All posts tagged "bluetooth"
-

 3.0KVulnerabilities
3.0KVulnerabilitiesNew Bluetooth Flaw Let Hackers Take Over Android, Linux, macOS, and iOS Devices
A critical Bluetooth security flaw could be exploited by threat actors to take control of Android, Linux, macOS and iOS devices. Tracked...
-

 2.7KMalware
2.7KMalwareNew Bluetooth Flaws Let Attackers Impersonate Legitimate Devices
Adversaries could exploit newly discovered security weaknesses in Bluetooth Core and Mesh Profile Specifications to masquerade as legitimate devices and carry out...
-

 5.1KMalware
5.1KMalwareNew Bluetooth Flaws Let Attackers Impersonate Legitimate Devices
Adversaries could exploit newly discovered security weaknesses in Bluetooth Core and Mesh Profile Specifications to masquerade as legitimate devices and carry out...
-
 1.1KMalware
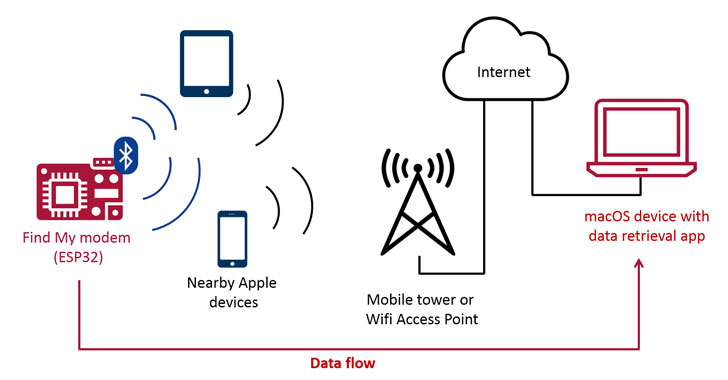
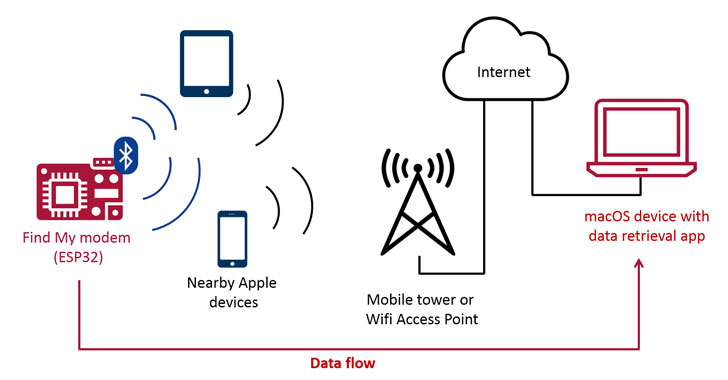
1.1KMalwareApple’s Find My Network Can be Abused to Exfiltrate Data From Nearby Devices
Latest research has demonstrated a new exploit that enables arbitrary data to be uploaded from devices that are not connected to the...
-

