All posts tagged "cryptocurrency"
-
 4.9KMalware
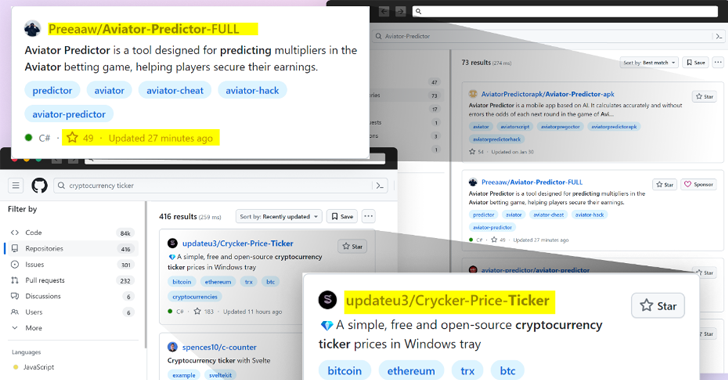
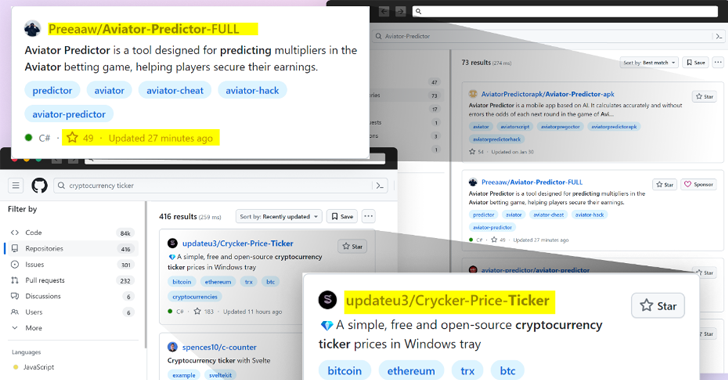
4.9KMalwareBeware: GitHub’s Fake Popularity Scam Tricking Developers into Downloading Malware
Threat actors are now taking advantage of GitHub’s search functionality to trick unsuspecting users looking for popular repositories into downloading spurious counterparts...
-

 2.5KMalware
2.5KMalwareAttackers Using Obfuscation Tools to Deliver Multi-Stage Malware via Invoice Phishing
Cybersecurity researchers have discovered an intricate multi-stage attack that leverages invoice-themed phishing decoys to deliver a wide range of malware such as...
-

 1.2KMalware
1.2KMalwareGoogle Sues App Developers Over Fake Crypto Investment App Scam
Google has filed a lawsuit in the U.S. against two app developers for allegedly engaging in an “international online consumer investment fraud...
-

 4.6KMalware
4.6KMalwareHackers Target macOS Users with Malicious Ads Spreading Stealer Malware
Malicious ads and bogus websites are acting as a conduit to deliver two different stealer malware, including Atomic Stealer, targeting Apple macOS...
-

 2.0KVulnerabilities
2.0KVulnerabilitiesCritical Unpatched Ray AI Platform Vulnerability Exploited for Cryptocurrency Mining
Cybersecurity researchers are warning that threat actors are actively exploiting a “disputed” and unpatched vulnerability in an open-source artificial intelligence (AI) platform...
-

 1.1KMalware
1.1KMalwareTeamCity Flaw Leads to Surge in Ransomware, Cryptomining, and RAT Attacks
Multiple threat actors are exploiting the recently disclosed security flaws in JetBrains TeamCity software to deploy ransomware, cryptocurrency miners, Cobalt Strike beacons,...
-
 2.8KMalware
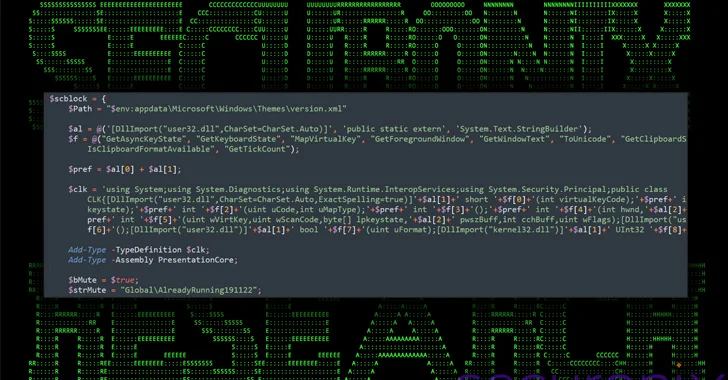
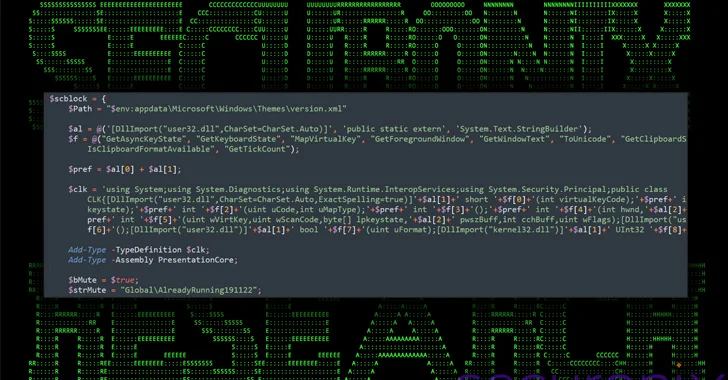
2.8KMalwareNew DEEP#GOSU Malware Campaign Targets Windows Users with Advanced Tactics
A new elaborate attack campaign has been observed employing PowerShell and VBScript malware to infect Windows systems and harvest sensitive information. Cybersecurity...
-
 4.1KMalware
4.1KMalwareHackers Using Sneaky HTML Smuggling to Deliver Malware via Fake Google Sites
Cybersecurity researchers have discovered a new malware campaign that leverages bogus Google Sites pages and HTML smuggling to distribute a commercial malware...
-
 506Data Breach
506Data BreachLockBit Ransomware Hacker Ordered to Pay $860,000 After Guilty Plea in Canada
A 34-year-old Russian-Canadian national has been sentenced to nearly four years in jail in Canada for his participation in the LockBit global...
-

