Search results for "Toolkit"
-
 526Malware
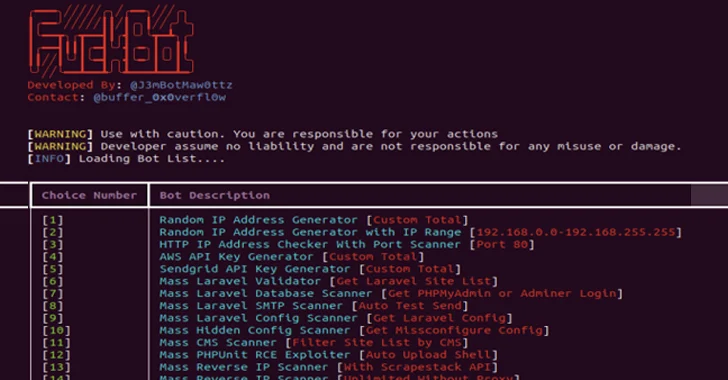
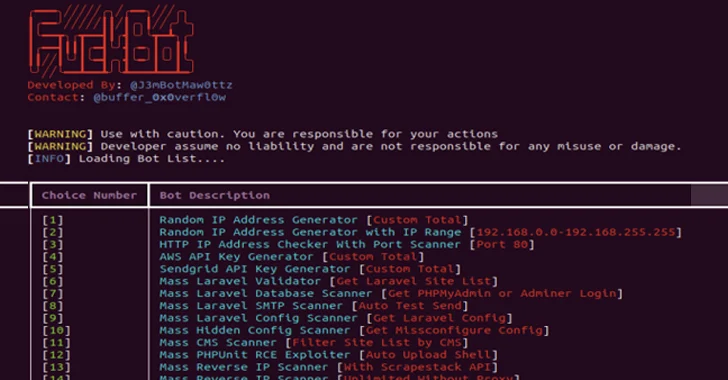
526MalwareNew Python-based FBot Hacking Toolkit Aims at Cloud and SaaS Platforms
A new Python-based hacking tool called FBot has been uncovered targeting web servers, cloud services, content management systems (CMS), and SaaS platforms...
-

 1.8KIncidents
1.8KIncidentsHow $400 toolkit EvilProxy was used to send 120k phishing emails to hundreds of companies
Researchers have discovered that malicious actors have been utilizing the phishing toolkit EvilProxy to gain control of cloud-based Microsoft 365 accounts belonging...
-

 3.3KMalware
3.3KMalwareFIN8 Revamped Hacking Toolkit with New Stealthy Attack Features
Syssphinx (aka FIN8) is a financially motivated cyber-crime group deploying revamped sardonic backdoor to deliver Noberus ransomware. This group has been active since...
-

 765Malware
765MalwareHackers Targeting Italian Corporate Banking Clients with New Web-Inject Toolkit DrIBAN
Italian corporate banking clients are the target of an ongoing financial fraud campaign that has been leveraging a new web-inject toolkit called...
-

 4.7KPhishing
4.7KPhishingTelegram – New Market Place for Selling Phishing Toolkits & Services
Telegram is becoming an increasingly popular platform for users as well as cyber-criminals. It has become a Mini Dark-web since 2021 when...
-

 3.8KMalware
3.8KMalwareOpen Source Ransomware Toolkit Cryptonite Turns Into Accidental Wiper Malware
A version of an open source ransomware toolkit called Cryptonite has been observed in the wild with wiper capabilities due to its...
-
 4.9KMalware
4.9KMalwareOldGremlin Hacker Group Expanded Toolkit With Dedicated Linux Ransomware
It appears that 16 malicious campaigns have been carried out by a Russian-speaking ransomware group called OldGremlin (aka TinyScouts). A combination of...
-

 3.8KMalware
3.8KMalwareDoNot Team Hackers Updated its Malware Toolkit with Improved Capabilities
The Donot Team threat actor has updated its Jaca Windows malware toolkit with improved capabilities, including a revamped stealer module designed to...
-

