Search results for "Takeover"
-

 1.9KVulnerabilities
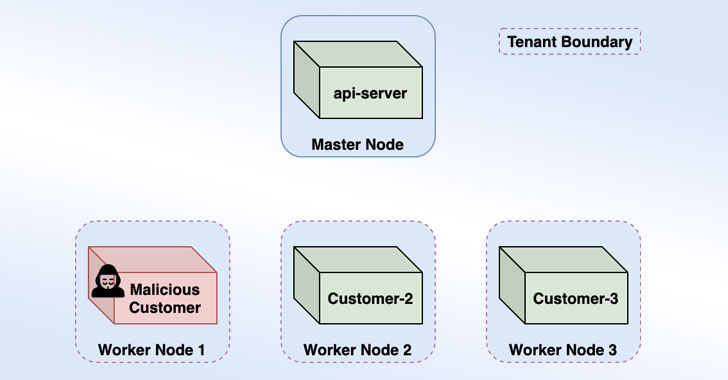
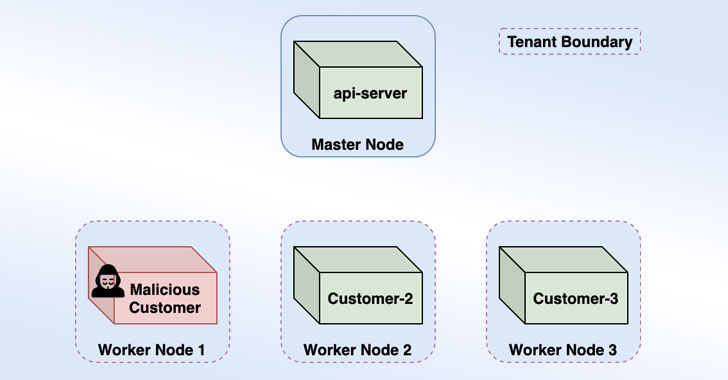
1.9KVulnerabilitiesResearchers Detail Kubernetes Vulnerability That Enables Windows Node Takeover
Details have been made public about a now-patched high-severity flaw in Kubernetes that could allow a malicious attacker to achieve remote code...
-
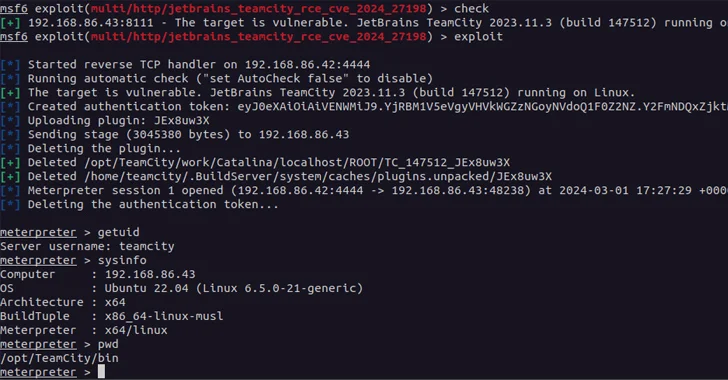
 4.8KVulnerabilities
4.8KVulnerabilitiesCritical JetBrains TeamCity On-Premises Flaws Could Lead to Server Takeovers
A new pair of security vulnerabilities have been disclosed in JetBrains TeamCity On-Premises software that could be exploited by a threat actor...
-
 4.5KMalware
4.5KMalwareResearchers Find 34 Windows Drivers Vulnerable to Full Device Takeover
As many as 34 unique vulnerable Windows Driver Model (WDM) and Windows Driver Frameworks (WDF) drivers could be exploited by non-privileged threat...
-
 1.9KVulnerabilities
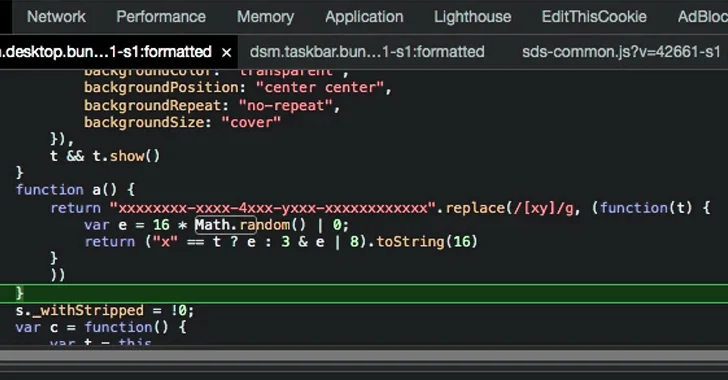
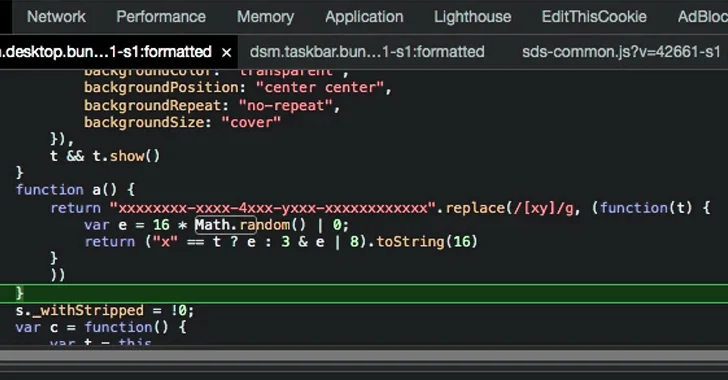
1.9KVulnerabilitiesNew Admin Takeover Vulnerability Exposed in Synology’s DiskStation Manager
A medium-severity flaw has been discovered in Synology’s DiskStation Manager (DSM) that could be exploited to decipher an administrator’s password and remotely...
-