 1.9KInformation Gathering
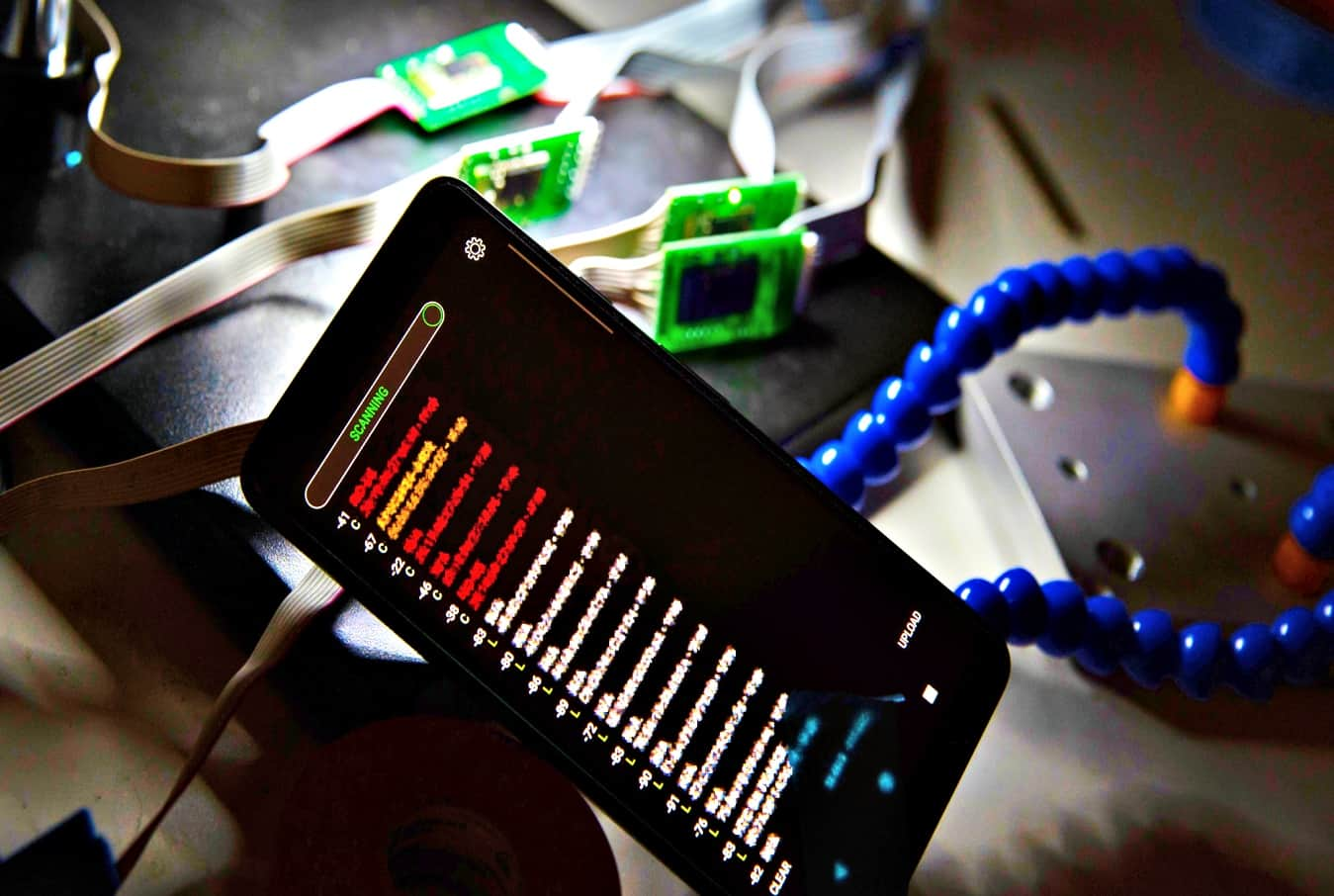
1.9KInformation GatheringRadareEye – Scan Nearby devices [BLE, Bluetooth And Wifi]
A tool made for specially scanning nearby devices[BLE,Bluetooth & Wifi] and execute our given command on our system when the target...
-
 2.9KVulnerabilities
2.9KVulnerabilitiesHow to use headphones or Bluetooth to hack and take control of any Android device
A recent research published by vulnerability testing specialists from Purdue University details a new exploit that abuses some Android operating system smartphones...
-

