Search results for "Vulnerability Management"
-

 3.7KVulnerabilities
3.7KVulnerabilitiesGoogle Launches New Cybersecurity Initiatives to Strengthen Vulnerability Management
Google on Thursday outlined a set of initiatives aimed at improving the vulnerability management ecosystem and establishing greater transparency measures around exploitation....
-

 312News
312NewsOverview Of Vulnerability Management
As we discuss more and more stories about vulnerabilities everyday here in Hackercombat.com, we need to empower you – our readers of...
-
 172Articles
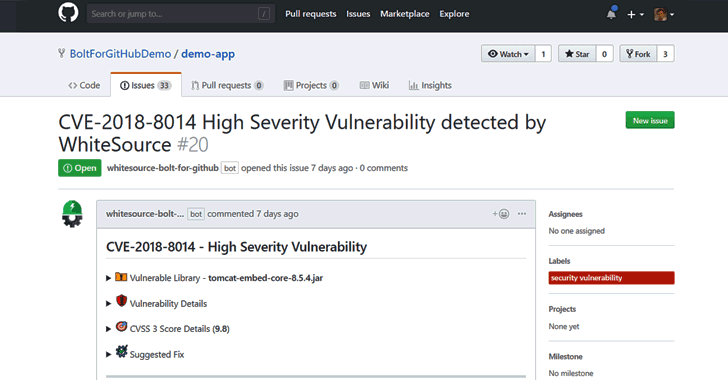
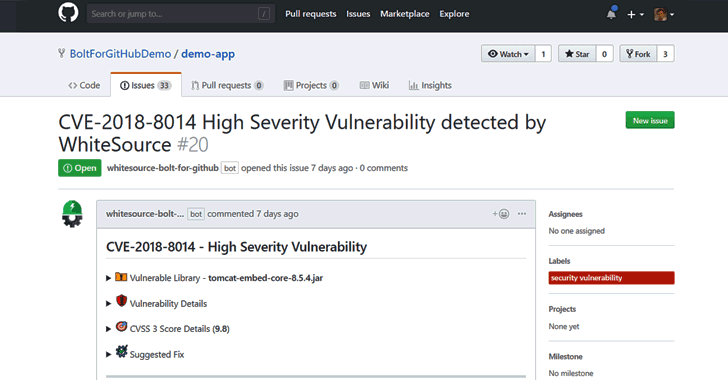
172ArticlesFree Open Source Vulnerability Management App for Developers
Developers around the world depend on open source components to build their software products. According to industry estimates, open source components account...
-