 790Malware
790MalwareBeware! Hacker-Sold macOS HVNC Tool Allows Complete Takeover
Threat actors targeting macOS have increased lately as there were several cases of macOS information stealer malware found in the past, and...
-

 1.4KVulnerabilities
1.4KVulnerabilitiesMastodon Social Network Patches Critical Flaws Allowing Server Takeover
Mastodon, a popular decentralized social network, has released a security update to fix critical vulnerabilities that could expose millions of users to...
-

 4.8KVulnerabilities
4.8KVulnerabilitiesWooCommerce’s serious vulnerability allows unauthorized wordpress website takeover
A serious flaw has been found in WooCommerce, a popular plug-in for managing online businesses that are built on the WordPress platform....
-
 810Malware
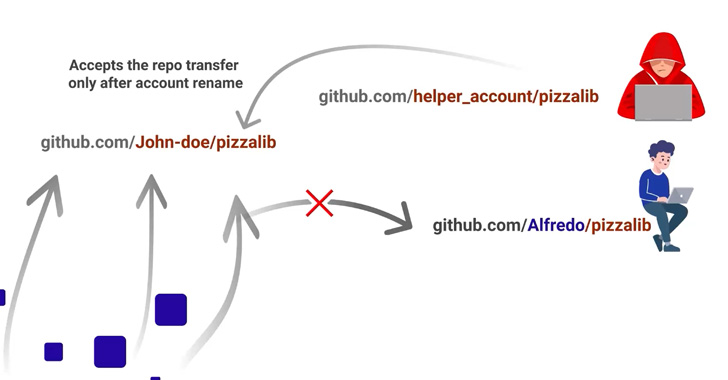
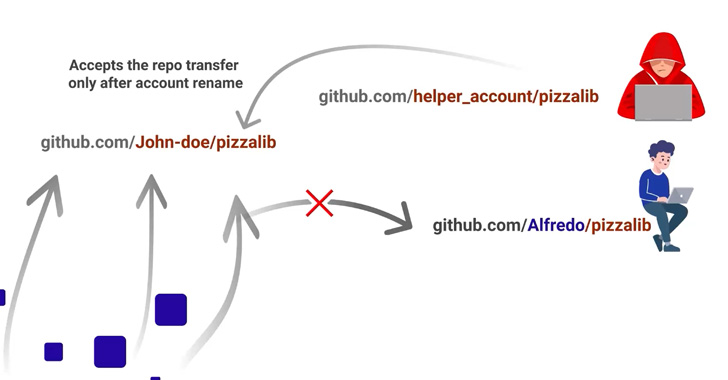
810MalwareGitHub Repojacking Bug Could’ve Allowed Attackers to Takeover Other Users’ Repositories
Cloud-based repository hosting service GitHub has addressed a high-severity security flaw that could have been exploited to create malicious repositories and mount...
-

 1.1KVulnerabilities
1.1KVulnerabilities3 critical vulnerabilities in 9 Cisco Router models allows complete takeover of any network
3 vulnerabilities in Cisco Small Business RV160, RV260, RV340, and RV345 Series Routers could allow an unauthenticated threat actor to remotely execute...
-

 1.5KVulnerabilities
1.5KVulnerabilitiesGitLab Issues Security Patch for Critical Account Takeover Vulnerability
GitLab has moved to address a critical security flaw in its service that, if successfully exploited, could result in an account takeover....
-

 4.9KVulnerabilities
4.9KVulnerabilities9 critical vulnerabilities in Mozilla Thunderbird allow easy takeover of your machine via email
Cybersecurity specialists reported the detection of multiple flaws in the Mozilla Thunderbird multiplatform email client, which successful exploitation would allow malicious hackers...
-

 4.7KMalware
4.7KMalwareResearchers Takeover Unpatched 3rd-Party Antivirus Sandboxes via VirusTotal
Security researchers have disclosed a security issue that could have allowed attackers to weaponize the VirusTotal platform as a conduit to achieve...
-