 388Vulnerabilities
388VulnerabilitiesTurn off your Bluetooth. Experts discover new Bluetooth KNOB vulnerability
A group of vulnerability testing researchers has revealed a new method to break Bluetooth’s encryption key negotiation protocol; the attack, dubbed ‘Key...
-
 310Data Security
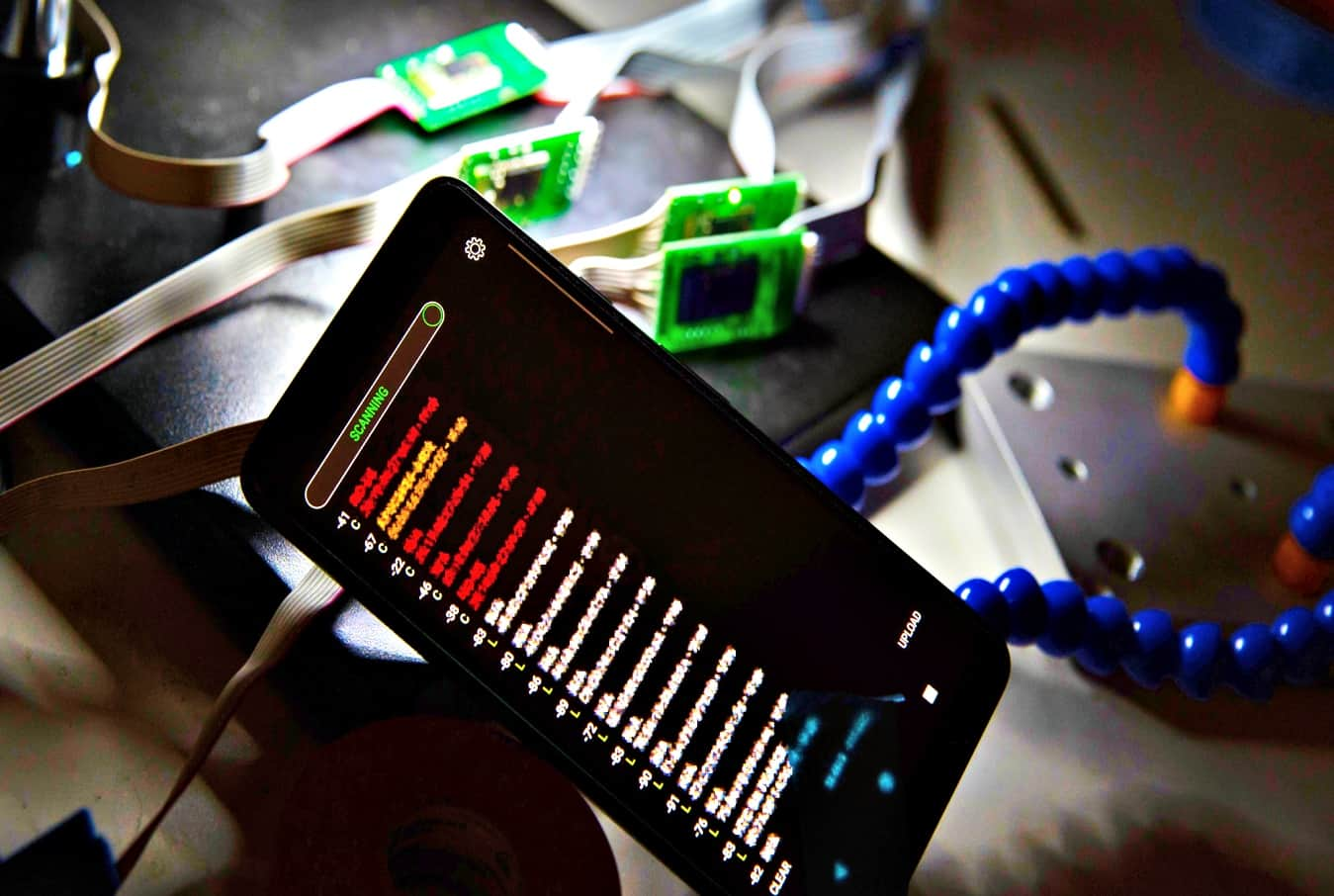
310Data SecurityBluetana app detects gas pumps card skimmers in 3 seconds
Bluetana takes 3 seconds to detect illegal card skimmers, unlike law enforcement agencies who can take up to 30 minutes for inspection....
-

 414Vulnerabilities
414VulnerabilitiesNew Bluetooth vulnerability allows hacking iOS and Android devices
Wireless protocols are not exempt from cybersecurity risks. IT security audit specialists say that more than one billion Bluetooth-enabled devices (smartphones, IoT...
-

 338News
338NewsBluetooth Flaw Allows Tracking Of Windows, iOS, macOS Devices But Android Is Safe
A recent flaw found in Bluetooth can be used to track Bluetooth devices, which mostly include phones, laptops and other devices by...
-