 2.0KTutorials
2.0KTutorialsHow to Use Advanced Network Intelligence Toolkit for Pentesting: badKarma
Searching vulnerabilities on the host (the host can be a website, web server, network device (router and others), end-user computer) begins with...
-

 2.8KTutorials
2.8KTutorialsTutorial for pentesting Android apps using the free ZANTI toolkit
In this tutorial, the specialists of the Cyber Security 360 course of the International Institute of Cyber Security (IICS) will show us...
-
 1.5KSystem Administration
1.5KSystem AdministrationCDK – Zero Dependency Container Penetration Toolkit
CDK is an open-sourced container penetration toolkit, designed for offering stable exploitation in different slimmed containers without any OS dependency. It...
-
 4.8KMalware
4.8KMalwareRamsay: A cyber‑espionage toolkit tailored for air‑gapped networks
ESET researchers uncover several instances of malware that uses various attack vectors to target systems isolated by an air gap
-
 5.5KPhishing
5.5KPhishing16Shop – Malware-as-a-service Phishing Toolkit Attack PayPal Users With Anti-Detection Techniques
A prolific phishing kit distribution network dubbed “16Shop” believed to be active since 2018 and developed by a hacking group called the...
-
 1.2KHack Tools
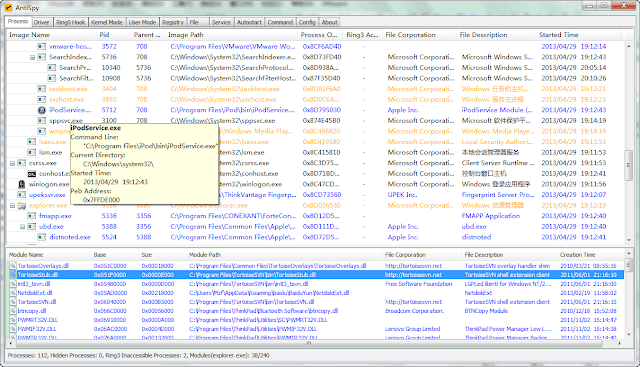
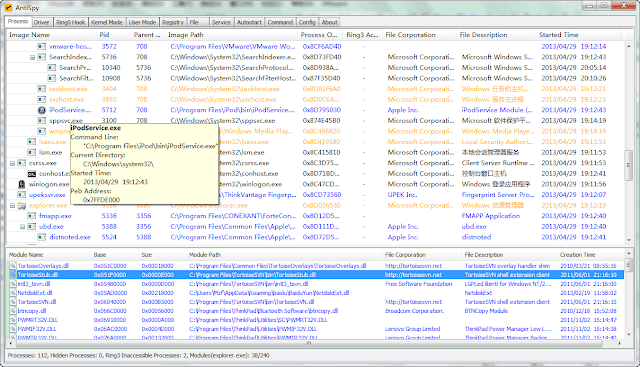
1.2KHack ToolsAntispy – A Free But Powerful Anti Virus And Rootkits Toolkit
AntiSpy is a free but powerful anti virus and rootkits toolkit.It offers you the ability with the highest privileges that can detect,analyze...
-
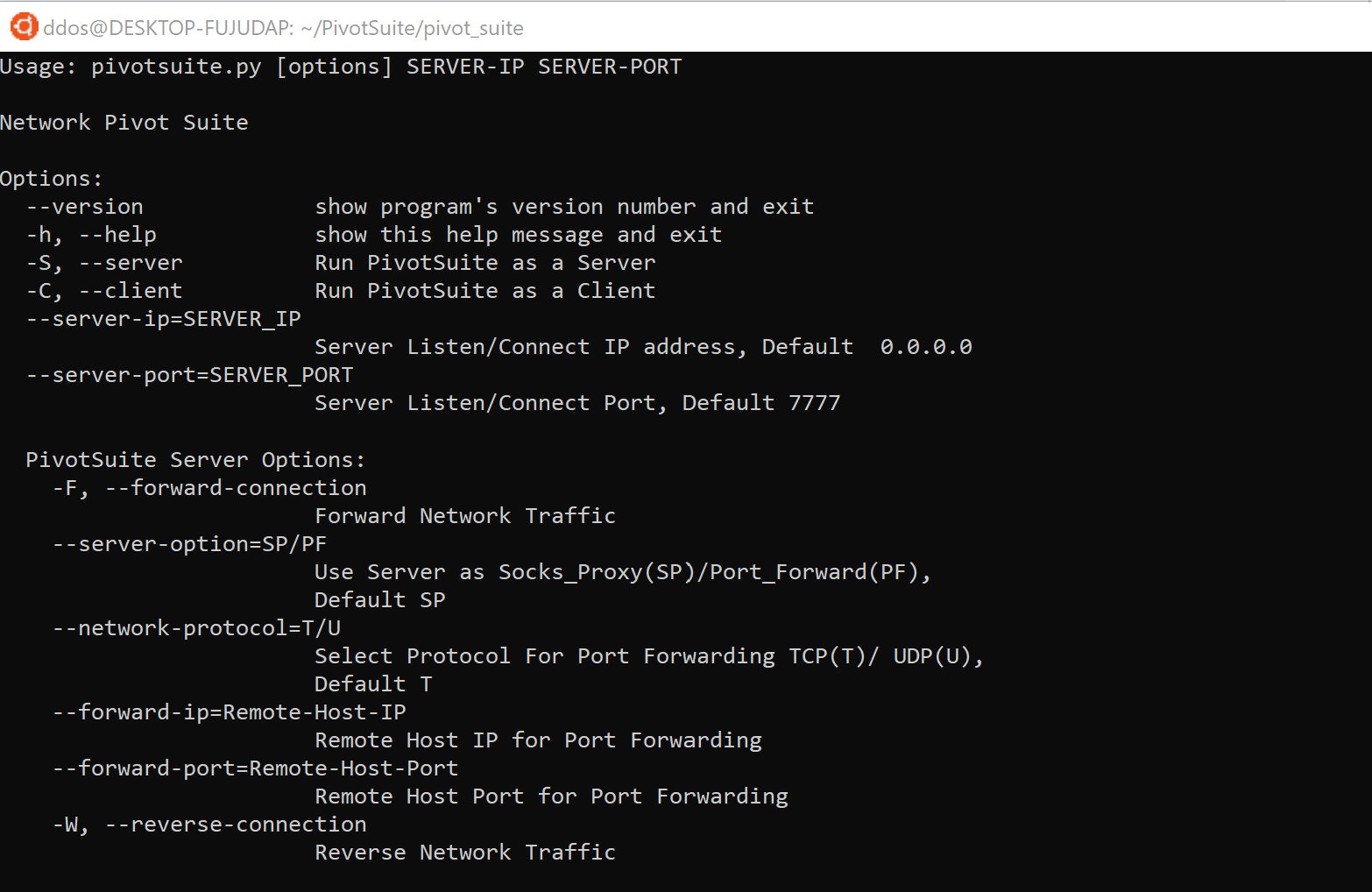
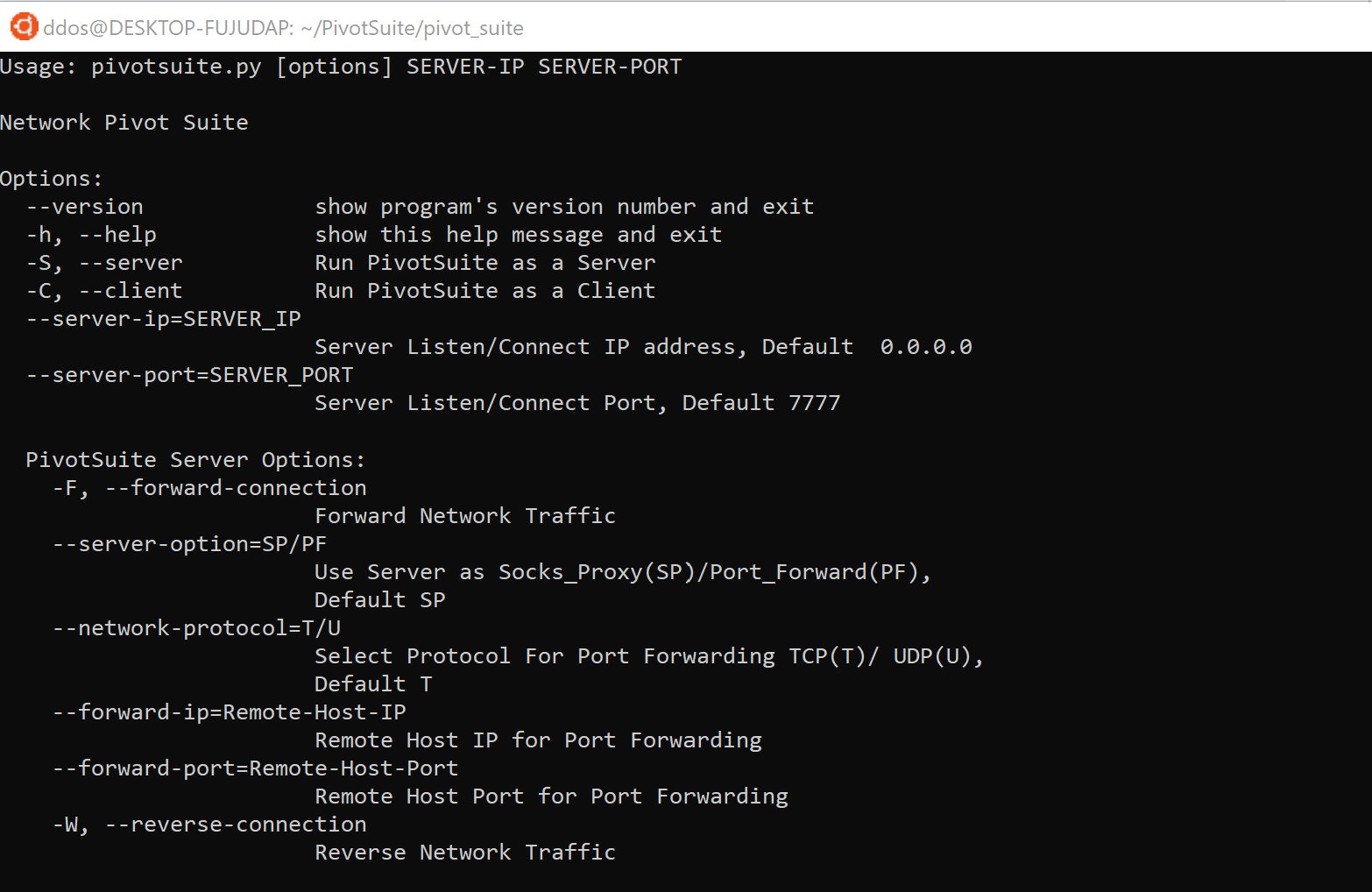 4.2KHack Tools
4.2KHack ToolsPivotSuite: A Network Pivoting Toolkit
PivotSuite PivotSuite: Hack The Hidden Network – A Network Pivoting Toolkit It is a portable, platform-independent and powerful network pivoting toolkit, Which...
-