 4.8KVulnerabilities
4.8KVulnerabilities30 vulnerabilities in different Juniper products could allow the total takeover of the affected network. Update immediately
Cybersecurity specialists from Juniper Networks announced the release of multiple security patches to address more than 30 flaws in their products, including...
-
 4.0KVulnerabilities
4.0KVulnerabilitiesActive Directory Domain Service Bug Let Attackers To Takeover Windows Domains
During the November 2021 Patch Tuesday Two Active Directory domain service privilege escalation security flaws have been detected recently by Andrew Bartlett...
-

 1.7KData Security
1.7KData SecuritySMA 100 flaws in SonicWall VPN expose devices to remote takeover
If exploited, an unauthenticated, remote attacker can execute code as a “nobody user” in the device meaning attacker would get root access...
-
 5.1KVulnerabilities
5.1KVulnerabilitiesMicrosoft Warns of Cross-Account Takeover Bug in Azure Container Instances
Microsoft on Wednesday said it remediated a vulnerability in its Azure Container Instances (ACI) services that could have been weaponized by a...
-

 4.8KVulnerabilities
4.8KVulnerabilitiesCritical vulnerabilities in NGINX allows complete takeover of affected systems. Exploit publicly available; patch now
Nginx security teams published a report related to a critical vulnerability in their DNS resolution implementation. Tracked as CVE-2021-23017, successful exploitation of...
-

 5.0KMobile Security
5.0KMobile SecurityiPhone hack allowed device takeover via Wi‑Fi
Using a zero-click exploit, an attacker could have taken complete control of any iPhone within Wi-Fi range in seconds
-
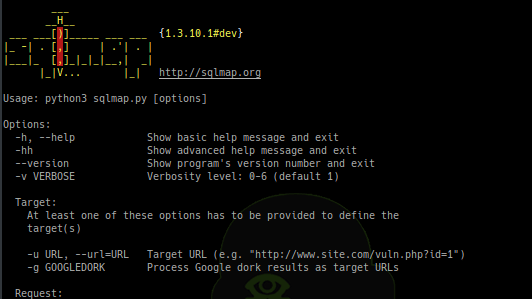
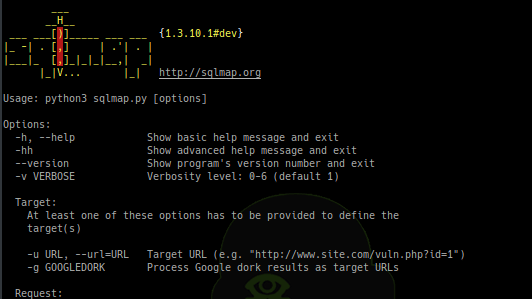 489Exploitation Tools
489Exploitation ToolsSQLMap v1.3.10 – Automatic SQL Injection And Database Takeover Tool
SQLMap is an open source penetration testing tool that automates the process of detecting and exploiting SQL injection flaws and taking...
-
455News
New Instagram Login Vulnerability Allow Hackers To Takeover Your Account In Minutes
The researcher has found a way to hack Instagram accounts in minutes. As it turns out, a new Instagram login vulnerability that...
-
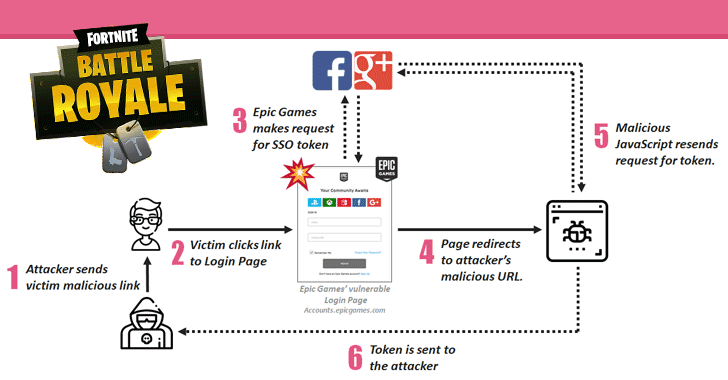
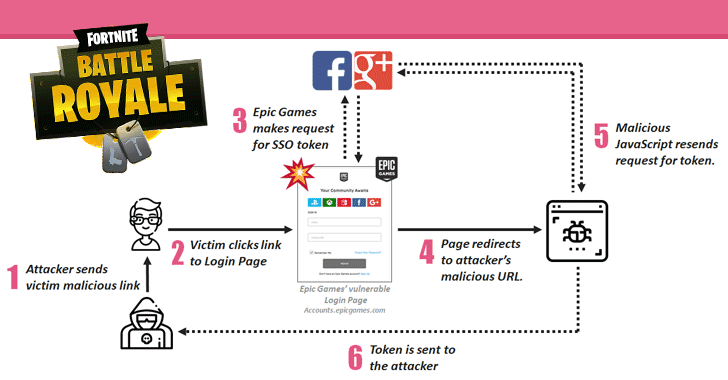 218Articles
218ArticlesFortnite Flaws Allowed Hackers to Takeover Gamers’ Accounts
Check Point researchers have discovered multiple security vulnerabilities in Fortnite, a massively popular online battle game, one of which could have allowed...