 219News
219NewsiPhone XI Could Play Music On Two Audio Devices Simultaneously
If reports from Macotakara are to be believed, the 2019 iPhone will feature dual Bluetooth audio support. The current generation of iPads...
-
 227News
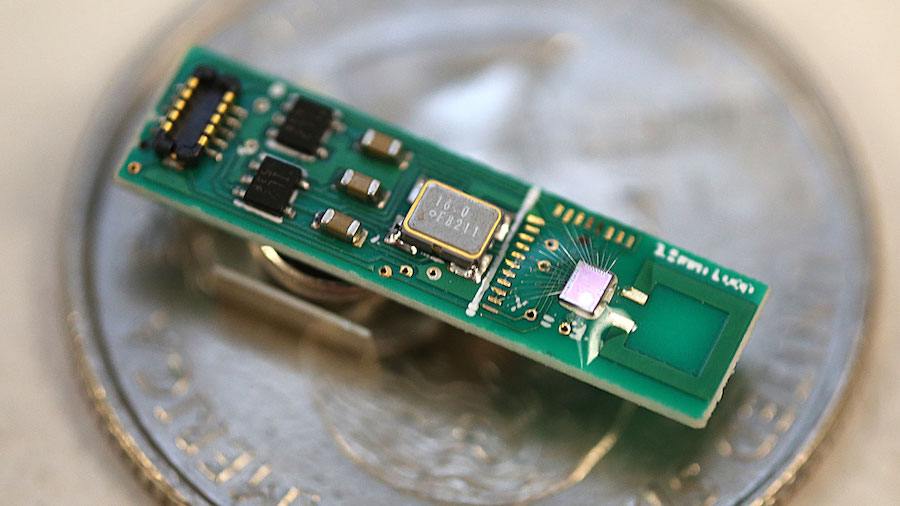
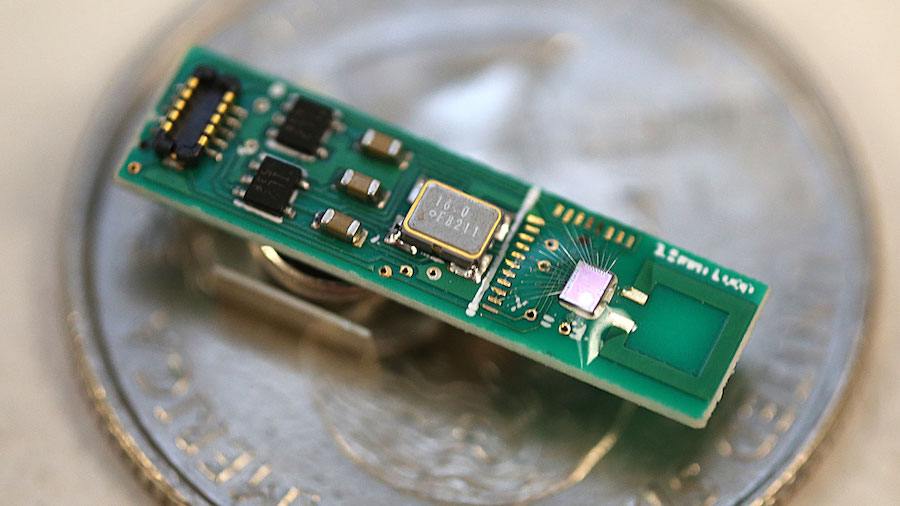
227NewsFirst Millimeter-sized Bluetooth Chip Invented To Send Low-Energy Data Packets
We are surrounded by Bluetooth radio signals and most of the devices that we see around — smartphones, wireless computer networks, and wireless...
-

 370Geek
370GeekNew Samsung Galaxy S10 review and features
The all new Samsung Galaxy S10 family has been released by Samsung on 8th March, 2019 and despite the high price &...
-

 317News
317NewsCritical SHAREit Flaw Gives Attackers Full Access To Device Files
Data sharing apps like SHAREit and Xender have transformed the way files are shared, since their release a few years ago. The...
-

 261Vulnerabilities
261VulnerabilitiesVulnerability in Xiaomi scooters could put the users’ life at risk
The flaw allows sending unauthenticated commands via Bluetooth to the scooter Although the use of smart devices has simplified many daily tasks,...
-

 235News
235NewsIntel Discovers And Publishes New Bluetooth Vulnerability
Turns out, Intel has now discovered and published a new Bluetooth vulnerability, which could help intercept and manipulate transmissions between two compatible...
-

 321Data Security
321Data SecurityUpdate your devices: New Bluetooth flaw lets attackers monitor traffic
The Bluetooth flaw also opens door to a man-in-the-middle attack. The IT security researchers at Israel Institute of Technology have discovered a critical security vulnerability in...
-

 407Data Security
407Data SecurityDNS rebinding attack puts half a billion IoT devices at risk
Armis, an Internet of Things (IoT) security vendor and cyber-security firm, reports that about half a billion smart devices being used around...
-
 280Video Tutorials
280Video TutorialsHow to Enable/Fix Bluetooth Problem in Kali Linux 2017.3
If you are running Kali Linux and your Bluetooth is not working. Let’s fix that. It will be up and running in...
-

 227Security Tools
227Security ToolsBlueMaho v090417 – Bluetooth Security Testing Suite
BlueMaho is GUI-shell (interface) for suite of tools for testing security of bluetooth devices. It is freeware, opensource, written on python, uses...
-

 282Man-In-The-Middle
282Man-In-The-MiddleBtleJuice Framework – Bluetooth Smart (LE) Man-in-the-Middle Framework
BtleJuice is a complete framework to perform Man-in-the-Middle attacks on Bluetooth Smart devices (also known as Bluetooth Low Energy). It is composed...






