been spotted in the wild, cybersecurity firm Deep...






