Search results for "Vulnerable Apps"
-

 149Articles
149ArticlesCritical SQLite Flaw Leaves Millions of Apps Vulnerable to Hackers
Cybersecurity researchers have discovered a critical vulnerability in widely used SQLite database software that exposes billions of deployments to hackers. Dubbed as...
-

 273News
273NewsAre Apps Like Slack And Dropbox Actually Vulnerable To Attack?
According to a recent survey report, many big IT decision-makers see Enterprise Communication and Collaboration (EC&C ) apps like Slack, Dropbox, etc...
-

 138Incidents
138IncidentsVehicle-sharing apps are vulnerable to hacking
Researchers specializing in enterprise data protection services have analyzed more than a dozen mobile apps provided by shared car companies and have...
-

 151Cyber Attack
151Cyber AttackMajor Banking Apps Are Vulnerable To Man In The Middle Attack Over SSL
Man In The Middle Attack Over SSL A group of security researchers found a critical man in the middle attack implementation gap...
-

 351Vulnerabilities
351VulnerabilitiesMan-in-the-middle flaw left smartphone banking apps vulnerable
A flaw in certificate pinning exposed customers of a number of high-profile banks to man-in-the-middle attacks on both iOS and Android devices....
-

 202Vulnerability Analysis
202Vulnerability AnalysisDorkNet – Selenium Powered Python Script To Automate Searching For Vulnerable Web Apps
Selenium powered Python script to automate searching the web for vulnerable applications. DorkNet can take a single dork or a list of...
-
 127Geek
127Geek76 Famous iOS Apps Vulnerable to Silent Data Interception
The IT security researchers at Verify.ly, a service responsible for scanning the binary coding of iOS apps to identify any prevailing security...
-
 172Vulnerabilities
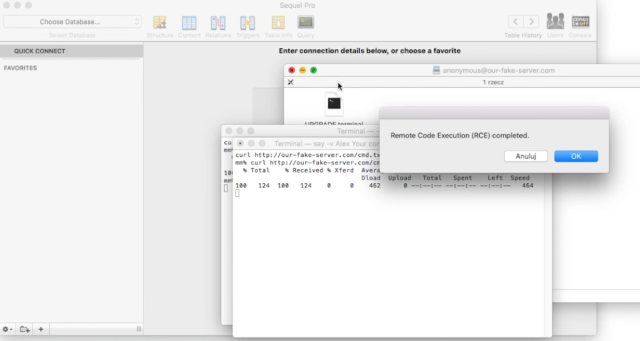
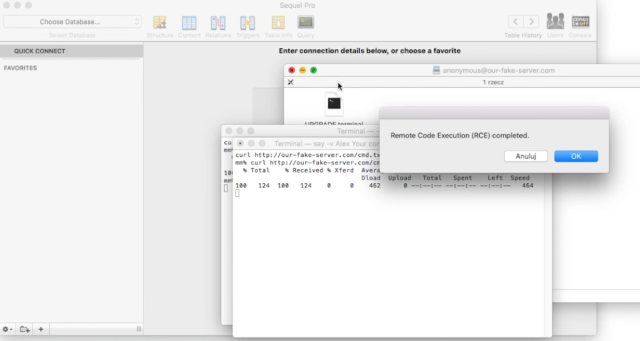
172Vulnerabilities“Huge” number of Mac apps vulnerable to hijacking, and a fix is elusive
Apps that use 3rd-party updater over insecure HTTP channels subject to MiTM attacks. Camtasia, uTorrent, and a large number of other Mac...
-

 284Geek
284GeekAndroid Devices Vulnerable to Certifi-Gate Flaw Exploited By Remote Support Apps
Officials at Check Point, the IT security vendor, have discovered a rogue app on the Google Play Store that is exploiting the...
-

 164Hacked
164HackedThousands of Popular iOS and Android Apps Still Vulnerable to FREAK
While whole world was worried about the FREAK vulnerability of the browsers, hundreds of popular apps of Android and iOS are still...