 430News
430NewsMicro Fixes Vulnerability in an Anti-Threat Toolkit
Trend Micro recently patched its Anti-Threat Toolkit (ATTK) for a high-grade remote software execution vulnerability. The Trend Micro ATTK tool lets users...
-
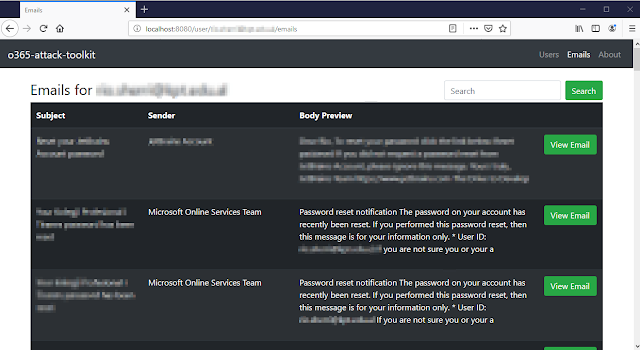
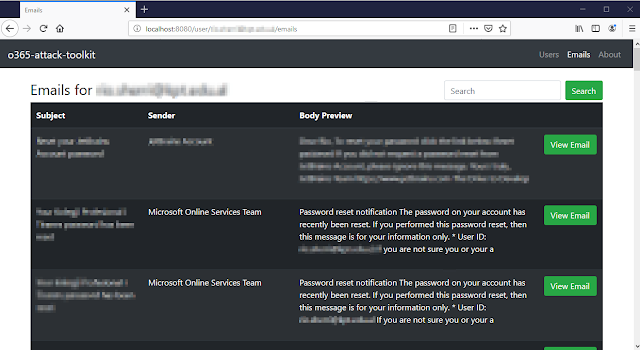 334Exploitation
334ExploitationO365 Attack Toolkit – A Toolkit to Attack Office365
o365-attack-toolkit allows operators to perform an OAuth phishing attack and later on use the Microsoft Graph API to extract interesting information. Some...
-
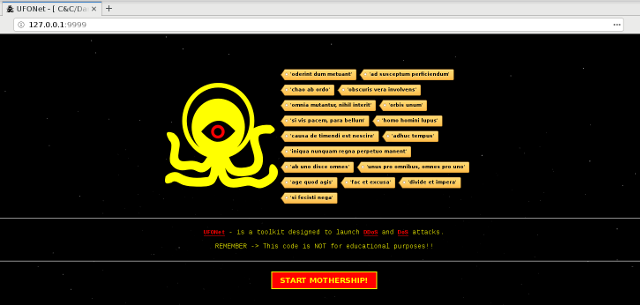
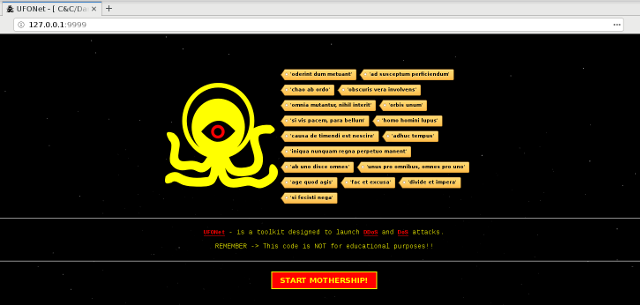 321Denial of service
321Denial of serviceUFONet – Toolkit Designed to launch DDoS and DoS attacks.
UFONet is a tool designed to launch Layer 7 (HTTP/Web Abuse) DDoS attacks, using ‘Open Redirect’ vectors, generally located on third part-y...
-

 341Car Hacking
341Car Hackingpyvit: Python Vehicle Interface Toolkit
Pyvit is a toolkit for interfacing with cars from Python. It aims to implement common hardware interfaces and protocols used in the...
-
 267Enumeration
267EnumerationMegaping – Network Mapping Toolkit
MegaPing is the ultimate must-have toolkit that provides essential utilities for Information System specialists, system administrators, IT solution providers or individuals. The...
-
 307Malware Analysis
307Malware AnalysisBT3 – Blue Team Training Toolkit
Blue Team Training Toolkit (BT3) is software for defensive security training, which will bring your network analysis training sessions, incident response drills...