 343Vulnerability Analysis
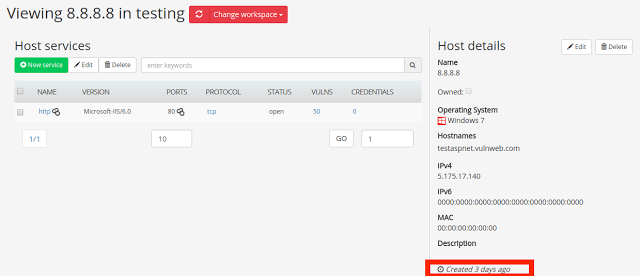
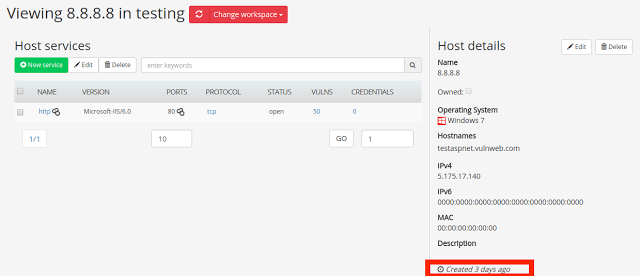
343Vulnerability AnalysisFaraday v3.3 – Collaborative Penetration Test and Vulnerability Management Platform
Here’s the main new features and improvements in Faraday v3.3: Workspace archive You are now able to make the whole workspace read...
-
 250Vulnerability Analysis
250Vulnerability AnalysisFaraday v2.7 – Collaborative Penetration Test and Vulnerability Management Platform
Faraday is the Integrated Multiuser Risk Environment you have always been looking for! It maps and leverages all the data you generate in real time,...
-
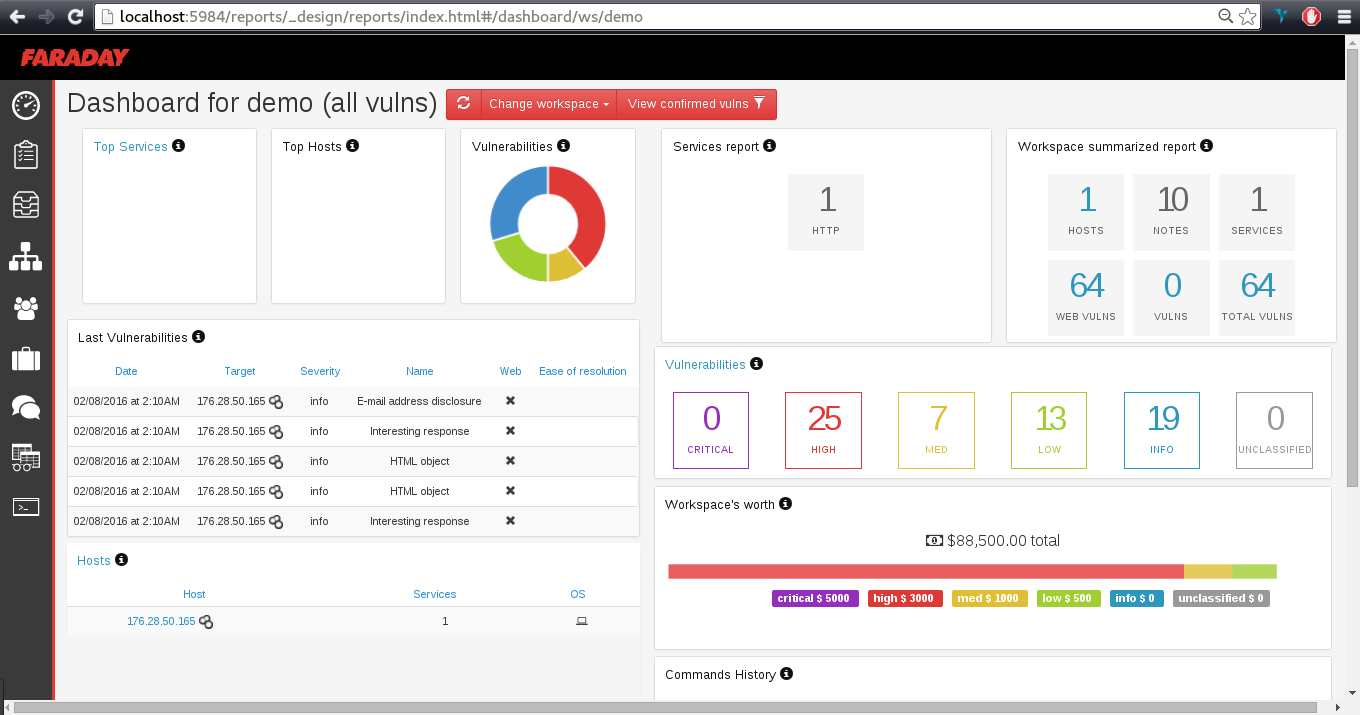
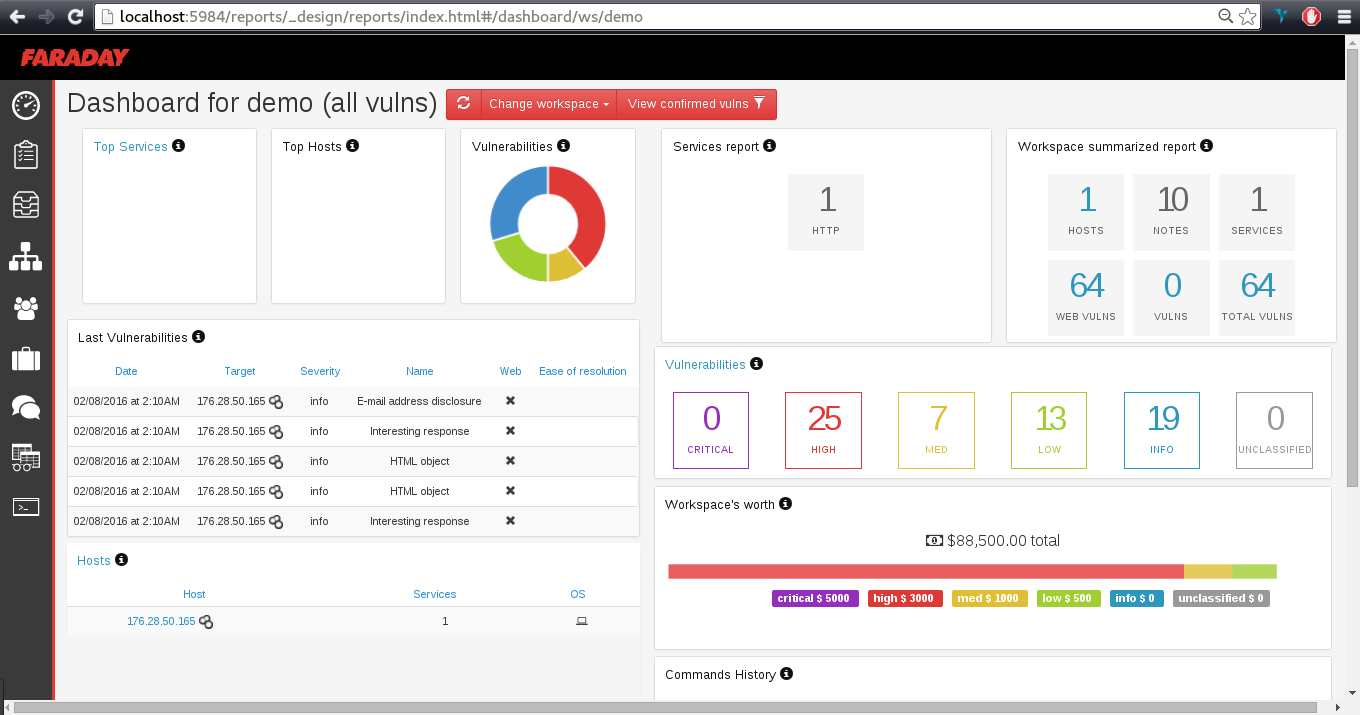 186Hack Tools
186Hack ToolsFaraday – Penetration Test and Vulnerability Management Platform
Faraday introduces a new concept – IPE (Integrated Penetration-Test Environment) a multiuser Penetration test IDE. Designed for distribution, indexation and analysis of...
-

