Search results for "Virtual Machine"
-

 2.4KMalware
2.4KMalwareExperts Detail Virtual Machine Used by Wslink Malware Loader for Obfuscation
Cybersecurity researchers have shed more light on a malicious loader that runs as a server and executes received modules in memory, laying...
-

 2.1KNews
2.1KNewsBetter Cloud Services: Tech giant Google Unveils Compute Optimized Virtual Machines (VMs) Powered by AMD EPYC Processors
An Instance refers to a server that is running our applications. Assume a single server is a single instance. Our cloud workloads...
-
 3.0KVulnerabilities
3.0KVulnerabilitiesAMD confirms two dangerous attacks that can compromise any virtual machine
Tech firm AMD issued a security guide to address two potential attacks against the Secure Encrypted Virtualization (SEV) solution, which keeps virtual...
-
 377Operating Systems
377Operating SystemsRedhunt OS – Virtual Machine for Adversary Emulation and Threat Hunting
RedHunt aims to be a one stop shop for all your threat emulation and threat hunting needs by integrating attacker’s arsenal as...
-
 228Geek
228GeekLinux Is Powering Almost Half Of All Microsoft Azure Virtual Machines
Around 40% of Microsoft’s Azure VMs now run Linux distributions, according to a tweet made by Microsoft Developer UK twitter account, ZDNet reports....
-

 317Malware
317MalwareA Banking Trojan Called “Ursnif” Using Mouse Moments for Evasion and Decryption From Virtual Machine
Bank Trojan called “Ursnif” using clever Trick to Evade sandbox Detection from the Virtual Machine Environment by using mouse movements. New Futures has...
-
 84Malware
84MalwareBanking Trojan Uses Mouse Movements to Distinguish Users From Virtual Machines
In July 2017, security researchers have spotted a new version of the proficient Ursnif banking trojan that comes with a clever trick...
-

 212Vulnerabilities
212VulnerabilitiesVirtual machine escape fetches $105,000 at Pwn2Own hacking contest [updated]
Hack worked by stitching together three separate exploits. Contestants at this year’s Pwn2Own hacking competition in Vancouver just pulled off an unusually...
-
 194Hacked
194HackedBeware! This Ruthless Malware Returned From The Dead Is Now A Virtual Machine Killer
Short Bytes: The security researchers at Palo Alto Networks have detected two versions of a malware similar to Shamoon which attacked 35,000...
-
 327Hacked
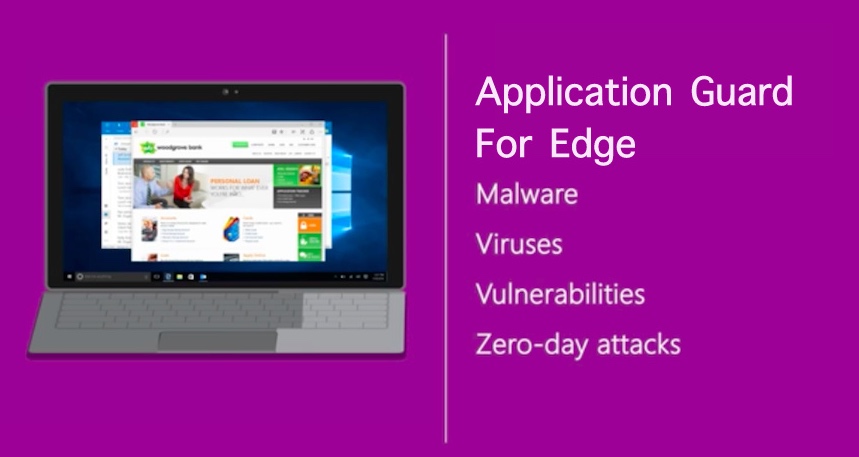
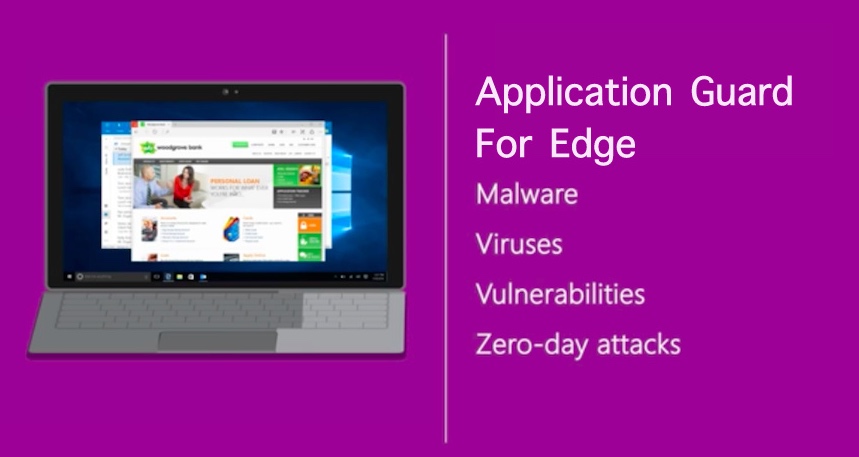
327HackedWindows 10 Will Run Edge Browser In A Virtual Machine For Extra Security
Short Bytes: At its Ignite conference, Microsoft announced Windows Defender Application Guard for its Edge Browser. This technology will run Edge in...
-

 92Data Security
92Data SecurityNew cloud attack takes full control of virtual machines with little effort
Existing crypto software “wholly unequipped” to counter Rowhammer attacks. The world has seen the most unsettling attack yet resulting from the so-called Rowhammer...
-
 257Geek
257Geek33% Of Microsoft Azure Virtual Machines Now Run Linux Operating System
Short Bytes: Microsoft’s investments in cloud-based open source technologies is now paying off. Thanks to the high demand for Linux on Azure, more...
-

 109Opinion
109OpinionVirtual machine security – offloading the endpoint
If many endpoints’ traffic pass through the VM host, why not move security there, sort of catch “bad things” before they even...