 3.0KMalware
3.0KMalwareBianLian Threat Actors Exploiting JetBrains TeamCity Flaws in Ransomware Attacks
The threat actors behind the BianLian ransomware have been observed exploiting security flaws in JetBrains TeamCity software to conduct their extortion-only attacks....
-

 1.8KCyber Attack
1.8KCyber AttackExit Scam: BlackCat Ransomware Group Vanishes After $22 Million Payout
The threat actors behind the BlackCat ransomware have shut down their darknet website and likely pulled an exit scam after uploading a...
-

 2.8KVulnerabilities
2.8KVulnerabilitiesWordPress Plugin Alert – Critical SQLi Vulnerability Threatens 200K+ Websites
A critical security flaw has been disclosed in a popular WordPress plugin called Ultimate Member that has more than 200,000 active installations....
-

 3.8KMalware
3.8KMalwareNew Migo Malware Targeting Redis Servers for Cryptocurrency Mining
A novel malware campaign has been observed targeting Redis servers for initial access with the ultimate goal of mining cryptocurrency on compromised...
-

 1.9KData Breach
1.9KData BreachLockBit Ransomware Operation Shut Down; Criminals Arrested; Decryption Keys Released
The U.K. National Crime Agency (NCA) on Tuesday confirmed that it obtained LockBit’s source code as well as a wealth of intelligence...
-

 2.9KVulnerabilities
2.9KVulnerabilitiesFritzFrog Returns with Log4Shell and PwnKit, Spreading Malware Inside Your Network
The threat actor behind a peer-to-peer (P2P) botnet known as FritzFrog has made a return with a new variant that leverages the...
-

 3.6KMalware
3.6KMalwareHeadCrab 2.0 Goes Fileless, Targeting Redis Servers for Crypto Mining
Cybersecurity researchers have detailed an updated version of the malware HeadCrab that’s known to target Redis database servers across the world since...
-

 1.6KData Breach
1.6KData BreachU.S., U.K., Australia Sanction Russian REvil Hacker Behind Medibank Breach
Governments from Australia, the U.K., and the U.S. have imposed financial sanctions on a Russian national for his alleged role in the...
-
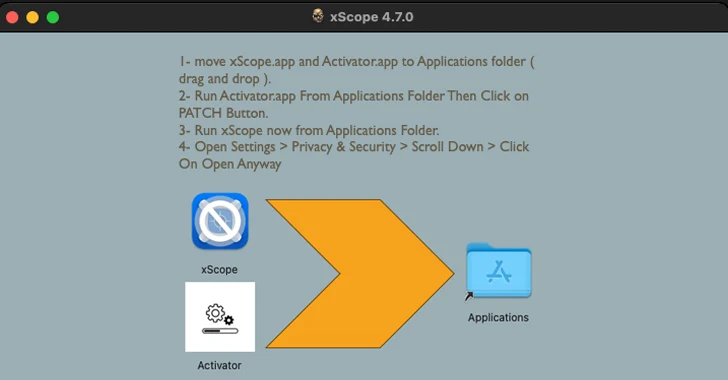
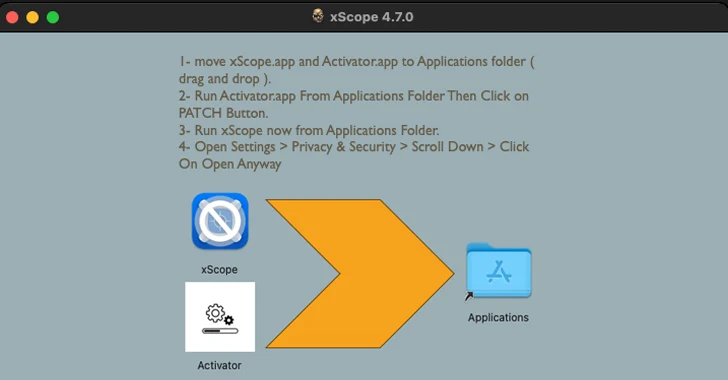 3.5KMalware
3.5KMalware“Activator” Alert: MacOS Malware Hides in Cracked Apps, Targeting Crypto Wallets
Cracked software have been observed infecting Apple macOS users with a previously undocumented stealer malware capable of harvesting system information and cryptocurrency...
-

 478Data Breach
478Data BreachMFA Spamming and Fatigue: When Security Measures Go Wrong
In today’s digital landscape, traditional password-only authentication systems have proven to be vulnerable to a wide range of cyberattacks. To safeguard critical...
-

 793Malware
793MalwareHackers Weaponize Windows Flaw to Deploy Crypto-Siphoning Phemedrone Stealer
Threat actors have been observed leveraging a now-patched security flaw in Microsoft Windows to deploy an open-source information stealer called Phemedrone Stealer....
-

 2.7KMalware
2.7KMalwareCryptominers Targeting Misconfigured Apache Hadoop and Flink with Rootkit in New Attacks
Cybersecurity researchers have identified a new attack that exploits misconfigurations in Apache Hadoop and Flink to deploy cryptocurrency miners within targeted environments....