 624Vulnerabilities
624VulnerabilitiesAtlassian’s Jira Service Management Found Vulnerable to Critical Vulnerability
Atlassian has released fixes to resolve a critical security flaw in Jira Service Management Server and Data Center that could be abused...
-

 1.3KVulnerabilities
1.3KVulnerabilitiesSERIOUS PRIVILEGES ESCALATION VULNERABILITY IN SYMANTEC PRIVILEGED ACCESS MANAGEMENT
Protecting sensitive organizational credentials, limiting privileged user access, actively imposing security policies, and monitoring and recording privileged user behavior across virtual, cloud,...
-

 2.1KVulnerabilities
2.1KVulnerabilitiesExploitation code for CVE-2022-1388 available: Critical remote code execution vulnerability in F5 Network management tools
A few days ago, the security teams of F5 Networks reported the correction of more than 50 vulnerabilities in various versions of...
-

 4.5KVulnerabilities
4.5KVulnerabilitiesHigh severity vulnerability in Sudo affects Aruba AirWave management platform allows any local user to gain root privileges
Hewlett Packard Enterprise (HPE) security teams report a severe vulnerability in Sudo, the open source program used by the Aruba AirWave solution....
-

 3.5KVulnerabilities
3.5KVulnerabilitiesZero day vulnerability in Codester Medisol, a doctors’ patient management system
Cybersecurity specialists report the discovery of a critical vulnerability in Medisol, a medical services management system developed by the technology firm Codester....
-

 3.8KHack Tools
3.8KHack ToolsMondoo v0.6 releases: Cloud-Native Security & Vulnerability Risk Management
Mondoo Mondoo is a natural language query system for scanning, deploying and remediating your cloud-native applications. Feature Insights into your fleet Ask...
-

 316Vulnerabilities
316VulnerabilitiesCritical vulnerability in Cisco network management tool: Network Assurance Engine
The company discovered a severe security flaw during a routine process Cisco has notified its customers that it is necessary to install...
-
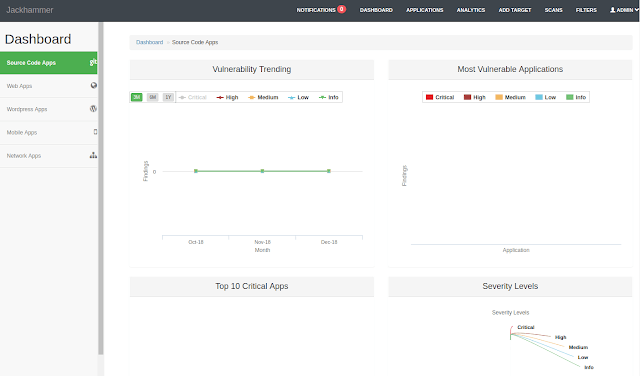
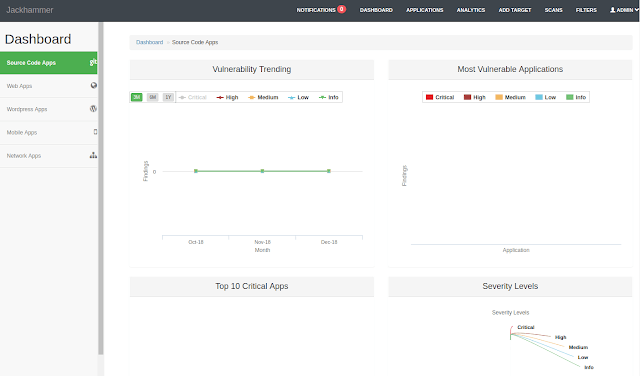 286Information Gathering
286Information GatheringJackhammer – One Security Vulnerability Assessment/Management Tool To Solve All The Security Team Problems
One Security vulnerability assessment/management tool to solve all the security team problems. What is Jackhammer? Jackhammer is a collaboration tool built with...
-

 266Incident Response
266Incident ResponseArchery – Open Source Vulnerability Assessment and Management
Archery is an opensource vulnerability assessment and management tool which helps developers and pentesters to perform scans and manage vulnerabilities. Archery uses...
-
Articles
Another Vulnerability is found in Intel Management Engine which allows execution of Code with no Digital Fingerprint
Taking advantage of Intel ME technology, within which attackers can execute unsigned code on the target machine. This leads to a full...






